Collaboration Platform API Abuse Attacks: Stealthy Backdoors
Collaboration Platform API Abuse Attacks: Stealthy Backdoors in Enterprise Communication
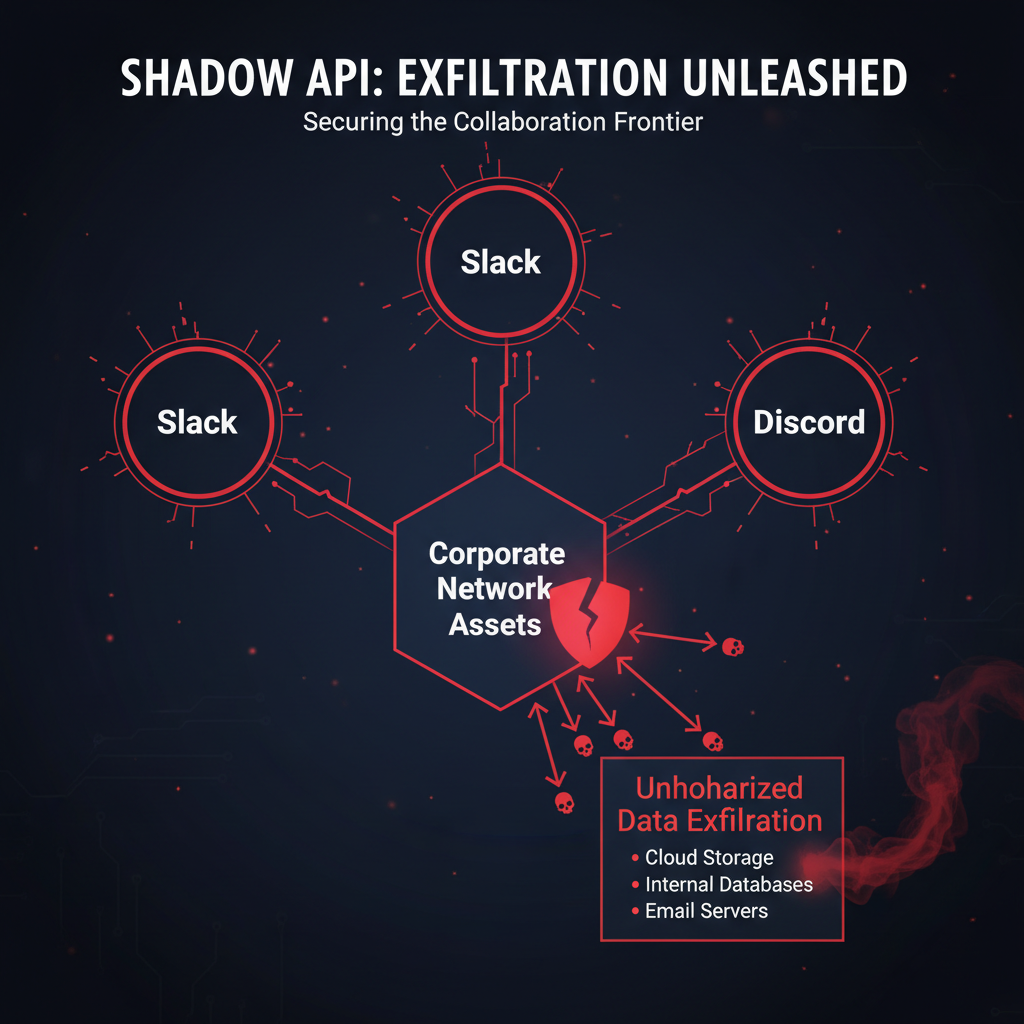
In today's interconnected digital landscape, collaboration platforms like Slack, Microsoft Teams, and Discord have become the backbone of enterprise communication. However, this widespread adoption has also made them prime targets for sophisticated cyberattacks. In Q1 2026 alone, security incidents involving unauthorized API access to these business communication platforms surged by an alarming 340%, with attackers increasingly leveraging legitimate business workflows to establish persistent backdoors within enterprise environments.
