AI Ransomware Negotiation Detection Through Behavioral Analysis
AI Ransomware Negotiation Detection Through Behavioral Analysis
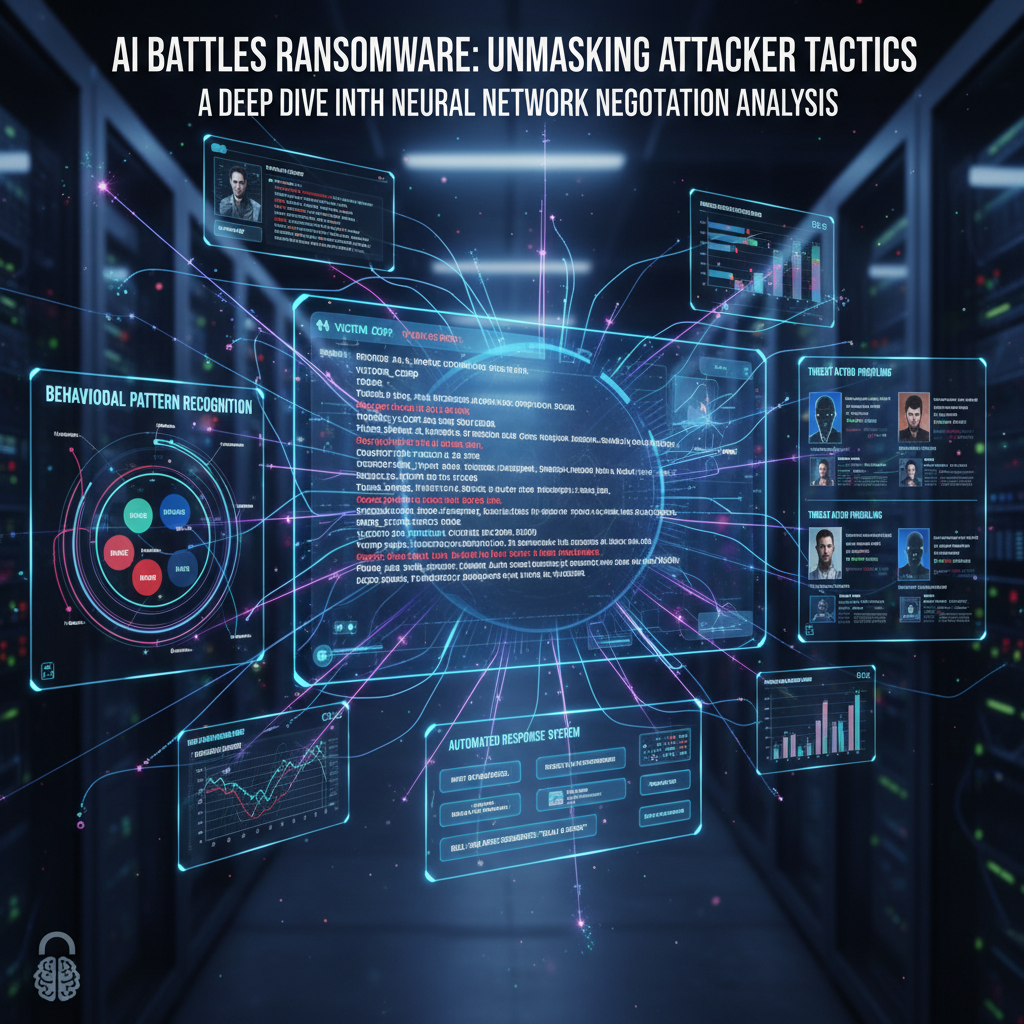
In 2026, ransomware attacks have evolved beyond simple encryption schemes into sophisticated multi-stage campaigns involving automated negotiation processes. Threat actors now leverage chatbots, social engineering tactics, and psychological manipulation to maximize their payouts while minimizing detection windows. Traditional security measures often fall short against these adaptive adversaries, necessitating advanced solutions powered by artificial intelligence.
