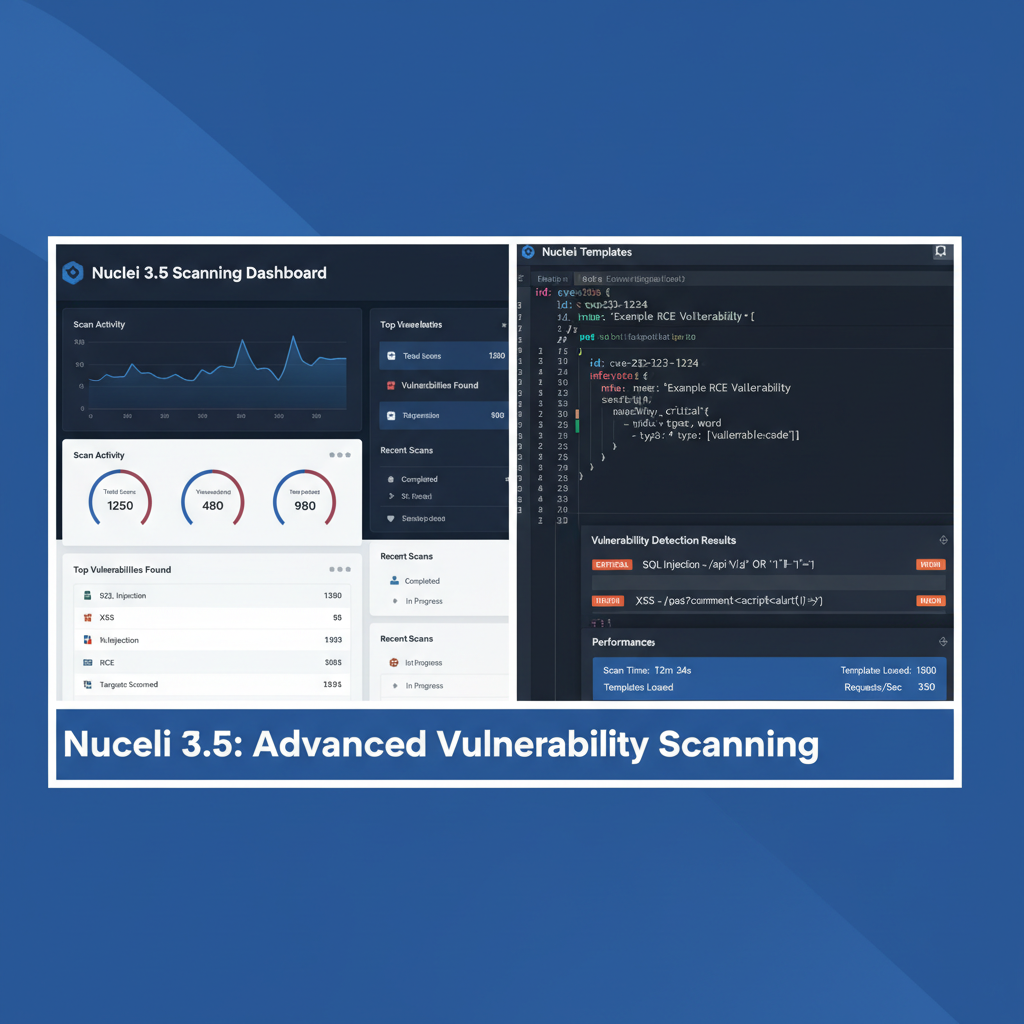
CrackMapExec 6.0 Active Directory Pentesting: Complete Review
CrackMapExec 6.0 Active Directory Pentesting: A Comprehensive Hands-On Review
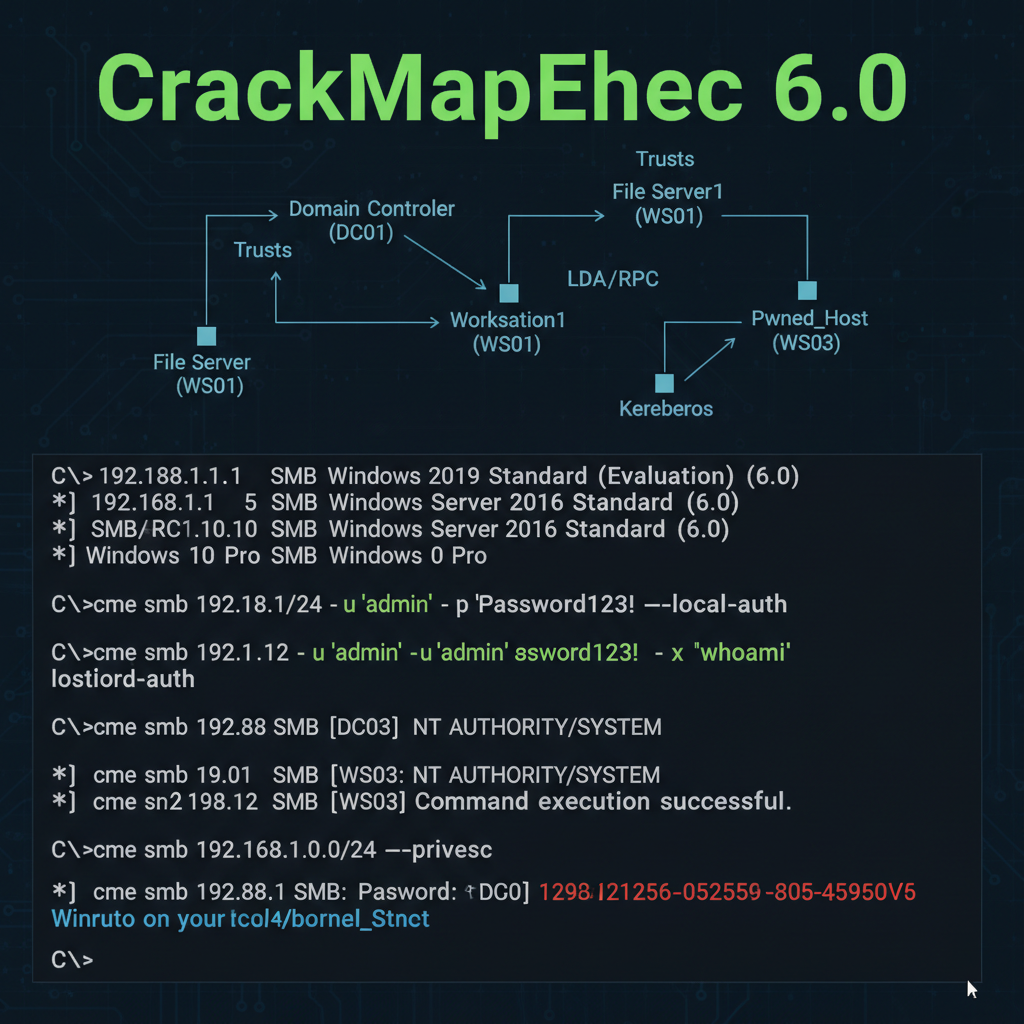
Active Directory (AD) remains one of the most critical attack surfaces in enterprise environments. As organizations adopt hybrid cloud architectures and modern authentication protocols, red teams and penetration testers need sophisticated tools to keep pace. CrackMapExec 6.0 emerges as a powerful solution, introducing groundbreaking features such as Kerberos relay capabilities, enhanced LDAP abuse modules, and seamless integration with modern authentication protocols.
This comprehensive guide provides a detailed hands-on review of CrackMapExec 6.0's new features. We'll explore practical examples of lateral movement, privilege escalation, and data exfiltration techniques. Through real-world scenarios and command-line demonstrations, we'll showcase how these enhancements improve efficiency and effectiveness in modern AD environments. Additionally, we'll compare performance metrics and new attack modules against previous versions to highlight the evolution of this essential penetration testing toolkit.
Whether you're a seasoned red teamer or an aspiring ethical hacker, understanding CrackMapExec 6.0's capabilities is crucial for staying ahead in the ever-evolving landscape of AD security. Throughout this article, we'll also demonstrate how mr7.ai's AI-powered tools can enhance your penetration testing workflow, providing intelligent assistance and automation capabilities that complement CrackMapExec's functionality.
What Makes CrackMapExec 6.0 a Game-Changer for Modern AD Environments?