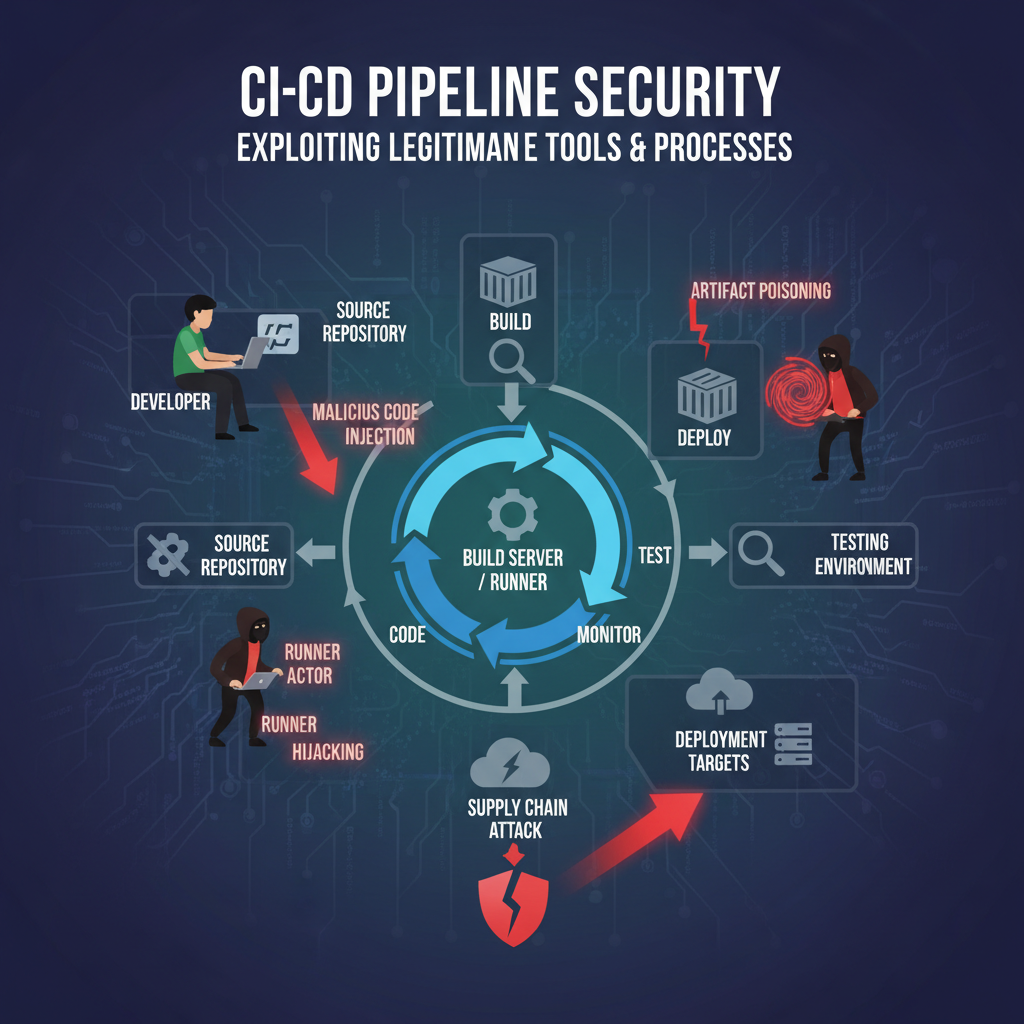
These modern attack vectors represent a significant evolution in threat actor tactics, moving beyond traditional network-based intrusions to exploit the very tools organizations rely on for daily operations. Attackers are now manipulating webhook configurations, creating malicious bots, abusing file storage capabilities, and intercepting sensitive communications through compromised API integrations. These techniques allow them to maintain long-term access while remaining virtually undetectable within the normal flow of business activities.
Understanding these emerging threats requires deep technical knowledge of platform-specific APIs, authentication mechanisms, and potential abuse patterns. Security teams must evolve their defensive strategies to detect anomalous API behaviors, implement robust monitoring frameworks, and develop incident response procedures tailored to these unique attack scenarios. This comprehensive guide explores the latest techniques used by threat actors, provides real-world incident examples from 2026 breaches, and offers detailed mitigation procedures for security professionals.
Throughout this article, we'll examine specific API abuse patterns, demonstrate detection methodologies, analyze forensic artifacts, and present defensive hardening measures that can significantly reduce organizational risk exposure. Additionally, we'll showcase how advanced AI-powered tools like those available through mr7.ai can enhance security research capabilities and accelerate incident response workflows.
How Are Attackers Exploiting Collaboration Platform APIs for Persistent Access?
Modern collaboration platforms offer extensive API capabilities designed to facilitate seamless integration with third-party applications and services. While these features enhance productivity, they also introduce significant security risks when misused by threat actors seeking persistent access to enterprise environments. Understanding the specific exploitation techniques is crucial for developing effective defensive strategies.
