Buffer Overflow Vulnerabilities: Techniques and AI-Assisted Exploits
Buffer Overflow Vulnerabilities: Techniques and AI-Assisted Exploits
Buffer overflow vulnerabilities have been a cornerstone of software security research for decades. These vulnerabilities occur when a program writes more data to a buffer, or memory storage area, than it can hold, leading to potential memory corruption and arbitrary code execution. In this article, we'll delve into the intricacies of stack-based and heap-based buffer overflows, shellcode writing, ROP chains, and techniques to bypass modern security measures like ASLR and DEP. We'll also explore how AI coding assistants, such as those available on mr7.ai, can significantly aid in developing and understanding these exploits.
Understanding Buffer Overflow Vulnerabilities
Buffer overflows are fundamentally about memory management errors. When a program doesn't properly check the bounds of an array or buffer, it can write data beyond the allocated memory, overwriting adjacent memory locations. This can lead to a variety of security issues, including crashing the program or executing arbitrary code.
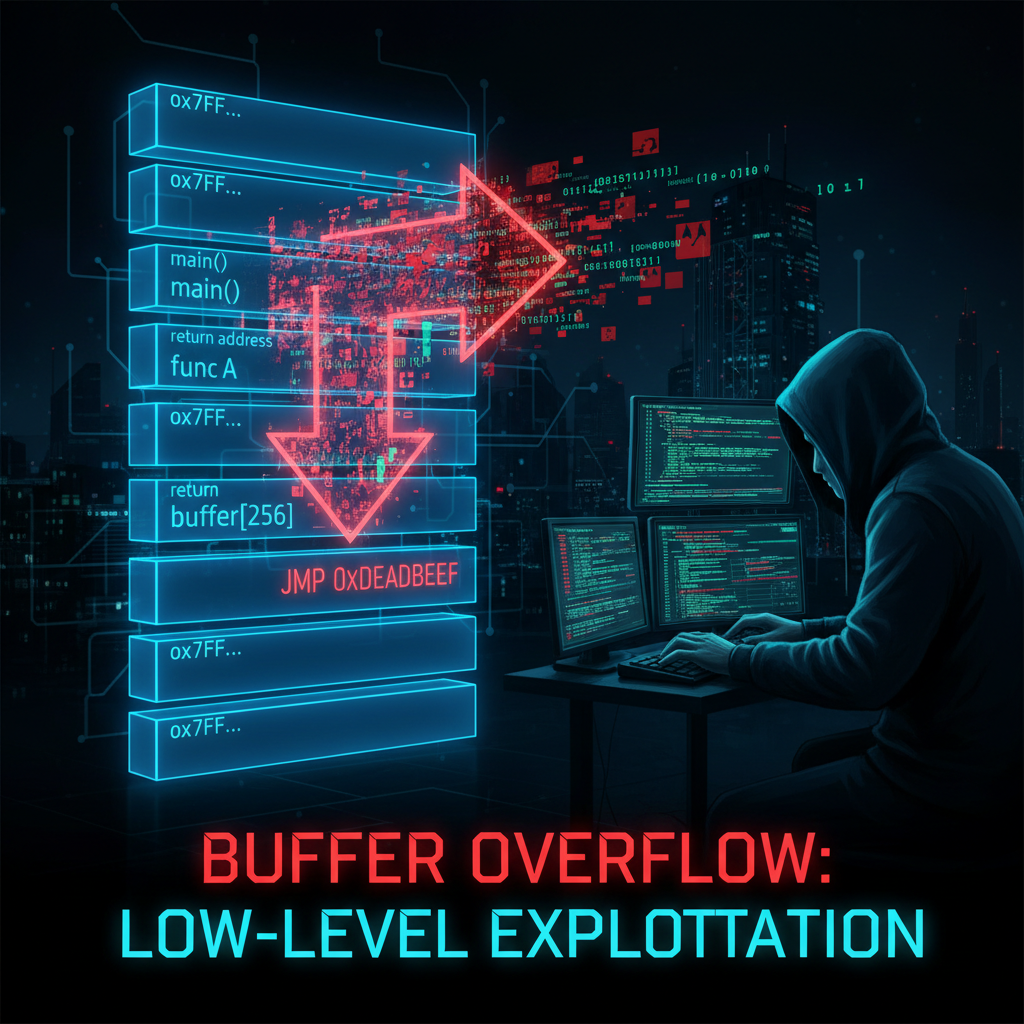
Stack-Based Buffer Overflows
Stack-based buffer overflows occur when a buffer on the stack is overwritten. The stack is a region of memory that stores local variables, function parameters, and return addresses. When a buffer on the stack is overflowed, it can overwrite these critical data, allowing an attacker to redirect the flow of execution.
