CVE-2026-11023 Analysis: Heap Overflow in SSH Handshake Renegotiation

In the landscape of network security, the Secure Shell (SSH) protocol remains a cornerstone of secure remote administration. However, the recent disclosure of CVE-2026-11023 has sent tremors through the security community, revealing a critical heap-based buffer overflow vulnerability that occurs during the SSH handshake renegotiation phase. For security professionals and system administrators, this vulnerability represents a significant risk because it can be triggered remotely without prior authentication, potentially leading to a complete system compromise. This article provides a deep-dive CVE-2026-11023 analysis, examining the technical mechanisms of the overflow, the pathways to remote code execution (RCE), and the rigorous steps required to secure affected Linux environments.
How Does the CVE-2026-11023 Heap Overflow Occur During SSH Renegotiation?
The technical root cause of CVE-2026-11023 lies in the flawed memory management logic within the SSH daemon's handling of the KEXINIT packet during a session renegotiation. In a standard SSH handshake, the client and server exchange version strings and then enter key exchange (KEX). Under normal circumstances, this process is seamless. However, CVE-2026-11023 is triggered when a malicious client sends a specially crafted renegotiation request that specifies an unsupported or excessively large number of supported algorithms for key exchange or encryption, coupled with a malformed packet length field.
When the SSH server processes the SSH_MSG_KEXINIT packet, it allocates a buffer on the heap to store the list of algorithms offered by the client. The vulnerability arises because the server fails to properly validate the size of the incoming algorithm list against the pre-allocated buffer size. If the client sends a packet where the declared length of the algorithm list exceeds the actual remaining space in the heap allocation, the server continues to write the incoming data into memory, overflowing the allocated boundary into adjacent memory regions. This is a classic heap-based buffer overflow, where data is written beyond the end of a buffer, potentially overwriting critical control structures or data used by other parts of the application.
From a memory-corruption perspective, the overflow occurs during the loop responsible for parsing the comma-separated string of algorithms. The code assumes that the length field provided in the SSH packet is accurate and that the buffer allocated is sufficient to hold that length. By providing a length field that is larger than the allocated space but smaller than the maximum packet size, an attacker can force the server to write beyond the heap chunk boundary. This corrupts the heap metadata, leading to unpredictable behavior or, in more severe cases, a crash of the SSH service, resulting in a denial-of-service (DoS) condition.
To understand the technicality, consider a simplified C representation of the vulnerable logic:
c /* Simplified vulnerable parsing logic */ void process_kexinit(uint8_t *packet_data, size_t packet_len) { char *algo_buffer = malloc(256); // Fixed size allocation size_t declared_len = read_uint32(packet_data); // Length declared by attacker
// VULNERABILITY: No check if declared_len > 256 memcpy(algo_buffer, packet_data + 4, declared_len);
// Further processing...
}
In this scenario, if declared_len is 512, the memcpy operation will write 256 bytes beyond the end of algo_buffer, corrupting the heap. This flaw highlights the importance of input validation in network-facing services. The primary takeaway is that trust in client-supplied length fields is the fundamental weakness that leads to this heap overflow.
What is the Pathway from Memory Corruption to Remote Code Execution (RCE)?
