YARA Rules for Detecting Reflective Loading in Memory
Detecting .NET Reflective Loading with YARA Rules: A Comprehensive Guide
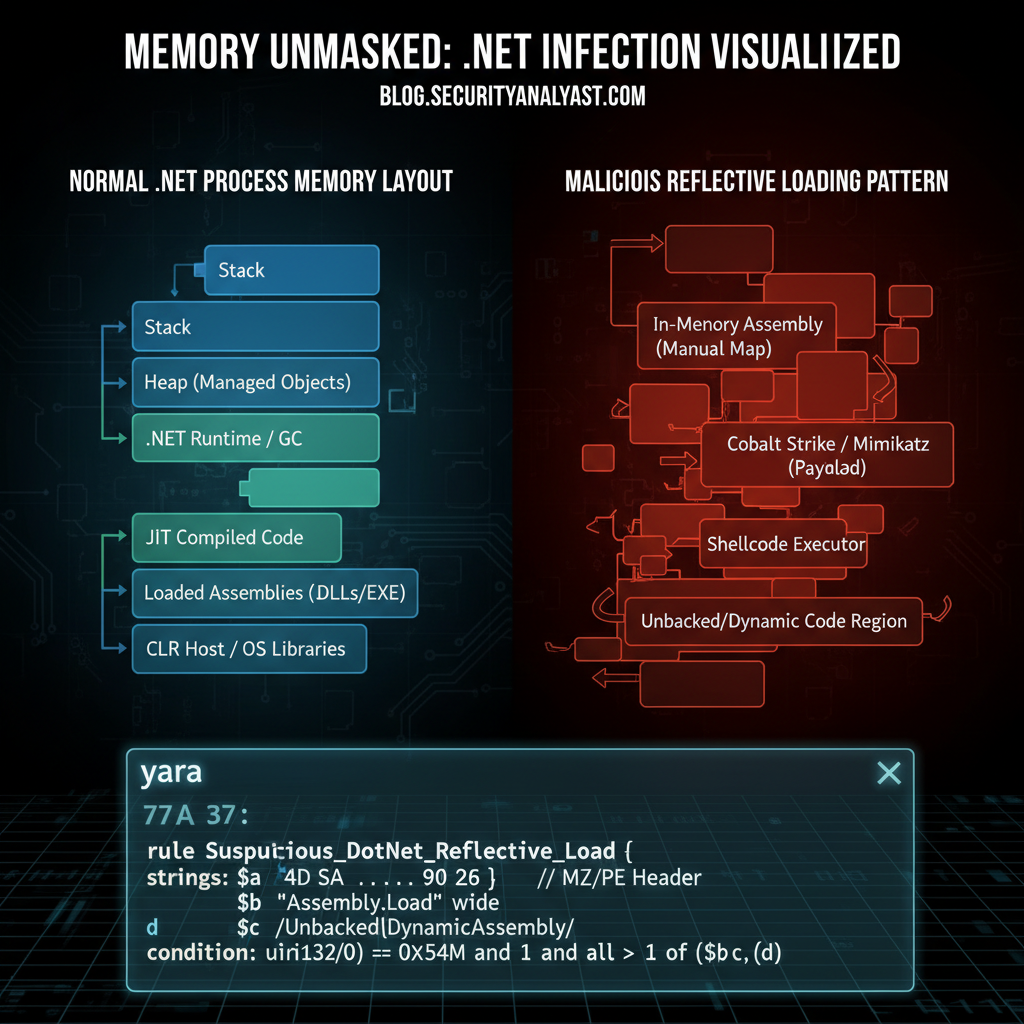
In-memory attacks have become one of the most challenging threats facing modern security teams. With a reported 280% increase in such attacks during 2026, traditional signature-based antivirus solutions often fall short. Malware loaders like Cobalt Strike and Sliver leverage reflective DLL injection within .NET processes to execute payloads entirely in memory, bypassing file-based detection mechanisms. This technique allows attackers to maintain persistence while avoiding forensic artifacts on disk.
To combat these advanced threats, security researchers are turning to YARA rules for memory analysis. YARA provides a powerful pattern-matching language that enables the identification of specific byte sequences, strings, and structural patterns associated with malicious activity. However, crafting effective YARA rules for detecting reflective loading requires deep understanding of both the underlying attack techniques and the memory structures involved.
