Beginner's Guide to Malware Analysis: Static & Dynamic Techniques
Beginner's Guide to Malware Analysis: Static & Dynamic Techniques
Malware analysis is a critical skill for cybersecurity professionals, helping to identify, understand, and mitigate threats. This guide will walk you through the fundamentals of static and dynamic analysis, sandboxing, and how AI assistants can streamline your work.
What is Malware Analysis?
Malware analysis is the process of examining malicious software to understand its behavior, capabilities, and impact. It involves reverse engineering and dissecting the code to uncover how it operates and what it targets.
Static Malware Analysis
Static analysis involves examining the malware without executing it. This is the first step in malware analysis and helps to quickly identify potential threats.
Key Techniques
- File Inspection: Check file properties, headers, and metadata.
- String Analysis: Extract and analyze text strings within the file to identify URLs, IP addresses, or keywords.
- Code Disassembly: Convert the binary code into assembly language to understand the program's logic.
Tools for Static Analysis
- IDA Pro: A powerful disassembler and debugger.
- Ghidra: A software reverse engineering suite developed by the NSA.
- KaliGPT: mr7.ai's AI tool can assist in identifying suspicious code patterns during static analysis.
Dynamic Malware Analysis
Dynamic analysis involves executing the malware in a controlled environment to observe its behavior in real-time.
Key Techniques
- Behavior Monitoring: Track system changes, network activity, and file modifications.
- API Monitoring: Log and analyze API calls made by the malware.
- Debugging: Step through the code execution to understand its flow and identify key functions.
Tools for Dynamic Analysis
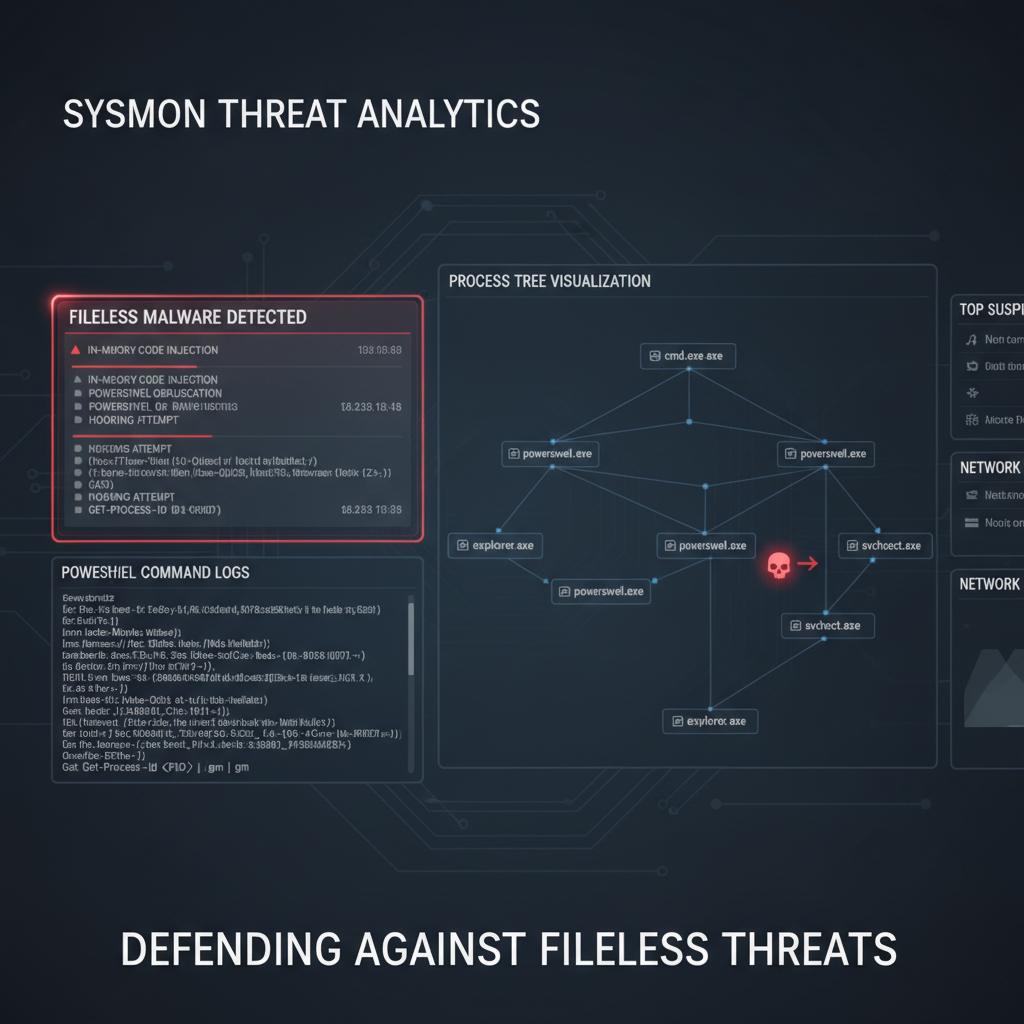
- Process Monitor: A sysinternals tool for monitoring real-time file system, registry, and process activity.