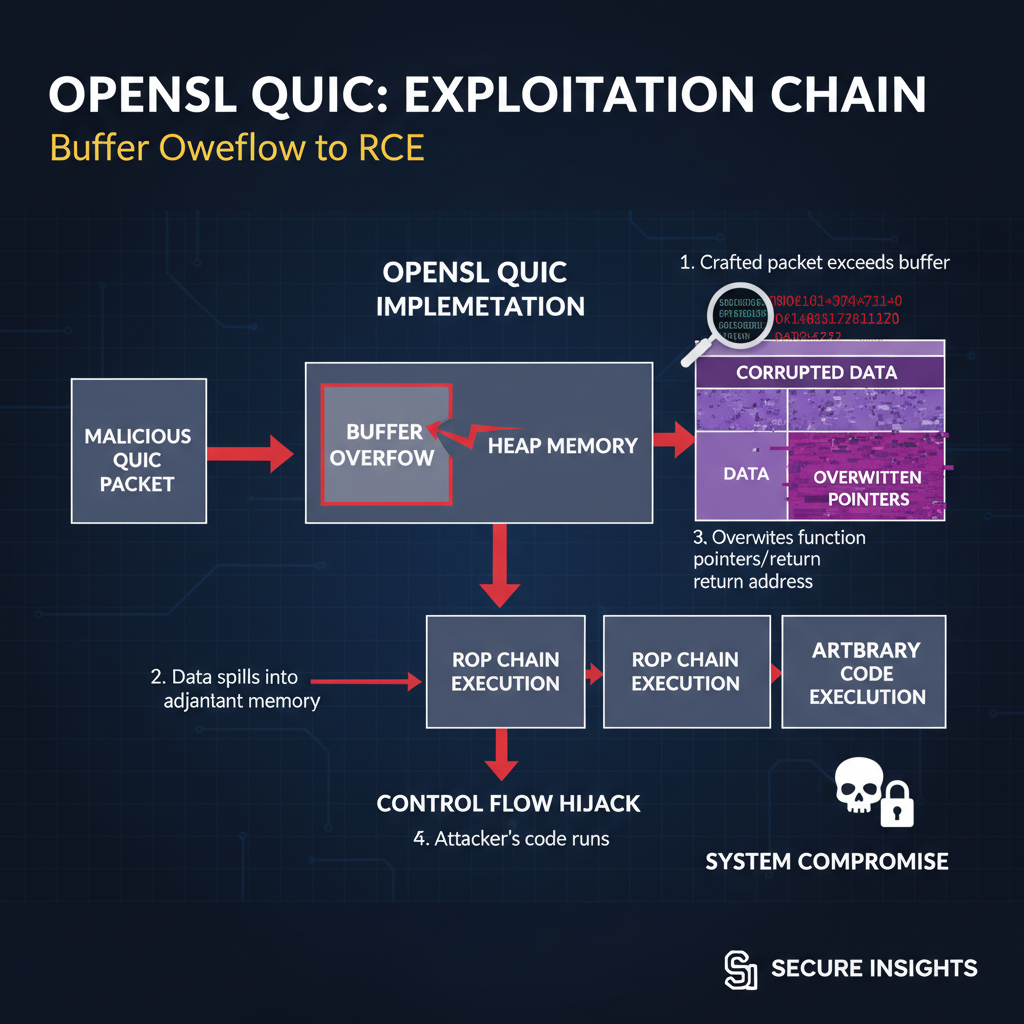
While a heap overflow often results in a simple crash (DoS), CVE-2026-11023 is particularly dangerous because it opens the door to Remote Code Execution (RCE). The transition from memory corruption to RCE occurs when an attacker can leverage the overflow to overwrite a function pointer or a return address on the heap. In the context of an SSH daemon, which often runs with high privileges (such as root), the impact of such an overwrite is catastrophic if not mitigated.
When the heap is corrupted, the attacker can potentially overwrite the pointer to a callback function that the SSH server uses to handle key exchange completion. By carefully crafting the payload within the KEXINIT packet, the attacker can overwrite this pointer with the address of a malicious instruction sequence—often referred to as a "gadget" in the context of Return-Oriented Programming (ROP). Instead of jumping to the legitimate key exchange logic, the CPU jumps to a location controlled by the attacker, executing their arbitrary code.
To achieve RCE, the attacker must bypass modern security mitigations such as Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP/NX). This is typically done by leaking memory addresses through other vulnerabilities or by guessing the base address of common libraries. Once the attacker has the address of a system function like system() or a sequence of instructions that marks a page of memory as executable, they can redirect the execution flow of the server process to run their payload.
bash
Example of how an attacker might probe for memory layouts
Using a tool like Nmap to check SSH version and potential vulnerabilities
nmap -sV --script ssh-auth-methods,ssh-hostkey 192.168.1.100
As the execution flow is hijacked, the attacker can spawn a reverse shell or install a persistent backdoor. The goal is to transition from a network-level vulnerability (the heap overflow) to a system-level compromise. The complexity of the exploit depends on the specific version of the SSH implementation and the underlying OS protections. However, the fundamental principle remains the same: corrupting the heap allows the attacker to gain control over the Instruction Pointer (EIP/RIP), leading to arbitrary code execution.
Try it yourself: Use mr7.ai's AI models to automate this process, or download mr7 Agent for local automated pentesting. Start free with 10,000 tokens.
How Can Administrators Detect and Verify CVE-2026-11023 in Their Environment?
Detecting the presence of CVE-2026-11023 requires a systematic approach that combines version checking, vulnerability scanning, and active probing. The first step for any system administrator is to identify the exact version of the SSH daemon running on their servers. In most Linux distributions, this can be done using the package manager or by querying the binary directly. It is critical to realize that backported patches may exist, so version numbers alone may not tell the whole story.