This shift has led to the emergence of AI-driven behavioral analysis as a critical component in modern incident response strategies. By analyzing communication patterns between attackers and victims during negotiation phases, security teams can detect ongoing compromises, predict attack trajectories, and potentially intervene before financial losses occur. Machine learning models trained on historical ransomware negotiations enable real-time identification of suspicious interactions across various channels including email, messaging platforms, and dark web forums.
Natural Language Processing (NLP) plays a pivotal role in extracting meaningful insights from unstructured text-based communications. Techniques such as sentiment analysis, linguistic fingerprinting, and discourse modeling allow security professionals to profile threat actors based on their writing styles, emotional states, and strategic approaches. These profiles aid in attribution efforts and help tailor defensive responses accordingly.
Furthermore, integrating deception technologies with AI-powered monitoring systems creates layered defense mechanisms that confuse attackers and buy time for responders. Automated response systems equipped with contextual understanding capabilities can engage with negotiators without revealing victim awareness, gathering intelligence while delaying payment decisions.
Throughout this article, we'll explore technical implementations of these concepts using cutting-edge tools available through mr7.ai. Whether you're building custom detection pipelines or enhancing existing SOC workflows, understanding how AI transforms ransomware negotiation detection is essential for staying ahead of evolving threats.
How Does AI Detect Ransomware Negotiation Attempts?
Detecting ransomware negotiation attempts requires distinguishing between legitimate communications and malicious interactions orchestrated by cybercriminals. AI systems accomplish this through multi-layered behavioral analysis frameworks that examine temporal patterns, linguistic characteristics, network behaviors, and contextual metadata associated with potential negotiations.
Machine learning algorithms typically begin by establishing baseline communication norms within an organization. This involves collecting anonymized samples of normal business correspondence across various channels including email servers, collaboration tools, and customer support portals. Statistical features extracted from these datasets serve as reference points for identifying anomalous activity.
Temporal pattern recognition focuses on detecting unusual timing sequences indicative of automated bot interactions or coordinated human activities. For instance, repeated message exchanges occurring at fixed intervals might suggest scripted negotiation procedures commonly employed by ransomware groups. Similarly, sudden spikes in outbound communications following known breach events could signal active negotiation phases.
Linguistic analysis leverages NLP techniques to evaluate textual content for signs of coercion, urgency, and financial demands characteristic of ransomware negotiations. Sentiment scoring algorithms assign numerical values representing emotional tones present in messages, helping differentiate between routine inquiries and threatening statements. Additionally, keyword spotting mechanisms flag specific terms frequently used in extortion scenarios such as "decrypt", "payment", "bitcoin", and "deadline".
Network-level behavioral indicators include unexpected protocol usage, irregular data transfer volumes, and connections to known malicious domains or IP addresses. Deep packet inspection combined with flow analysis enables identification of encrypted tunnels commonly utilized during covert negotiations. Furthermore, DNS query logs reveal attempts to access command-and-control infrastructure linked to ransomware operations.
Contextual metadata encompasses supplementary information surrounding each communication event, including sender reputation scores, geolocation data, device fingerprints, and historical interaction records. Correlating these factors provides holistic views of communication dynamics, enabling more accurate risk assessments.
Implementation-wise, organizations often deploy hybrid architectures combining rule-based filters with supervised learning classifiers. Initial screening rules eliminate obviously benign traffic while flagging borderline cases for deeper examination. Supervised models trained on labeled datasets containing both positive (negotiation-related) and negative (non-negotiation) examples then classify remaining candidates according to predefined confidence thresholds.
For example, consider implementing a basic logistic regression classifier using Python and scikit-learn:
python from sklearn.linear_model import LogisticRegression from sklearn.feature_extraction.text import TfidfVectorizer import pandas as pd
df = pd.read_csv('communications.csv') # Columns: 'text', 'label' vectorizer = TfidfVectorizer(max_features=1000) X = vectorizer.fit_transform(df['text']) y = df['label']
model = LogisticRegression() model.fit(X, y)
new_message = ["We've encrypted your files. Pay us 1 BTC within 48 hours."] transformed_msg = vectorizer.transform(new_message) prediction = model.predict(transformed_msg) print(f"Prediction: {prediction}")
Try it yourself: Use mr7.ai's AI models to automate this process, or download mr7 Agent for local automated pentesting. Start free with 10,000 tokens.
