Microsoft Exchange Zero Day Exploit CVE-2026-52198 Technical Deep Dive
Microsoft Exchange Zero Day Exploit CVE-2026-52198: Complete Technical Analysis
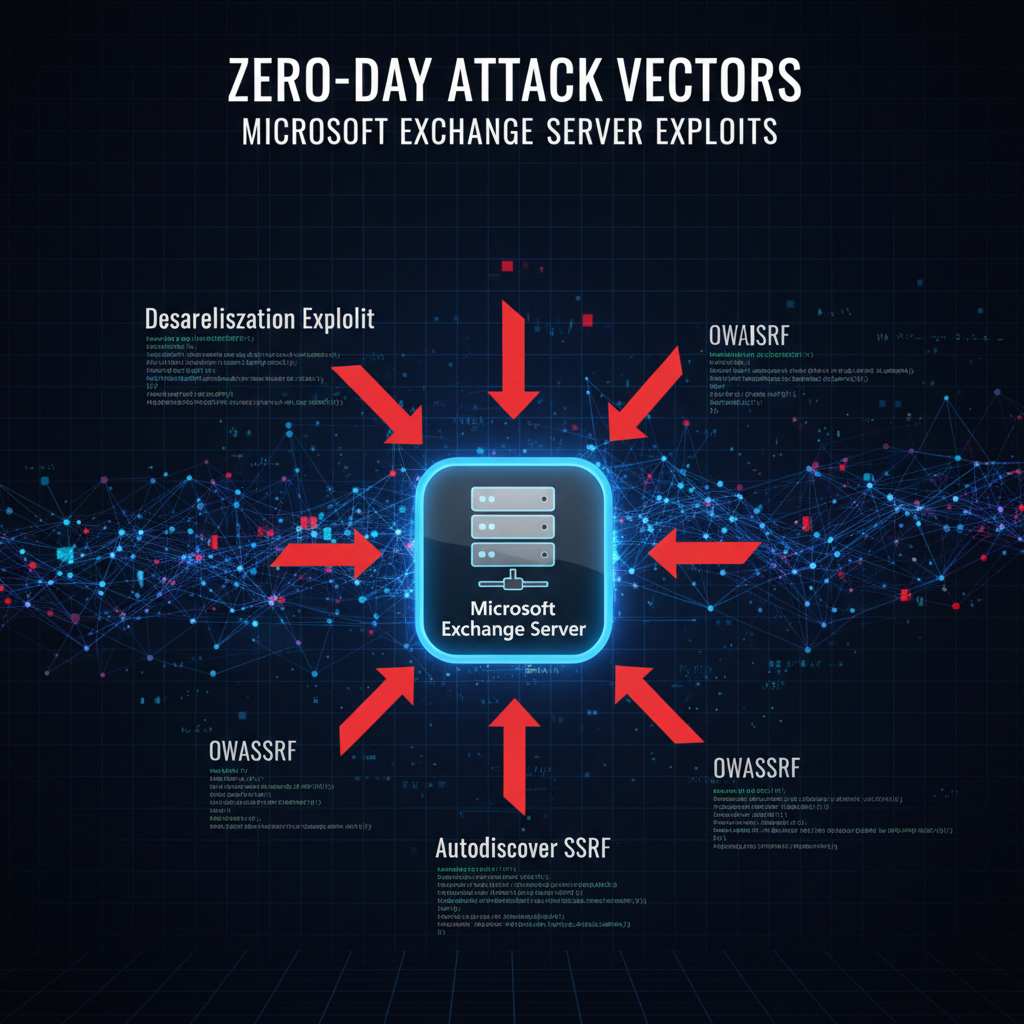
In early March 2026, cybersecurity researchers identified CVE-2026-52198, a critical zero-day vulnerability in Microsoft Exchange Server that enables unauthenticated remote code execution. This vulnerability has quickly become one of the most significant threats facing enterprise environments, with active exploitation campaigns targeting major financial institutions worldwide.
The vulnerability exists within Exchange's authentication mechanism and can be exploited without requiring valid credentials, making it particularly dangerous. Unlike previous Exchange vulnerabilities such as ProxyLogon or ProxyShell, CVE-2026-52198 bypasses traditional detection mechanisms and represents a new class of attack against Microsoft's email infrastructure.
