EDR Bypass Syscalls: Advanced Techniques for Red Teams
EDR Bypass Syscalls: Advanced Techniques for Red Teams
In today's advanced threat landscape, endpoint detection and response (EDR) systems have evolved to detect traditional malware delivery mechanisms with unprecedented accuracy. As organizations deploy increasingly sophisticated behavioral analytics and machine learning-based detection, red teams must adapt by leveraging lower-level evasion techniques that operate beneath the radar of conventional security controls.
One such technique that has gained significant traction among advanced red teams is the use of direct system calls—also known as syscalls—to bypass EDR solutions that rely heavily on hooking high-level Windows APIs. By communicating directly with the kernel through undocumented system service numbers, attackers can execute malicious operations while avoiding the scrutiny of user-mode hooks placed by security software. This approach significantly reduces the forensic footprint of post-exploitation activities and enables sustained access within target environments.
This comprehensive guide delves into the technical intricacies of implementing direct syscalls for EDR bypass, covering everything from foundational concepts to advanced evasion strategies. We'll explore practical implementations using modern frameworks like SysWhispers3, demonstrate stack spoofing techniques to evade behavioral analysis, and examine methods for patching Event Tracing for Windows (ETW) to prevent telemetry leakage. Throughout this journey, we'll also highlight how mr7.ai's cutting-edge AI tools can accelerate your research and development process, providing intelligent assistance for exploit development and operational security considerations.
Whether you're a seasoned penetration tester looking to enhance your tradecraft or an ethical hacker seeking to understand defensive evasion mechanisms, this guide offers actionable insights that bridge theoretical knowledge with real-world application. Our goal is to equip you with the skills and resources necessary to navigate the complex landscape of modern endpoint security while maintaining operational effectiveness in adversarial simulations.
What Are EDR Bypass Syscalls and Why Are They Critical?