Actionable takeaway: Implement multi-dimensional behavioral analysis combining temporal, linguistic, and network signals to effectively detect ransomware negotiation attempts in real-time environments.
What Machine Learning Models Identify Negotiation Patterns?
Effective ransomware negotiation detection relies heavily on selecting appropriate machine learning models capable of capturing complex behavioral patterns inherent in adversarial communications. Different algorithmic families excel under varying conditions, making informed model selection crucial for achieving optimal performance metrics.
Supervised learning approaches dominate current deployments due to their ability to generalize from annotated training sets. Support Vector Machines (SVMs) demonstrate strong classification accuracy when dealing with high-dimensional feature spaces typical in NLP applications. Their robustness against overfitting makes SVMs particularly suitable for scenarios involving limited labeled data availability.
Random Forest ensembles offer another popular choice thanks to built-in feature importance rankings and resistance to noise corruption. Ensemble methods inherently reduce variance compared to single decision trees, leading to improved stability during production deployment. Moreover, Random Forests handle mixed data types gracefully, accommodating combinations of categorical variables alongside continuous measurements.
Deep learning architectures represent emerging frontiers in negotiation pattern recognition. Convolutional Neural Networks (CNNs) applied to tokenized text sequences capture local dependencies missed by traditional bag-of-words representations. Meanwhile, Recurrent Neural Networks (RNNs) excel at modeling sequential relationships present in conversational dialogues. Long Short-Term Memory (LSTM) variants further enhance memory retention capabilities, allowing networks to maintain context across extended message chains.
Unsupervised learning techniques complement supervised paradigms by uncovering hidden structures within unlabeled datasets. Clustering algorithms group similar communication instances together, facilitating discovery of previously unknown negotiation clusters or novel attack vectors. Principal Component Analysis (PCA) dimensionality reduction helps visualize high-dimensional embeddings generated by deep neural networks, supporting interpretability efforts.
Anomaly detection models operate independently of explicit labels, focusing instead on identifying outliers deviating significantly from established baselines. Isolation Forests isolate abnormal samples by recursively partitioning input space until isolated nodes contain only singular observations. Autoencoders reconstruct original inputs from compressed latent representations; reconstruction errors exceeding threshold values indicate potential anomalies warranting investigation.
Table comparing common ML models for negotiation detection:
| Model Type | Strengths | Weaknesses | Best Use Case |
|---|---|---|---|
| SVM | High accuracy, robust | Computationally intensive | Limited labeled data |
| Random Forest | Feature ranking, noise tolerant | Less interpretable | Mixed variable types |
| LSTM | Sequential dependency modeling | Requires large datasets | Conversational analysis |
| Isolation Forest | Label-free anomaly detection | May miss subtle deviations | Baseline deviation monitoring |
| Autoencoder | Dimensionality reduction | Reconstruction quality dependent | Data visualization |
Ensemble stacking combines predictions from multiple base learners to produce final outputs. Meta-classifiers weigh individual contributions dynamically based on observed performances, creating adaptive ensemble configurations optimized for changing threat landscapes. Stacking frameworks prove especially useful when incorporating diverse modalities such as text, audio, and video streams simultaneously.
Consider implementing an ensemble approach using VotingClassifier in scikit-learn:
python from sklearn.ensemble import RandomForestClassifier, VotingClassifier from sklearn.svm import SVC
rf_clf = RandomForestClassifier(n_estimators=100) svm_clf = SVC(probability=True)
ensemble = VotingClassifier(estimators=[('rf', rf_clf), ('svm', svm_clf)], voting='soft') ensemble.fit(X_train, y_train)
predictions = ensemble.predict_proba(X_test) final_prediction = np.argmax(predictions, axis=1)
Key insight: Select machine learning models based on data characteristics, computational resources, and desired interpretability levels to maximize effectiveness in detecting ransomware negotiation patterns.