Webhook Manipulation Techniques
Webhooks serve as automated communication channels between applications, allowing real-time data exchange without continuous polling. Attackers frequently target webhook endpoints to create persistent backdoors that can exfiltrate data or execute commands remotely. In a notable 2026 incident affecting a financial services firm, attackers gained initial access through a compromised employee account and subsequently created malicious webhooks in their Slack workspace.
bash
Example of malicious webhook creation via Slack API
POST /api/apps.manifest.create HTTP/1.1 Host: slack.com Authorization: Bearer xoxp-TOKEN Content-Type: application/json
{ "manifest": { "display_information": { "name": "Security Integration" }, "features": { "bot_user": { "display_name": "Security Bot", "always_online": true } }, "oauth_config": { "scopes": { "bot": [ "channels:read", "chat:write", "files:read", "incoming-webhook" ] } } } }
Once established, these webhooks can be configured to send sensitive information to attacker-controlled domains or trigger malicious actions based on specific keywords or events. Detection of such activities requires monitoring for unusual webhook creation patterns, unexpected outbound network connections, and anomalous data transfer volumes.
Bot Creation and Abuse Patterns
Collaboration platforms allow users to create custom bots with varying permission levels and capabilities. Threat actors exploit this functionality by creating seemingly legitimate bots that perform reconnaissance, data collection, and command execution tasks. A recent case study from March 2026 involved attackers who created multiple bots across different departments within a technology company's Microsoft Teams environment.
These bots were designed to mimic legitimate administrative tools, making them difficult to distinguish from authorized applications. They systematically collected user information, monitored channel conversations, and maintained persistent access through regular token refreshes. The bots operated under the guise of routine maintenance scripts, effectively evading standard security controls.
python
Python example of bot behavior simulation for security testing
import requests import time
def monitor_channels(team_id, access_token): headers = { 'Authorization': f'Bearer {access_token}', 'Content-Type': 'application/json' }
List channels in team
channels_url = f'https://graph.microsoft.com/v1.0/teams/{team_id}/channels'response = requests.get(channels_url, headers=headers)if response.status_code == 200: channels = response.json()['value'] for channel in channels: print(f"Monitoring channel: {channel['displayName']}") # Additional logic for message monitoring would go hereelse: print(f"Failed to retrieve channels: {response.status_code}")Usage example
monitor_channels('TEAM-ID-HERE', 'ACCESS-TOKEN-HERE')
Security teams should implement strict bot approval processes, regularly audit bot permissions, and monitor for unusual bot activity patterns that might indicate compromise or malicious intent.
File Storage Abuse Mechanisms
Collaboration platforms often provide substantial file storage capabilities, which attackers can abuse for data staging, malware distribution, or maintaining persistent access. In several documented cases from early 2026, threat actors uploaded encrypted payloads to shared drives and used scheduled messages or automated bots to download and execute these files at predetermined intervals.
This technique leverages the implicit trust placed in internal communication platforms, making it particularly effective for bypassing traditional network security controls. Files stored in these environments typically don't undergo the same scrutiny as external downloads, allowing malicious content to remain undetected for extended periods.
Organizations should implement comprehensive file scanning policies, restrict executable file uploads where possible, and establish baseline monitoring for unusual file access patterns that could indicate malicious activity.
Actionable Insight: Regularly audit webhook configurations, bot permissions, and file sharing settings to identify potential security gaps that could enable persistent access.
What Specific API Abuse Patterns Enable Covert Data Exfiltration?
Data exfiltration through collaboration platform APIs represents one of the most concerning aspects of modern cyber threats. Unlike traditional network-based data theft methods, these techniques leverage legitimate communication channels, making detection significantly more challenging. Understanding the specific patterns and mechanisms involved is essential for implementing effective defensive measures.
Message Interception and Monitoring
One of the most prevalent API abuse patterns involves unauthorized access to message content within collaboration platforms. Attackers achieve this by obtaining valid API tokens through various means, including phishing attacks, credential stuffing, or exploiting vulnerabilities in existing integrations. Once authenticated, they can systematically monitor conversations, extract sensitive information, and relay it to external systems.
A high-profile incident in February 2026 demonstrated how attackers used compromised OAuth tokens to continuously monitor private channels in a healthcare organization's Slack workspace. They specifically targeted discussions related to patient data, financial records, and strategic business plans, collecting vast amounts of confidential information over several months before detection.
javascript // Node.js example of message monitoring using Slack Events API const express = require('express'); const { createEventAdapter } = require('@slack/events-api');
const slackEvents = createEventAdapter(process.env.SLACK_SIGNING_SECRET); const app = express();
app.use('/slack/events', slackEvents.expressMiddleware());
slackEvents.on('message', (event) => { // Monitor for sensitive keywords const sensitiveKeywords = ['confidential', 'password', 'financial'];
if (sensitiveKeywords.some(keyword =>
event.text.toLowerCase().includes(keyword))) {
console.log(Sensitive content detected: ${event.text});
// Log or alert on suspicious content
}
});
app.listen(3000, () => { console.log('Server listening on port 3000'); });
Scheduled Message Manipulation
Collaboration platforms often support scheduled messaging features, allowing users to queue messages for future delivery. Attackers can abuse this functionality to create covert communication channels that activate at specific times, reducing the likelihood of immediate detection. By scheduling messages containing encoded commands or data exfiltration instructions, they can maintain control over compromised systems while appearing as normal business communications.