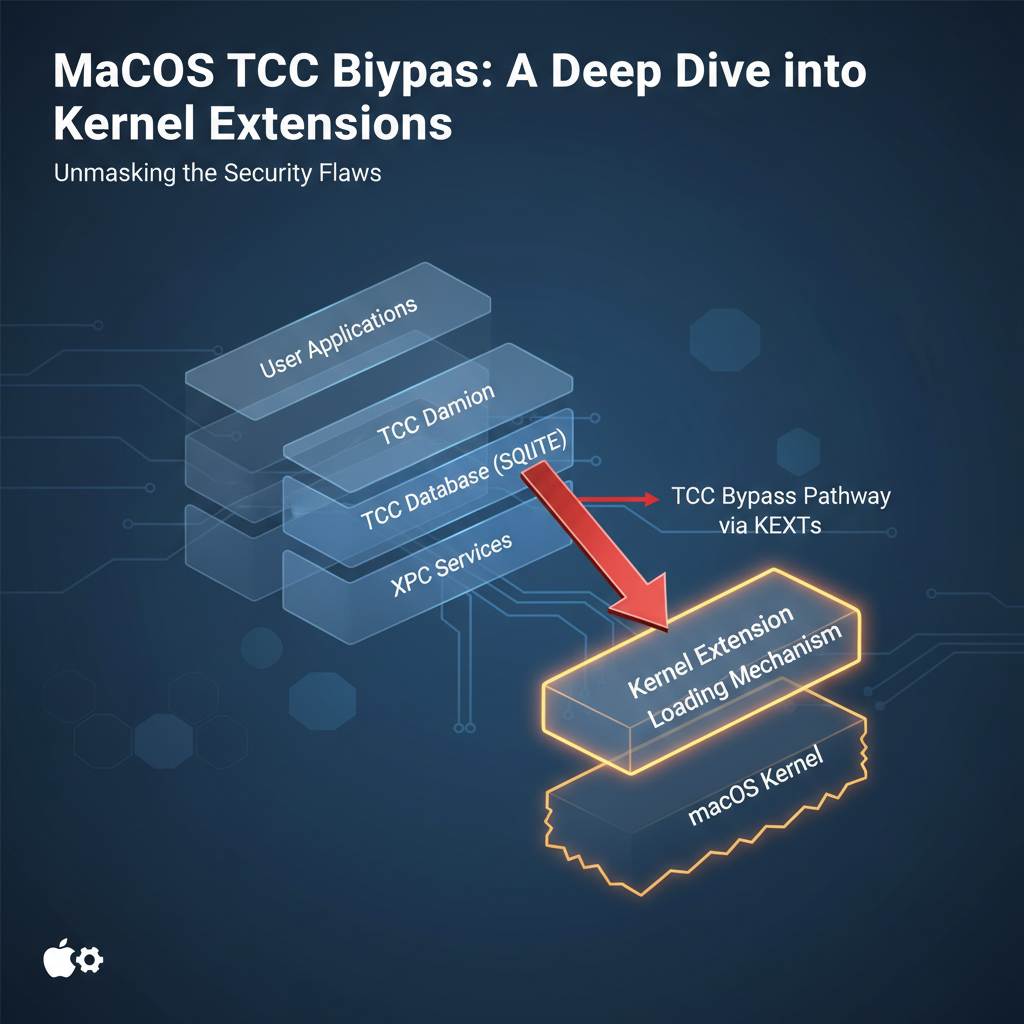
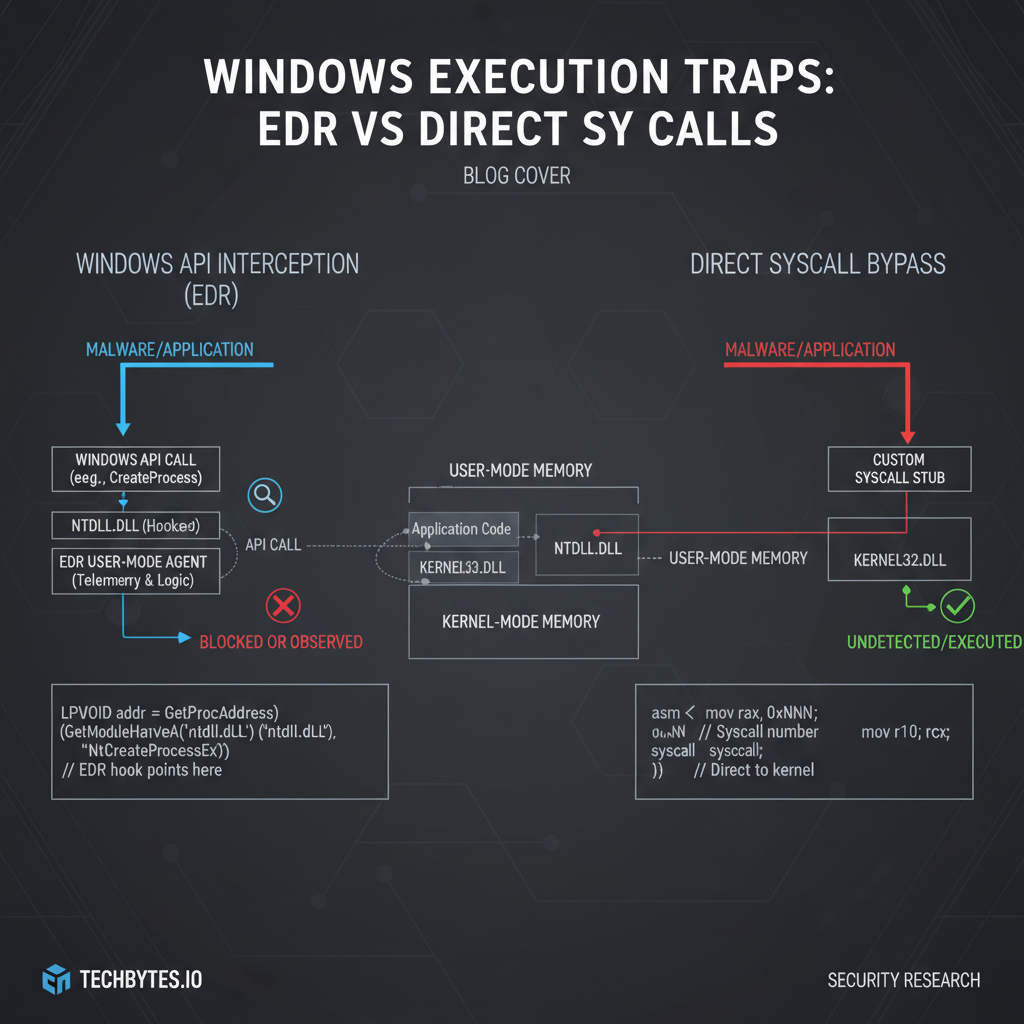
System calls represent the fundamental interface between user-mode applications and the Windows kernel, enabling programs to request privileged operations such as file manipulation, process creation, and memory management. Traditionally, these requests are made through documented Windows APIs like CreateFile, VirtualAlloc, or WriteProcessMemory, which internally translate user requests into corresponding system service calls. However, this translation layer has become a prime target for EDR vendors seeking to monitor and control potentially malicious activity.
Modern EDR solutions employ various hooking mechanisms to intercept API calls before they reach the kernel. These include inline hooks that modify function prologues, Import Address Table (IAT) hooks that redirect API calls through trampolines, and more sophisticated techniques like Microsoft's own Antimalware Scan Interface (AMSI). While effective against many attack vectors, these hooking methods create a detectable footprint that skilled adversaries can circumvent by bypassing the hooked APIs altogether.
Direct syscalls achieve this bypass by invoking system services directly through the SYSCALL instruction on x64 architectures (or INT 0x2E on older x86 systems). Instead of calling NtCreateFile through ntdll.dll, an attacker would manually construct the required parameters, load the appropriate system service number into the EAX register, and execute the SYSCALL instruction directly. This approach completely sidesteps any user-mode interception mechanisms since the execution flow transitions immediately from user code to kernel mode without passing through monitored API functions.
The critical advantage of syscall-based evasion lies in its ability to maintain operational stealth while preserving functionality. Unlike traditional shellcode injection techniques that trigger heuristic alerts or behavioral anomalies, properly implemented syscalls exhibit normal system behavior patterns that blend seamlessly with legitimate processes. This makes them particularly valuable for long-term persistence scenarios where minimizing detection risk is paramount.