How Can Natural Language Processing Profile Threat Actors?
Natural Language Processing (NLP) serves as the cornerstone technology enabling detailed profiling of threat actors engaged in ransomware negotiations. By systematically dissecting linguistic artifacts left behind during digital conversations, security analysts gain unprecedented visibility into adversary motivations, skill levels, cultural backgrounds, and operational preferences.
Stylometric analysis examines writing styles unique to individuals or groups, functioning similarly to handwriting analysis in forensic investigations. Metrics encompass vocabulary diversity ratios, sentence length distributions, punctuation frequency counts, and grammatical error rates. Consistent deviations from standard English norms may indicate non-native speakers attempting to mask identities through deliberate obfuscation techniques.
Sentiment analysis quantifies emotional undertones embedded within textual communications. Lexicon-based approaches utilize precompiled dictionaries mapping words to affective dimensions like valence, arousal, and dominance. Alternatively, machine learning models trained on emotion-labeled corpora achieve higher precision when classifying nuanced sentiments expressed through sarcasm, irony, or coded language.
Discourse structure evaluation reveals organizational coherence present in multi-message exchanges. Coherence measures assess logical flow consistency, argument progression logic, and persuasive strategy employment. Disjointed narratives lacking clear objectives often originate from less experienced operators relying heavily on template scripts rather than improvisational skills.
Semantic similarity computations compare incoming messages against previously encountered utterances stored in knowledge bases. Cosine similarity calculations performed on TF-IDF weighted term matrices efficiently retrieve semantically related historical entries, accelerating response generation cycles during live engagements. Embedding-based methods employing Word2Vec or BERT-derived vector spaces yield superior results when handling polysemous expressions requiring contextual disambiguation.
Topic modeling discovers latent themes underlying collections of documents without prior categorization assumptions. Latent Dirichlet Allocation (LDA) decomposes document-term matrices into probabilistic topic mixtures, assigning topic probabilities to each analyzed piece of text. Dominant topics emerge naturally reflecting prevalent concerns discussed throughout negotiation sessions, ranging from technical troubleshooting assistance requests to payment method verification instructions.
Language identification tools automatically determine spoken/written languages exhibited in intercepted communications. Open-source libraries like langdetect or fastText rapidly classify texts belonging to dozens of supported tongues, streamlining triage workflows involving international jurisdictions. Accurate language tagging facilitates subsequent translation services integration, expanding reach beyond monolingual analyst pools.
Here's a sample implementation using spaCy for stylometric feature extraction:
python import spacy from collections import Counter
nlp = spacy.load("en_core_web_sm") text = "Your files are encrypted. Send 1 BTC to receive decryption key." doc = nlp(text)
features = { 'sentence_count': len(list(doc.sents)), 'token_count': len([token for token in doc if not token.is_punct]), 'pos_distribution': Counter([token.pos_ for token in doc]), 'unique_words': len(set([token.lemma_.lower() for token in doc if not token.is_stop])) } print(features)
Try it yourself: Use mr7.ai's AI models to automate this process, or download mr7 Agent for local automated pentesting. Start free with 10,000 tokens.
Practical tip: Combine multiple NLP techniques iteratively to build comprehensive threat actor profiles informing tactical decision-making throughout negotiation lifecycles.
How Do Automated Response Systems Work in Negotiation Scenarios?
Automated response systems play increasingly vital roles in managing initial stages of ransomware negotiations while preserving responder bandwidth for critical interventions. These intelligent agents simulate human-like reactions tailored specifically toward prolonging engagement timelines, extracting additional intelligence, and ultimately reducing likelihood of successful monetary transfers.