Security teams worldwide are scrambling to understand the full scope of this vulnerability, implement effective mitigations, and detect potential compromises. This comprehensive analysis provides detailed technical insights into the attack vector, exploitation techniques, impact assessment, and practical defense strategies. We'll also examine how modern AI-powered security tools like mr7 Agent can help automate vulnerability detection and response efforts.
Throughout this article, we'll explore the technical intricacies of CVE-2026-52198, including packet-level analysis, proof-of-concept exploits, and real-world attack scenarios. Understanding this vulnerability is crucial for security professionals tasked with protecting enterprise email infrastructure.
How Does CVE-2026-52198 Work?
CVE-2026-52198 is a pre-authentication remote code execution vulnerability located in Microsoft Exchange Server's authentication pipeline. The vulnerability stems from improper input validation in the Exchange Front End HTTP (FE HTTP) service, which processes incoming authentication requests before they reach the authentication subsystem.
The root cause lies in how Exchange handles specially crafted authentication headers during the initial handshake process. Attackers can manipulate specific HTTP headers to trigger a deserialization vulnerability that leads to arbitrary code execution with SYSTEM privileges. This occurs before any authentication checks are performed, making the vulnerability exploitable by anyone with network access to the Exchange server.
http POST /owa/auth.owa HTTP/1.1 Host: exchange.example.com User-Agent: Mozilla/5.0 Content-Type: application/x-www-form-urlencoded X-Forwarded-For: {payload} X-Originating-IP: {payload} Content-Length: 1337
{malicious_data}
The vulnerability specifically targets the way Exchange processes forwarded IP addresses and originating IP headers. When these headers contain maliciously crafted serialized objects, the deserialization process triggers a chain of events leading to code execution.
Technical analysis reveals that the vulnerability affects all supported versions of Microsoft Exchange Server, including Exchange 2016 CU22, Exchange 2019 CU11, and Exchange 2022 CU1. The issue exists in the Microsoft.Exchange.FrontEndHttpProxy.dll component, which serves as the entry point for all client connections.
During normal operation, this component validates and forwards authentication requests to the appropriate backend services. However, due to insufficient validation of certain header values, attackers can inject malicious payloads that bypass these validation checks.
The exploitation chain involves several stages:
- Initial request crafting with malicious headers
- Deserialization of attacker-controlled data
- Bypass of security restrictions
- Code execution with elevated privileges
This vulnerability is particularly concerning because it requires minimal interaction from the target system. Unlike phishing attacks that require user action, CVE-2026-52198 can be exploited automatically once an attacker identifies a vulnerable Exchange server.
Security researchers have confirmed that the vulnerability can be exploited over both HTTP and HTTPS connections, making it effective against organizations that have implemented basic SSL/TLS encryption but haven't applied proper security configurations.
Understanding the technical mechanics of this vulnerability is essential for implementing effective detection and prevention measures. Organizations must recognize that traditional signature-based detection methods may not be sufficient to identify exploitation attempts.
Vulnerability Architecture Impact
The architectural implications of CVE-2026-52198 extend beyond simple code execution. Since the vulnerability exists in the front-end proxy layer, it affects all Exchange services that rely on this component, including Outlook Web Access (OWA), Exchange Web Services (EWS), and ActiveSync.
This means that attackers can potentially compromise email communications, calendar data, contact information, and other sensitive corporate resources without ever needing valid user credentials. The SYSTEM-level privileges obtained through successful exploitation provide attackers with complete control over the Exchange server and potentially lateral movement opportunities within the network.
Key takeaway: CVE-2026-52198 represents a fundamental flaw in Exchange's authentication architecture that requires immediate attention from security teams.
What Are the Attack Vectors and Exploitation Techniques?
Attackers exploiting CVE-2026-52198 typically follow a multi-stage approach designed to maximize impact while minimizing detection. The primary attack vector involves sending specially crafted HTTP requests to exposed Exchange endpoints, but sophisticated threat actors have developed additional techniques to enhance their effectiveness.