However, implementing effective syscall evasion requires deep understanding of low-level Windows internals, including system service numbering conventions, parameter marshaling requirements, and architecture-specific calling conventions. Additionally, successful deployment necessitates careful attention to anti-analysis techniques that prevent reverse engineers from easily identifying malicious syscall usage through static or dynamic analysis methods.
To illustrate the practical implications of syscall-based evasion, consider a scenario where an attacker needs to inject shellcode into a remote process. Using traditional WinAPI methods like WriteProcessMemory followed by CreateRemoteThread would likely trigger multiple EDR alerts due to the suspicious combination of memory allocation, writing, and thread creation operations. In contrast, achieving the same result through direct syscalls allows the attacker to perform identical operations while evading detection mechanisms designed to catch high-level API misuse.
The sophistication of modern EDR bypass techniques continues to evolve alongside defensive capabilities. Recent advancements in behavioral analytics and machine learning-based detection have prompted red teams to develop increasingly nuanced approaches to syscall implementation, incorporating elements like randomized execution timing, environmental awareness checks, and adaptive payload delivery mechanisms. Understanding these developments is crucial for both offensive practitioners seeking to maintain operational effectiveness and defensive analysts tasked with detecting emerging threats.
Key takeaway: Direct syscalls provide a powerful mechanism for bypassing EDR solutions by communicating directly with the Windows kernel, circumventing user-mode API hooks that form the backbone of many security monitoring systems.
How Do Modern EDR Solutions Detect and Prevent Syscall Abuse?
Contemporary endpoint detection and response platforms have evolved beyond simple signature-based detection to incorporate sophisticated behavioral analysis techniques that can identify anomalous syscall patterns even when traditional API hooks are bypassed. Understanding these detection mechanisms is essential for developing effective evasion strategies that maintain operational security while achieving tactical objectives.
At the core of EDR syscall detection lies the concept of syscall tracing, which involves monitoring system service invocations through various kernel-level interfaces. Microsoft's Event Tracing for Windows (ETW) framework provides extensive logging capabilities that capture detailed information about each syscall, including caller process context, timestamp data, parameter values, and return codes. Security vendors leverage this telemetry to build behavioral models that can distinguish between legitimate and malicious syscall sequences based on factors like execution frequency, temporal patterns, and contextual indicators.
Advanced EDR solutions also employ kernel-mode drivers that hook critical system service dispatch routines, allowing them to inspect syscall parameters before they're processed by the kernel. These hooks enable real-time analysis of syscall arguments, enabling detection of suspicious combinations such as memory allocation requests targeting protected processes or unusual file operation patterns indicative of data exfiltration attempts. Some vendors extend this capability through hardware-assisted virtualization features that trap syscall instructions at the CPU level, providing complete visibility into kernel interactions regardless of user-mode obfuscation techniques.
Machine learning algorithms play an increasingly prominent role in modern EDR detection capabilities, analyzing vast datasets of syscall traces to identify subtle anomalies that might indicate malicious activity. These systems can detect deviations from established baselines, flagging unusual syscall sequences that deviate from normal application behavior patterns. For example, a legitimate browser process making frequent calls to NtAllocateVirtualMemory with RWX permissions might trigger alerts even if individual syscalls appear benign in isolation.
Behavioral correlation engines further enhance detection accuracy by analyzing syscall patterns in conjunction with other telemetry sources like network traffic, registry modifications, and file system activity. This multi-dimensional approach enables EDR systems to identify complex attack chains that might otherwise evade single-vector detection mechanisms. For instance, a sequence of syscalls related to process hollowing might be correlated with suspicious DNS queries and unusual parent-child process relationships to generate high-confidence alerts.
Despite these sophisticated detection capabilities, EDR systems face inherent limitations in their ability to comprehensively monitor all syscall activity. Performance constraints prevent continuous tracing of every system service invocation across all processes, leading to selective sampling strategies that prioritize high-risk operations or suspicious processes. Additionally, certain syscall categories like those related to graphics rendering or audio processing are often excluded from intensive monitoring due to their high volume and low threat potential.
Kernel-mode rootkits and bootkits represent another challenge for EDR detection, as they can disable or subvert syscall monitoring mechanisms entirely. While modern secure boot implementations and hypervisor-based protection schemes mitigate many of these threats, sophisticated adversaries continue to develop innovative techniques for achieving kernel-level persistence that can undermine syscall-based detection approaches.
Understanding these detection mechanisms highlights the importance of implementing comprehensive evasion strategies that address multiple layers of EDR scrutiny. Effective syscall bypass implementations must consider not only the immediate detection risks associated with individual system service calls but also the broader behavioral patterns that might reveal malicious intent through correlation analysis. This holistic approach to evasion requires careful orchestration of syscall timing, parameter selection, and execution context to minimize anomaly scores while maintaining operational effectiveness.
Key takeaway: Modern EDR solutions employ multiple layers of syscall detection including ETW tracing, kernel hooks, machine learning analysis, and behavioral correlation to identify malicious activity even when traditional API hooks are bypassed.
Step-by-Step Implementation of Direct Syscalls
Implementing direct syscalls requires careful attention to several critical components including system service number identification, parameter marshaling, calling convention adherence, and architecture-specific considerations. This section provides a comprehensive walkthrough of the technical implementation process, demonstrating practical techniques that can be applied to bypass modern EDR solutions effectively.
