Malware Analysis for Beginners: Static & Dynamic Techniques

Malware Analysis for Beginners: Static & Dynamic Techniques
Malware analysis is a crucial skill for any cybersecurity professional. It involves examining malicious software to understand its behavior, capabilities, and potential impact. Whether you're a novice or looking to refine your skills, this guide will walk you through the fundamentals of static and dynamic analysis, sandboxing, and how AI-assisted tools can streamline the process.
What is Malware Analysis?
Malware analysis is the process of examining malware to identify its purpose, functionality, and potential threats. This analysis is divided into two main categories: static analysis and dynamic analysis.
Static Analysis
Static analysis involves examining a malicious program without executing it. This method is useful for quickly identifying potential threats and understanding the code structure. Key techniques include:
-
Code Review: Manually inspecting the source code or decompiled binary to identify suspicious functions, APIs, and patterns.
-
String Analysis: Searching for meaningful strings within the binary that might indicate malicious intent, such as URLs, file paths, or command-line options.
-
Hash Comparison: Checking the hash value of a file against known malware databases to identify matches.
-
PE Header Analysis: Examining the Portable Executable (PE) header for anomalies that might suggest malicious modifications.
Example
Suppose you have a suspicious executable. You can use tools like strings to extract and analyze strings:
bash
strings suspicious_exe | grep -i 'http'
This command searches for HTTP strings, which could indicate network communication.
Dynamic Analysis
Dynamic analysis involves executing the malware in a controlled environment to observe its behavior. This method provides insights into how the malware interacts with the system and network. Key techniques include:
-
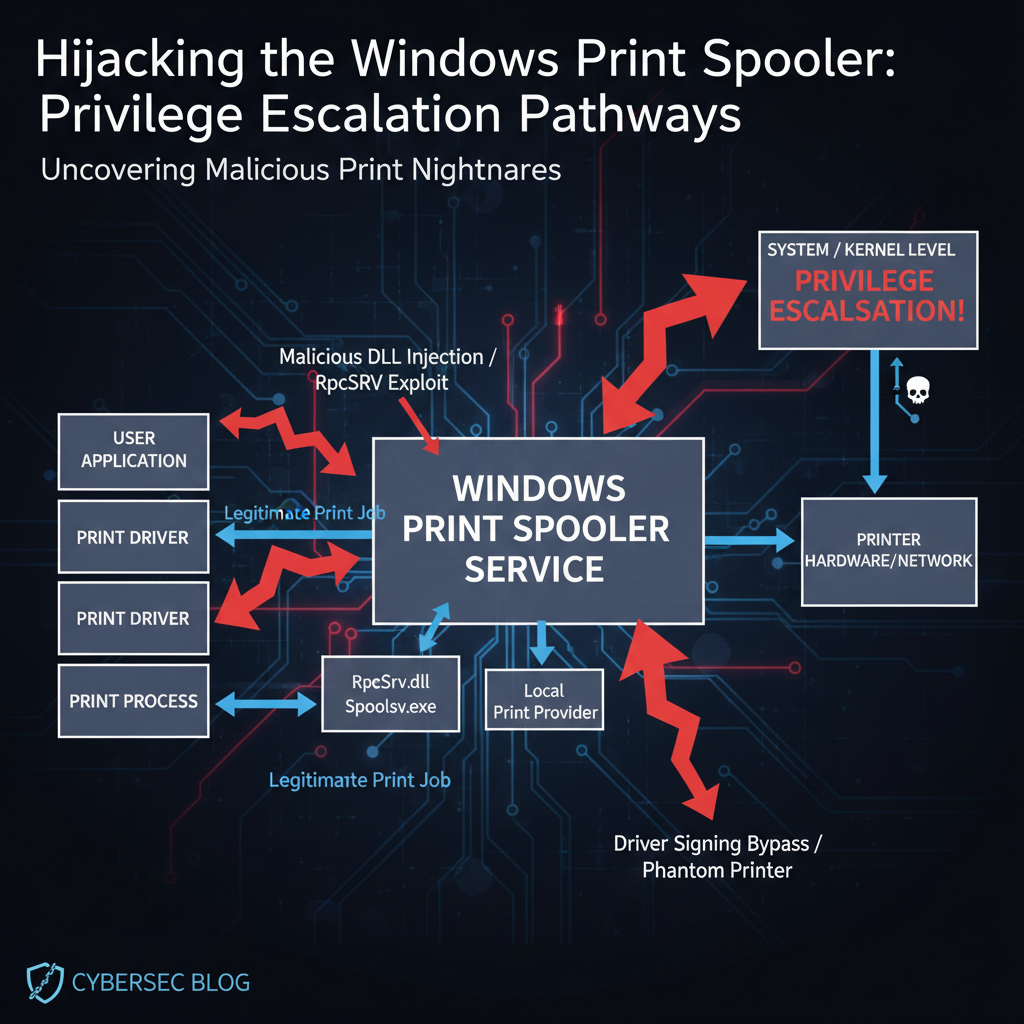
Behavior Monitoring: Using tools to monitor system calls, registry changes, and network activity.