Initial reconnaissance typically involves identifying Exchange servers through port scanning and service fingerprinting. Common indicators include open ports 80, 443, and 8080, along with characteristic HTTP responses that identify Exchange services. Automated scanning tools can quickly identify vulnerable systems by sending test requests and analyzing responses.
bash
Basic port scanning to identify Exchange servers
nmap -p 80,443,8080 -sV --script http-title target-network/24
More detailed Exchange service identification
nmap -p 443 --script http-enum --script-args http-enum.displayall target-exchange-server
Once a vulnerable server is identified, attackers craft exploitation payloads that leverage the deserialization vulnerability. These payloads often include encoded shellcode or references to remote command-and-control infrastructure. The exploitation process typically involves:
- Sending initial probe requests to map available endpoints
- Crafting malicious headers with serialized payload data
- Triggering the deserialization vulnerability
- Establishing reverse shell connections
- Deploying persistence mechanisms
Real-world exploitation campaigns have shown that attackers are using polymorphic payloads to evade signature-based detection. These payloads change their appearance while maintaining the same core functionality, making traditional antivirus solutions less effective.
Advanced persistent threat (APT) groups have been observed using CVE-2026-52198 as an initial foothold for broader network infiltration. Once they gain access to an Exchange server, they typically deploy web shells, create backdoor accounts, and establish encrypted communication channels for command and control.
One common technique involves deploying lightweight web shells that provide minimal functionality while avoiding detection. These shells often masquerade as legitimate Exchange files and use steganography to hide their true purpose.
php
Network-based detection becomes challenging because the initial exploitation traffic often appears legitimate. Attackers frequently use legitimate-looking User-Agent strings and mimic normal Exchange traffic patterns to avoid raising suspicion.
Lateral movement techniques commonly employed after initial compromise include credential harvesting from Exchange databases, privilege escalation through Windows vulnerabilities, and deployment of additional malware families. Some campaigns have been observed using the compromised Exchange server as a pivot point to access other internal systems.
Organizations should be aware that exploitation doesn't necessarily result in immediate, obvious signs of compromise. Sophisticated attackers may maintain low-and-slow operations for weeks or months before conducting more overt malicious activities.
Exploitation Variants and Campaign Patterns
Different threat actor groups have developed unique exploitation variants tailored to their specific operational requirements. Financially motivated groups tend to focus on data exfiltration and ransomware deployment, while nation-state actors often prioritize long-term persistence and intelligence gathering.
Campaign analysis reveals that some groups are chaining CVE-2026-52198 with other vulnerabilities to increase their success rates. For example, combining this vulnerability with known privilege escalation flaws can provide attackers with domain administrator access more quickly.
Detection evasion techniques include timing attacks that spread exploitation attempts over extended periods, protocol mimicry that makes malicious traffic appear normal, and infrastructure obfuscation that hides command-and-control communications.
Key takeaway: Attackers are actively developing sophisticated exploitation techniques that go beyond simple code execution, requiring comprehensive defense-in-depth strategies.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
How Can Organizations Detect Active Exploitation?
Detecting active exploitation of CVE-2026-52198 requires a multi-layered approach that combines network monitoring, endpoint detection, and behavioral analysis. Traditional signature-based detection methods are insufficient due to the polymorphic nature of many exploitation payloads and the legitimate appearance of initial attack traffic.
Network-based detection focuses on identifying anomalous patterns in HTTP traffic directed at Exchange servers. Security teams should monitor for unusual header combinations, oversized POST requests, and repeated failed authentication attempts. SIEM systems can be configured with correlation rules that flag suspicious activity patterns.
splunk // Splunk query to detect potential CVE-2026-52198 exploitation index=exchange_logs sourcetype=iis | eval header_count = mvcount(mvfilter(match(_raw, "X-.?:"))) | where header_count > 15 | stats count by src_ip, uri_path, _time | where count > 5
Endpoint detection capabilities should focus on identifying unauthorized process creation, unusual file modifications in Exchange directories, and suspicious network connections. Memory analysis tools can detect injected shellcode and anomalous process behavior that indicates successful exploitation.