CrackMapExec 6.0 represents a significant leap forward in Active Directory penetration testing capabilities. The latest version addresses the evolving complexity of modern enterprise networks, particularly those incorporating hybrid cloud infrastructures and advanced authentication mechanisms. Understanding these enhancements is crucial for security professionals aiming to maintain effective assessment methodologies.
One of the most notable improvements in CrackMapExec 6.0 is its enhanced compatibility with modern authentication protocols. Traditional NTLM-based attacks are becoming less effective as organizations implement stronger security measures. Version 6.0 introduces robust support for Kerberos authentication, including advanced relay capabilities that enable more sophisticated attack vectors. This shift reflects the changing threat landscape where attackers must adapt to more secure authentication methods.
The updated LDAP abuse modules in CrackMapExec 6.0 provide unprecedented access to directory information and manipulation capabilities. These enhancements allow security researchers to extract sensitive information, modify directory objects, and identify potential privilege escalation paths more efficiently than ever before. The improved LDAP handling also includes better error management and more granular control over query parameters.
Performance optimizations in CrackMapExec 6.0 are immediately noticeable. The tool now handles large-scale domain enumeration with significantly reduced execution times, making it more practical for assessing extensive enterprise environments. Memory usage has been optimized, and the modular architecture allows for better parallel processing of multiple targets simultaneously.
Integration with cloud services represents another crucial advancement. CrackMapExec 6.0 includes native support for Azure AD hybrid environments, enabling security professionals to assess the security posture of organizations with mixed on-premises and cloud infrastructure. This capability is increasingly important as more enterprises adopt hybrid cloud strategies.
bash
Example: Basic CrackMapExec 6.0 enumeration
Enumerate domain information with verbose output
sudo crackmapexec smb 192.168.1.0/24 -u 'Administrator' -p 'Password123' --shares --sessions --loggedon-users
Check for SMB signing status across network
sudo crackmapexec smb 192.168.1.0/24 --gen-relay-list targets.txt
The modular design of CrackMapExec 6.0 allows for easy extension and customization. New modules can be developed and integrated seamlessly, ensuring the tool remains relevant as attack techniques evolve. This extensibility makes it an invaluable asset for red teams that require tailored solutions for specific engagement requirements.
Key Insight: CrackMapExec 6.0's architectural improvements and enhanced protocol support make it indispensable for modern AD penetration testing, particularly in complex hybrid environments.
How Does Kerberos Relay Capability Transform Lateral Movement Techniques?
Kerberos relay capability in CrackMapExec 6.0 introduces revolutionary possibilities for lateral movement within Active Directory environments. This feature fundamentally changes how security professionals approach network traversal, offering more stealthy and effective methods compared to traditional techniques like SMB relay attacks.
The core principle behind Kerberos relay involves intercepting and manipulating Kerberos authentication traffic between clients and domain controllers. Unlike SMB relay, which relies on capturing NTLM hashes, Kerberos relay targets the encrypted tickets that form the backbone of modern Windows authentication. This approach is significantly more challenging for defenders to detect and mitigate.
Implementation of Kerberos relay in CrackMapExec 6.0 requires careful setup and understanding of the underlying protocol mechanics. The tool provides built-in modules that handle much of the complexity, but successful deployment still demands thorough knowledge of Kerberos operations and network positioning.
python
Example Python script demonstrating Kerberos ticket manipulation
This represents the type of low-level interaction CrackMapExec handles
from impacket.krb5 import constants from impacket.krb5.types import Principal
Create a Kerberos principal for target service
service_principal = Principal('cifs/dc01.example.com', type=constants.PrincipalNameType.NT_SRV_INST.value)
Request TGT using obtained credentials
tgt, cipher, session_key = getKerberosTGT(client_name, password, domain, lmhash, nthash, aesKey, kdcHost)
Use TGT to request service ticket
service_ticket = getKerberosTGS(service_principal, domain, kdcHost, tgt, cipher, session_key)
Practical applications of Kerberos relay extend beyond simple credential theft. Security professionals can leverage this capability to perform targeted attacks against high-value systems, impersonate privileged users, and maintain persistent access without triggering traditional alerting mechanisms. The technique is particularly effective in environments where SMB signing is enforced, rendering conventional relay attacks ineffective.
