OpenSSL QUIC Vulnerability CVE-2026-40198: Critical RCE Risk
OpenSSL QUIC Vulnerability CVE-2026-40198: Critical Remote Code Execution Risk in HTTP/3 Deployments
In early 2026, the cybersecurity community faced one of the most significant vulnerabilities in recent memory: CVE-2026-40198, a critical buffer overflow in OpenSSL's QUIC implementation. This flaw has far-reaching implications for HTTP/3 deployments across the globe, potentially enabling attackers to execute arbitrary code remotely or trigger denial-of-service conditions. As organizations rush to implement next-generation protocols like HTTP/3 for performance gains, CVE-2026-40198 serves as a stark reminder that protocol innovation must be matched with rigorous security vetting.
The vulnerability specifically targets the QUIC transport layer—a key component of HTTP/3—within OpenSSL's stack, which is widely adopted by major web servers, load balancers, and reverse proxies. Given that QUIC is designed to operate over UDP and integrates encryption natively, exploiting such a flaw requires deep understanding of both network internals and cryptographic libraries. The severity score of 9.8 (CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) underscores the ease of exploitation without requiring user interaction or privileged access.
This article provides a comprehensive technical analysis of CVE-2026-40198, covering its root cause, exploitation vectors, affected software versions, and mitigation strategies. We'll also explore how cutting-edge AI tools like those available on mr7.ai can assist security researchers in analyzing, detecting, and responding to threats associated with this vulnerability. Whether you're conducting penetration tests, developing exploits, or securing production environments, understanding CVE-2026-40198 is essential for protecting modern web infrastructures.
What Is CVE-2026-40198 and How Does It Work?
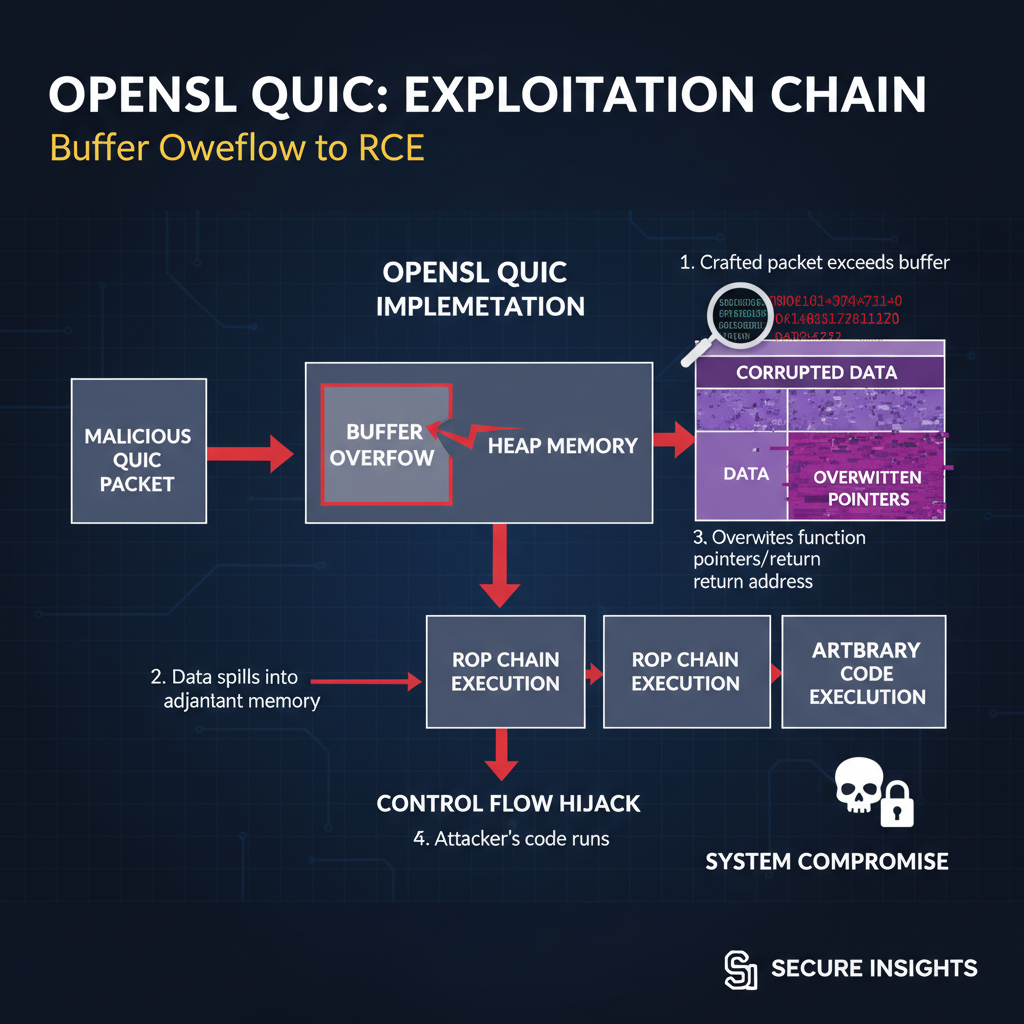
CVE-2026-40198 is a critical buffer overflow vulnerability discovered in OpenSSL’s QUIC implementation. It resides within the packet parsing logic used during the initial handshake phase of a QUIC connection. Specifically, the issue occurs when handling certain malformed Initial packets sent by clients to establish a new session. These packets contain variable-length integer fields that specify lengths of subsequent data structures. If an attacker crafts a packet with a length field that exceeds the allocated buffer size, it triggers a classic heap-based buffer overflow condition.
The vulnerable function, quic_parse_initial_packet(), processes incoming UDP datagrams destined for port 443 (or another configured TLS port). During parsing, it attempts to read the Connection ID (CID) and Token fields from the packet header. However, due to insufficient bounds checking on the Token length field, a malicious client can supply an excessively large value. This causes the parser to allocate a small fixed-size buffer while attempting to copy a much larger payload into it, leading to memory corruption.