The first step in syscall implementation involves identifying the correct system service numbers for target operations across different Windows versions and architectures. System service numbers are essentially indices into the kernel's system service descriptor table (SSDT) that map to specific kernel functions. These numbers vary between Windows releases and between 32-bit and 64-bit architectures, requiring careful version-specific handling to ensure compatibility across target environments.
For x64 systems, system service numbers typically follow a predictable pattern where the upper bits contain version information and the lower bits specify the actual service index. Tools like IDA Pro or custom disassemblers can extract these numbers by analyzing ntdll.dll exports and tracing their internal syscall invocations. Alternatively, automated frameworks like SysWhispers3 can generate version-compatible syscall stubs by parsing Microsoft's public symbols and applying heuristic analysis to determine appropriate service numbers.
Here's an example of a basic syscall stub implementation for NtAllocateVirtualMemory:
c EXTERN_C NTSTATUS NtAllocateVirtualMemory( HANDLE ProcessHandle, PVOID* BaseAddress, ULONG_PTR ZeroBits, PSIZE_T RegionSize, ULONG AllocationType, ULONG Protect) { NTSTATUS status; asm volatile ( "mov $0x18, %%eax\n" "mov %1, %%rcx\n" "mov %2, %%rdx\n" "mov %3, %%r8\n" "mov %4, %%r9\n" "mov %5, %%r10\n" "mov %6, %%r11\n" "syscall\n" "mov %%rax, %0\n" : "=r" (status) : "r" (ProcessHandle), "r" (BaseAddress), "r" (ZeroBits), "r" (RegionSize), "r" (AllocationType), "r" (Protect) : "rax", "rcx", "rdx", "r8", "r9", "r10", "r11" ); return status; }*
This assembly implementation demonstrates the core principles of direct syscall invocation: loading the system service number into EAX, placing parameters in the appropriate registers according to the Windows x64 calling convention, executing the SYSCALL instruction, and capturing the return value from RAX. Similar patterns apply to other system services, with parameter counts and register assignments varying based on function signatures.
Parameter marshaling represents another critical aspect of successful syscall implementation, particularly when dealing with complex data structures or variable-length buffers. Many Windows system services expect pointers to user-mode memory regions containing structured data, requiring careful allocation and initialization to prevent access violations or unexpected behavior. For example, when calling NtCreateFile, the ObjectAttributes parameter must point to a properly initialized OBJECT_ATTRIBUTES structure that specifies the target file path through a UNICODE_STRING descriptor.
Memory layout considerations become especially important when implementing syscalls in position-independent code designed to run within constrained environments like reflective DLL injection scenarios. In these cases, developers must ensure that all data structures are allocated within the payload's memory space and that relative addressing modes are used appropriately to maintain relocatability. This often involves implementing custom heap management routines or leveraging existing libraries like HeapAlloc wrappers that can operate within limited memory contexts.
Error handling in syscall implementations requires careful consideration of return value semantics and failure recovery strategies. Unlike high-level APIs that provide detailed error information through GetLastError or exception handling mechanisms, raw syscalls return simple status codes that must be interpreted according to NTSTATUS conventions. Successful error handling involves mapping these codes to meaningful diagnostic information and implementing appropriate retry logic or fallback mechanisms when operations fail due to resource constraints or access restrictions.
Architecture-specific optimizations can significantly improve syscall performance and reliability across different target platforms. For instance, ARM64 implementations require different register usage patterns and instruction encodings compared to x64 systems, while WoW64 compatibility layers introduce additional complexity when executing 32-bit syscalls on 64-bit hosts. Proper implementation requires conditional compilation directives and runtime architecture detection to ensure optimal performance across diverse deployment scenarios.
Integration with existing exploit frameworks often involves wrapping syscall implementations in higher-level abstractions that provide familiar interfaces while maintaining low-level control over execution flow. This approach enables seamless substitution of traditional API calls with syscall equivalents without requiring extensive code modifications throughout the payload ecosystem. Frameworks like Cobalt Strike or Empire can benefit significantly from syscall integration by reducing their EDR detection surface while preserving functional compatibility with existing tooling.
Key takeaway: Successful syscall implementation requires precise attention to system service numbers, parameter marshaling, calling conventions, and error handling across different Windows versions and architectures.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
Advanced Stack Spoofing Techniques for Operational Security
Stack spoofing represents a crucial component of effective syscall evasion, addressing the fact that even direct kernel communication can leave detectable artifacts in execution context and call stack analysis. Modern EDR solutions employ sophisticated stack walking algorithms that can reconstruct execution history even when traditional API hooks are bypassed, making it essential for red teams to implement comprehensive stack manipulation techniques that preserve operational security.
The fundamental principle behind stack spoofing involves modifying the return address chain and stack frame layout to simulate legitimate execution paths that align with expected application behavior. This process requires careful coordination between syscall invocation points and stack manipulation routines to ensure that reverse engineering analysis reveals plausible call sequences rather than obvious evasion artifacts. Effective stack spoofing goes beyond simple return address modification to encompass comprehensive context simulation including register state preservation, stack cookie management, and exception handler setup.
