toolssemgrepapi-securityowasp-api-top-10
Semgrep API Security Testing: Mastering Automated API Vulnerability Detection
March 18, 202626 min read35 views

Table of Contents


Learn how eBPF rootkit detection identifies stealthy threats using ebpf-explorer and Tetragon. Boost your security posture at mr7.ai today!

Explore Wfuzz 4.0's new capabilities for GraphQL endpoint fuzzing, JWT token manipulation, and modern framework testing. Try mr7.ai's free tools today.
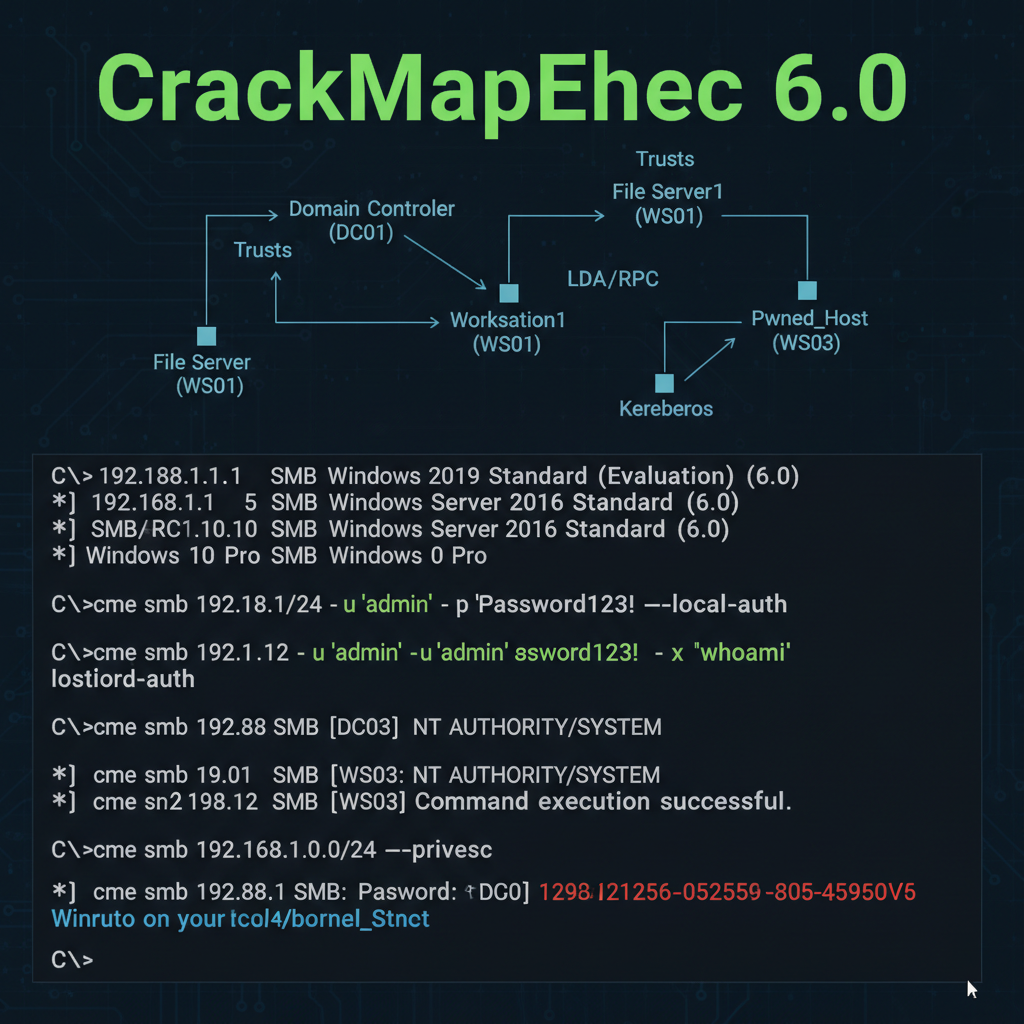
Deep dive into CrackMapExec 6.0's new features for AD pentesting. Learn Kerberos relay, LDAP abuse & modern auth techniques. Try mr7.ai free!