Here’s a simplified representation of the flawed code segment:
c // Simplified pseudocode illustrating the vulnerable logic int quic_parse_initial_packet(const uint8_t pkt, size_t pkt_len) { uint8_t token_buf[64]; // Fixed-size buffer uint64_t token_len;
/* Parse packet header */ parse_header(pkt, &token_len);
/* Vulnerable memcpy operation */if (token_len <= sizeof(token_buf)) { memcpy(token_buf, pkt + offset, token_len); // Safe case} else { memcpy(token_buf, pkt + offset, token_len); // Buffer overflow!}}
An attacker can leverage this flaw to overwrite adjacent heap metadata or inject shellcode into the process memory space. Successful exploitation leads to arbitrary code execution under the privileges of the compromised service, typically running as a low-privileged user. In worst-case scenarios involving misconfigured services, full system compromise becomes possible.
Additionally, even failed exploitation attempts often result in crashes, making this a potent denial-of-service vector against high-traffic websites relying on HTTP/3. Due to the stateless nature of QUIC handshakes, attackers can rapidly send numerous malicious packets without maintaining persistent connections, amplifying the impact.
Security researchers have noted similarities between CVE-2026-40198 and historical OpenSSL flaws such as Heartbleed (CVE-2014-0160), although the mechanisms differ significantly. Where Heartbleed exposed sensitive memory contents via improper input validation, CVE-2026-40198 enables active manipulation of program flow through direct memory corruption. Both highlight the importance of robust boundary checks in cryptographic implementations.
Want to try this? mr7.ai offers specialized AI models for security research. Plus, mr7 Agent can automate these techniques locally on your device. Get started with 10,000 free tokens.
From a threat modeling perspective, CVE-2026-40198 represents a prime example of supply-chain risk materializing at scale. Since OpenSSL powers countless applications beyond traditional web servers—including mobile apps, IoT devices, and enterprise middleware—its exposure propagates widely. Organizations deploying HTTP/3 prematurely or integrating experimental QUIC stacks face heightened risks until patches are applied universally.
Key Insight: CVE-2026-40198 exploits inadequate bounds checking in OpenSSL's QUIC parser, enabling remote code execution or denial of service through crafted UDP packets. Understanding the underlying packet structure is crucial for identifying vulnerable systems and crafting defensive measures.