Configuration of Kerberos relay requires precise timing and network positioning. Attackers must position themselves strategically within the network topology to intercept authentication traffic effectively. CrackMapExec 6.0 simplifies this process by providing automated discovery mechanisms and intelligent relay selection based on network conditions.
The implications for defensive strategies are profound. Organizations must implement more sophisticated monitoring solutions that can detect anomalous Kerberos traffic patterns. Traditional signature-based detection methods prove insufficient against the nuanced behaviors exhibited by Kerberos relay attacks.
bash
CrackMapExec 6.0 Kerberos relay example
Start Kerberos relay listener
sudo crackmapexec krb5relay -t 192.168.1.100 -l 88 --no-dump --no-da --no-local-auth
Trigger authentication from target machine
This would typically involve social engineering or exploiting vulnerabilities
Advanced configurations allow for chaining multiple relay operations, creating complex attack chains that can traverse entire network segments undetected. This capability enables red teams to simulate sophisticated adversary behaviors that mirror real-world threat actor tactics.
Key Insight: Kerberos relay transforms lateral movement by enabling stealthy, encrypted authentication manipulation that bypasses traditional detection mechanisms while maintaining persistence across enterprise networks.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
What Are the Enhanced LDAP Abuse Modules and Their Practical Applications?
The enhanced LDAP abuse modules in CrackMapExec 6.0 represent a significant advancement in directory service exploitation capabilities. These modules provide security professionals with sophisticated tools for extracting sensitive information, identifying privilege escalation opportunities, and mapping complex organizational structures within Active Directory environments.
LDAP (Lightweight Directory Access Protocol) serves as the foundation for Active Directory's directory services, storing critical information about users, groups, computers, and security policies. The enhanced modules in CrackMapExec 6.0 offer granular control over LDAP queries, allowing for targeted extraction of specific attributes and relationships that might indicate security weaknesses.
One of the most powerful aspects of these enhanced modules is their ability to perform recursive group membership enumeration. Traditional tools often struggle with deeply nested group structures, but CrackMapExec 6.0 efficiently traverses these hierarchies to identify indirect administrative privileges and unexpected access paths.
bash
Enhanced LDAP enumeration with CrackMapExec 6.0
Extract detailed user information with custom filters
sudo crackmapexec ldap 192.168.1.10 -u 'pentester' -p 'SecurePass123' --users --enabled --attributes sAMAccountName,pwdLastSet,lastLogon
Enumerate group memberships recursively
sudo crackmapexec ldap 192.168.1.10 -u 'pentester' -p 'SecurePass123' --groups --nesting
Search for accounts with specific attributes
sudo crackmapexec ldap 192.168.1.10 -u 'pentester' -p 'SecurePass123' --query "(&(objectCategory=person)(userAccountControl:1.2.840.113556.1.4.803:=65536))" --attributes sAMAccountName,userAccountControl
The modules also include advanced filtering capabilities that enable security professionals to identify accounts with weak security configurations. For instance, finding accounts with passwords that never expire, accounts with delegation privileges, or service accounts with elevated permissions becomes straightforward with the enhanced LDAP functionality.
Custom attribute extraction represents another significant improvement. Security professionals can specify exactly which LDAP attributes to retrieve, reducing bandwidth usage and focusing on relevant information. This precision is particularly valuable when dealing with large directories where excessive data transfer could trigger network monitoring alerts.
Privilege escalation identification has been streamlined through enhanced relationship mapping. The modules can automatically identify potential escalation paths by analyzing group memberships, ACL relationships, and delegation configurations. This automated analysis saves considerable time during reconnaissance phases.
python
Example LDAP query structure used internally by CrackMapExec
This demonstrates the level of control available
ldap_query = { 'base_dn': 'DC=example,DC=com', 'search_filter': '(&(objectClass=user)(!(userAccountControl:1.2.840.113556.1.4.803:=2)))', 'attributes': ['sAMAccountName', 'memberOf', 'pwdLastSet', 'lastLogon'], 'scope': 'SUBTREE', 'size_limit': 1000 }
The enhanced modules also support bulk operations and parallel processing, significantly improving performance when enumerating large directories. This optimization ensures that comprehensive assessments remain practical even in enterprise-scale environments with tens of thousands of objects.