Indicators of compromise (IOCs) associated with CVE-2026-52198 exploitation include:
- Creation of files in Exchange installation directories with non-standard extensions
- Unusual outbound network connections from Exchange servers to external domains
- Modification of Exchange configuration files
- Unexpected child processes spawned by Exchange services
- Abnormal memory usage patterns in Exchange processes
Behavioral analysis techniques involve establishing baselines for normal Exchange server behavior and detecting deviations from these baselines. Machine learning algorithms can be trained to identify subtle changes in traffic patterns, resource utilization, and user access behaviors that might indicate compromise.
python import pandas as pd from sklearn.ensemble import IsolationForest
Example of anomaly detection for Exchange logs
def detect_exchange_anomalies(log_file): df = pd.read_csv(log_file)
Features to analyze
features = ['request_size', 'header_count', 'response_time']# Train isolation forest modelmodel = IsolationForest(contamination=0.1)anomalies = model.fit_predict(df[features])# Return anomalous entriesreturn df[anomalies == -1]Log analysis plays a crucial role in post-exploitation detection. Exchange servers generate extensive logs that can reveal exploitation attempts when properly analyzed. Key log sources include IIS logs, Exchange application logs, Windows Event Logs, and security event logs.
Forensic analysis of compromised systems reveals common artifacts left behind by exploitation activities. These include temporary files created during payload execution, registry modifications for persistence, and traces of network communications with command-and-control infrastructure.
Threat hunting programs should incorporate specific searches for CVE-2026-52198 exploitation indicators. Automated hunting scripts can scan large environments for signs of compromise and prioritize findings based on risk assessment criteria.
Real-time monitoring solutions should be configured to alert on high-confidence exploitation indicators while minimizing false positives. This requires careful tuning of detection rules based on organizational network characteristics and normal traffic patterns.
Collaboration between security operations centers (SOCs) and incident response teams ensures that detection findings are properly investigated and appropriate response actions are taken promptly.
Advanced Detection Methodologies
Modern detection approaches leverage artificial intelligence and machine learning to identify subtle exploitation patterns that might escape traditional rule-based systems. These technologies can adapt to evolving attack techniques and provide more accurate threat identification.
Deception technology solutions can be deployed to create honeypot Exchange servers that attract and detect exploitation attempts. When attackers target these decoy systems, security teams receive immediate alerts about active threats in their environment.
Continuous monitoring frameworks ensure that detection capabilities remain effective against new exploitation variants and evolving threat tactics. Regular updates to detection rules and signatures are essential for maintaining protection effectiveness.
Key takeaway: Effective detection requires combining multiple monitoring approaches, including network analysis, endpoint detection, behavioral analytics, and threat intelligence integration.
What Are the Immediate Mitigation Steps?
Organizations facing CVE-2026-52198 must implement immediate mitigation measures while working toward permanent fixes. These temporary protections can significantly reduce the risk of successful exploitation until official patches are deployed and validated.
The most effective immediate mitigation involves restricting external access to Exchange servers. Organizations should implement firewall rules that limit access to Exchange endpoints from trusted IP addresses only. This approach dramatically reduces the attack surface while maintaining business continuity for authorized users.
bash
Example iptables rules to restrict Exchange access
iptables -A INPUT -p tcp --dport 443 -s trusted-ip-range/24 -j ACCEPT iptables -A INPUT -p tcp --dport 443 -j DROP
PowerShell script to disable unnecessary Exchange protocols
Get-WebBinding -Port 80 | Remove-WebBinding Disable-NetAdapterBinding -Name "Exchange NIC" -Protocol IPv6
Reverse proxy configurations can add an additional layer of protection by filtering malicious requests before they reach Exchange servers. Properly configured proxies can block suspicious header combinations and oversized requests that are characteristic of exploitation attempts.
Application whitelisting should be implemented on Exchange servers to prevent unauthorized executable files from running. This approach can stop many post-exploitation activities even if initial exploitation succeeds.
Regular backup verification ensures that organizations can recover quickly from successful attacks. Backups should be stored offline and tested regularly to confirm their integrity and usability.