Chatbot architectures designed for negotiation contexts incorporate state management components responsible for tracking conversation history, maintaining session persistence, and updating internal belief states regarding opponent intentions. Finite State Machines (FSMs) define permissible transitions between discrete dialogue stages, ensuring coherent progression aligned with predetermined engagement protocols. Hierarchical Task Network (HTN) planners extend FSM functionality by introducing conditional branching paths responsive to dynamic environmental changes.
Intent recognition modules parse incoming user queries to infer underlying goals driving particular actions. Intent classification employs either slot-filling mechanisms extracting structured parameters from unstructured sentences or semantic parsing techniques converting natural language constructs into executable programmatic calls. Accurate intent resolution forms foundation upon which personalized replies depend, influencing overall engagement effectiveness.
Dialogue policy engines govern selection criteria determining which predefined templates or dynamically generated responses should be dispatched next. Reinforcement Learning (RL) algorithms optimize policies by rewarding desirable outcomes such as extended interaction durations or increased disclosure frequencies. Policy gradient methods update action probability distributions directly, avoiding reliance on value function estimations prone to instability issues.
Response generation subsystems synthesize natural sounding utterances matching selected templates while incorporating relevant contextual elements gathered throughout preceding interactions. Template-based generators substitute placeholders with actual values retrieved from conversation memory stores. Neural generation models trained on massive dialogue corpora produce fluent continuations mimicking authentic conversational flows albeit sometimes lacking factual grounding guarantees.
Integration layers connect external APIs providing supplementary functionalities like cryptocurrency rate conversion calculators, deadline reminder schedulers, and secure file upload endpoints. Middleware orchestrators route requests appropriately among constituent microservices, abstracting complexity away from core negotiation logic handlers.
Example pseudo-code illustrating basic automated response workflow:
function handleNegotiationMessage(message): currentState = getSessionState(sessionId) intent = getIntent(message)
switch(intent.type): case "demand_payment": responseTemplate = selectPaymentDelayTemplate(currentState.delayLevel) nextState = advanceToNextStage(currentState) break case "request_decryption": responseTemplate = acknowledgeRequestWithConditions() scheduleFollowUp(24h) break default: responseTemplate = fallbackGenericReply()
reply = generateResponse(responseTemplate, message.context)sendReply(reply)updateSessionState(nextState)Security considerations mandate rigorous validation checks applied to all externally sourced inputs preventing injection attacks targeting backend infrastructure. Input sanitization routines strip potentially harmful characters sequences before passing sanitized strings downstream processing pipelines. Rate limiting controls prevent abuse stemming from automated spamming attempts originating from compromised accounts.
Strategic takeaway: Design automated response systems balancing realism with delay-inducing objectives to maximize intelligence collection opportunities while minimizing chances of premature resolution.
How Does Deception Technology Enhance Negotiation Monitoring?
Deception technology introduces deliberate misinformation layers aimed at confusing adversaries and exposing reconnaissance activities undertaken prior to formal negotiation initiation. When integrated seamlessly into broader monitoring ecosystems, deceptive assets act as tripwires triggering alerts whenever unauthorized access occurs, thereby alerting defenders about impending compromise attempts.
Honeytokens represent lightweight decoy objects strategically placed inside sensitive directories, databases, configuration files, or application source codes. Modifications affecting honeytoken contents instantly trigger notifications sent directly to designated incident response teams. Unlike honeypots requiring dedicated hardware installations, honeytokens impose minimal overhead costs while offering granular control over placement locations.
Decoy networks consist of virtualized infrastructure mimicking real enterprise topologies complete with fake servers, workstations, printers, routers, switches, firewalls, load balancers, and domain controllers. Network segmentation policies ensure realistic inter-device connectivity mirroring production setups closely enough to fool casual observers yet sufficiently distinct to distinguish between authorized personnel and intruders.
Bait documents contain misleading information intentionally crafted to entice curious explorers towards fabricated storylines. Phony spreadsheets listing nonexistent employee salaries, dummy contracts referencing fictional clients, and forged meeting minutes describing imaginary boardroom discussions all contribute towards constructing believable narratives designed to waste attacker time.