In a documented case from January 2026, attackers used scheduled messages in Discord servers to coordinate ransomware deployment across multiple victim networks. The messages contained base64-encoded payloads that were automatically executed by compromised systems at predetermined times, ensuring synchronized attacks that maximized impact and complicated response efforts.
Channel Membership Manipulation
Unauthorized modification of channel membership lists can facilitate data exfiltration by granting attackers access to previously restricted conversations. Through API manipulation, threat actors can add themselves or their controlled accounts to private channels, gaining visibility into sensitive discussions and documents shared within those spaces.
This technique becomes particularly dangerous when combined with other API abuse patterns, creating a multi-layered approach to information gathering that can remain undetected for extended periods. Organizations should implement strict access controls and regularly audit channel membership changes to identify potentially malicious modifications.
Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
File Sharing and Download Abuse
Collaboration platforms frequently allow users to share files both internally and externally through direct links or download mechanisms. Attackers can exploit these features to establish data staging areas or distribute malicious content. By uploading encrypted payloads or malicious documents, they create persistent access points that can be activated remotely.
Detection of such activities requires monitoring for unusual file upload patterns, excessive download activity from single accounts, and abnormal file type distributions that deviate from normal business practices.
Key Detection Strategy: Implement comprehensive logging and monitoring for all API interactions, focusing on message access, file operations, and membership changes that could indicate unauthorized data collection activities.
Which Forensic Artifacts Reveal Compromised Collaboration Platform Access?
Identifying and analyzing forensic artifacts left behind by attackers who have compromised collaboration platform access is critical for understanding the scope of an incident and preventing future breaches. These digital traces provide invaluable insights into attack methodologies, timeline reconstruction, and evidence required for legal proceedings or regulatory compliance reporting.
Authentication Token Artifacts
OAuth tokens and session cookies represent some of the most telling forensic indicators of unauthorized platform access. When examining system logs and browser artifacts, security investigators should look for unusual token generation events, multiple simultaneous sessions from geographically dispersed locations, and token usage patterns that deviate from normal user behavior.
In many 2026 breach investigations, forensic analysts discovered that attackers had obtained long-lived refresh tokens through social engineering campaigns or by compromising legitimate service accounts. These tokens allowed sustained access for months without requiring additional authentication, making them particularly dangerous for persistent compromise scenarios.
Browser forensics play a crucial role in identifying token-related artifacts. Local storage databases, cookie files, and browsing history entries can reveal unauthorized access attempts and provide timestamps for reconstructing attack timelines. Tools like SQLite browsers and memory analysis utilities are essential for extracting this information from compromised systems.
API Call Logging and Analysis
Most collaboration platforms maintain detailed logs of API interactions, including caller identification, requested resources, and response codes. These logs serve as primary forensic sources for investigating unauthorized access incidents. Security teams should focus on identifying anomalous API call patterns, such as unusually high request volumes, access to rarely-used endpoints, or calls made outside normal business hours.
A common finding in recent investigations involved attackers making repeated calls to user listing endpoints (users.list in Slack, users in Microsoft Graph API) to build comprehensive directories of potential targets. Subsequent targeted attacks against high-value individuals often followed these reconnaissance activities, highlighting the importance of detecting early-stage enumeration efforts.
// Example of suspicious API log entry { "timestamp": "2026-03-15T02:34:17Z", "user_agent": "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0)", "ip_address": "185.132.189.10", "endpoint": "/api/users.list", "method": "GET", "status_code": 200, "request_count": 47, "time_window_minutes": 5 }
Configuration Change Records
Unauthorized modifications to platform configurations, including webhook additions, bot creations, and permission adjustments, leave distinct forensic footprints. These changes often occur through administrative APIs that require elevated privileges, making them attractive targets for attackers who have compromised privileged accounts.
Forensic investigation should include examining configuration backup files, audit logs, and version histories to identify unauthorized modifications. Many platforms maintain detailed change logs that record who made specific changes, when they occurred, and what parameters were modified. Correlating these records with other forensic evidence helps build comprehensive incident timelines.
Network Traffic Analysis
While collaboration platforms primarily operate over encrypted HTTPS connections, network-level artifacts can still provide valuable forensic insights. DNS query logs may reveal connections to attacker-controlled domains, while firewall and proxy logs can show unusual traffic patterns or data exfiltration attempts.
Deep packet inspection tools can sometimes extract useful metadata from encrypted traffic, such as server names, connection timing, and data volume measurements. This information helps investigators understand the scope and scale of unauthorized platform access.