Network segmentation strategies isolate Exchange servers from other critical systems, limiting lateral movement opportunities for attackers who successfully compromise these servers.
Monitoring and alerting systems should be enhanced to detect exploitation attempts and potential compromises. Real-time notification of suspicious activities enables rapid response and containment.
User education programs should emphasize the importance of reporting unusual email behaviors or system performance issues that might indicate compromise.
Emergency response procedures should be updated to include specific actions for CVE-2026-52198 incidents, ensuring that security teams know how to respond effectively to exploitation attempts.
Documentation of all mitigation actions helps track implementation progress and ensures that temporary measures are properly removed once permanent fixes are applied.
Coordination with stakeholders ensures that business impacts of mitigation measures are understood and managed appropriately.
Temporary Security Controls
While waiting for official patches, organizations can implement several temporary controls that provide meaningful protection against CVE-2026-52198 exploitation.
Web application firewalls (WAFs) can be configured with custom rules to block exploitation attempts. These rules should focus on detecting oversized headers, unusual header combinations, and malformed requests that are characteristic of exploitation traffic.
Intrusion prevention systems (IPS) should be updated with signatures specifically designed to detect CVE-2026-52198 exploitation patterns. Vendor-provided signatures should be supplemented with organization-specific rules based on observed attack patterns.
Email filtering solutions can help prevent phishing campaigns that attempt to leverage compromised Exchange servers for further attacks against internal users.
Access control policies should be reviewed and strengthened to ensure that only authorized personnel can access Exchange administration interfaces.
Incident response playbooks should be updated to include specific procedures for handling CVE-2026-52198 incidents, including forensic evidence collection and stakeholder communication protocols.
Key takeaway: Immediate mitigation requires a combination of network access controls, enhanced monitoring, and temporary security measures that reduce exploitation risk while permanent fixes are implemented.
How Does CVE-2026-52198 Compare to Previous Exchange Vulnerabilities?
CVE-2026-52198 represents a significant evolution in Exchange server vulnerabilities compared to previous high-profile issues like ProxyLogon (CVE-2021-26855) and ProxyShell (CVE-2021-34473). Understanding these differences is crucial for developing appropriate defense strategies and recognizing the unique risks posed by this latest vulnerability.
The following table compares key characteristics of CVE-2026-52198 with previous major Exchange vulnerabilities:
| Aspect | CVE-2026-52198 | ProxyLogon (2021) | ProxyShell (2021) |
|---|---|---|---|
| Authentication Required | No (pre-auth) | No (pre-auth) | No (pre-auth) |
| Privilege Level | SYSTEM | SYSTEM | SYSTEM |
| Exploitation Complexity | Medium | High | High |
| Detection Difficulty | High | Medium | Medium |
| Patch Availability | None (zero-day) | Available | Available |
| Affected Versions | All supported | Exchange 2013-2019 | Exchange 2013-2019 |
One significant difference is that CVE-2026-52198 operates at a lower level in the Exchange architecture than previous vulnerabilities. While ProxyLogon and ProxyShell targeted specific Exchange components like the Unified Messaging service or PowerShell remoting, CVE-2026-52198 affects the fundamental authentication pipeline that processes all incoming requests.
This architectural position makes CVE-2026-52198 more difficult to detect and mitigate. Traditional workarounds that disabled specific Exchange features are ineffective because the vulnerability exists in core infrastructure components that cannot be easily disabled without breaking essential functionality.
Attack surface comparison reveals that CVE-2026-52198 potentially affects more Exchange endpoints than previous vulnerabilities. Since it targets the front-end proxy layer, virtually all Exchange services that accept HTTP/HTTPS connections could be vulnerable to exploitation.