Canary files monitor read/write/delete operations executed against protected resources, logging timestamps, usernames, hostnames, process IDs, and full execution stacks involved in unauthorized accesses. Tamper-resistant checksums embedded within canary binaries detect modifications indicating compromise status changes warranting immediate escalation procedures.
Table comparing deception techniques effectiveness:
| Technique | Detection Coverage | False Positive Rate | Resource Requirements | Stealth Level |
|---|---|---|---|---|
| Honeytokens | Medium | Low | Minimal | High |
| Decoy Networks | High | Very Low | Moderate-High | Medium |
| Bait Documents | Low-Medium | Medium | Low | High |
| Canary Files | High | Very Low | Minimal | High |
Digital watermarking embeds imperceptible identifiers within seemingly innocuous electronic materials distributed throughout corporate networks. Watermarks survive copy-paste operations, screen captures, printouts, scans, OCR conversions, compression/decompression cycles, and numerous other transformations preserving traceability back to originating sources.
Behavioral lures exploit cognitive biases influencing decision-making processes guiding adversarial choices during exploration phases. Psychological triggers rooted in curiosity, greed, authority respect, scarcity perception, social proof, commitment reciprocity, loss aversion, and urgency exploitation manipulate targets into performing desired actions beneficial to defender interests.
Sample implementation deploying honeytoken in Python script:
python import os import hashlib import smtplib from email.mime.text import MIMEText
def create_honeytoken(path, alert_email): fake_data = b"CONFIDENTIAL_SALARY_INFO" with open(path, 'wb') as f: f.write(fake_data) hash_value = hashlib.sha256(fake_data).hexdigest() return hash_value
def check_honeytoken_integrity(path, original_hash): with open(path, 'rb') as f: current_data = f.read() current_hash = hashlib.sha256(current_data).hexdigest() if current_hash != original_hash: send_alert(original_hash[:8])
def send_alert(token_id): msg = MIMEText(f"Honeytoken {token_id} accessed!") msg['Subject'] = "Security Alert" msg['From'] = "[email protected]" msg['To'] = "[email protected]"
server = smtplib.SMTP('localhost') server.send_message(msg) server.quit()
Operational insight: Deploy heterogeneous deception assets spanning physical, logical, and behavioral domains to create comprehensive early warning systems deterring premature negotiation initiations.
What Are Real-World Examples of Successful Intervention?
Real-world success stories highlight practical applications where AI-enhanced negotiation monitoring delivered measurable improvements in incident containment times, evidence preservation qualities, and overall organizational resilience metrics. These case studies showcase tangible benefits derived from investing in proactive detection capabilities centered around behavioral analytics.
Case Study #1: Financial Institution Prevents Multi-Million Dollar Loss A multinational bank detected anomalous email thread activity suggesting ongoing ransomware negotiation shortly after experiencing targeted phishing campaign infiltration. Utilizing internally developed LSTM-based classifier trained on past incidents, security operations center personnel identified telltale linguistic markers consistent with known criminal syndicates operating regionally.
Upon confirming suspicion via cross-referencing metadata logs showing concurrent unauthorized lateral movements, incident responders initiated controlled engagement protocol involving specially trained negotiators working alongside automated chatbots programmed to stall payment deadlines indefinitely. Over successive weeks, investigators collected sufficient forensic artifacts enabling law enforcement cooperation resulting in arrests conducted overseas jurisdictions.
Case Study #2: Healthcare Provider Avoids HIPAA Violations Following suspected ransomware infection impacting patient record database accessibility, hospital administrators faced mounting pressure from regulatory bodies demanding swift remediation progress updates. Rather than capitulating immediately, IT leadership deployed combination deception assets including fake PHI-filled CSV exports scattered throughout shared drives alongside modified registry keys designed to mimic credential storage locations.
