
Reinforcement Learning Firmware Fuzzing IoT Security
Discover how reinforcement learning transforms firmware fuzzing for IoT security. Learn RL vs traditional methods, benchmarks, and automation with mr7.ai.
Stay updated with the latest in cybersecurity, ethical hacking techniques, and AI-powered security research.

Discover how reinforcement learning transforms firmware fuzzing for IoT security. Learn RL vs traditional methods, benchmarks, and automation with mr7.ai.
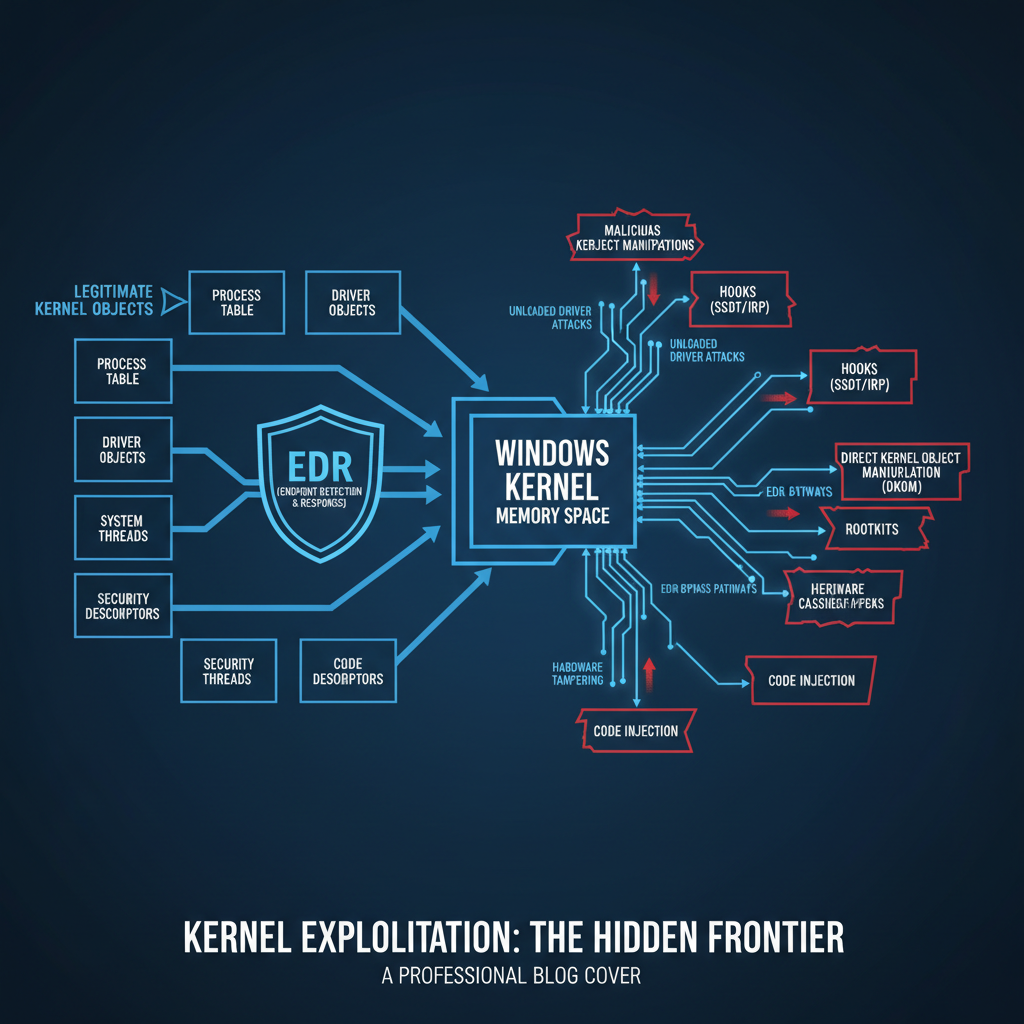
Learn how adversaries bypass EDR via kernel object manipulation. Discover detection evasion strategies and forensic countermeasures for blue teams. Try mr7.ai free.