This guide will walk you through the process of creating targeted YARA rules specifically designed to detect .NET reflective loading. We'll explore the technical characteristics of reflective DLL injection, examine memory patterns indicative of compromise, and demonstrate practical rule creation with real-world examples. Additionally, we'll discuss testing methodologies, integration with SIEM systems, and strategies for reducing false positives while maintaining high detection accuracy.
Throughout this article, we'll showcase how mr7.ai's suite of AI-powered tools can enhance your threat hunting capabilities. From assisting with rule development to automating complex analysis tasks, mr7.ai offers specialized models tailored for security professionals working in this domain.
By mastering the techniques outlined here, you'll be better equipped to detect and respond to sophisticated in-memory attacks that evade conventional defenses.
What Makes .NET Reflective Loading Difficult to Detect?
.NET reflective loading represents a significant challenge for traditional security controls because it operates entirely within the memory space of legitimate processes. Unlike conventional malware that writes executable files to disk, reflective loaders inject their payload directly into running applications, often leveraging trusted system utilities like PowerShell, rundll32.exe, or wscript.exe.
The core concept behind reflective loading involves manually mapping a DLL into the address space of a host process without relying on standard Windows loader APIs. This technique was popularized by tools like Reflective DLL Injection (RDLL) and has since been adopted by numerous offensive frameworks including Cobalt Strike's Beacon and Sliver's implant stagers.
Several factors contribute to the stealthiness of .NET reflective loading:
- No File Artifacts: Since the malicious code never touches disk, there are no file hashes or paths to monitor or blacklist.
- Process Masquerading: Attackers typically inject into legitimate processes, making behavioral analysis more complex.
- Memory Obfuscation: Payloads may employ encryption, compression, or packing to hide their true nature until execution time.
- Dynamic Allocation: Memory regions used for injection are often allocated with RWX permissions temporarily, complicating static analysis.
These characteristics make reflective loading particularly effective against host-based intrusion prevention systems (HIPS) and endpoint detection and response (EDR) solutions that rely heavily on file-based indicators.
Detecting such activity requires shifting focus from file-based signatures to memory-resident artifacts. This includes identifying unusual memory allocation patterns, unexpected module loads, and anomalous API calls related to process manipulation.
From a YARA perspective, successful detection hinges on recognizing distinctive byte sequences or structural elements present in injected modules before they're fully unpacked or executed. These might include PE headers with non-standard characteristics, embedded configuration data, or unique string constants used by known frameworks.
Understanding these nuances is critical when developing YARA rules aimed at catching reflective loading attempts early in the attack lifecycle.
Common Indicators of Compromise
Security analysts investigating potential compromises should look for several telltale signs associated with reflective loading:
- Unusual Process Behavior: Processes exhibiting abnormal network connections, registry modifications, or file operations inconsistent with their typical function.
- Suspicious Memory Patterns: Allocations marked as PAGE_EXECUTE_READWRITE (0x40) or similar executable permissions in unexpected contexts.
- Missing Module Entries: Loaded libraries that don't appear in the process's module list despite being mapped into memory.
- API Hooking Evidence: Calls to functions like
WriteProcessMemory,CreateRemoteThread, orNtMapViewOfSectionoriginating from benign processes. - Embedded Strings: Presence of framework-specific identifiers such as "Beacon", "CobaltStrike", or "Sliver" within memory dumps.
By correlating these observations across multiple data sources—including process monitoring logs, kernel callbacks, and raw memory captures—analysts can build a more complete picture of ongoing exploitation attempts.
Actionable Insight: Effective detection of .NET reflective loading requires combining behavioral analytics with low-level memory inspection techniques. Focus on identifying deviations from baseline process behavior rather than relying solely on static signatures.
How Does Reflective DLL Injection Work in .NET Environments?
Reflective DLL injection in .NET environments leverages the flexibility of the Common Language Runtime (CLR) to load and execute unmanaged code without requiring explicit linking or registration. This approach exploits the dynamic nature of .NET assemblies and the ability to manipulate memory directly through unsafe code blocks or interoperability layers.