Forensic Best Practice: Maintain comprehensive logging for all platform API interactions and regularly archive these records for forensic analysis. Implement centralized log management solutions to ensure consistent collection and retention of relevant forensic data.
How Can Security Teams Detect and Prevent These Sophisticated API Attacks?
Preventing and detecting sophisticated API abuse attacks against collaboration platforms requires a multi-layered defensive approach that combines technical controls, monitoring capabilities, and proactive threat hunting methodologies. Modern security teams must move beyond traditional signature-based detection methods to embrace behavioral analytics and anomaly detection techniques.
Behavioral Analytics and Anomaly Detection
Implementing machine learning-based anomaly detection systems represents one of the most effective approaches for identifying suspicious API usage patterns. These systems learn normal usage behaviors and flag deviations that might indicate malicious activity. For collaboration platforms, normal behavior baselines should include typical message volumes, file sharing frequencies, bot interaction patterns, and user engagement metrics.
A successful implementation involves training detection models on historical data to establish baseline behaviors, then continuously monitoring for statistically significant deviations. Machine learning algorithms can identify subtle patterns that human analysts might miss, such as gradual increases in API call frequency or coordinated activities across multiple user accounts.
python
Example of anomaly detection algorithm for API call monitoring
import numpy as np from sklearn.ensemble import IsolationForest
class APIMonitor: def init(self): self.model = IsolationForest(contamination=0.1) self.training_data = []
def train(self, normal_behavior_data): """Train model on normal API usage patterns""" self.model.fit(normal_behavior_data)
def detect_anomalies(self, current_data): """Detect anomalous API usage patterns""" predictions = self.model.predict(current_data) anomalies = np.where(predictions == -1)[0] return anomaliesUsage example with sample data
monitor = APIMonitor()
Normal training data would include features like:
api_calls_per_hour, unique_endpoints_accessed, [blocked]
data_volume_transferred, active_users_count]
normal_data = [ [50, 15, 2.5, 200], [45, 12, 2.1, 180], [55, 18, 3.2, 220] ] monitor.train(normal_data)
Real-Time Alerting and Response
Effective detection requires real-time alerting capabilities that can notify security teams immediately when suspicious activities are detected. Alert fatigue remains a significant challenge, so alerts should be carefully tuned to minimize false positives while ensuring critical threats receive immediate attention.
Integration with Security Information and Event Management (SIEM) systems enables correlation of API abuse indicators with other security events, providing context that helps prioritize response efforts. Automated response capabilities, such as temporary account suspension or mandatory re-authentication requirements, can help contain threats while human analysts investigate further.
User Behavior Analytics (UBA)
User Behavior Analytics solutions specialize in detecting insider threats and compromised accounts by analyzing user activity patterns. For collaboration platforms, UBA systems should monitor for unusual working hours, geographic location inconsistencies, rapid switching between different applications or channels, and sudden changes in communication patterns.
Advanced UBA implementations can identify subtle behavioral changes that precede major security incidents. For example, a user who suddenly begins accessing channels they've never interacted with before, or starts downloading large numbers of files during off-hours, might be exhibiting signs of compromise that warrant investigation.
Continuous Platform Monitoring
Regular security assessments and continuous monitoring of collaboration platform configurations help prevent unauthorized access opportunities. This includes auditing installed applications, reviewing permission scopes, verifying webhook destinations, and ensuring proper access controls are in place.
Automated scanning tools can help identify misconfigurations and potential security gaps, but manual review by experienced security professionals remains essential for detecting sophisticated threats that might evade automated detection systems.
Defensive Recommendation: Deploy comprehensive behavioral analytics solutions that can detect anomalous API usage patterns and integrate with existing security infrastructure to enable rapid incident response.
What Are the Most Effective Hardening Measures Against Platform API Abuse?
Hardening collaboration platforms against API abuse requires implementing robust security controls across multiple layers, from authentication mechanisms to application-level restrictions. Organizations must adopt a defense-in-depth approach that addresses both technical vulnerabilities and operational security weaknesses.
Authentication and Authorization Controls
Implementing strong authentication mechanisms represents the foundation of effective API security. Multi-factor authentication (MFA) should be mandatory for all accounts with API access capabilities, particularly administrative and service accounts. Time-based one-time passwords (TOTP) or hardware security keys provide significantly stronger protection than SMS-based MFA, which remains vulnerable to SIM swapping attacks.