To verify the version, one might use the following command:
bash
Check SSH version on Debian/Ubuntu
ssh -V
If the version falls within the known vulnerable range, the next step is to utilize professional vulnerability scanners. Tools like OpenVAS or Nessus can identify the vulnerability by firing specific packets at the SSH service and analyzing the response. However, for those seeking a more automated and integrated approach, the mr7 Agent can be deployed locally to conduct a thorough audit of the system's surface area, identifying not just the CVE but also the potential impact of the vulnerability based on the specific configuration of the server.
Beyond automated scanning, administrators can use the tcpdump tool to monitor for unusual KEXINIT patterns that might indicate exploitation attempts. By filtering for SSH traffic on port 22 and analyzing the packet lengths, administrators can spot anomalies that suggest an attacker is trying to trigger the heap overflow.
bash
Monitor for SSH KEXINIT packets with suspicious lengths
Assuming SSH is on default port 22
sudo tcpdump -i eth0 -X 'tcp port 22 and (tcp[((tcp[12] & 0xf0) >> 2):2] == 0x0021)'
In the table below, we compare the manual verification process with the automated approach offered by the mr7 Agent.
| Verification Method | Tools Used | Speed | Accuracy | Effort Level |
|---|---|---|---|---|
| Manual Audit | ssh -V, tcpdump, manual log review | Slow | High (if expert) | High |
| Automated Scan | OpenVAS, Nessus | Medium | High | Low |
| mr7 Agent Audit | mr7 Agent (local AI automation) | Fast | Extremely High | Very Low |
What are the Best Practices for Patching and Hardening Against CVE-2026-11023?
Patching is the primary defense against CVE-2026-11023, but a holistic security posture involves more than just updating a single package. The first priority is to apply the official security update provided by the SSH software maintainers or the OS distribution. On a Debian-based system, this is typically handled through apt-get:
bash
Update package lists and upgrade the openssh-server package
sudo apt-get update sudo apt-get install --only-upgrade openssh-server
Restart the service to apply the patch
sudo systemctl restart ssh
After patching, it is vital to verify that the service is functioning correctly and that the vulnerability has been mitigated. This can be done by running a version check again or using the mr7 Agent to perform a post-patching security audit. Hardening the SSH configuration is the next logical step. The sshd_config file should be reviewed to disable unused authentication methods and restrict access to a minimal set of users. For example, disabling root login and enforcing public key authentication significantly reduces the attack surface.
bash
/etc/ssh/sshd_config recommendations
PermitRootLogin no PasswordAuthentication no PubkeyAuthentication yes KexAlgorithms [email protected],diffie-hellman-group-exchange-sha256
Furthermore, implementing a firewall to limit SSH access to known IP addresses or a VPN subnet can prevent unauthorized actors from even reaching the SSH handshake phase. Many organizations utilize a bastion host or jump box to centralize access, ensuring that the internal infrastructure is not exposed to the public internet. By combining patching with these hardening techniques, administrators can effectively neutralize the threat posed by CVE-2026-11023.
How Does the mr7 Agent Assist in Remediation and Post-Patch Testing?
The mr7 Agent provides an automated bridge between vulnerability discovery and final remediation. When a critical vulnerability like CVE-2026-11023 is announced, the sheer volume of assets in an enterprise environment can make manual patching and verification an impossible task. The mr7 Agent solves this by automating the reconnaissance and auditing phases of the security lifecycle. It can be configured to scan the network for vulnerable SSH versions, cross-reference them with the CVE database, and then suggest the precise commands needed to apply the fix.
Beyond simple scanning, the mr7 Agent can be utilized to perform "safe" penetration testing against the patched service. For instance, it can attempt to trigger the overflow using controlled payloads to ensure that the patch has been successfully applied and the system no longer exhibits vulnerable behavior. This is far more effective than relying on a version string, which can be spoofed or backported without changing the version number displayed to the user.
One of the most powerful features of the mr7 Agent is its ability to generate a comprehensive remediation report. This report doesn't just say "update your software"; it provides context on why the update is necessary, the specific risk level (CVSS score) of CVE-2026-11023, and the potential impact of not patching. This makes it an invaluable tool for security professionals who must communicate risks to non-technical stakeholders or compliance officers.
bash
Example concept: invoking mr7 Agent to check for SSH vulnerabilities
This is a conceptual example of how mr7 Agent might be invoked via CLI
./mr7-agent --scan --service ssh --cve CVE-2026-11023 --report-type detailed
By automating these repetitive tasks, the mr7 Agent allows security teams to focus on high-level strategy rather than manual version auditing. It transforms a reactive patching cycle into a proactive security posture.