The general workflow for reflective injection follows these steps:
- Payload Delivery: An initial dropper or stage-one component delivers the reflective loader payload, which may be embedded within a larger script or encoded within a legitimate application.
- Memory Allocation: The loader allocates a region of memory within the target process using functions like
VirtualAllocExorNtAllocateVirtualMemory. This region is typically marked with read-write-execute (RWX) permissions to allow subsequent code execution. - Code Injection: The reflective loader copies the malicious DLL image into the allocated memory space. Crucially, this copy doesn't follow standard PE layout conventions; instead, it contains position-independent code designed to resolve its own imports and relocations at runtime.
- Execution Handoff: Control is transferred to the injected code via a remote thread created using
CreateRemoteThreador equivalent syscall wrappers. The injected DLL then performs self-loading procedures, resolving necessary dependencies and preparing itself for execution. - Self-Relocation: Once active, the injected module adjusts its internal references based on its actual load address. It also resolves external symbols by walking the export tables of loaded modules or manually parsing import descriptors.
- Payload Execution: Finally, the reflective loader executes its intended functionality, whether that's establishing a reverse shell, deploying additional stages, or performing lateral movement.
In .NET contexts, this process can be further obscured by wrapping the reflective loader inside managed code that uses P/Invoke to interact with native Win32 APIs. For example, a C# assembly might contain Base64-encoded shellcode that gets decoded and injected into another process using Marshal.AllocHGlobal() and Marshal.Copy() methods.
This hybrid approach blurs the line between managed and unmanaged execution, potentially evading EDR hooks placed on common injection APIs. Moreover, since much of the malicious logic resides in dynamically generated machine code, traditional .NET decompilers offer limited visibility into the attacker's intent.
Another variation involves leveraging .NET's built-in support for loading assemblies from byte arrays (Assembly.Load(byte[])). While this method still requires writing the assembly to memory, it avoids touching disk and can be combined with obfuscation techniques to hinder analysis.
It's worth noting that many modern offensive frameworks implement custom reflective loaders optimized for evasion. These loaders often incorporate anti-analysis features such as stack walking checks, debugger detection routines, and delayed execution timers to frustrate automated sandbox environments.
Understanding these mechanics is essential for crafting YARA rules capable of identifying pre-execution artifacts left behind by reflective loaders. By focusing on structural anomalies and framework-specific constants, defenders can develop signatures that catch malicious activity regardless of the delivery mechanism.
Key Point: Reflective injection bypasses normal OS loader mechanisms, allowing attackers to run arbitrary code within trusted processes. Detection efforts must focus on identifying the unique memory footprints left by these techniques.
What Are the Memory Patterns Associated with Reflective Loading?
Identifying reflective loading in memory requires recognizing specific patterns that distinguish malicious injection from legitimate software behavior. These patterns manifest across various dimensions including memory layout, access permissions, content structure, and temporal relationships between allocations.
One of the most prominent indicators is the presence of RWX memory regions. Legitimate applications rarely require pages with simultaneous read, write, and execute permissions except during brief periods such as JIT compilation or dynamic code generation. Persistent RWX allocations lasting beyond expected intervals often signal malicious activity.
Additionally, reflective loaders frequently exhibit distinct memory layouts characterized by:
- Non-Standard Section Characteristics: Injected modules may lack typical section names (.text, .data, .rsrc) or possess unusual size ratios between code and data segments.
- Embedded Configuration Data: Many frameworks embed configuration blobs containing C2 server addresses, encryption keys, or sleep intervals. These structures often have predictable formats or contain identifiable magic values.
- Compressed or Encrypted Content: To evade static analysis, payloads are commonly compressed or encrypted prior to injection. Decompression stubs or cryptographic initialization routines leave characteristic traces in memory.
- Import Address Table Reconstruction: Reflective loaders must reconstruct their IAT manually, leading to observable patterns in memory reads corresponding to API resolution activities.