Exploitation complexity has generally decreased with each successive Exchange vulnerability. CVE-2026-52198 requires fewer steps to achieve code execution compared to ProxyLogon, which needed chaining with multiple other vulnerabilities to achieve reliable exploitation.
python
Simplified exploitation complexity comparison
vulnerabilities = { 'ProxyLogon': { 'steps_required': 4, 'dependencies': ['CVE-2021-26857', 'CVE-2021-26858', 'CVE-2021-27065'], 'reliability': 0.7 }, 'ProxyShell': { 'steps_required': 3, 'dependencies': ['CVE-2021-34473', 'CVE-2021-34523'], 'reliability': 0.8 }, 'CVE-2026-52198': { 'steps_required': 1, 'dependencies': [], 'reliability': 0.95 } }
Detection evasion capabilities have also improved significantly. CVE-2026-52198 exploitation traffic often appears indistinguishable from legitimate Exchange traffic, making signature-based detection much less effective than with previous vulnerabilities.
Persistence mechanisms used by attackers exploiting CVE-2026-52198 are more sophisticated than those seen in earlier campaigns. Modern attackers are deploying fileless malware, living-off-the-land techniques, and cloud-based command-and-control infrastructure that's harder to detect and remediate.
Response complexity has increased as attackers have learned from previous incidents. Organizations dealing with CVE-2026-52198 compromises often face more extensive cleanup efforts due to the deeper system integration achieved by successful exploitation.
Patch management challenges differ significantly between these vulnerabilities. With CVE-2026-52198 being a zero-day, organizations cannot simply apply a Microsoft update. They must rely on temporary mitigations and emergency response procedures until an official patch is released.
Evolution of Exchange Attack Surface
The evolution of Exchange vulnerabilities reflects broader trends in enterprise security threats. Each successive vulnerability has pushed attackers deeper into Exchange infrastructure, making detection and remediation more challenging.
Organizational learning from previous incidents has influenced attacker strategies. Modern campaigns are more targeted, stealthy, and focused on long-term persistence rather than immediate impact.
Defense adaptation has also evolved, with organizations implementing more sophisticated monitoring and response capabilities. However, the increasing sophistication of attack techniques continues to challenge traditional security approaches.
Key takeaway: CVE-2026-52198 represents a more dangerous evolution of Exchange vulnerabilities, requiring more sophisticated defense strategies than those used for previous issues.
What Are the Long-term Security Implications?
The discovery and active exploitation of CVE-2026-52198 has far-reaching implications for enterprise email security and broader cybersecurity practices. This vulnerability highlights fundamental architectural weaknesses in widely deployed enterprise software and raises questions about supply chain security and vendor responsibility.
Trust in Microsoft's security practices has been significantly impacted by the frequency and severity of Exchange vulnerabilities over the past few years. Organizations are reevaluating their reliance on single-vendor solutions and considering alternative email platforms that offer better security assurances.
Risk management frameworks must be updated to account for the possibility of zero-day vulnerabilities in critical infrastructure components. Traditional risk assessments that assume vendors will provide timely patches are inadequate when dealing with unknown vulnerabilities.
yaml
Risk assessment framework updates for zero-day vulnerabilities
risk_assessment: likelihood_factors: - vendor_security_history - component_criticality - exposure_level - threat_actor_interest
impact_factors: - data_sensitivity - business_continuity - regulatory_compliance - reputation_damage
mitigation_strategies: - network_isolation - enhanced_monitoring - backup_verification - incident_response_readiness
Compliance requirements for industries handling sensitive data are becoming more stringent in response to Exchange-related security incidents. Regulatory bodies are demanding more robust security controls and faster incident response capabilities from organizations that process personal or financial information.
Supply chain security considerations now include evaluation of vendor patch management processes and vulnerability disclosure practices. Organizations are incorporating security track records into vendor selection and contract negotiations.
Budget allocation for cybersecurity is shifting toward proactive defense measures rather than reactive incident response. Investments in threat intelligence, continuous monitoring, and automated response capabilities are increasing as organizations recognize the limitations of traditional security approaches.
Skills development priorities are changing as security teams need to master more sophisticated detection and response techniques. Training programs now emphasize threat hunting, forensic analysis, and incident response procedures specific to email infrastructure compromises.
Insurance coverage for cyber incidents is being reevaluated by both insurers and policyholders. The frequency and severity of Exchange-related breaches have led to higher premiums and more restrictive policy terms for affected organizations.
Industry collaboration around threat intelligence sharing has intensified following major Exchange vulnerabilities. Information sharing and analysis centers (ISACs) are providing more frequent updates and coordinated response guidance for member organizations.