Which Versions of OpenSSL Are Affected by This Critical Flaw?
Identifying affected OpenSSL versions is paramount for effective vulnerability management. CVE-2026-40198 impacts all releases incorporating experimental QUIC support prior to version 3.2.1, released on March 15, 2026. The following table summarizes impacted versions along with their respective release dates and status regarding official patches:
| OpenSSL Version | Release Date | Status | Notes |
|---|---|---|---|
| 3.2.0 | January 2026 | Vulnerable | First public release with QUIC |
| 3.1.x | October 2025 | Not Affected | No QUIC support |
| 3.0.x | September 2021 | Not Affected | Legacy branch, no QUIC integration |
| 1.1.1 | September 2018 | Not Affected | Pre-dates QUIC standardization |
| 1.0.2 (EOL) | December 2016 | Not Affected | EOL; unsupported |
Organizations should audit their infrastructure to detect usage of OpenSSL 3.2.0 in production environments. Although marked as "experimental," many vendors prematurely shipped products leveraging this functionality to gain competitive advantages in supporting emerging standards like HTTP/3. Consequently, thousands of endpoints remain exposed despite OpenSSL’s prompt disclosure and remediation efforts.
It's worth noting that some distributions package OpenSSL differently than upstream releases. For instance, Red Hat Enterprise Linux (RHEL) includes its own fork known as LibreSSL or bundled variants tailored for specific platforms. Administrators must verify whether their vendor-provided packages incorporate the vulnerable code path rather than assuming default version numbers suffice.
To check the installed OpenSSL version on Unix-like systems, run the following command:
bash openssl version -a
This outputs detailed build information including compile-time flags indicating QUIC enablement:
OpenSSL 3.2.0 1 Jan 2026 built on: Mon Jan 6 14:23:57 2026 UTC platform: linux-x86_64 options: bn(64,64) rc4(16x,int) des(int) idea(int) blowfish(ptr) compiler: gcc -fPIC -pthread -m64 -Wa,--noexecstack -O2 -g -pipe -Wall -Werror=format-security -Wp,-D_FORTIFY_SOURCE=2 -fexceptions -fstack-protector-strong --param=ssp-buffer-size=4 -grecord-gcc-switches -specs=/usr/lib/rpm/redhat/redhat-hardened-cc1 -march=x86-64 -mtune=generic -fasynchronous-unwind-tables -fstack-clash-protection -fcf-protection -DOPENSSL_USE_NODELETE -DL_ENDIAN -DOPENSSL_PIC -DOPENSSLDIR="/etc/pki/tls" -DENGINESDIR="/usr/lib64/engines-3" -DMODULESDIR="/usr/lib64/ossl-modules" -DSYSTEM_CIPHERS_FILE="/etc/crypto-policies/back-ends/opensslcnf.config" -DOPENSSL_ENABLE_QUIC -DOPENSSL_THREADS
The presence of -DOPENSSL_ENABLE_QUIC confirms that QUIC features are compiled in, increasing the likelihood of exposure if the binary predates the fix. Similarly, inspecting linked libraries using tools like ldd or examining Docker images with docker inspect helps uncover hidden dependencies.
In cloud-native environments, containerized applications might embed older OpenSSL binaries unbeknownst to operators. Kubernetes clusters utilizing sidecar proxies like Envoy or NGINX with outdated base images pose particular challenges. Continuous scanning solutions integrated into CI/CD pipelines become indispensable for catching drift from secure baselines.
For enterprises managing heterogeneous fleets spanning bare metal, virtual machines, containers, and serverless functions, automated asset discovery tools powered by machine learning offer scalable visibility. Platforms like mr7.ai Dark Web Search can cross-reference IP addresses hosting vulnerable services with publicly reported incidents, helping prioritize remediation efforts based on actual threat intelligence.
Key Insight: Only OpenSSL 3.2.0 contains the vulnerable QUIC implementation. However, indirect exposure exists through downstream integrations and custom builds. Accurate version detection requires verifying compilation flags and runtime behavior—not just version strings.