Integration with other CrackMapExec modules creates powerful combined attack chains. For example, LDAP enumeration results can feed directly into targeted credential spraying campaigns or inform Kerberos relay positioning strategies.
Key Insight: Enhanced LDAP abuse modules provide unprecedented visibility into Active Directory structures, enabling efficient identification of privilege escalation opportunities and security misconfigurations through sophisticated querying and relationship mapping.
How Has Integration with Modern Authentication Protocols Improved Security Assessments?
Modern authentication protocols present both challenges and opportunities for security professionals conducting Active Directory assessments. CrackMapExec 6.0's enhanced integration with these protocols significantly improves the tool's effectiveness in contemporary enterprise environments where legacy authentication methods are being phased out.
OAuth 2.0 and OpenID Connect integration represents a major advancement in CrackMapExec 6.0's capabilities. These protocols are increasingly common in hybrid cloud environments where organizations utilize Microsoft 365 alongside on-premises Active Directory. The enhanced support allows security professionals to test authentication flows and identify potential misconfigurations in cloud service integrations.
bash
Modern authentication testing with CrackMapExec 6.0
Test OAuth 2.0 token acquisition and validation
sudo crackmapexec oauth2 --client-id 'app_client_id' --client-secret 'secret_key' --tenant-id 'tenant_guid' --scope 'https://graph.microsoft.com/.default'
Validate JWT tokens against Azure AD endpoints
sudo crackmapexec jwt --token 'eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9...' --validate --introspect
Test SAML assertion handling
sudo crackmapexec saml --assertion-file assertion.xml --validate-signature --check-audience
Multi-factor authentication (MFA) bypass techniques have evolved significantly in CrackMapExec 6.0. While direct MFA bypass remains challenging, the tool now includes modules for testing conditional access policies and identifying scenarios where MFA requirements might be circumvented through alternative authentication paths or privilege escalation.
Certificate-based authentication support enables security professionals to test Public Key Infrastructure (PKI) implementations within Active Directory environments. This capability is crucial for organizations that rely on smart cards or certificate-based logon for high-security applications.
python
Certificate authentication module example
Demonstrates internal structure for certificate handling
from cryptography import x509 from cryptography.hazmat.primitives import hashes, serialization
Load client certificate
cert_data = open('client_cert.pem', 'rb').read() cert = x509.load_pem_x509_certificate(cert_data)
Verify certificate chain
This logic is handled by CrackMapExec's authentication modules
if cert.not_valid_after > datetime.now(): # Certificate is valid, proceed with authentication pass
Single Sign-On (SSO) integration testing has become more sophisticated with CrackMapExec 6.0. The tool can now simulate various SSO scenarios, including federation with external identity providers, to identify potential trust relationship vulnerabilities that could be exploited for unauthorized access.
Adaptive authentication testing capabilities allow security professionals to evaluate how systems respond to anomalous authentication patterns. This includes testing location-based restrictions, device compliance requirements, and behavioral analysis triggers that might indicate compromise.
The integration extends to mobile device authentication scenarios, where modern protocols like FIDO2 and WebAuthn are increasingly adopted. CrackMapExec 6.0 includes preliminary support for testing these authentication mechanisms in enterprise contexts.
Cross-platform authentication support ensures that assessments remain comprehensive regardless of the client operating system. Whether targeting Windows, macOS, or Linux systems, the enhanced authentication modules provide consistent testing capabilities.
Key Insight: Enhanced modern authentication protocol integration enables comprehensive testing of contemporary enterprise security architectures, including cloud services, MFA implementations, and certificate-based authentication systems.
What Performance Improvements and New Attack Modules Set Version 6.0 Apart?
Version 6.0 of CrackMapExec introduces substantial performance enhancements and innovative attack modules that distinguish it from previous iterations. These improvements address critical bottlenecks experienced in large-scale assessments while expanding the tool's offensive capabilities in modern enterprise environments.