Let's examine some concrete examples using memory dumps from known samples:
bash
Using Volatility to analyze a suspected infection
volatility -f infected_memory.dmp --profile=Win7SP1x64 malfind
This command reveals memory sections with suspicious protection attributes and content:
Process: svchost.exe Pid: 1234 Address: 0x0000000002a10000 Tag: Vad Protection: PAGE_EXECUTE_READWRITE
0x0000000002a10000 4d 5a 90 00 03 00 00 00 04 00 00 00 ff ff 00 00 MZ.............. 0x0000000002a10010 b8 00 00 00 00 00 00 00 40 00 00 00 00 00 00 00 ........@.......
Notice the classic PE header signature (MZ) followed by an NT header offset pointing to a valid DOS stub. Such findings strongly suggest reflective injection, especially if found outside known module boundaries.
Framework-specific artifacts also provide valuable clues. Consider the following excerpt from a Cobalt Strike Beacon dump:
c unsigned char beacon_config[] = { 0x00, 0x00, 0xbe, 0xef, // Magic value 0x01, 0x00, // Protocol version 0x7f, 0x00, 0x00, 0x01, // C2 IP (127.0.0.1) 0x01, 0xbb, // Port (443) ... };
Unique byte sequences like the 0xbeef magic number serve as excellent candidates for YARA rules targeting Cobalt Strike deployments.
Beyond raw bytes, timing and sequence analysis can reveal reflective loading attempts. Tools like ProcMon or custom ETW providers can capture events showing rapid succession of memory allocation, write, and thread creation operations—all hallmarks of injection workflows.
Combining these approaches yields robust detection coverage spanning both static and behavioral aspects of reflective loading campaigns.
Pro Tip: Monitor for repeated small allocations followed by large RWX regions—a common artifact of staged reflective loaders decompressing final payloads in memory.
Step-by-Step: Creating YARA Rules for Reflective Loading Detection
Creating effective YARA rules for detecting reflective loading requires careful attention to specificity, performance, and maintainability. Below is a detailed walkthrough covering everything from initial reconnaissance to deployment-ready signatures.
Initial Reconnaissance
Begin by collecting representative samples of known reflective loaders. Public repositories like VirusTotal, ANY.RUN, or Hybrid-Analysis provide access to detonated malware with full behavioral reports. Focus on variants associated with Cobalt Strike, Sliver, or Meterpreter to ensure broad applicability.
Use memory forensic tools to extract relevant artifacts:
bash
Extract memory-resident modules using Volatility
volatility -f sample_memory.dmp --profile=Win7SP1x64 modscan > modules.txt volatility -f sample_memory.dmp --profile=Win7SP1x64 memdump -p -D ./dumps/
Next, analyze extracted binaries using disassemblers and hex editors to locate distinguishing features. Look for:
- Embedded strings or GUIDs
- Cryptographic constants
- Compression library footprints
- Framework-specific opcodes
Document all promising candidates for inclusion in your YARA rule set.
Rule Structure Basics
A basic YARA rule consists of metadata, strings, and conditions sections. Here's a minimal template:
yara rule ReflectiveLoader_Generic { meta: description = "Detects generic reflective loader artifacts" author = "Security Researcher" date = "2026-03-18" strings: $mz_header = { 4D 5A } $pe_magic = { 50 45 00 00 } $rw_alloc = "VirtualAllocEx" ascii wide condition: uint16(0) == 0x5a4d and $pe_magic at (uint32(0x3c)) and $rw_alloc }
While functional, this rule lacks precision and could generate excessive false positives. Refine it by incorporating framework-specific markers:
yara rule CobaltStrike_Beacon_Stageless { meta: description = "Detects Cobalt Strike stageless beacon" reference = "https://www.cobaltstrike.com/help-beacon" hash = "e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855" strings: $magic = { 00 00 be ef } $c2_ip = /\x7f\x00\x00\x01/ // Loopback IP placeholder $aes_key = { 60 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? } condition: filesize < 5MB and $magic and $c2_ip and $aes_key }
This improved version narrows scope significantly by checking for known Cobalt Strike configuration structures. Adjust thresholds according to observed prevalence in your environment.