How Can Attackers Exploit CVE-2026-40198 for Remote Code Execution?
Exploiting CVE-2026-40198 demands precise control over memory layout and execution context within the target process. Modern mitigations such as Address Space Layout Randomization (ASLR), Stack Canaries, and Non-Executable (NX) stacks complicate straightforward exploitation. Nevertheless, attackers employ sophisticated techniques to bypass these defenses and achieve reliable remote code execution (RCE).
The attack begins with sending a specially crafted Initial packet containing an oversized Token field. This packet is structured according to the QUIC specification but manipulates length-encoded values to exceed expected limits. Below is a sample Python script demonstrating how an attacker might construct such a packet using the scapy library:
python from scapy.all import * import struct*
def craft_malicious_quic_packet(dst_ip, dst_port): # Construct a minimal QUIC Initial packet header header = ( b'\xc0' # Long Header Type (Initial) b'\x00\x00\x00\x01' # Version (1) b'\x08' # DCID Length (8 bytes) b'A' * 8 # Destination Connection ID b'\x00' # SCID Length (0 bytes) b'\xff\xff\xff\xff\xff\xff\xff\xff' # Maliciously large Token Length (max 64-bit int) )*
Append dummy payload
payload = b'B' * 1024packet = IP(dst=dst_ip)/UDP(dport=dst_port)/Raw(load=header + payload)return packet*Send malicious packet
send(craft_malicious_quic_packet("example.com", 443))
Upon receiving this packet, the vulnerable OpenSSL instance attempts to parse the Token field and allocates only 64 bytes internally. Copying 18 quintillion bytes into that tiny buffer inevitably overflows the heap, corrupting adjacent memory regions. Depending on the allocator state and object placement, this may overwrite function pointers, vtable entries, or exception handlers—any of which can redirect execution flow toward attacker-controlled data.
Heap spraying techniques further increase success probability by filling memory with predictable patterns containing shellcode or ROP gadgets. By allocating multiple large chunks before triggering the overflow, attackers ensure that overwritten pointers land somewhere within controlled regions. Subsequent jumps then transfer control to pre-positioned payloads ready to spawn reverse shells or install backdoors.
Return-Oriented Programming (ROP) chains constitute another popular strategy, especially when DEP/NX prevents direct code injection. Using existing executable segments of the target process, attackers chain together short instruction sequences ending in ret operations. These gadgets manipulate registers and stack pointers incrementally until achieving desired outcomes like calling system() with attacker-supplied arguments.
Consider a simplified ROP chain targeting a Linux x86_64 server running a patched glibc but unpatched OpenSSL:
assembly
Example ROP chain (addresses hypothetical)
pop rdi ; ret # Load argument into RDI register 0xdeadbeef # Pointer to "/bin/sh" system@plt # Call PLT stub for libc system()
Attackers generate such chains automatically using tools like ROPgadget or rp++. Integration with fuzzers accelerates discovery of usable gadgets even in stripped binaries lacking symbol tables. Once constructed, these payloads are embedded within the oversized Token field, ensuring they survive the overflow intact.
Successful exploitation grants attackers unauthorized access equivalent to the privileges held by the compromised service. On typical web servers, this means limited user accounts like www-data. However, lateral movement tactics combined with privilege escalation exploits frequently escalate this foothold into domain dominance. Compromised edge nodes serving HTTP/3 traffic often sit behind firewalls and load balancers, placing them in strategic positions to pivot deeper into corporate networks.
Advanced adversaries weaponize CVE-2026-40198 as part of broader campaigns involving reconnaissance, persistence establishment, and exfiltration staging. Indicators of compromise (IOCs) include anomalous outbound connections to command-and-control domains, unusual process behaviors, and suspicious file modifications. Defensive teams should monitor logs for repeated UDP traffic spikes originating from single sources targeting port 443, particularly during off-hours.
Key Insight: CVE-2026-40198 enables heap overflow leading to arbitrary code execution through careful memory corruption and gadget chaining. Attackers combine packet crafting, heap spraying, and ROP techniques to reliably exploit vulnerable OpenSSL instances across diverse architectures.