- Wireshark: A network protocol analyzer to capture and inspect network traffic.
- DarkGPT: mr7.ai's AI can help correlate dynamic analysis data to identify malicious patterns.
Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
Sandboxing
Sandboxing provides an isolated environment to run and observe malware without affecting the host system.
Benefits of Sandboxing
- Isolation: Contains the malware to prevent it from infecting other systems.
- Observability: Allows for detailed monitoring of malware behavior.
- Reproducibility: Creates a consistent environment for analysis and testing.
Popular Sandbox Tools
- Cuckoo Sandbox: An open-source automated malware analysis system.
- Any.Run: A cloud-based sandbox for interactive malware analysis.
- OnionGPT: mr7.ai's AI can enhance sandbox analysis by providing insights into the observed behaviors.
How AI Assists in Malware Analysis
AI assistants like those offered by mr7.ai can significantly enhance malware analysis by automating repetitive tasks and providing deeper insights.
AI-Powered Analysis with mr7.ai
- KaliGPT: Assists in static analysis by identifying suspicious code patterns and providing context.
- 0Day Coder: Helps in discovering zero-day vulnerabilities by analyzing code for potential exploits.
- DarkGPT: Enhances dynamic analysis by correlating behavior data and predicting malicious intent.
- OnionGPT: Provides insights into sandbox analysis by interpreting observed behaviors and suggesting further investigation paths.
Conclusion
Malware analysis is a complex but rewarding field that combines technical skills with a deep understanding of cyber threats. By leveraging both static and dynamic analysis techniques, along with the power of AI, you can become a more effective and efficient security researcher.
🔓 Unlock Your Security Potential
Stop spending hours on manual tasks. Let AI handle the heavy lifting while you focus on what matters - finding vulnerabilities.
Key Takeaways
- Malware analysis involves both static (examining code without execution) and dynamic (observing behavior during execution) techniques to understand threats.
- Static analysis helps identify indicators like strings, imports, and packers, offering a preliminary understanding without risking system infection.
- Dynamic analysis, often performed in a sandbox, reveals runtime behavior such as file modifications, network communications, and process injections.
- Sandboxing is crucial for dynamic analysis, providing an isolated and controlled environment to safely execute and observe malware.
- Combining static and dynamic analysis offers a comprehensive view of malware, allowing for more effective threat identification and mitigation.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: What is the primary difference between static and dynamic malware analysis?
Static analysis examines malware without executing it, focusing on code structure, strings, and metadata to infer its potential behavior. Dynamic analysis, conversely, involves running the malware in a controlled environment to observe its actual runtime actions, such as network connections or file system changes. Both methods are complementary and provide different insights into the malware's functionality.
Q: Why is sandboxing essential for dynamic malware analysis?
Sandboxing provides an isolated and controlled environment where malware can be executed safely without posing a threat to the analyst's host system or network. This allows for observation of its full behavior, including network communication, file system modifications, and process interactions, without risk of infection or propagation. It's a critical safety measure for understanding malicious payloads.
Q: What are some common indicators looked for during static analysis?
During static analysis, common indicators include imported functions (e.g., API calls related to file I/O, network, or registry manipulation), embedded strings (URLs, error messages, filenames), and packing signatures. Identifying these elements can provide clues about the malware's capabilities, target systems, and potential communication channels before execution.
Q: How can AI tools help with malware analysis, specifically static and dynamic techniques?
AI tools like [mr7.ai]'s KaliGPT can assist by automating the parsing of static analysis data, identifying patterns in code, or summarizing complex behavioral reports from dynamic analysis. mr7 Agent could potentially automate sandbox setup, execute malware, and extract key indicators, significantly streamlining the analysis process and reducing manual effort.
Q: What's the best way for a beginner to start practicing malware analysis?
A great way to start is by setting up a virtual lab environment with a clean Windows VM and a Linux distribution like REMnux, then practicing with safe malware samples (e.g., from public repositories). Begin with basic static analysis tools like strings and PE-bear, then move to dynamic analysis using a sandbox like Cuckoo Sandbox. You can also try [mr7.ai]'s free tokens to experiment with AI-powered analysis assistance.
Automate Your Penetration Testing with mr7 Agent
mr7 Agent is your local AI-powered penetration testing automation platform. Automate bug bounty hunting, solve CTF challenges, and run security assessments - all from your own device.