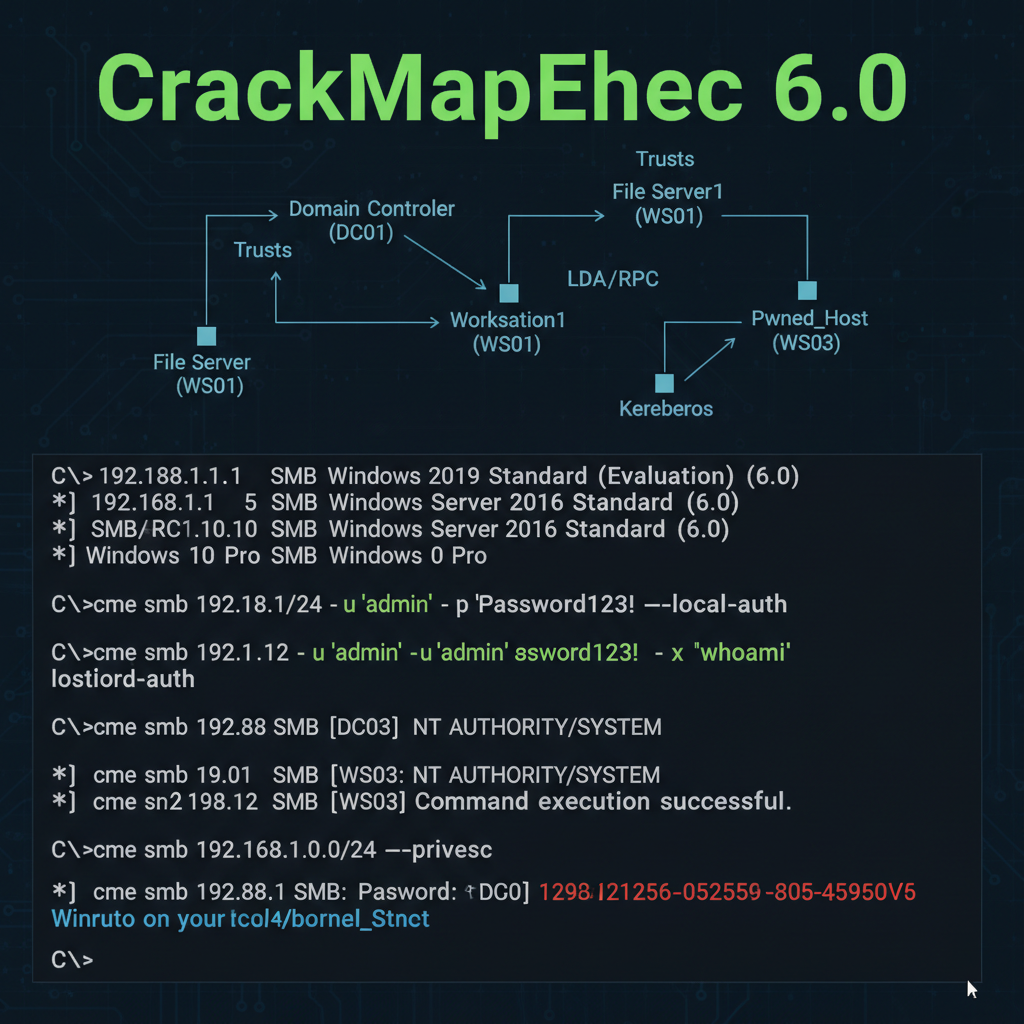
Deep dive into CrackMapExec 6.0's new features for AD pentesting. Learn Kerberos relay, LDAP abuse & modern auth techniques. Try mr7.ai free!

Discover how AI enhances browser-based living-off-the-land attacks using WebAssembly & WebGPU. Learn detection methods and defend against AI-assisted browser exploitation.