Return address manipulation forms the cornerstone of basic stack spoofing implementations, involving the replacement of syscall return addresses with pointers to legitimate code locations within trusted modules. This technique leverages the fact that many EDR systems perform cursory stack analysis that focuses primarily on identifying unexpected module boundaries rather than conducting deep behavioral inspection of individual code segments. By chaining together a series of believable return addresses, attackers can create execution histories that appear consistent with normal application flow even when underlying operations involve malicious activity.
Here's an example of basic return address spoofing implemented through inline assembly:
c void SpoofedSyscall() { PVOID original_rsp; PVOID spoofed_ret_addr;
// Save original stack pointer asm volatile ("mov %%rsp, %0" : "=r" (original_rsp));
// Set spoofed return address to legitimate modulespoofed_ret_addr = GetLegitimateReturnAddress();// Manipulate stack to simulate normal callasm volatile ( "sub $0x28, %%rsp\n" // Allocate shadow space "mov %0, 0x20(%%rsp)\n" // Store spoofed return address "mov $0x18, %%eax\n" // Syscall number "syscall\n" // Execute syscall "add $0x28, %%rsp\n" // Restore stack :: "r" (spoofed_ret_addr) : "rax", "memory");}
Advanced stack spoofing extends beyond simple return address manipulation to include comprehensive frame reconstruction that simulates the complete calling convention of legitimate functions. This involves creating artificial stack frames with appropriate saved registers, parameter storage areas, and alignment padding that mirror the structure of genuine function calls. Such implementations require detailed understanding of compiler-generated code patterns and runtime library behaviors to ensure that spoofed stacks pass scrutiny under advanced analysis tools.
Exception handling simulation represents another critical aspect of sophisticated stack spoofing, as many debugging and analysis tools rely on structured exception handling (SEH) records to trace execution flow and identify异常 conditions. Properly implemented spoofing must establish believable SEH chains that correspond to the simulated call stack, preventing analysis tools from detecting inconsistencies that might indicate evasion activity. This becomes particularly important when syscalls are executed within exception handlers or other non-standard execution contexts that could raise suspicion during forensic investigation.
Register state preservation plays a vital role in maintaining credible stack spoofing across multiple syscall invocations, as inconsistent register usage patterns can reveal artificial execution flows even when individual stack frames appear legitimate. Effective implementations must carefully manage register allocation and restoration to ensure that simulated call sequences exhibit natural variability consistent with genuine application behavior. This often involves implementing pseudo-random register initialization routines that mimic the unpredictable nature of real-world code execution while maintaining deterministic behavior for reliable payload operation.
Temporal correlation techniques further enhance stack spoofing effectiveness by coordinating syscall timing with legitimate application activity to create believable execution patterns. This might involve delaying syscall execution until specific application events occur, synchronizing with system timer interrupts, or aligning with normal process scheduling intervals to avoid statistical anomalies that could trigger behavioral analysis alerts. Advanced implementations may even incorporate environmental awareness checks that adapt spoofing behavior based on detected analysis tools or system configuration characteristics.
Memory forensics resistance adds another dimension to stack spoofing considerations, as sophisticated incident response teams often conduct detailed memory analysis to reconstruct attack timelines and identify evasion techniques. Effective spoofing implementations must ensure that stack manipulation artifacts are cleaned up promptly after syscall completion, preventing residual evidence that could compromise operational security during post-incident investigation. This requires careful attention to memory allocation patterns, heap metadata consistency, and cache coherency issues that might leave detectable traces of evasion activity.
Key takeaway: Advanced stack spoofing techniques manipulate call stack artifacts and execution context to simulate legitimate program behavior, preventing detection by EDR systems that analyze return address chains and execution flow patterns.
ETW Patching Methods to Prevent Telemetry Leakage
Event Tracing for Windows (ETW) represents one of the most comprehensive telemetry collection mechanisms available to modern EDR solutions, providing detailed insights into system behavior through structured event logging and real-time monitoring capabilities. For red teams seeking to maintain operational security while conducting adversarial simulations, understanding and mitigating ETW-based detection represents a critical component of effective evasion strategy implementation.
ETW operates through a provider-consumer model where system components register as event providers that generate structured telemetry data describing various aspects of system operation. These providers include kernel-mode drivers, user-mode libraries, and application-specific instrumentation that collectively create a rich dataset describing process creation, file operations, network activity, registry modifications, and numerous other behavioral indicators. EDR vendors leverage this telemetry through dedicated consumer applications that process event streams in real-time to identify suspicious patterns and generate alert notifications.
The challenge for syscall-based evasion lies in the fact that many ETW providers operate independently of traditional API hooking mechanisms, generating telemetry directly from kernel-mode drivers or through specialized notification interfaces that bypass user-mode interception points. This means that even perfectly implemented direct syscalls can still trigger ETW events that reveal malicious activity through behavioral analysis rather than signature-based detection. Consequently, effective evasion requires proactive ETW manipulation techniques that prevent telemetry generation rather than simply avoiding hook detection.