Role-based access control (RBAC) ensures that users and applications only have access to the minimum resources necessary for their functions. Regular reviews of permission assignments help identify and remove unnecessary access rights that could be exploited by attackers. Principle of least privilege should extend to bot and integration permissions, limiting their capabilities to only what's absolutely required.
yaml
Example IAM policy for restricting Slack bot permissions
Version: "2012-10-17" Statement:
- Effect: Allow
Action:
- "slack:channels:read"
- "slack:chat:write:bot"
- "slack:users:read"
Resource: "*"
- Effect: Deny
Action:
- "slack:admin.*"
- "slack:files:write:user" Resource: ""
- Effect: Deny
Action:
Application and Integration Security
Third-party applications and custom integrations represent common attack vectors for API abuse. Organizations should implement strict application vetting processes that include security reviews, code analysis, and permission audits before allowing new integrations. Regular re-evaluation of existing applications ensures that security standards remain current and that deprecated or unused applications are removed promptly.
Application whitelisting can prevent unauthorized integrations from being installed, while granular permission controls limit what approved applications can access. Many platforms now offer granular OAuth scopes that allow fine-tuned control over application capabilities, reducing the potential impact of compromised integrations.
Network-Level Protections
Network segmentation and firewall rules can help contain API abuse incidents by limiting where compromised accounts can communicate. Restricting outbound connections from collaboration platform environments to known good destinations reduces the effectiveness of data exfiltration attempts.
API rate limiting prevents attackers from overwhelming systems with excessive requests, while geographic filtering can block access from high-risk regions. These controls work together to create multiple barriers that attackers must overcome to successfully exploit platform vulnerabilities.
Logging and Audit Capabilities
Comprehensive logging serves both preventive and detective functions in API security. Detailed audit trails enable rapid incident response and provide evidence for forensic investigations. Logs should capture authentication events, API calls, configuration changes, and data access activities with sufficient detail to support security analysis.
Centralized log management systems ensure that security-relevant events are preserved and searchable, while automated alerting mechanisms notify teams of potentially malicious activities. Regular log reviews help identify trends and emerging threats that might require updated defensive measures.
Hardening Priority: Focus initial hardening efforts on strengthening authentication controls, implementing principle of least privilege for all accounts and applications, and enabling comprehensive logging for security analysis.
Which Real Incident Examples Demonstrate These Attack Vectors in Action?
Real-world incident examples provide concrete illustrations of how collaboration platform API abuse techniques manifest in actual attacks. These case studies highlight the sophistication of modern threat actors and demonstrate the importance of proactive defensive measures.
Financial Services Breach (January 2026)
A major financial institution suffered a significant data breach in January 2026 when attackers exploited a compromised service account to gain persistent access to their Microsoft Teams environment. Initial access was achieved through a targeted phishing campaign that successfully captured credentials from a privileged user responsible for managing third-party integrations.
Once inside the environment, attackers created multiple custom bots with extensive permissions, including the ability to read private channel messages, access file shares, and monitor user presence information. These bots operated for over three months before detection, systematically collecting sensitive financial documents, customer communications, and internal strategic plans.