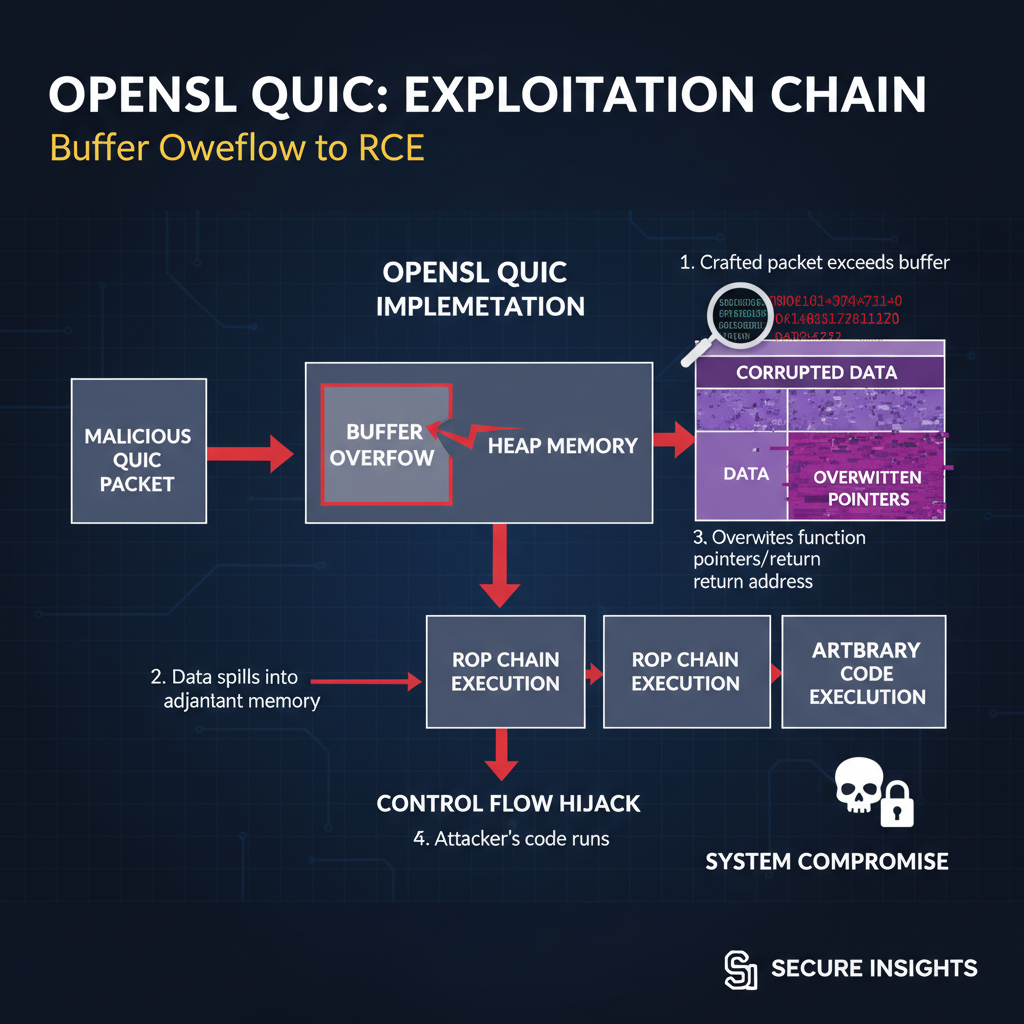
CVE-2026-40198 is a critical OpenSSL QUIC buffer overflow allowing RCE. Learn exploitation, patching, and mitigation. Try mr7.ai's free tools.
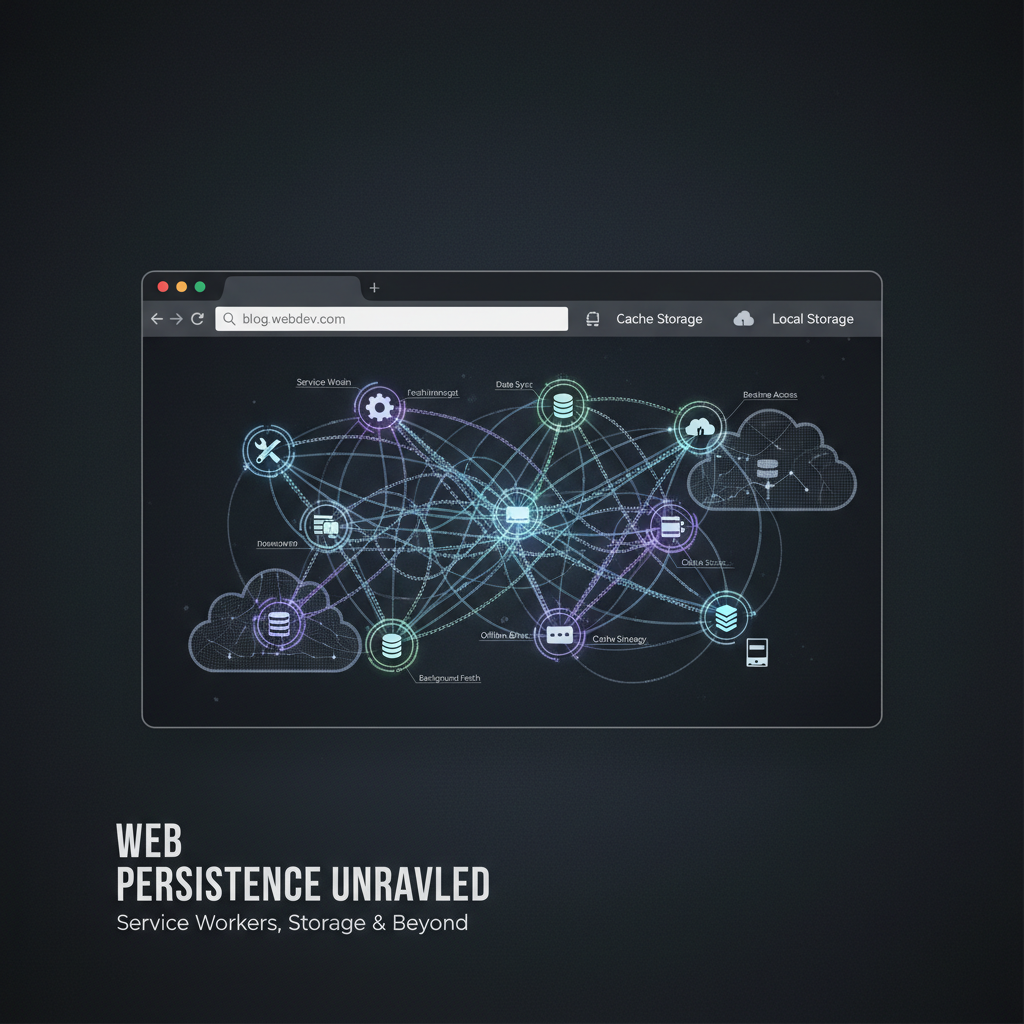
Master advanced browser based persistence techniques using service workers, IndexedDB, and WASM. Learn evasion methods and detection signatures. Try mr7.ai free.