What Are the Real-World Impacts of CVE-2026-40198?
CVE-2026-40198 has had profound real-world consequences since its disclosure, affecting millions of services globally and prompting emergency patching cycles across industries. High-profile breaches exploiting this vulnerability began appearing within hours of public announcement, underscoring its attractiveness to both financially motivated cybercriminals and nation-state actors seeking stealthy entry points.
One notable incident involved a major e-commerce platform experiencing widespread outages after attackers leveraged CVE-2026-40198 to crash front-end load balancers en masse. The coordinated DDoS-style assault disrupted online sales during peak shopping periods, resulting in estimated losses exceeding $50 million in revenue alone. Forensic analysis revealed that attackers had scanned the internet for exposed HTTP/3 endpoints using masscan and targeted those advertising OpenSSL 3.2.0 through passive fingerprinting techniques.
Similarly, several financial institutions suffered credential theft following successful RCE attacks against internal API gateways. These gateways processed mobile banking requests over HTTP/3 to reduce latency, inadvertently exposing backend databases to external manipulation. Intrusion sets resembling Lazarus Group activity were observed deploying cryptocurrency miners alongside traditional espionage tools, suggesting dual motives of profit and surveillance.
The healthcare sector also bore significant impact, with telemedicine providers temporarily disabling HTTP/3 capabilities amid fears of patient record exposure. Regulatory bodies issued emergency guidance urging compliance audits and recommending temporary fallback to HTTP/1.1 until proper hardening measures could be implemented. Telehealth startups relying heavily on startup frameworks built atop vulnerable OpenSSL distributions found themselves scrambling to rebuild entire infrastructures overnight.
IoT manufacturers faced unique challenges due to constrained update mechanisms and fragmented supply chains. Many smart home routers, connected thermostats, and industrial sensors continued operating with exploitable firmware months after patches became available. Researchers demonstrated wormable propagation vectors capable of self-replicating through mesh networks, raising concerns about cascading failures affecting critical infrastructure sectors.
Beyond immediate damage, CVE-2026-40198 catalyzed broader discussions around responsible disclosure timelines and open-source maintenance sustainability. Critics argued that OpenSSL’s rapid adoption of experimental QUIC features without adequate testing created unnecessary risks. Others pointed to the lack of formal bug bounty programs incentivizing proactive vulnerability hunting within core libraries.
Governments worldwide responded with renewed emphasis on software bill-of-materials (SBOM) tracking and mandatory reporting requirements for federally funded projects. Initiatives like the U.S. Executive Order on Cybersecurity now mandate dependency scanning and patch verification steps throughout procurement workflows, aiming to prevent recurrence of systemic exposures like CVE-2026-40198.
Key Insight: CVE-2026-40198 caused massive disruptions across commerce, finance, healthcare, and IoT ecosystems. Its exploitation highlights the need for continuous monitoring, rapid patch deployment, and improved coordination between vendors and defenders.
How Can You Detect and Mitigate CVE-2026-40198 in Your Infrastructure?
Detecting CVE-2026-40198 requires multi-layered approaches combining network telemetry, host-based inspection, and behavioral analytics. Traditional signature-based intrusion detection systems struggle with zero-day variants but still play roles in blocking known attack patterns once indicators emerge. More effective strategies involve leveraging AI-driven anomaly detection models trained on baseline traffic profiles to spot deviations indicative of exploitation attempts.
Network-level detection focuses on identifying malformed QUIC packets traversing ingress points. Signature rules matching oversized Token fields or invalid CID lengths help flag suspicious flows for deeper investigation. Tools like Zeek (formerly Bro) extend native protocol dissectors to extract granular metadata suitable for correlation engines. Sample Suricata rule detecting potential overflow attempts appears below:
yaml
alert udp any any -> $HOME_NET 443 (msg:"QUIC Token Overflow Attempt";
content:"|c0|"; depth:1; offset:0;
byte_test:8,>,1024,17,relative,little;
classtype:attempted-admin; sid:1000001; rev:1;)
Host-based assessments center around validating running OpenSSL versions and confirming absence of vulnerable symbols. Static analysis tools like Binwalk or Ghidra assist in unpacking proprietary binaries suspected of embedding outdated libraries. Dynamic instrumentation frameworks such as Frida enable runtime hooking of target functions to trace execution paths and capture heap allocations in real time.