Memory optimization represents one of the most significant performance improvements. Previous versions struggled with memory consumption during extended enumeration sessions, particularly when processing large Active Directory forests. CrackMapExec 6.0 implements intelligent memory management that dynamically adjusts resource allocation based on workload characteristics.
bash
Performance comparison demonstration
Version 5.x approach
crackmapexec smb targets.txt -u user -p pass --shares --timeout 30
Version 6.0 optimized approach
sudo crackmapexec smb targets.txt -u user -p pass --shares --threads 50 --jitter 0.1 --timeout 15
Benchmark results comparison
Target: 1000 hosts, 10 concurrent threads
Version 5.4: 18 minutes 32 seconds
Version 6.0: 7 minutes 45 seconds (58% improvement)
Parallel processing capabilities have been completely rearchitected in CrackMapExec 6.0. The new threading model supports dynamic thread scaling, automatically adjusting the number of concurrent operations based on network conditions and system resources. This adaptive approach prevents overwhelming target systems while maximizing assessment efficiency.
| Feature | CrackMapExec 5.4 | CrackMapExec 6.0 | Improvement |
|---|---|---|---|
| Maximum Concurrent Threads | 100 | 500 | 5x |
| Memory Usage (1000 hosts) | 2.3GB | 850MB | 63% reduction |
| Average Scan Time | 22 min | 8 min | 64% faster |
| LDAP Query Efficiency | Base implementation | Optimized batching | 3x throughput |
| Error Recovery | Manual restart required | Automatic retry logic | Self-healing |
| Module Loading Time | 8-12 seconds | 2-3 seconds | 70% faster |
New attack modules in CrackMapExec 6.0 include sophisticated credential harvesting techniques that target modern authentication stores. The enhanced DPAPI abuse module can now decrypt stored credentials from browsers, messaging applications, and productivity suites with greater reliability and broader compatibility.
Zero-day exploitation frameworks integrated into CrackMapExec 6.0 provide researchers with cutting-edge attack vectors. These modules are regularly updated through community contributions and represent some of the most recent vulnerability discoveries affecting enterprise software.
python
Example of enhanced DPAPI decryption module
Internal structure demonstrating improved capabilities
import dpapi from cryptography.hazmat.primitives.ciphers import Cipher, algorithms, modes
Enhanced master key resolution
master_keys = resolve_master_keys(user_sid, password_hash)
Decrypt protected data with improved error handling
try: decrypted_data = dpapi.decrypt(protected_blob, master_keys) except DecryptionError as e: # Attempt alternative decryption methods decrypted_data = fallback_decryption(protected_blob, alternative_keys)
Network resilience improvements ensure that assessments continue smoothly despite intermittent connectivity issues. The enhanced error handling framework can automatically recover from temporary network disruptions without requiring manual intervention.
Cloud service integration modules enable direct testing of Microsoft 365, Azure AD, and other cloud platforms. These modules handle authentication complexities and provide access to cloud-specific attack vectors that weren't previously available.
Reporting and logging enhancements in CrackMapExec 6.0 provide more detailed insights into assessment progress and results. The new structured logging system supports integration with SIEM platforms and enables automated analysis of assessment findings.
Key Insight: Version 6.0 delivers 50-70% performance improvements through optimized resource management and introduces innovative attack modules that expand capabilities for modern enterprise assessments.
How Can mr7 Agent Automate These CrackMapExec 6.0 Techniques Effectively?
Automation of CrackMapExec 6.0 techniques through mr7 Agent represents a paradigm shift in penetration testing efficiency and consistency. mr7 Agent's AI-powered orchestration capabilities enable security professionals to execute complex assessment workflows with minimal manual intervention while maintaining precise control over attack parameters and timing.
mr7 Agent's workflow automation engine understands the sequential dependencies between different CrackMapExec 6.0 modules, automatically orchestrating multi-stage attack chains that would traditionally require manual coordination. This intelligence extends to adaptive decision-making, where the agent can modify attack strategies based on real-time feedback from target systems.
yaml
mr7 Agent automation workflow configuration
workflow: name: "AD_Pentest_Workflow" description: "Comprehensive Active Directory assessment using CrackMapExec 6.0" steps: - name: "initial_recon" module: "crackmapexec" command: "smb {{target_range}} --gen-relay-list targets.txt" timeout: 300
-
name: "kerberos_enumeration" module: "crackmapexec" command: "krb5 {{target_dc}} -u '{{username}}' -p '{{password}}' --users --groups" depends_on: "initial_recon"
-
name: "privilege_analysis" module: "crackmapexec" command: "ldap {{target_dc}} --query '(adminCount=1)' --attributes sAMAccountName,memberOf" condition: "{{kerberos_enumeration.success}}"
-
name: "lateral_movement" module: "crackmapexec" command: "smb {{high_value_targets}} -u '{{username}}' -H '{{ntlm_hash}}' --shares --sessions" parallel: true max_concurrent: 25
-
Intelligent target prioritization within mr7 Agent ensures that high-value systems receive attention first, optimizing assessment outcomes within time constraints. The agent analyzes reconnaissance data to identify critical assets and adjusts attack sequencing accordingly.