What are the Broader Implications of CVE-2026-11023 for SSH Architectures?
CVE-2026-11023 is more than just a bug; it is a reminder of the inherent risks associated with parsing complex, external input in low-level languages like C. The SSH protocol, designed decades ago, must now withstand sophisticated attacks that the original developers may not have fully anticipated. This vulnerability underscores the need for memory-safe programming practices and the adoption of safer languages for new implementations of critical network protocols.
The industry is gradually moving towards memory-safe alternatives such as Rust for implementing key components of the SSH stack. The use of languages that prevent buffer overflows at compile-time or through runtime checks (like bounds checking) would eliminate entire classes of vulnerabilities like CVE-2026-11023. For those stuck with legacy C-based implementations, the adoption of advanced fuzzing tools and static analysis—integrated into the CI/CD pipeline—is essential.
Moreover, CVE-2026-11023 highlights the importance of defenses-in-depth. A heap overflow in the SSH daemon should not lead to a total system compromise if other layers of security are in place. This includes the use of sandboxing, where the SSH process is isolated from the rest of the system, and the principle of least privilege, ensuring the daemon does not have unnecessary administrative rights. When these layers are combined, a single vulnerability becomes a manageable hurdle rather than a catastrophic failure.
Below is a comparison of the old "trusting" approach to input parsing versus the modern "zero-trust" memory management approach:
| Aspect | Legacy Approach (Vulnerable to CVE-2026-11023) | Modern Hardened Approach |
|---|---|---|
| Input Length | Trusted directly from packet header | Validated against strict limits |
| Buffer Allocation | Fixed-size or assumed size | Dynamic allocation based on validated length |
| Memory Safety | Manual pointer arithmetic (C/C++) | Memory-safe languages or smart pointers |
| Error Handling | Potential crash or undefined behavior | Graceful rejection of malformed packets |
| Testing | Manual unit testing | Fuzzing and formal verification |
Key Takeaways
- Root Cause: CVE-2026-11023 is a heap-based buffer overflow triggered by a lack of validation on the
KEXINITpacket length during SSH renegotiation. - Risk: Successful exploitation can lead to a Denial of Service (DoS) or Remote Code Execution (RCE) if the attacker can overwrite function pointers on the heap.
- Detection: Administrators should verify their SSH version (
ssh -V) and use specialized scanners or themr7 Agentto perform an automated audit of the service. - Remediation: Immediate patching of the SSH daemon is required. Additionally, hardening the
sshd_config(e.g., disabling root logins, enforcing public key auth) reduces the attack surface. - Verification: Use
tcpdumpto monitor for malformed packets and run post-patch vulnerability scans to ensure the fix is effective. - Long-term Strategy: Transitioning to memory-safe languages and implementing a zero-trust architecture minimizes the impact of future memory corruption vulnerabilities.
Frequently Asked Questions
Q: Can CVE-2026-11023 be exploited without authentication?
A: Yes, the vulnerability occurs during the SSH handshake process, which happens before the user provides credentials. This makes it a high-risk vulnerability as it can be triggered by any remote entity capable of initiating a connection to the SSH port.
Q: Is there a workaround if I cannot patch my system immediately?
A: While patching is the only permanent fix, you can mitigate risk by implementing a strict firewall rule that limits SSH access to only known, trusted IP addresses, thereby preventing anonymous remote actors from interacting with the service.
Q: Which Linux distributions are most affected by this vulnerability?
Any Linux distribution that uses the affected version of the SSH daemon is susceptible. This generally includes most mainstream distributions such as Ubuntu, CentOS, Debian, and RHEL, although the specific version number varies by distribution.
Q: Does the mr7 Agent only detect the vulnerability or can it assist in patching?
The mr7 Agent can identify the vulnerability, analyze the impact on your specific system configuration, and provide the necessary commands or scripts to automate the patching process across multiple servers.
Q: How does this vulnerability differ from a stack-based buffer overflow?
In a heap overflow, memory is corrupted in the dynamic memory area (the heap), which typically affects data objects and function pointers. A stack overflow occurs in the temporary storage area for function calls, often targeting the return address of the current function to redirect execution flow.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.