The attack was eventually discovered when network monitoring systems flagged unusual outbound data transfers to domains registered shortly before the incident. Forensic analysis revealed that attackers had established multiple redundant access paths, including webhook endpoints and scheduled message triggers, ensuring continued access even if individual components were discovered and disabled.
Healthcare Organization Compromise (February 2026)
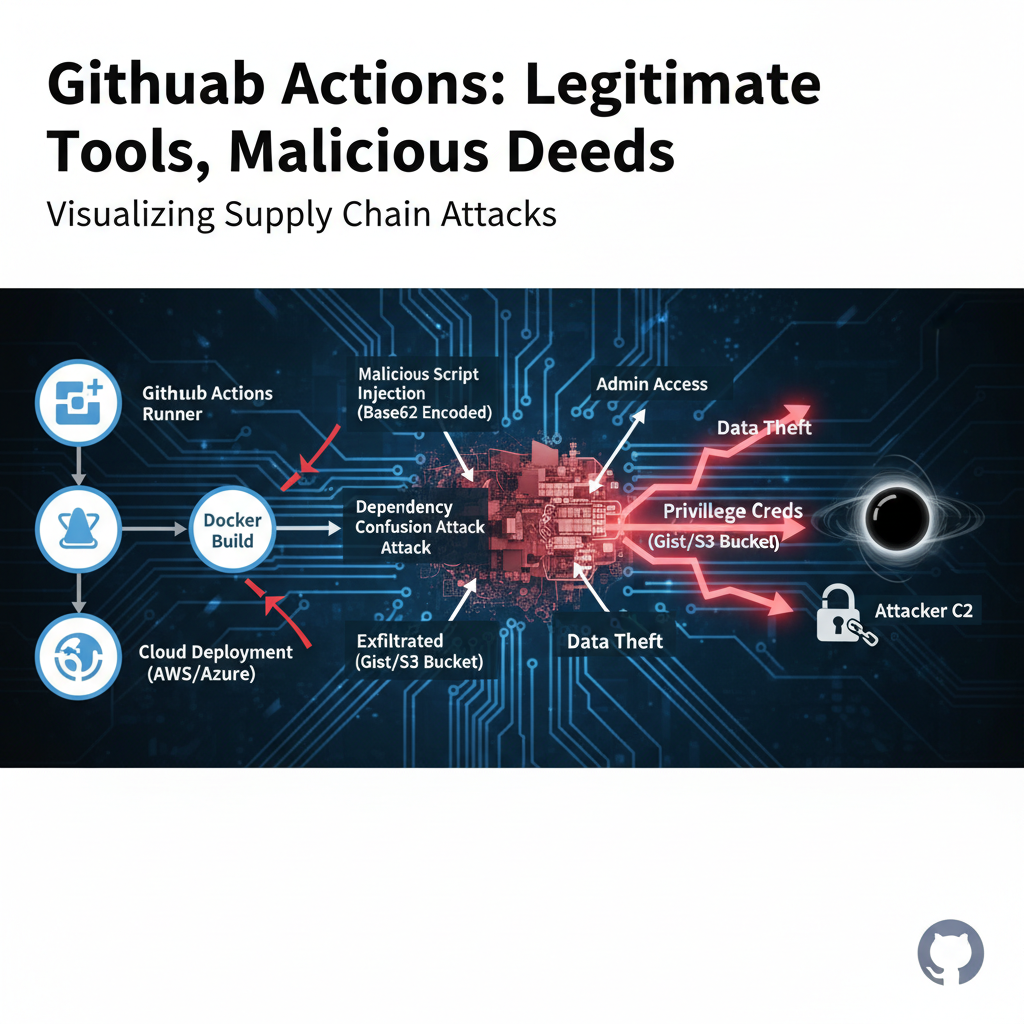
A regional healthcare provider experienced a targeted attack in February 2026 that leveraged Slack API vulnerabilities to access protected health information (PHI). Attackers initially gained access through a supply chain compromise affecting a popular Slack integration used for appointment scheduling.
The malicious integration had been modified to include hidden API calls that collected user information and channel content, storing the data in encrypted form within the platform's file storage system. Attackers then used legitimate file sharing features to gradually exfiltrate the collected information to external storage services.
Detection occurred when automated security tools identified unusual file access patterns and correlated them with anomalous API call sequences. The investigation revealed that attackers had carefully timed their activities to coincide with normal business operations, making their presence difficult to distinguish from legitimate user behavior.
Technology Company Supply Chain Attack (March 2026)
A software development company fell victim to a sophisticated supply chain attack in March 2026 that compromised their Discord server infrastructure. Attackers gained initial access by compromising a vendor's Discord bot development environment and injecting malicious code into legitimate applications.
The compromised bots were distributed through official channels and appeared to function normally, but included hidden capabilities for monitoring private conversations, collecting source code snippets, and establishing command and control communications. The attack affected multiple organizations simultaneously, demonstrating the cascading effects of third-party compromises.
Discovery occurred when one of the affected companies noticed unusual bot behavior during routine security testing. Collaborative investigation with other victims and the vendor revealed the full scope of the compromise, leading to coordinated remediation efforts across the affected organizations.
| Attack Vector | Primary Platform | Discovery Method | Impact Duration |
|---|---|---|---|
| Service Account Compromise | Microsoft Teams | Network Monitoring | 3+ months |
| Integration Supply Chain | Slack | Automated Detection | 2+ months |
| Third-Party Bot Compromise | Discord | Security Testing | 4+ weeks |
Incident Response Lesson: Comprehensive monitoring and rapid incident response capabilities are essential for minimizing damage from collaboration platform API abuse attacks. Early detection significantly reduces potential impact and recovery costs.
What Step-by-Step Mitigation Procedures Should Security Teams Follow?
Responding effectively to collaboration platform API abuse incidents requires systematic procedures that address immediate containment needs while preserving evidence for forensic analysis. These step-by-step mitigation procedures ensure comprehensive incident handling and reduce the risk of recurrence.
Immediate Containment Actions
Upon detecting suspected API abuse, security teams should immediately initiate containment procedures to prevent further damage. This includes revoking compromised credentials, disabling suspicious applications, and blocking malicious network connections. Speed is critical in these initial steps, as delays can allow attackers to expand their access or destroy evidence.
bash
Example containment script for Slack environment
#!/bin/bash
Revoke specific bot token
curl -X POST https://slack.com/api/auth.revoke
-H "Authorization: Bearer xoxb-COMPROMISED-TOKEN"
-d "test=true"
Disable suspicious app
APP_ID="A012AB3CD4E"
curl -X POST "https://slack.com/api/apps.permissions.resources.list?app_id=${APP_ID}"
-H "Authorization: Bearer xoxp-ADMIN-TOKEN"
Block malicious domain
iptables -A OUTPUT -d malicious-domain.com -j DROP
Documentation of all containment actions is essential for legal and regulatory purposes. Teams should maintain detailed logs of revoked tokens, disabled applications, and blocked connections, including timestamps and responsible personnel information.