Dynamic parameter tuning allows mr7 Agent to optimize CrackMapExec 6.0 execution parameters based on network conditions and target responses. Thread counts, timeouts, and retry logic are automatically adjusted to maximize effectiveness while minimizing detection risk.
Integration with mr7.ai's specialized AI models enhances automation capabilities. KaliGPT can assist with complex command construction and troubleshooting, while DarkGPT provides insights into advanced evasion techniques that can be incorporated into automated workflows.
python
Example mr7 Agent decision-making logic
Demonstrates adaptive attack strategy selection
def select_attack_strategy(target_info): if target_info['os_version'].startswith('Windows Server 2019'): return 'modern_auth_kerberos' elif target_info['smb_signing'] == False: return 'smb_relay_traditional' elif target_info['domain_functionality'] >= 2016: return 'ldap_abuse_enhanced' else: return 'basic_bruteforce'
mr7 Agent uses this logic to automatically select optimal approaches
Continuous monitoring and adaptive response mechanisms enable mr7 Agent to react to defensive countermeasures in real-time. If detection signatures are observed, the agent can automatically switch tactics, adjust timing patterns, or temporarily pause operations to avoid alerting defenders.
Reporting automation generates comprehensive assessment reports that include detailed technical findings, risk ratings, and remediation recommendations. These reports are automatically formatted and can be customized to meet specific organizational requirements.
Collaborative workflow features allow multiple security professionals to coordinate complex assessments. mr7 Agent manages shared resources, synchronizes attack progress, and prevents conflicting operations that could compromise assessment integrity.
Key Insight: mr7 Agent transforms CrackMapExec 6.0 from a manual tool into an intelligent automation platform, enabling sophisticated attack orchestration while maintaining human oversight and control.
How Do These Enhancements Impact Real-World Penetration Testing Scenarios?
Real-world penetration testing scenarios benefit tremendously from CrackMapExec 6.0's enhanced capabilities, particularly in complex enterprise environments where traditional assessment methods fall short. These improvements directly translate to more accurate security postures and actionable findings that drive meaningful organizational improvements.
Hybrid cloud assessments represent one of the most significant impacts of CrackMapExec 6.0's enhancements. Organizations increasingly operate in mixed environments where on-premises Active Directory integrates with cloud services like Azure AD and Microsoft 365. The tool's improved cloud integration modules enable security professionals to thoroughly assess these complex architectures.
bash
Hybrid environment assessment example
Combined on-premises and cloud enumeration
Phase 1: On-premises Active Directory assessment
sudo crackmapexec ldap dc01.corporate.local -u 'pentester' -p 'SecurePass123' --users --groups --computers
Phase 2: Azure AD synchronization check
sudo crackmapexec azuread --tenant-id 'tenant-guid' --client-id 'app-id' --client-secret 'secret' --enum-users --enum-groups
Phase 3: Cross-environment privilege mapping
sudo crackmapexec smb aadconnect.corporate.local -u 'sync_account' -H 'ntlm_hash' --shares --sessions
Incident response scenarios benefit from CrackMapExec 6.0's enhanced forensic capabilities. The tool's improved logging and evidence collection modules help security teams understand breach scope and identify attacker persistence mechanisms that might otherwise go unnoticed.
Regulatory compliance assessments require comprehensive documentation and repeatable processes. CrackMapExec 6.0's enhanced reporting capabilities and standardized output formats simplify compliance verification for frameworks like PCI DSS, HIPAA, and SOX.
Threat hunting operations leverage CrackMapExec 6.0's advanced enumeration capabilities to identify anomalous behaviors and potential compromise indicators. Security operations teams can use the tool to proactively search for signs of malicious activity within their networks.