Advanced Techniques
For greater sophistication, consider employing YARA's advanced features:
Regular Expressions
Capture variable-length fields using regex patterns:
yara $c2_url = /http://([a-z0-9]+.){1,3}[a-z]{2,}/ nocase
String Modifiers
Apply modifiers to improve matching reliability:
yara $cmdline = "powershell.exe" fullword ascii
External Variables
Parameterize rules for easier tuning:
yara rule Suspicious_Allocation { strings: $alloc = "VirtualAlloc" ascii condition: $alloc and filesize >= min_size }
Then invoke with parameters:
bash yara -x min_size=1048576 suspicious.yar sample.bin
Performance Optimization
Avoid overly broad conditions that force full-file scans:
yara // Slow - scans entire file condition: any of them
// Fast - anchors match to known offsets condition: $header at 0 and $footer at filesize - 4
Profile rules extensively using test corpora to measure impact on scan times and resource consumption.
Testing Methodologies
Validate newly crafted rules against diverse datasets comprising clean files, benign implants, and confirmed malicious samples. Automated pipelines facilitate regression testing and continuous improvement.
Leverage tools like yarGen or Loki for semi-automatic rule generation and refinement:
bash python3 yarGen.py -m /path/to/malware/samples/ -o generated_rules.yar
Integrate findings back into manual review cycles to refine heuristics and reduce noise.
Best Practice: Version control all YARA rules alongside documentation explaining design rationale and update history. This ensures traceability and simplifies collaboration among team members.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
How Can You Reduce False Positives in Reflective Loading Rules?
False positives represent one of the biggest challenges when deploying YARA rules for reflective loading detection. Overly permissive rules risk overwhelming analysts with irrelevant alerts, while overly restrictive ones may miss genuine threats. Achieving optimal balance requires strategic use of contextual filters, statistical modeling, and feedback loops informed by operational experience.
Contextual Filtering
Incorporate environmental awareness into rule logic wherever possible. For instance, certain behaviors are more suspicious coming from user-mode processes than kernel drivers:
yara rule Suspicious_RWX_Allocation { strings: $rwx = { 90 90 90 90 } // NOP sled condition: not pe.is_driver and pe.sections[0].name != ".text" and $rwx }
Similarly, prioritize alerts involving privileged accounts or cross-process communication:
yara condition: pe.imphash() == "known_malicious_hash" and (pe.subsystem == IMAGE_SUBSYSTEM_WINDOWS_GUI or pe.subsystem == IMAGE_SUBSYSTEM_WINDOWS_CUI)
Such refinements help suppress benign cases while preserving sensitivity to malicious activity.
Statistical Modeling
Analyze historical alert volumes to establish baselines for acceptable false positive rates. Set thresholds accordingly:
| Alert Type | Baseline Rate | Threshold |
|---|---|---|
| Generic Loader Signature | 5% | 2% |
| Framework-Specific Artifact | 1% | 0.5% |
| Behavioral Pattern Match | 10% | 5% |
Monitor deviations over time using dashboards integrated with SIEM platforms. Investigate spikes promptly to determine root causes and adjust rules accordingly.
Feedback Loops
Establish formal channels for analyst input regarding rule effectiveness. Periodically solicit feedback through surveys or informal discussions:
- Which alerts proved actionable?
- Were any missed detections identified post-incident?
- Could existing rules benefit from additional constraints?
Translate insights into iterative improvements applied systematically across the rulebase.
Comparative Analysis
Compare performance metrics side-by-side to highlight strengths and weaknesses:
| Metric | Rule A | Rule B | Improvement |
|---|---|---|---|
| Precision | 82% | 91% | +9% |
| Recall | 76% | 85% | +9% |
| Throughput | 1000/sec | 800/sec | -20% |
Choose tradeoffs wisely based on organizational priorities and available resources.
Ultimately, minimizing false positives demands constant vigilance and willingness to adapt. Stay engaged with evolving threat landscapes and refine detection logic proactively rather than reactively.
Warning: Never deploy experimental rules directly into production without adequate validation. Always conduct thorough testing in isolated environments first.
What Are the Best Practices for Testing YARA Rules Against Real Malware?
Effective testing forms the backbone of reliable YARA rule development. Without rigorous evaluation procedures, even well-crafted signatures carry inherent risks of failure under real-world conditions. Adopt systematic approaches grounded in empirical evidence to maximize confidence in deployed rules.
