tutorialsedr-bypasskernel-securitymalware-analysis
EDR Bypass Kernel Object Manipulation: Advanced Adversary Techniques
April 27, 202620 min read1 views
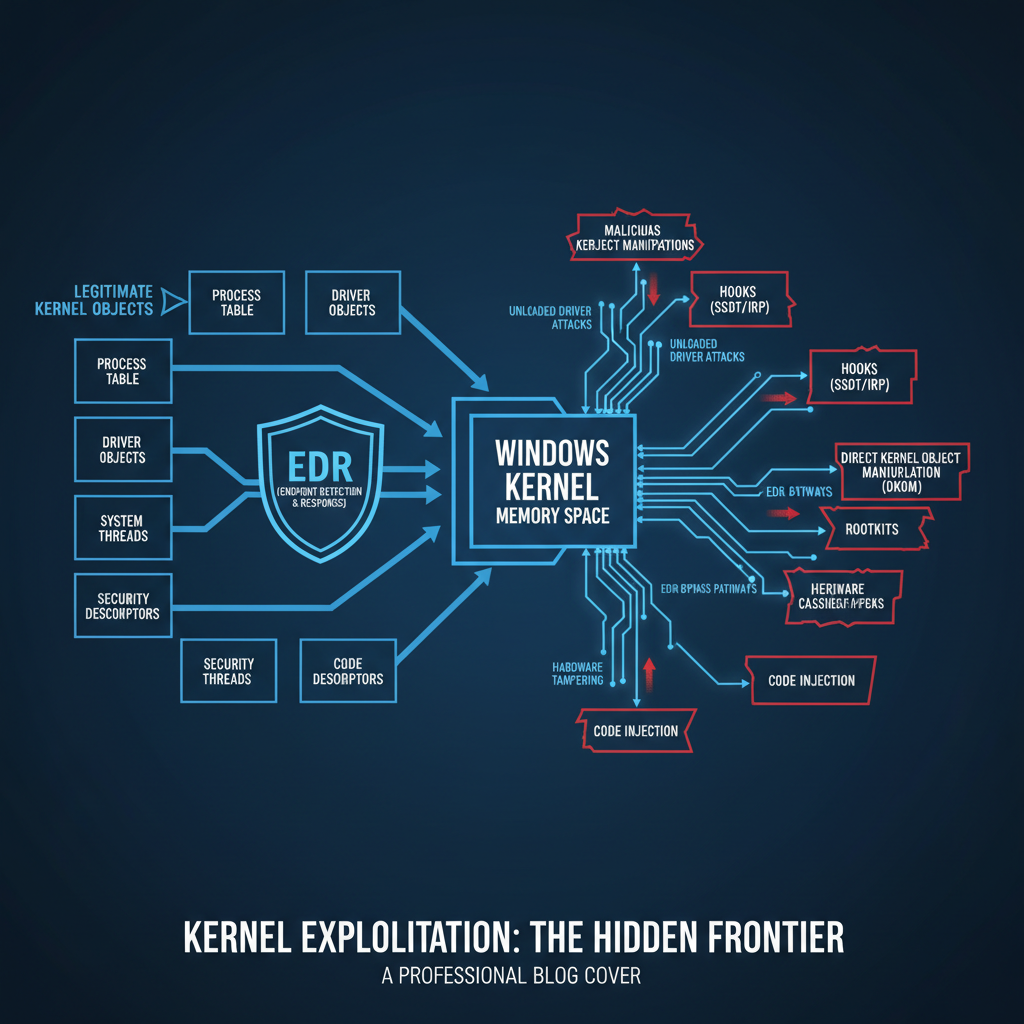
Table of Contents
Master advanced browser based persistence techniques using service workers, IndexedDB, and WASM. Learn evasion methods and detection signatures. Try mr7.ai free.

Learn advanced techniques for detecting FPGA-based network implants using JTAG interface analysis. Hands-on guide with real tools and methods.
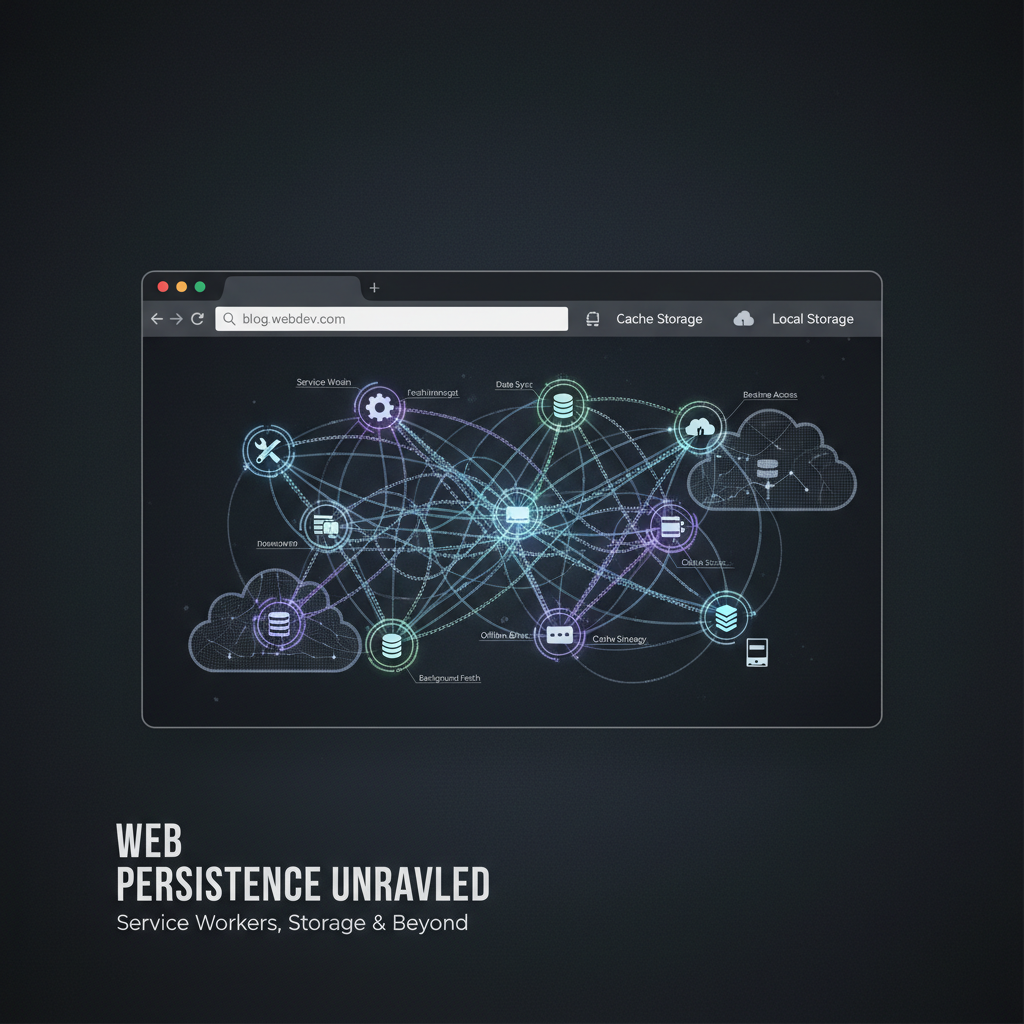
Master EDR bypass syscalls with direct system calls, stack spoofing, and ETW patching. Learn modern evasion techniques and try mr7.ai free.