Example: Simple Stack Overflow
Consider a simple C program:
c #include <stdio.h> #include <string.h>
void vulnerable_function(char str) { char buffer[16]; strcpy(buffer, str); printf("Buffer: %s\n", buffer); }
int main(int argc, char argv) { vulnerable_function(argv[1]); return 0; }
In this program, vulnerable_function copies the input string str into a 16-byte buffer without checking its length. If the input string is longer than 15 characters (plus the null terminator), it will overflow the buffer, potentially overwriting the return address on the stack.
Heap-Based Buffer Overflows
Heap-based buffer overflows occur when a buffer on the heap is overwritten. The heap is a region of memory used for dynamic memory allocation. When a buffer on the heap is overflowed, it can corrupt heap metadata, leading to arbitrary memory writes or reads.
Example: Heap Overflow in a Linked List
Consider a simple linked list implementation:
c #include <stdio.h> #include <stdlib.h> #include <string.h>
struct Node { int data; struct Node next; };
void insert_node(struct Node **head, int data) { struct Node *new_node = (struct Node *)malloc(sizeof(struct Node)); new_node->data = data; new_node->next = *head; *head = new_node; }
void print_list(struct Node *head) { struct Node *current = head; while (current != NULL) { printf("%d -> ", current->data); current = current->next; } printf("NULL\n"); }
int main() { struct Node head = NULL; insert_node(&head, 1); insert_node(&head, 2); insert_node(&head, 3); print_list(head); return 0; }
In this program, if the insert_node function is modified to write more data than the allocated size of new_node, it can overflow the heap, corrupting the linked list structure and potentially leading to arbitrary code execution.
Writing Shellcode for Buffer Overflows
Shellcode is a small piece of code used as the payload in the exploitation of a software vulnerability. It is typically written in assembly language and is designed to perform a specific task, such as spawning a shell.
Crafting Basic Shellcode
A simple shellcode for spawning a shell on a Linux system might look like this:
assembly section .text global start
start: xor eax, eax push eax mov ebx, 0xb mov ecx, esp mov edx, eax int 0x80 ret
This shellcode uses the execve system call to spawn a shell. The int 0x80 instruction is used to make the system call, and the arguments are set up on the stack.
Encoding Shellcode
To make shellcode more robust, it is often encoded to avoid null bytes and other problematic characters. A common encoding technique is XOR encoding.
Example: XOR Encoding
python shellcode = b"\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x53\x89\xe1\xb0\x0b\xcd\x80" encoded = b"" for byte in shellcode: encoded += bytes([byte ^ 0xaa]) print(encoded)
This Python script XOR encodes the shellcode with the key 0xaa, making it more suitable for use in exploits.
Return-Oriented Programming (ROP) Chains
Return-Oriented Programming (ROP) is a technique used to execute arbitrary code in the presence of security measures like DEP (Data Execution Prevention). ROP chains are constructed by chaining together small code snippets, called gadgets, that end with a ret instruction.
Building ROP Chains
To build a ROP chain, you need to identify useful gadgets in the binary. Gadgets are short sequences of instructions that end with a ret and perform a useful operation, such as moving data between registers.
Example: Finding Gadgets
bash ROPgadget --binary /path/to/binary --only "ret"
This command uses ROPgadget to find all gadgets in a binary that end with a ret instruction. You can then use these gadgets to construct a ROP chain that performs the desired operation.
Bypassing ASLR and DEP
ASLR (Address Space Layout Randomization) and DEP (Data Execution Prevention) are modern security measures designed to mitigate buffer overflow exploits. ASLR randomizes the memory addresses used by system and application processes, making it harder to predict the location of code. DEP prevents data from being executed as code.
Bypassing ASLR
To bypass ASLR, you can use information leaks to determine the base address of the binary at runtime. This can be done by reading a known address and calculating the base address from it.
Bypassing DEP
To bypass DEP, you can use ROP chains to construct a code path that executes data as code. This involves chaining together gadgets that perform useful operations, such as moving data between registers and making system calls.
Try it yourself: Use mr7.ai's AI models to automate this process, or download mr7 Agent for local automated pentesting. Start free with 10,000 tokens.
AI-Assisted Exploit Development with mr7.ai
AI coding assistants, such as those available on mr7.ai, can significantly enhance the process of developing and understanding buffer overflow exploits. These tools can help generate shellcode, identify gadgets, and even construct ROP chains.
Generating Shellcode with AI
AI tools can generate shellcode tailored to specific architectures and operating systems. For example, you can use an AI assistant to generate shellcode for spawning a shell on a 64-bit Linux system.
Example: AI-Generated Shellcode
bash 0Day Coder: Generate shellcode for spawning a shell on 64-bit Linux.
This command would prompt the AI assistant to generate the appropriate shellcode, saving you time and effort.
Identifying Gadgets with AI
AI assistants can also help identify useful gadgets in a binary for constructing ROP chains. By analyzing the binary, the AI can suggest gadgets that perform specific operations, such as moving data between registers.
Example: AI-Generated Gadgets
bash 0Day Coder: Find gadgets in /path/to/binary that move data between registers.