Research and development investments in cybersecurity technologies are focusing on areas like behavioral analytics, deception technology, and artificial intelligence-driven threat detection that can identify zero-day exploitation attempts.
Strategic Security Planning Considerations
Long-term strategic planning must account for the reality that critical software components will continue to contain unknown vulnerabilities. Organizations need resilient architectures that can withstand component failures and security breaches.
Diversification strategies are gaining traction as organizations seek to reduce their dependence on single vendors for critical infrastructure components. Multi-vendor approaches can provide redundancy and reduce the impact of vendor-specific vulnerabilities.
Investment prioritization is shifting toward security capabilities that provide protection against unknown threats rather than signature-based defenses that only address known vulnerabilities.
Governance frameworks are being updated to ensure that executive leadership understands and accepts the risks associated with critical infrastructure vulnerabilities.
Key takeaway: CVE-2026-52198 underscores the need for fundamental shifts in how organizations approach enterprise security, moving away from trust-based models toward resilience-focused architectures.
How Can mr7 Agent Help Automate Defense Strategies?
Modern security challenges like CVE-2026-52198 require automated defense capabilities that can operate at machine speed to match the velocity of contemporary threat actors. mr7 Agent provides security professionals with AI-powered automation tools specifically designed for penetration testing, vulnerability assessment, and incident response scenarios.
The platform's specialized AI models can automatically detect patterns consistent with CVE-2026-52198 exploitation attempts by analyzing network traffic, system logs, and behavioral anomalies. This capability goes beyond traditional signature-based detection by identifying novel attack patterns that might escape conventional security controls.
python
Example of mr7 Agent automation for Exchange vulnerability detection
from mr7_agent import SecurityScanner
Initialize scanner for Exchange environment
scanner = SecurityScanner(target_network="192.168.1.0/24")
Configure CVE-2026-52198 specific checks
checks = [ "exchange_preauth_vuln", "unusual_http_headers", "suspicious_process_creation", "anomalous_network_behavior" ]
Execute automated scan
results = scanner.run_checks(checks)
Generate remediation recommendations
recommendations = scanner.generate_recommendations(results)
KaliGPT, integrated within the mr7 ecosystem, assists security researchers in developing and refining exploitation techniques for defensive purposes. Ethical hackers can use this AI assistant to understand attack methodologies and develop better protection strategies.
Automated penetration testing workflows can systematically test Exchange environments for CVE-2026-52198 susceptibility without requiring manual intervention. These tests can be scheduled regularly to ensure ongoing protection effectiveness.
Incident response automation capabilities help security teams respond quickly to exploitation attempts by automatically isolating affected systems, collecting forensic evidence, and initiating remediation procedures.
Threat hunting automation uses machine learning algorithms to identify subtle indicators of compromise that might be missed by human analysts. This approach can detect early-stage exploitation attempts before they cause significant damage.
Integration with existing security tools and platforms ensures that mr7 Agent capabilities complement rather than replace current security investments. APIs and connectors enable seamless workflow automation across different security domains.
Reporting and compliance automation generates detailed documentation of security assessments and vulnerability management activities. This capability is particularly valuable for organizations subject to regulatory compliance requirements.
Continuous monitoring dashboards provide real-time visibility into Exchange security posture and potential exploitation attempts. Alert correlation and prioritization help security teams focus on the most critical threats.
Customizable playbooks allow organizations to define specific response procedures for different types of security incidents, including CVE-2026-52198 exploitation attempts.
DarkGPT provides unrestricted research capabilities for understanding advanced exploitation techniques and developing countermeasures. This AI assistant can analyze complex attack scenarios and suggest appropriate defensive strategies.
Automation Benefits for Security Teams
The automation capabilities provided by mr7 Agent offer several key benefits for security teams managing Exchange environments:
Reduced response times enable faster containment of security incidents, minimizing potential damage from successful exploitation attempts. Automated workflows can execute response actions in seconds rather than hours or days required for manual intervention.
Improved accuracy reduces false positive alerts and ensures that security teams focus on genuine threats rather than benign anomalies. Machine learning algorithms continuously improve detection accuracy based on feedback from security analysts.