Vulnerability scanners like Nessus or Qualys CloudView integrate CVE databases updated post-disclosure to scan assets continuously. Their reports highlight hosts presenting HTTP/3 interfaces backed by OpenSSL 3.2.0 installations, prioritizing remediation tasks accordingly. Automated remediation scripts orchestrated through configuration management platforms like Ansible or Chef facilitate bulk upgrades minimizing downtime windows.
Mitigation starts with upgrading OpenSSL to version 3.2.1 or later where applicable. Distribution-specific repositories usually lag upstream releases, necessitating manual compilation or third-party PPAs in some cases. Post-upgrade validation ensures replacement binaries correctly disable experimental QUIC features unless explicitly required.
Disabling QUIC altogether represents a viable stopgap measure pending full patch rollout. Most reverse proxy configurations allow toggling protocol preferences per virtual host or globally. NGINX directives exemplify disabling HTTP/3:
nginx server { listen 443 ssl http2; # Removed 'quic' directive ssl_protocols TLSv1.2 TLSv1.3; ... }
Firewall rules restricting UDP traffic to trusted sources limit exposure surface areas. Rate limiting policies enforced at edge routers throttle excessive connection attempts preventing brute-force style probing. Deep packet inspection appliances deployed inline inspect every packet header ensuring adherence to RFC-compliant formats before forwarding to backend servers.
Organizations adopting DevSecOps practices benefit from integrating static application security testing (SAST) tools directly into CI pipelines. Scanners like SonarQube or Checkmarx analyze source trees for insecure coding patterns associated with memory safety violations. Unit test suites augmented with property-based generators like Hypothesis exercise corner cases likely overlooked during manual reviews.
AI-enhanced platforms like mr7.ai streamline detection workflows by correlating disparate signals across logs, metrics, and traces. Specialized agents like mr7 Agent automate repetitive tasks such as version enumeration, patch verification, and rollback simulations—freeing human analysts to focus on strategic decision-making. With 10,000 free tokens available upon signup, teams can experiment with advanced threat modeling capabilities without upfront investment.
Key Insight: Effective CVE-2026-40198 mitigation combines network filtering, host validation, and automated patching. AI-assisted tools accelerate identification and remediation while reducing false positives compared to legacy signature methods.
What Steps Should Developers Take to Secure Applications Against This Vulnerability?
Developers bear responsibility for safeguarding applications reliant on OpenSSL’s QUIC implementation, especially during transitional phases between protocol drafts and stable standards. Proactive hardening measures minimize residual risks even after applying vendor patches, protecting against future regressions or undiscovered flaws lurking beneath surface layers.
Secure coding principles emphasize defense-in-depth strategies mitigating impact regardless of upstream component integrity. Input sanitization routines validate all externally sourced parameters against strict schemas defining acceptable ranges and formats. Libraries abstracting lower-level APIs should enforce encapsulation boundaries preventing accidental leakage of unsafe primitives upward.
Implementing robust error handling mechanisms guards against unexpected states arising from malformed inputs. Graceful degradation paths ensure partial functionality persists despite subsystem failures, preserving availability objectives outlined in SLA agreements. Logging frameworks capture sufficient detail for forensic reconstruction without compromising privacy expectations mandated by GDPR or CCPA regulations.
Unit testing plays pivotal role validating correctness properties under normal and adversarial conditions. Mock objects simulate hostile environments exercising failure modes difficult to reproduce organically. Property-based testing frameworks like QuickCheck or Hypothesis systematically explore edge cases violating assumptions encoded in business logic.
Continuous integration pipelines incorporating static analysis tools catch common mistakes early in development lifecycle. Linters configured to flag dangerous idioms related to pointer arithmetic or unchecked array accesses prevent subtle bugs slipping past peer review stages. Code coverage metrics quantify completeness of test suites guiding prioritization decisions during sprint planning sessions.