Evidence Preservation and Collection
Preserving digital evidence requires careful coordination to avoid destroying volatile data while ensuring comprehensive collection. Memory dumps, network captures, and system logs should be collected immediately, as they may contain critical forensic artifacts that disappear quickly after system restarts or network disruptions.
Platform-specific evidence collection procedures should follow established forensic guidelines. For cloud-based collaboration platforms, this often involves working with vendor support teams to obtain detailed audit logs and API call records that might not be readily accessible through standard interfaces.
Chain of custody documentation ensures that evidence remains admissible in legal proceedings. All collected materials should be properly labeled, secured, and handled according to established protocols to maintain their integrity throughout the investigation process.
Root Cause Analysis and Remediation
Identifying the root cause of an API abuse incident requires thorough investigation of initial compromise vectors, lateral movement techniques, and persistence mechanisms. This analysis informs remediation efforts and helps prevent similar incidents from occurring in the future.
Remediation should address both technical vulnerabilities and procedural weaknesses that contributed to the incident. This might include implementing additional security controls, updating policies and procedures, and providing additional training to staff members who were involved in the compromise.
Post-incident reviews should evaluate the effectiveness of existing security measures and identify areas for improvement. Lessons learned documentation helps ensure that valuable insights from the incident are incorporated into future security planning and incident response procedures.
Long-term Prevention Implementation
Long-term prevention requires implementing comprehensive security improvements based on incident findings. This includes updating security architectures, enhancing monitoring capabilities, and strengthening access controls to address identified vulnerabilities.
Regular security assessments and penetration testing help validate that implemented controls are effective and identify new potential vulnerabilities. Continuous improvement processes ensure that security measures evolve to address emerging threats and changing business requirements.
Staff training and awareness programs help prevent future incidents by educating users about common attack techniques and appropriate security practices. Regular updates and refresher training ensure that security knowledge remains current and relevant to evolving threat landscapes.
Response Framework: Establish clear incident response procedures that include immediate containment, evidence preservation, root cause analysis, and long-term prevention measures to effectively handle collaboration platform API abuse incidents.
Key Takeaways
• Webhook manipulation and bot creation represent primary attack vectors for establishing persistent backdoors in collaboration platforms • Message interception and file storage abuse enable covert data exfiltration through legitimate communication channels • Forensic artifacts including authentication tokens, API logs, and configuration changes provide critical evidence for incident investigation • Behavioral analytics and anomaly detection systems are essential for identifying sophisticated API abuse patterns in real-time • Strong authentication controls, principle of least privilege, and comprehensive logging form the foundation of effective platform hardening • Real incident examples demonstrate the sophistication and persistence of modern collaboration platform API abuse attacks • Systematic mitigation procedures including immediate containment, evidence preservation, and root cause analysis ensure effective incident response
Frequently Asked Questions
Q: How do attackers typically gain initial access to collaboration platform APIs?
Attackers commonly use phishing campaigns to steal user credentials, exploit vulnerabilities in third-party integrations, or compromise service accounts with excessive permissions. Social engineering techniques targeting privileged users who manage platform configurations are also frequently successful.
Q: What are the most common indicators of compromise for API abuse attacks?
The most reliable indicators include unusual API call volumes, access to rarely-used endpoints, authentication from unfamiliar IP addresses or geographic locations, and anomalous data transfer patterns. Monitoring for these behaviors requires comprehensive logging and behavioral analytics capabilities.
Q: How can organizations prevent unauthorized bot creation and webhook manipulation?
Organizations should implement strict application approval processes, enable granular permission controls for integrations, regularly audit installed applications and webhooks, and enforce multi-factor authentication for all accounts with administrative privileges. Automated monitoring for suspicious configuration changes is also essential.
Q: What forensic evidence should security teams collect during collaboration platform incident investigations?
Critical forensic evidence includes authentication logs, API call records, configuration change histories, network traffic captures, and browser artifacts from compromised accounts. Platform vendors often maintain additional forensic data that may require special requests to access.
Q: How does mr7 Agent help security teams defend against collaboration platform API abuse?
mr7 Agent automates security testing workflows, performs continuous monitoring for suspicious API behaviors, and provides AI-powered analysis of potential threats. Its local deployment ensures sensitive data remains secure while enabling comprehensive security assessment capabilities.
Supercharge Your Security Workflow
Professional security researchers trust mr7.ai for AI-powered code analysis, vulnerability research, dark web intelligence, and automated security testing with mr7 Agent.