Sample Acquisition Strategy
Source test material responsibly from reputable providers adhering to legal and ethical standards. Avoid unverified third-party sites that may distribute pirated or illegally obtained content. Preferred options include:
- Government-sponsored repositories (e.g., National Software Reference Library)
- Commercial threat intelligence feeds
- Academic research collections
- Internal incident response archives (subject to privacy protections)
Ensure diversity in collected specimens spanning different threat actors, TTPs, and geographies. Balance representation between prevalent families and emerging trends to maintain relevance over time.
Test Environment Setup
Recreate realistic operational scenarios within controlled lab settings. Configure virtual machines mirroring target infrastructure down to patch levels and installed software suites. Isolate each test case to prevent contamination or interference effects.
Install representative endpoint agents and logging mechanisms to simulate actual monitoring configurations. Capture telemetry streams parallel to YARA scan outputs for later correlation and analysis.
Document setup procedures meticulously to enable reproducibility and troubleshooting efforts. Version-control all scripts, configurations, and auxiliary tools used throughout the testing pipeline.
Evaluation Metrics
Define clear success criteria aligned with business objectives and risk tolerance levels. Quantitative measures facilitate objective comparisons between competing rule sets:
- True Positive Rate (Recall): Proportion of malicious samples correctly flagged
- False Positive Rate: Fraction of benign inputs incorrectly classified
- F-Measure: Harmonic mean balancing precision and recall
- Scan Time: Average duration required to evaluate individual files
- Resource Consumption: CPU/memory usage during peak activity periods
Track these metrics consistently across iterations to assess progress toward stated goals. Visualize trends graphically to identify areas needing attention or optimization.
Automation Frameworks
Scale testing operations using purpose-built frameworks that streamline repetitive tasks and enforce standardized workflows. Popular choices include:
- YaraCI: Continuous integration service for validating rule changes
- ThreatIngestor: Open-source tool for automating IOC extraction and testing
- Custom Python/Ruby scripts interfacing with RESTful APIs exposed by security vendors
Automate routine activities such as dataset preparation, rule compilation, batch scanning, and result aggregation. Reserve human oversight for nuanced decision-making and exception handling.
Reporting Standards
Generate comprehensive reports detailing methodology, findings, limitations, and recommendations for future work. Include visualizations, tabular summaries, and annotated excerpts illustrating key observations.
Structure deliverables logically with executive summaries catering to management audiences and technical appendices serving practitioner needs. Archive all artifacts securely for audit purposes and reference during peer reviews.
By embracing disciplined testing practices, organizations can deploy YARA rules with higher assurance of meeting intended security outcomes.
Tip: Maintain separate training, validation, and test datasets to avoid overfitting and ensure generalization capability across unseen data distributions.
How Do You Integrate YARA-Based Detection with SIEM Correlation Rules?
Integrating YARA-based detection into broader SIEM architectures amplifies overall defensive posture by enabling cross-domain correlations and enriched alert context. This synergy transforms discrete file inspections into holistic situational awareness capabilities spanning endpoints, networks, and cloud services.
Event Normalization
Standardize incoming YARA scan results into structured formats compatible with SIEM ingestion pipelines. Map native output fields to universal schemas such as ECS (Elastic Common Schema) or STIX/TAXII taxonomies:
{ "@timestamp": "2026-03-18T12:34:56Z", "event.kind": "alert", "rule.name": "Suspicious_NET_Loader", "file.path": "/tmp/sample.exe", "host.name": "workstation-01", "threat.framework": "MITRE ATT&CK", "threat.technique.id": "T1055.002" }
Normalize field names, data types, and categorical values to promote consistency and simplify query construction downstream.
Alert Enrichment
Augment basic YARA matches with supplementary information drawn from asset inventories, identity stores, and threat intelligence feeds. Examples include:
- User/group ownership details
- Departmental affiliations
- Criticality ratings
- Recent behavioral anomalies
- Known adversary associations
Enrichment enhances triage efficiency by providing richer context upfront, enabling faster prioritization decisions.
Cross-Correlation Logic
Design correlation rules linking YARA hits with complementary signals from other sensors. Possible combinations include:
- File hash reputation checks against VT/MISP
- Network flow analysis revealing outbound beaconing
- Registry modification tracking indicating persistence establishment
- Logon session anomalies suggesting lateral movement
Example SPLUNK SPL query combining YARA and Sysmon events:
spl
index=endpoint sourcetype="sysmon" EventCode=1 Image="\powershell.exe"
| join _raw [search index=yara rule_name="PowerShell_Reflective_Load"]
| stats count by host, user, process_guid_
Such queries surface multi-stage attacks unfolding over time and space, improving chances of early intervention.