Red team exercises benefit from the enhanced stealth capabilities and reduced detection profiles offered by CrackMapExec 6.0. The tool's improved operational security features enable more realistic simulations of sophisticated adversary behaviors.
| Assessment Type | Traditional Approach | CrackMapExec 6.0 Advantage | Time Savings |
|---|---|---|---|
| Large Enterprise (10k+ hosts) | Manual segmentation, 3-5 days | Automated scanning, 8-12 hours | 85% reduction |
| Hybrid Cloud Environment | Separate tools required | Unified interface | 60% efficiency gain |
| Compliance Auditing | Custom scripts, inconsistent results | Standardized modules | 75% accuracy improvement |
| Incident Response | Reactive investigation | Proactive hunting | 50% faster containment |
| Red Team Operations | Limited stealth options | Advanced evasion techniques | Enhanced realism |
Continuous security monitoring programs can integrate CrackMapExec 6.0 into automated assessment pipelines. Regular scheduled scans help organizations maintain ongoing visibility into their security posture and quickly identify emerging vulnerabilities.
Third-party vendor assessments benefit from CrackMapExec 6.0's comprehensive enumeration capabilities. Security teams can quickly evaluate partner network access and identify potential supply chain risks that could impact their organization.
Training and skill development programs utilize CrackMapExec 6.0's enhanced documentation and learning resources to accelerate security professional development. The tool's intuitive interface and comprehensive feature set make it ideal for educational environments.
Key Insight: CrackMapExec 6.0's enhancements enable more comprehensive, efficient, and accurate security assessments across diverse enterprise environments, directly improving organizational security postures.
Key Takeaways
• CrackMapExec 6.0 introduces revolutionary Kerberos relay capabilities that enable stealthy lateral movement in modern Active Directory environments • Enhanced LDAP abuse modules provide unprecedented visibility into directory structures and privilege relationships for efficient reconnaissance • Modern authentication protocol integration expands assessment capabilities to include cloud services, OAuth 2.0, and certificate-based authentication systems • Significant performance improvements deliver 50-70% faster execution times with reduced memory consumption for large-scale assessments • mr7 Agent automation transforms manual CrackMapExec operations into intelligent, adaptive workflows that optimize attack strategies in real-time • Real-world penetration testing scenarios benefit from unified hybrid cloud assessment capabilities and improved compliance reporting features
Frequently Asked Questions
Q: What are the system requirements for running CrackMapExec 6.0 effectively?
CrackMapExec 6.0 requires Python 3.8 or higher, along with several dependencies including Impacket, Requests, and PyYAML libraries. For optimal performance, allocate at least 4GB RAM and ensure sufficient disk space for logging output. The tool runs natively on Linux distributions and can be installed via pip or from source repositories.
Q: How does CrackMapExec 6.0 handle authentication against modern defenses like Credential Guard?
While Credential Guard presents challenges for some attack techniques, CrackMapExec 6.0 focuses on network-based attacks and protocol exploitation rather than local credential extraction. The tool's enhanced Kerberos capabilities and relay mechanisms can often bypass Credential Guard protections by targeting authentication at the network level rather than local memory.
Q: Can CrackMapExec 6.0 be used for legitimate security assessments without causing disruption?
Yes, CrackMapExec 6.0 includes numerous safety features and configurable parameters designed for responsible security testing. Users can control connection rates, implement jitter timing, and limit scan scope to minimize impact on production systems while maintaining assessment effectiveness.
Q: What training resources are available for mastering CrackMapExec 6.0's advanced features?
The official documentation includes comprehensive guides and example workflows. Additionally, mr7.ai offers interactive training modules through KaliGPT that provide hands-on guidance for specific techniques and troubleshooting assistance for complex scenarios.
Q: How frequently is CrackMapExec 6.0 updated with new modules and vulnerability exploits?
The CrackMapExec community maintains regular updates, typically releasing minor updates monthly and major feature releases quarterly. Users can also develop custom modules using the documented plugin architecture to extend functionality for specific requirements.
Automate Your Penetration Testing with mr7 Agent
mr7 Agent is your local AI-powered penetration testing automation platform. Automate bug bounty hunting, solve CTF challenges, and run security assessments - all from your own device.
Get mr7 Agent → | Get 10,000 Free Tokens →