This command would prompt the AI assistant to analyze the binary and suggest relevant gadgets.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder - your AI coding assistant for security tools.
Advanced Exploitation Techniques
As security measures evolve, so do the techniques used to exploit buffer overflow vulnerabilities. Advanced techniques include format string exploits, heap spraying, and use-after-free vulnerabilities.
Format String Exploits
Format string vulnerabilities occur when user input is used as a format string in a function like printf. This can lead to reading or writing arbitrary memory locations.
Example: Format String Vulnerability
c #include <stdio.h>
void vulnerable_function(char format) { printf(format); }
int main(int argc, char argv) { vulnerable_function(argv[1]); return 0; }
In this program, if the input string contains format specifiers (e.g., %x), it can be used to read or write arbitrary memory locations.
Heap Spraying
Heap spraying is a technique used to increase the likelihood of successful exploitation by filling the heap with shellcode or ROP gadgets. This is particularly useful in the presence of ASLR, as it increases the chances of the exploit landing in a executable region of memory.
Example: Heap Spraying in JavaScript
javascript function spray() { var sprayArray = new Array(1000000); for (var i = 0; i < sprayArray.length; i++) { sprayArray[i] = "A".repeat(0x400); } } spray();
This JavaScript code sprays the heap with a large number of 0x400-byte buffers, increasing the likelihood of a successful exploit.
Use-After-Free Vulnerabilities
Use-after-free vulnerabilities occur when a program continues to use a pointer after the memory it points to has been freed. This can lead to arbitrary code execution if the freed memory is reused for another purpose.
Example: Use-After-Free in C
c #include <stdio.h> #include <stdlib.h>
int main() { int *ptr = (int *)malloc(sizeof(int)); *ptr = 42; free(ptr); printf("%d\n", *ptr); // Use-after-free return 0; }
In this program, the pointer ptr is used after it has been freed, leading to undefined behavior and potential security vulnerabilities.
Ready to Level Up Your Security Research?
Get 10,000 free tokens and start using KaliGPT, 0Day Coder, DarkGPT, and OnionGPT today. No credit card required!
Key Takeaways
- Buffer overflows occur when data exceeds a buffer's capacity, leading to memory corruption and potential arbitrary code execution, affecting both stack and heap memory.
- Understanding stack-based and heap-based buffer overflows is crucial for identifying different exploitation vectors and mitigation strategies.
- Shellcode writing and Return-Oriented Programming (ROP) chains are advanced techniques used by attackers to achieve arbitrary code execution after a successful buffer overflow.
- Effective mitigation involves secure coding practices, memory safety features, and dynamic analysis to prevent buffer overflow vulnerabilities.
- AI-assisted tools are emerging to help identify, analyze, and even generate exploits for buffer overflow vulnerabilities, streamlining the discovery and patching process.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: What is the fundamental difference between stack-based and heap-based buffer overflows?
Stack-based buffer overflows occur in the stack memory, typically affecting local variables and return addresses, making them relatively easier to exploit for control flow hijacking. Heap-based overflows, on the other hand, corrupt data structures on the heap, which can be more complex to exploit but offer avenues for data manipulation or arbitrary write primitives.
Q: How do ROP chains enable arbitrary code execution even with non-executable stack protections?
ROP chains bypass non-executable stack protections (NX bit) by chaining together small snippets of existing executable code within the program's memory, called "gadgets." Each gadget performs a small operation, and by carefully arranging their addresses on the stack, an attacker can execute a sequence of operations to achieve arbitrary code execution without injecting new code.
Q: What role does shellcode play in exploiting buffer overflow vulnerabilities?
Shellcode is a small piece of assembly code designed to perform a specific task, often to spawn a command shell on the compromised system. In buffer overflow exploitation, shellcode is typically injected into memory and then executed by redirecting the program's control flow to its starting address, giving the attacker control over the system.
Q: How can AI tools help with identifying and exploiting buffer overflow vulnerabilities?
AI tools like KaliGPT can assist in generating proof-of-concept exploits based on vulnerability patterns, while mr7 Agent can automate the analysis of binary code to pinpoint potential buffer overflow locations and suggest mitigation strategies. These tools streamline the process of discovering and understanding these complex vulnerabilities, and can even help in crafting sophisticated ROP chains or shellcode.
Q: What are some initial steps to take when trying to understand and defend against buffer overflow attacks?
To get started, begin by studying common buffer overflow patterns in C/C++ and experiment with simple examples in a controlled environment. Utilizing platforms like mr7.ai, you can leverage free tokens to access AI-powered tools that can help analyze code for vulnerabilities and understand potential exploitation techniques, accelerating your learning curve in both offense and defense.
Ready to Level Up Your Security Research?
Get 10,000 free tokens and start using KaliGPT, 0Day Coder, DarkGPT, OnionGPT, and mr7 Agent today. No credit card required!