Adversaries fell victim to baited traps repeatedly accessing honeyfiles prompting instant notification dispatches triggering emergency incident declaration procedures. Concurrently, NLP-powered profiler engine constructed preliminary profiles identifying probable nationality origins and experience levels belonging to implicated parties. Armed with this intelligence, legal counsel negotiated favorable settlement terms involving partial recovery guarantees backed by escrow arrangements mitigating exposure risks.
Case Study #3: Manufacturing Company Leverages MR7 Agent Integration Automotive parts manufacturer incorporated mr7 Agent into existing endpoint protection framework to augment autonomous scanning routines focused on detecting anomalous network behavior indicative of active negotiation attempts. Within days of installation, mr7 Agent flagged suspicious outbound HTTPS traffic directed toward TOR-hidden service destinations previously unseen in baseline telemetry.
Forensic analysis revealed encrypted C2 beaconing originating from compromised workstation belonging to recently hired contractor whose credentials had been harvested months earlier via spear-phishing attack. Prompt isolation prevented lateral spread while allowing continued monitoring of encrypted communications stream until decryption keys became available through unrelated third-party breach disclosures.
These examples underscore necessity for layered defense postures incorporating both reactive and predictive elements working harmoniously to neutralize evolving ransomware negotiation threats. Organizations adopting comprehensive behavioral analysis strategies consistently report reduced dwell times, enhanced attribution accuracy, and elevated stakeholder confidence ratings compared to peers relying solely on reactive incident response protocols.
Lessons learned: Proactive investment in AI-driven negotiation monitoring yields substantial ROI through avoided ransom payments, expedited recovery timelines, and strengthened compliance postures protecting brand integrity.
How Can Security Teams Implement These Techniques Locally?
Local implementation of AI-powered ransomware negotiation detection requires careful consideration of available computing resources, dataset privacy requirements, integration complexity constraints, and long-term maintenance obligations. Fortunately, modern toolkits simplify many traditionally challenging aspects associated with deploying scalable machine learning infrastructures suitable for enterprise-grade deployments.
Containerization technologies like Docker streamline packaging dependencies necessary for executing complex analytical pipelines reliably regardless of underlying host operating systems. Pre-built images containing preconfigured environments save considerable setup effort compared to manual compilation steps traditionally required for installing scientific computing libraries, database drivers, web frameworks, and visualization packages individually.
Orchestration platforms such as Kubernetes facilitate horizontal scaling horizontally across commodity hardware clusters eliminating single points of failure commonly plaguing centralized monolithic deployments. Service meshes introduce fine-grained traffic routing policies governing communication flows between loosely coupled microservices participating in distributed computation graphs.
Edge computing paradigms bring processing closer to data sources reducing latency penalties imposed by round-trip communications traversing WAN links connecting remote sites to central data centers. Local inference accelerators including GPUs, TPUs, FPGAs, and ASIC chips dramatically accelerate prediction latencies enabling near-realtime responsiveness demanded by interactive negotiation scenarios.
Privacy-preserving computation methods address growing concerns surrounding personally identifiable information leakage during model training phases. Federated learning allows collaborative model improvement without exchanging raw data samples between participating entities. Homomorphic encryption preserves confidentiality throughout entire lifecycle including storage, transmission, aggregation, and evaluation stages.
Open-source frameworks democratize access to state-of-the-art research成果 previously confined exclusively to academic institutions and proprietary vendors. TensorFlow, PyTorch, Scikit-Learn, HuggingFace Transformers, FastAPI, Streamlit, Jupyter Notebooks, and countless others collectively form rich ecosystem empowering practitioners to prototype ideas quickly before transitioning into production-ready implementations.
Sample Dockerfile defining portable negotiation detection environment:
dockerfile FROM python:3.9-slim
WORKDIR /app COPY requirements.txt . RUN pip install --no-cache-dir -r requirements.txt
COPY src/ ./src/ CMD ["python", "./src/main.py"]
Requirements.txt excerpt showcasing essential libraries:
tensorflow>=2.8.0 scikit-learn>=1.0.0 pandas>=1.4.0 numpy>=1.21.0 spacy>=3.2.0 flask>=2.0.0 requests>=2.27.0
Configuration management tools like Ansible, Chef, Puppet, SaltStack, Terraform, CloudFormation, Helm Charts, and ArgoCD automate provisioning tasks ensuring reproducible deployments adhering to defined standards consistently enforced across heterogeneous deployment targets.