Explore CloudBrute 2.0's enhanced cloud enumeration capabilities for AWS, Azure, GCP. Get 10,000 free tokens to test mr7.ai's AI-powered security tools.

Explore how AI voice cloning transforms BEC attacks in 2026. Learn detection methods, defensive strategies, and how mr7.ai helps combat these threats.
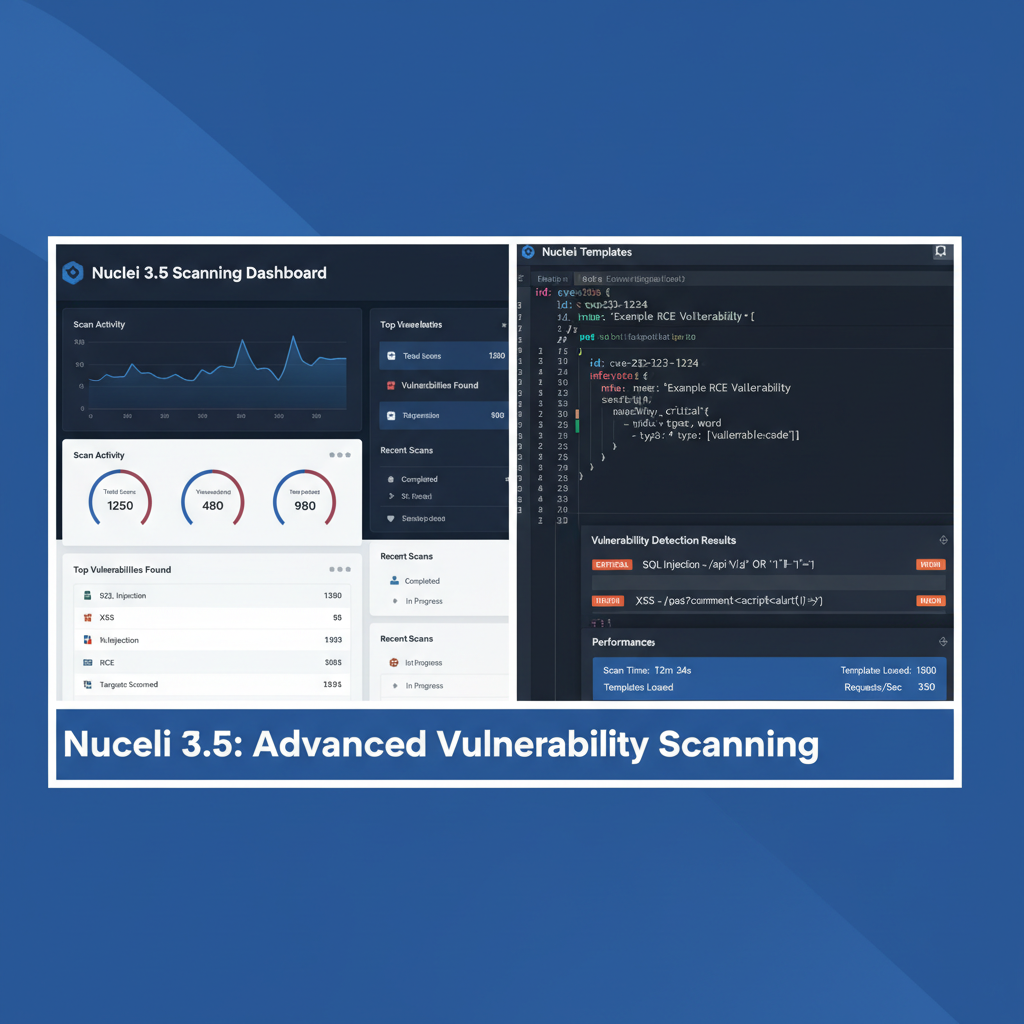
In-depth Nuclei vulnerability scanner review 2026 covering new features, performance benchmarks, and integration capabilities. Try mr7.ai free.