Response Orchestration
Trigger automated remediation actions upon confirmed positive identifications. Options range from simple notifications to complex containment workflows orchestrated via SOAR platforms:
- Quarantine affected hosts
- Initiate memory dump collection
- Block associated IPs/domains
- Reset compromised credentials
- Notify stakeholders
Coordinate responses carefully to minimize disruption while maximizing containment speed.
Dashboard Visualization
Present integrated insights visually through interactive dashboards aggregating disparate data streams into coherent narratives. Highlight trending threats, hotspots, and mitigation statuses to keep leadership apprised of evolving risks.
Utilize drill-down capabilities to expose granular details supporting investigative workflows. Enable ad-hoc exploration empowering analysts to pursue leads independently.
Through thoughtful integration, YARA-based detection becomes a cornerstone element within comprehensive cyber defense ecosystems.
Recommendation: Align correlation rules with MITRE ATT&CK mappings to facilitate benchmarking against industry standards and regulatory requirements.
Key Takeaways
- .NET reflective loading techniques pose significant detection challenges due to their in-memory execution model and avoidance of traditional file-based artifacts.
- Effective YARA rules for detecting reflective loading must focus on memory-resident patterns, framework-specific constants, and structural anomalies unique to injection workflows.
- Reducing false positives requires contextual filtering, statistical modeling, and continuous feedback from operational experiences.
- Rigorous testing against diverse malware samples using automated frameworks ensures rule reliability and minimizes blind spots.
- Integrating YARA alerts with SIEM correlation engines enables holistic threat detection and accelerated incident response.
- Modern AI assistants like KaliGPT and DarkGPT can assist in rule development, analysis, and threat research.
- mr7 Agent provides powerful automation capabilities for implementing these detection strategies at scale.
Frequently Asked Questions
Q: Why are traditional AV solutions ineffective against reflective loading?
Traditional antivirus relies heavily on file-based signatures and behavioral heuristics that assume malicious code exists on disk. Reflective loading bypasses these assumptions by executing entirely in memory without creating persistent files. Furthermore, many reflective loaders employ evasion techniques such as packing, encryption, and delayed execution that defeat static analysis engines.
Q: Can YARA rules detect all types of reflective loading?
No single detection mechanism guarantees universal coverage. While YARA excels at identifying known patterns and structural artifacts, novel or heavily obfuscated loaders may evade signature-based approaches. Defense-in-depth strategies combining YARA with behavioral analytics, memory forensics, and network monitoring yield superior results compared to isolated tactics.
Q: How do I optimize YARA rules for performance?
Optimization begins with anchoring searches to known offsets whenever possible to avoid full-file scans. Employ efficient string representations (hex vs. text), limit wildcard usage, and apply tight bounding conditions around matches. Profile rules against representative datasets to measure impact on throughput and memory utilization. Eliminate redundant clauses and consolidate overlapping patterns where feasible.
Q: What role does mr7 Agent play in detecting reflective loading?
mr7 Agent serves as an automated penetration testing and bug bounty platform that can incorporate YARA-based detection into its workflow. It can automate memory scanning, correlate findings with other security tools, and execute predefined response actions. Its local processing capabilities ensure sensitive data remains secure while benefiting from AI-enhanced analysis through integrations with mr7.ai's specialized models.
Q: Are there open-source tools to help create YARA rules for reflective loading?
Yes, several community-developed tools aid in YARA rule creation and refinement. Projects like yarGen automatically generate candidate rules from malware samples, while Loki provides comprehensive scanning and reporting functionalities. Additionally, mr7.ai offers free tokens for trying advanced AI-assisted tools like KaliGPT and DarkGPT that can accelerate rule development and threat analysis processes.
Supercharge Your Security Workflow
Professional security researchers trust mr7.ai for AI-powered code analysis, vulnerability research, dark web intelligence, and automated security testing with mr7 Agent.