Monitoring dashboards built atop Grafana, Prometheus, ELK Stack, Splunk, Datadog, NewRelic, Dynatrace, Sumo Logic, or equivalent observability suites deliver actionable insights illuminating system health statuses, performance bottlenecks, error trends, capacity utilization forecasts, and alert fatigue mitigation recommendations.
Continuous integration pipelines implemented using Jenkins, GitLab CI/CD, GitHub Actions, CircleCI, TravisCI, Drone.io, Bamboo, TeamCity, Azure DevOps, Bitbucket Pipelines, or similar DevOps practices guarantee consistent quality assurance standards upheld throughout software development lifecycles encompassing unit testing, static code analysis, vulnerability scanning, dependency auditing, license compliance verification, release tagging, artifact signing, rollback preparation, and post-deployment validation checks.
Deployment checklist summary:
- Containerize core components for portability
- Orchestrate scalability via Kubernetes
- Accelerate inference using edge devices
- Protect privacy through federated/homomorphic techniques
- Leverage open-source frameworks for rapid prototyping
- Automate provisioning using configuration managers
- Monitor health using observability stacks
- Enforce quality via CI/CD pipelines
Implementation tip: Begin with modular architecture designs emphasizing loose coupling principles enabling gradual migration from legacy systems towards fully autonomous AI-driven negotiation monitoring ecosystems.
Key Takeaways
- AI-powered behavioral analysis detects ransomware negotiation attempts by examining temporal, linguistic, and network patterns in attacker communications
- Machine learning models like SVMs, Random Forests, LSTMs, and anomaly detectors excel at identifying negotiation-specific behavioral signatures
- NLP techniques including stylometry, sentiment analysis, and topic modeling enable detailed threat actor profiling during negotiations
- Automated response systems prolong engagement timelines while collecting actionable intelligence from adversaries
- Deception technology enhances early detection through honeytokens, decoy networks, and behavioral lures
- Real-world case studies demonstrate significant ROI from proactive AI-driven negotiation monitoring investments
- Security teams can implement these techniques locally using containerization, orchestration, and open-source frameworks
Frequently Asked Questions
Q: What defines ransomware negotiation behavior worth detecting?
Ransomware negotiation behavior includes coercive language patterns, urgent payment demands, cryptocurrency references, deadline pressures, and repeated communication loops typical of automated bot interactions or human-led extortion campaigns.
Q: Which programming languages work best for building negotiation detection systems?
Python dominates due to extensive ecosystem including TensorFlow, PyTorch, Scikit-Learn, Pandas, NLTK, SpaCy, while JavaScript excels in frontend dashboard creation and Node.js backend services integration.
Q: How much training data do I need to train effective models?
Minimum viable datasets range from hundreds to thousands of labeled examples depending on problem complexity, though larger corpora generally improve generalization capabilities especially for deep learning architectures.
Q: Can deception assets interfere with legitimate business operations?
Well-designed deception assets minimize interference risks through careful placement strategies avoiding mission-critical pathways and utilizing tamper-evident indicators clearly marking decoy status to authorized users.
Q: Is mr7 Agent compatible with existing SIEM/SOAR platforms?
Yes, mr7 Agent supports RESTful API integrations enabling seamless data exchange with popular SIEM/SOAR ecosystems including Splunk Phantom, IBM Resilient, Palo Alto Cortex XSOAR, and LogRhythm Case Management.
Ready to Level Up Your Security Research?
Get 10,000 free tokens and start using KaliGPT, 0Day Coder, DarkGPT, OnionGPT, and mr7 Agent today. No credit card required!