Provider patching represents the most direct approach to ETW mitigation, involving the modification of ETW provider registration data to disable or redirect event generation for specific telemetry sources. This technique typically targets the EventRegister function within target modules, replacing provider GUIDs with invalid values or redirecting registration calls to dummy implementations that consume events without forwarding them to the ETW subsystem. Successful provider patching requires careful analysis of target module structures and runtime behavior to ensure that patched providers maintain functional compatibility while eliminating security-relevant telemetry output.
Here's an example of basic ETW provider patching through inline hooking:
c // Original ETW provider registration NTSTATUS OriginalEventRegister( LPCGUID ProviderId, PENABLECALLBACK EnableCallback, PVOID CallbackContext, PREGHANDLE RegHandle);
// Patched ETW provider registration NTSTATUS PatchedEventRegister( LPCGUID ProviderId, PENABLECALLBACK EnableCallback, PVOID CallbackContext, PREGHANDLE RegHandle) { // Check if this is a security-relevant provider if (IsSecurityProvider(ProviderId)) { // Return success without registering RegHandle = 0; return STATUS_SUCCESS; }
// Forward to original registration for non-security providers return OriginalEventRegister(ProviderId, EnableCallback, CallbackContext, RegHandle);
}
Session filtering provides an alternative approach to ETW mitigation by manipulating the event delivery pipeline rather than preventing event generation at the source. This technique involves modifying ETW session configurations to exclude specific event types or providers from security-relevant consumers while maintaining normal telemetry flow for legitimate monitoring purposes. Session filtering can be particularly effective when combined with provider patching, creating multiple layers of telemetry suppression that reduce the likelihood of detection through redundancy elimination.
Consumer interference techniques focus on disrupting the ETW event consumption process by targeting the applications and services that process telemetry data for security analysis. This might involve injecting code into EDR processes to disable specific analysis routines, modifying configuration files that control event processing behavior, or exploiting vulnerabilities in ETW infrastructure components to prevent security-relevant events from reaching their intended destinations. Consumer interference requires elevated privileges and careful implementation to avoid triggering defensive countermeasures that could compromise operational security.
Real-time event suppression represents a sophisticated ETW mitigation approach that dynamically filters events as they're generated, preventing security-relevant telemetry from propagating through the ETW pipeline without permanently disabling legitimate monitoring capabilities. This technique involves hooking low-level ETW APIs like EtwEventWrite or EtwTraceEvent to inspect event data and selectively suppress transmissions based on predefined criteria such as event type, process context, or parameter content. Real-time suppression requires careful performance optimization to avoid introducing noticeable delays that might reveal evasion activity through timing analysis.
Registry-based ETW configuration provides a persistent method for reducing telemetry generation by modifying system-wide ETW settings that control provider behavior and event delivery policies. This approach involves updating registry keys under HKLM\SYSTEM\CurrentControlSet\Services\EventLog or HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels to disable specific event channels or restrict logging verbosity for security-sensitive components. Registry-based mitigation requires administrative privileges and careful validation to ensure that changes don't interfere with legitimate system monitoring requirements.
Hardware-assisted ETW bypass techniques leverage modern CPU features like Intel PT (Processor Trace) or AMD SVM (Secure Virtual Machine) to intercept and modify ETW-related system calls at the hardware level, preventing telemetry generation through transparent redirection of execution flow. These approaches offer superior stealth characteristics compared to software-based methods but require specialized knowledge of hardware architecture and potential compatibility issues with virtualized environments commonly encountered in enterprise deployments.
Key takeaway: ETW patching prevents telemetry leakage by disabling or redirecting event generation from security-relevant providers, ensuring that syscall-based operations remain invisible to behavioral analysis systems that rely on structured event logging.
Leveraging SysWhispers3 for Automated Syscall Generation
SysWhispers3 has emerged as the premier framework for automating syscall generation and implementation across diverse Windows environments, providing red teams with sophisticated tooling that dramatically reduces the time and expertise required to develop effective EDR bypass capabilities. This open-source project represents a significant advancement over previous syscall generation approaches, incorporating machine learning-based heuristic analysis, cross-platform compatibility features, and integration support for popular exploit development frameworks.
The core innovation of SysWhispers3 lies in its ability to automatically extract system service numbers and function prototypes from official Microsoft symbol files while applying intelligent pattern recognition to resolve version-specific inconsistencies and architectural variations. Unlike earlier tools that relied on static lookup tables or manual reverse engineering efforts, SysWhispers3 employs dynamic analysis techniques that can adapt to new Windows releases and hotfix updates without requiring explicit developer intervention. This self-updating capability ensures that generated syscall implementations remain compatible with evolving target environments while maintaining optimal evasion characteristics.
Installation and basic usage of SysWhispers3 follows standard Python package management practices, with dependencies handled through pip and configuration managed through YAML-based profile files. The framework supports multiple output formats including raw assembly stubs, C++ wrapper classes, and integration-ready modules for popular exploitation frameworks like Cobalt Strike and Empire. This flexibility enables rapid prototyping and deployment across diverse operational scenarios while maintaining consistent quality standards for generated code artifacts.