Learn advanced techniques for detecting FPGA-based network implants using JTAG interface analysis. Hands-on guide with real tools and methods.
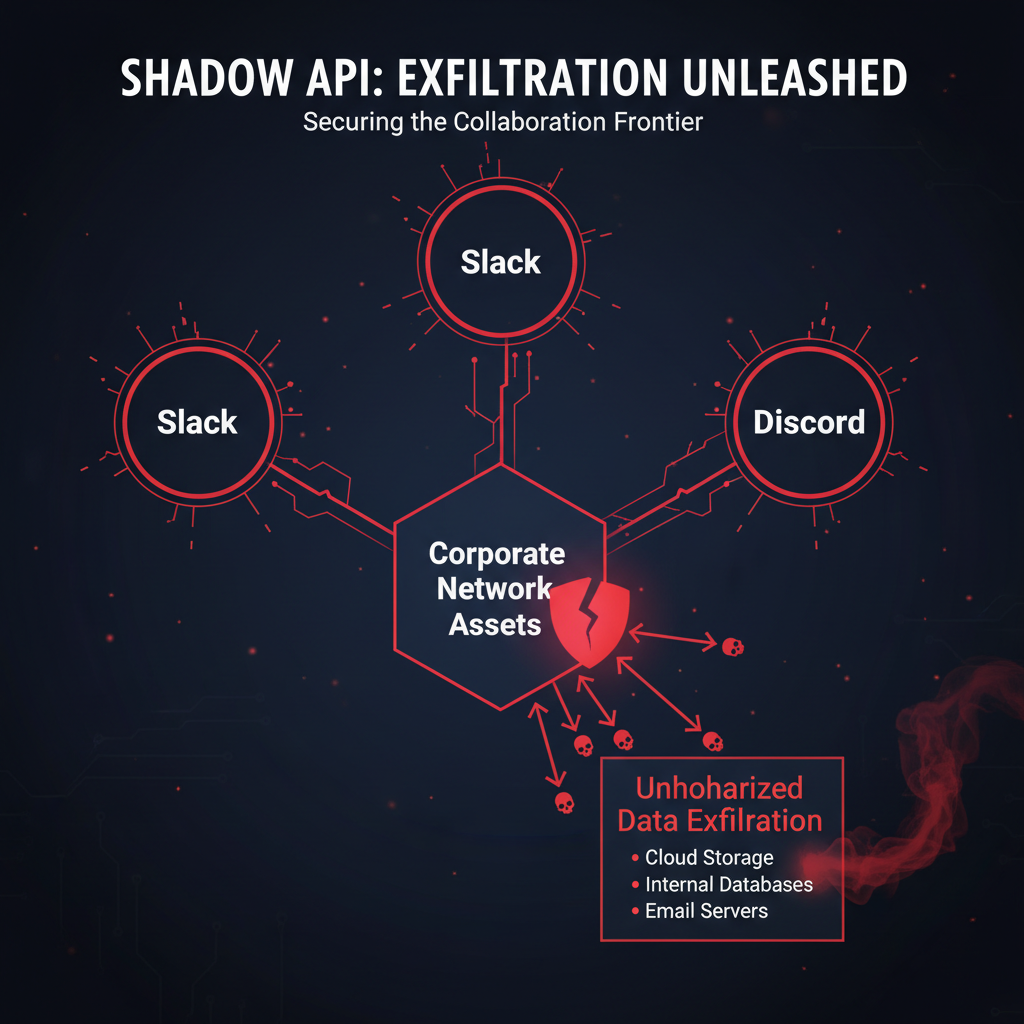
Discover 2026's emerging collaboration platform API abuse attacks targeting Slack, Teams & Discord. Learn detection, forensics & defense strategies.
Explore how transformer models enable AI-generated network traffic to evade detection. Learn defensive strategies and try mr7.ai's free tools.