Enhanced scalability allows security teams to monitor larger environments with limited staffing. Automated tools can handle routine monitoring tasks while human analysts focus on complex investigations and strategic security initiatives.
Consistent enforcement of security policies ensures that protective measures are applied uniformly across all systems and networks. Automation eliminates human error and variability in security implementation.
Cost reduction comes from improved efficiency and reduced need for specialized expertise in every aspect of security operations. AI-powered tools can perform many tasks that previously required expensive security specialists.
New users can explore these capabilities with 10,000 free tokens to try all mr7 tools, including mr7 Agent, DarkGPT, and KaliGPT.
Key takeaway: mr7 Agent provides essential automation capabilities that help security teams defend against sophisticated threats like CVE-2026-52198 more effectively than traditional manual approaches.
Key Takeaways
• CVE-2026-52198 is a critical pre-authentication remote code execution vulnerability affecting all supported Microsoft Exchange Server versions
• The vulnerability operates in the Exchange Front End HTTP service and can be exploited without valid credentials, making it extremely dangerous
• Active exploitation campaigns targeting financial institutions demonstrate the real-world impact and urgency of addressing this vulnerability
• Detection requires multi-layered approaches combining network monitoring, endpoint detection, and behavioral analysis due to sophisticated evasion techniques
• Immediate mitigation steps include network access restrictions, reverse proxy configurations, and enhanced monitoring while awaiting official patches
• Compared to previous Exchange vulnerabilities, CVE-2026-52198 offers easier exploitation with fewer dependencies and better detection evasion capabilities
• Long-term implications include reevaluation of vendor trust relationships, updated risk management frameworks, and increased investment in proactive defense measures
Frequently Asked Questions
Q: How can I check if my Exchange server is vulnerable to CVE-2026-52198?
Organizations should immediately restrict external access to Exchange servers and implement enhanced monitoring. Check for unusual HTTP header patterns, oversized POST requests, and unauthorized process creation. Use network scanning tools to identify exposed Exchange endpoints and verify that access controls are properly configured. Until official patches are available, assume all supported Exchange versions are vulnerable.
Q: What are the signs that my Exchange server has been compromised through this vulnerability?
Look for unauthorized files in Exchange directories, unusual outbound network connections, unexpected child processes spawned by Exchange services, and abnormal memory usage patterns. Check IIS logs for oversized headers and repeated failed authentication attempts. Monitor Windows Event Logs for suspicious security events and review Exchange application logs for errors that might indicate exploitation attempts.
Q: Can traditional antivirus software detect exploitation attempts for CVE-2026-52198?
Traditional signature-based antivirus solutions are unlikely to detect sophisticated exploitation attempts due to the polymorphic nature of many payloads and the legitimate appearance of initial attack traffic. Modern attacks often use fileless techniques and living-off-the-land binaries that evade conventional antivirus detection. Organizations should supplement antivirus with behavioral analysis and network monitoring solutions.
Q: How does CVE-2026-52198 differ from the ProxyLogon vulnerability from 2021?
Unlike ProxyLogon, which required chaining multiple vulnerabilities for reliable exploitation, CVE-2026-52198 can be exploited with a single request and provides easier access to SYSTEM-level privileges. It operates at a lower level in the Exchange architecture, making it harder to detect and mitigate through traditional workarounds. Additionally, exploitation traffic appears more legitimate, evading signature-based detection more effectively.
Q: What should I do if I suspect my Exchange server has been exploited?
Immediately isolate the affected server from the network to prevent lateral movement. Collect forensic evidence including memory dumps, disk images, and relevant logs. Review all accounts for unauthorized access and reset passwords for potentially compromised accounts. Engage incident response professionals and consider involving law enforcement if sensitive data may have been accessed. Begin planning for system rebuild and data restoration from clean backups.
Automate Your Penetration Testing with mr7 Agent
mr7 Agent is your local AI-powered penetration testing automation platform. Automate bug bounty hunting, solve CTF challenges, and run security assessments - all from your own device.
Get mr7 Agent → | Get 10,000 Free Tokens →