Here's a typical SysWhispers3 usage example for generating syscall stubs:
bash
Install SysWhispers3
pip install syswhispers3
Generate syscall stubs for specific functions
syswhispers --functions NtAllocateVirtualMemory,NtCreateThreadEx,NtWriteVirtualMemory
--out-file syscalls.asm
--arch x64
--os win10_21h2
Compile generated assembly into object file
ml64 /c syscalls.asm /link /nodefaultlib
Advanced configuration options enable fine-grained control over syscall generation parameters including custom calling convention specifications, architecture-specific optimizations, and integration with external symbol resolution services. These features prove particularly valuable when developing cross-platform payloads that must maintain compatibility across heterogeneous target environments while preserving optimal performance characteristics. Configuration profiles can be shared and version-controlled through standard source management practices, facilitating collaborative development and ensuring consistent implementation standards across team members.
Framework integration capabilities allow SysWhispers3-generated syscalls to be seamlessly incorporated into existing exploit development workflows through plugin architectures and API interfaces that abstract away low-level implementation details. Popular frameworks like Metasploit, Cobalt Strike, and Sliver can leverage SysWhispers3 output through dedicated modules that handle syscall parameter marshaling, error handling, and compatibility adaptation automatically. This integration eliminates the need for manual syscall implementation while maintaining the evasion benefits associated with direct kernel communication.
Custom syscall provider support extends SysWhispers3's capabilities beyond standard Windows APIs to include third-party drivers, undocumented system services, and experimental kernel interfaces that might provide additional evasion opportunities. This extensibility enables red teams to develop specialized syscall implementations tailored to specific target environments or operational requirements while leveraging the framework's robust generation infrastructure. Custom providers can be developed through plugin interfaces that expose low-level syscall construction primitives while maintaining compatibility with existing configuration and output mechanisms.
Performance optimization features built into SysWhispers3 include automatic dead code elimination, register allocation optimization, and architecture-specific instruction selection that maximizes execution efficiency while maintaining minimal forensic footprint. These optimizations prove particularly important for time-sensitive operations where syscall latency might impact payload reliability or increase detection risk through anomalous timing patterns. The framework's built-in benchmarking capabilities enable developers to evaluate performance tradeoffs and select optimal implementation strategies for specific use cases.
Community collaboration aspects of SysWhispers3 facilitate knowledge sharing and collective improvement through public repositories, issue tracking systems, and contribution guidelines that encourage responsible disclosure and coordinated vulnerability research. This collaborative approach accelerates development cycles while ensuring that generated syscalls remain effective against evolving defensive technologies. Regular security audits and peer review processes help maintain high-quality standards while identifying potential improvements or alternative implementation approaches that enhance overall framework effectiveness.
Key takeaway: SysWhispers3 automates syscall generation through intelligent symbol analysis and cross-platform compatibility features, enabling rapid development of EDR-bypassing implementations without requiring deep reverse engineering expertise.
Operational Security Considerations for Red Team Engagements
Maintaining operational security during red team engagements that utilize syscall-based evasion techniques requires careful consideration of multiple interrelated factors including environmental awareness, timing coordination, artifact cleanup, and forensic resilience. These considerations become increasingly important as defensive technologies evolve to detect and analyze low-level evasion mechanisms that were previously considered undetectable through conventional monitoring approaches.
Environmental awareness represents the foundation of effective operational security, requiring thorough reconnaissance and analysis of target environment characteristics before deploying syscall-based payloads. This includes identifying active EDR solutions, determining patch levels and configuration settings, assessing network monitoring capabilities, and evaluating potential analysis sandbox environments that might affect payload behavior. Proper environmental awareness enables red teams to tailor their syscall implementations to specific target characteristics while avoiding common detection signatures or behavioral patterns that could compromise operational effectiveness.
Timing coordination plays a crucial role in maintaining operational stealth by ensuring that syscall execution occurs within normal application behavior windows and avoids statistical anomalies that might trigger behavioral analysis alerts. This involves synchronizing payload execution with legitimate system activity, respecting normal process scheduling intervals, and adapting to environmental timing characteristics that might reveal artificial execution patterns. Advanced implementations may incorporate adaptive timing mechanisms that adjust execution frequency based on observed system load or defensive monitoring intensity to maintain credible operational cover.
Artifact cleanup procedures must address the comprehensive range of forensic evidence that might remain after syscall execution, including memory residuals, temporary files, registry entries, and network connection traces that could compromise operational security during post-engagement analysis. Effective cleanup requires careful planning and implementation of systematic evidence removal routines that operate consistently across diverse target environments while avoiding actions that might themselves trigger defensive responses. This often involves implementing staged cleanup procedures that progressively eliminate evidence traces while maintaining payload functionality throughout the engagement lifecycle.
Here's an example of a basic artifact cleanup routine:
c void CleanupArtifacts() { // Remove temporary files DeleteTemporaryFiles();
// Clear event logs ClearEventLogs(L"Security"); ClearEventLogs(L"System");
// Flush DNS cacheExecuteCommand(L"ipconfig /flushdns");// Remove registry tracesDeleteRegistryKeys(HKEY_CURRENT_USER, L"Software\\MaliciousEntries");// Zero out memory allocationsSecureZeroMemory(payload_buffer, buffer_size);VirtualFree(payload_buffer, 0, MEM_RELEASE);}
Forensic resilience measures extend beyond simple artifact removal to include proactive prevention of evidence creation through careful implementation design and execution flow management. This involves implementing memory encryption for sensitive data, using legitimate system resources wherever possible, avoiding suspicious API combinations that might trigger heuristic alerts, and incorporating anti-debugging and anti-analysis techniques that prevent detailed examination of payload behavior. Forensic resilience requires ongoing evaluation and adaptation as defensive technologies evolve to counter previously effective evasion mechanisms.