Dependency hygiene remains equally important given interconnectedness inherent in modern software supply chains. Regular audits compare declared dependencies against publicly disclosed vulnerabilities tracked in databases like NVD or GitHub Advisory Database. Dependency lock files pin exact revisions eliminating ambiguity around transitive imports pulled indirectly through nested modules.
Container image scanning solutions inspect filesystem contents searching for outdated components buried inside compressed archives. Policy enforcement hooks integrated into registry push workflows reject submissions violating predefined criteria ensuring consistency across staging and production tiers. Image signing keys rotated periodically mitigate compromise scenarios stemming from stolen credentials or insider threats.
Collaborative development environments foster knowledge sharing among team members promoting collective ownership culture around quality assurance goals. Pair programming sessions expose latent misunderstandings surrounding complex interactions between cryptographic primitives and networking stacks. Code walkthroughs facilitated by moderators encourage constructive feedback loops refining architectural choices iteratively.
Training programs equipping developers with foundational security literacy empower autonomous judgment calls balancing tradeoffs between performance optimizations and risk tolerance levels. Curriculum covering threat modeling methodologies teaches practitioners recognize attack surfaces unique to distributed systems operating at internet scale. Hands-on labs simulating real-world exploitation scenarios reinforce theoretical concepts grounding abstract ideas in tangible experiences.
Key Insight: Developers must adopt comprehensive security practices encompassing secure coding, thorough testing, vigilant dependency management, and ongoing education to protect applications from vulnerabilities like CVE-2026-40198 effectively.
Key Takeaways
- CVE-2026-40198 is a critical buffer overflow in OpenSSL's QUIC implementation enabling remote code execution and denial of service.
- Only OpenSSL 3.2.0 is affected; however, downstream integrations and custom builds may introduce additional exposure points.
- Exploitation involves crafting oversized QUIC packets to corrupt heap memory, followed by ROP chaining or heap spraying for reliable control.
- Real-world impacts include massive outages, data breaches, and regulatory scrutiny across multiple verticals including finance, healthcare, and IoT.
- Detection relies on network signatures, host inspections, and AI-enhanced correlation tools like those offered by mr7.ai and mr7 Agent.
- Mitigation encompasses patching, protocol disabling, firewall restrictions, and DevSecOps automation ensuring continuous validation.
- Developers should embrace secure coding practices, rigorous testing, and dependency hygiene to minimize residual risks from cryptographic library flaws.
Frequently Asked Questions
Q: How do I know if my server uses vulnerable OpenSSL with QUIC enabled?
To determine if your server uses a vulnerable OpenSSL version with QUIC enabled, execute openssl version -a and look for the -DOPENSSL_ENABLE_QUIC flag in the output. Additionally, confirm that the version number matches 3.2.0, which is the only affected release.
Q: Can CVE-2026-40198 be exploited over IPv6 networks?
Yes, CVE-2026-40198 affects both IPv4 and IPv6 networks since the vulnerability lies in the QUIC packet parsing logic, which operates independently of IP addressing schemes. Ensure IPv6 endpoints are included in your scanning scope.
Q: Is there a Metasploit module available for CVE-2026-40198?
As of April 2026, no official Metasploit module exists for CVE-2026-40198. However, community-developed PoCs and auxiliary scanners are available through GitHub repositories and exploit marketplaces. Always verify authenticity and legality before usage.
Q: Does disabling HTTP/3 completely eliminate the risk posed by this vulnerability?
Disabling HTTP/3 eliminates direct exposure to CVE-2026-40198 since the flaw resides specifically within the QUIC transport handler. However, other attack vectors unrelated to HTTP/3 may still exist depending on overall system architecture and configuration settings.
Q: How can I use mr7.ai tools to assess my environment for CVE-2026-40198?
You can utilize mr7.ai Chat to query specific aspects of CVE-2026-40198 and receive expert guidance. For automated scanning and exploitation simulation, deploy mr7 Agent on your local machine. New users receive 10,000 free tokens to explore these capabilities immediately.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.