Communication security considerations become particularly important when syscall-based payloads interact with external command and control infrastructure, as network traffic patterns and protocol characteristics can reveal operational details even when underlying execution mechanisms remain hidden. Effective communication security involves implementing protocol mimicry that blends malicious traffic with legitimate network activity, employing domain fronting or other traffic obfuscation techniques, and coordinating communication timing with normal application behavior patterns to avoid detection through network behavioral analysis.
Credential and identity management represents another critical aspect of operational security, particularly when syscall implementations require elevated privileges or access to protected system resources. Proper credential handling involves implementing secure storage mechanisms, avoiding plaintext credential exposure, using legitimate privilege escalation pathways when possible, and incorporating credential rotation and cleanup procedures that prevent long-term persistence of sensitive authentication material. Identity management considerations include maintaining consistent user context throughout payload execution and avoiding actions that might trigger account monitoring or anomaly detection systems.
Documentation and reporting protocols must balance the need for comprehensive operational records with security requirements that prevent sensitive information disclosure during engagement debriefings or incident response activities. This involves implementing secure documentation practices, using encrypted storage for sensitive operational data, establishing clear information classification guidelines, and coordinating with client security teams to ensure appropriate handling of discovered vulnerabilities or defensive weaknesses. Proper documentation enables effective knowledge transfer while maintaining operational integrity throughout the engagement lifecycle.
Key takeaway: Operational security for syscall-based red team engagements requires comprehensive consideration of environmental awareness, timing coordination, artifact cleanup, forensic resilience, and communication security to maintain stealth throughout the engagement lifecycle.
Key Takeaways
• Direct syscalls bypass EDR detection by communicating directly with the Windows kernel through undocumented system service numbers, circumventing user-mode API hooks that form the backbone of traditional security monitoring
• Modern EDR solutions employ sophisticated syscall detection mechanisms including ETW tracing, kernel hooks, machine learning analysis, and behavioral correlation to identify malicious activity even when traditional API monitoring is bypassed
• Successful syscall implementation requires precise attention to system service numbers, parameter marshaling, calling conventions, and error handling across different Windows versions and architectures
• Advanced stack spoofing techniques manipulate call stack artifacts and execution context to simulate legitimate program behavior, preventing detection by EDR systems that analyze return address chains and execution flow patterns
• ETW patching prevents telemetry leakage by disabling or redirecting event generation from security-relevant providers, ensuring that syscall-based operations remain invisible to behavioral analysis systems
• SysWhispers3 automates syscall generation through intelligent symbol analysis and cross-platform compatibility features, enabling rapid development of EDR-bypassing implementations without requiring deep reverse engineering expertise
• Operational security for syscall-based red team engagements requires comprehensive consideration of environmental awareness, timing coordination, artifact cleanup, forensic resilience, and communication security
Frequently Asked Questions
Q: How do direct syscalls bypass EDR detection mechanisms?
EDR bypass syscalls work by communicating directly with the Windows kernel through the SYSCALL instruction, circumventing user-mode API hooks that security software places on high-level functions. Instead of calling documented APIs like CreateFile or VirtualAlloc, attackers manually construct system service calls with appropriate parameters and service numbers, completely avoiding the monitored API layer where EDR solutions typically place their detection hooks.
Q: What are the main challenges in implementing syscall-based evasion?
The primary challenges include maintaining compatibility across different Windows versions and architectures, managing system service number variations, implementing proper parameter marshaling for complex data structures, handling error conditions gracefully, and ensuring that stack spoofing techniques don't introduce detectable artifacts that could compromise operational security during red team engagements.
Q: Can ETW-based detection be completely avoided through syscall implementation?
While direct syscalls can bypass traditional API hooking mechanisms, ETW-based detection operates at a different level by monitoring kernel-level events and behavioral patterns. Complete avoidance requires additional techniques like ETW provider patching, session filtering, or real-time event suppression to prevent telemetry generation that could reveal malicious activity through behavioral analysis rather than signature-based detection.
Q: How does SysWhispers3 improve upon previous syscall generation tools?
SysWhispers3 offers significant improvements through machine learning-based heuristic analysis for symbol resolution, cross-platform compatibility features that support multiple architectures and Windows versions, integration support for popular exploit frameworks, and self-updating capabilities that maintain compatibility with new Windows releases without requiring manual intervention or extensive reverse engineering efforts.
Q: What operational security considerations are most important for syscall-based red team operations?
The most critical operational security considerations include thorough environmental awareness to avoid detection signatures, careful timing coordination to prevent behavioral anomalies, comprehensive artifact cleanup procedures to eliminate forensic evidence, implementation of forensic resilience measures to prevent evidence creation, and secure communication protocols that blend malicious traffic with legitimate network activity to avoid network-based detection.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.