-
Debugging: Step-by-step execution of the malware to understand its flow and identify key functions.
-
Memory Analysis: Examining the memory dump to identify injected code, hidden processes, and other artifacts.
Example
You can use strace on Linux to monitor system calls made by a suspicious process:
bash
strace -p
This command attaches to the process and logs all system calls, helping you understand its behavior.
Try it yourself: Use mr7.ai's AI models to automate this process, or download mr7 Agent for local automated pentesting. Start free with 10,000 tokens.
Sandboxing
Sandboxing is a technique used to create an isolated environment for executing and analyzing malware. It prevents the malware from affecting the host system while allowing observers to monitor its behavior. Popular sandboxing tools include Cuckoo Sandbox and Firejail.
Example
To run a suspicious executable in a sandbox using Firejail:
bash
firejail suspicious_exe
This command executes the malware in a restricted environment, containing any potential damage.
AI-Assisted Malware Analysis
AI tools like those offered by mr7.ai can significantly enhance malware analysis by identifying complex patterns and automating repetitive tasks. Here's how AI can help:
-
KaliGPT: This tool can assist in automating static analysis tasks, such as identifying suspicious API calls and strings within malware binaries.
-
0Day Coder: Useful for dynamic analysis, 0Day Coder can help in monitoring and analyzing the behavior of malware in real-time, providing insights into its network and system interactions.
-
DarkGPT: Ideal for sandboxing, DarkGPT can create and manage isolated environments, ensuring that malware is contained while its behavior is observed.
-
OnionGPT: This tool can help in analyzing Tor-based malware, providing deep insights into its anonymity and communication patterns.
Example
To use KaliGPT for static analysis:
bash
kali-gpt analyze suspicious_exe
This command leverages AI to automatically identify and report on suspicious elements within the executable.
Conclusion
Malware analysis is a multifaceted discipline that combines static and dynamic techniques to understand and mitigate threats. By incorporating AI tools like those from mr7.ai, security researchers can enhance their efficiency and accuracy. Whether you're just starting or looking to upgrade your skills, these techniques and tools will be invaluable in your journey.
🔓 Unlock Your Security Potential
Stop spending hours on manual tasks. Let AI handle the heavy lifting while you focus on what matters - finding vulnerabilities.
Key Takeaways
- Malware analysis is a fundamental cybersecurity skill involving the examination of malicious software to understand its behavior and impact.
- Static analysis involves examining malware without executing it, focusing on code structure, strings, and metadata to identify potential threats.
- Dynamic analysis involves executing malware in a controlled environment to observe its real-time behavior, such as file system changes, network activity, and process manipulation.
- Sandboxing provides a safe, isolated environment for dynamic analysis, preventing malware from affecting the host system.
- Combining both static and dynamic analysis techniques offers a comprehensive understanding of malware, revealing both its potential and active behaviors.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: What is the primary difference between static and dynamic malware analysis?
Static analysis examines malware's code and structure without execution, looking for indicators like strings, imports, and metadata. Dynamic analysis, conversely, involves running the malware in a controlled environment to observe its real-time behavior, such as network connections, file modifications, and process injections. Both are crucial for a complete understanding of a threat.
Q: Why is sandboxing essential for dynamic malware analysis?
Sandboxing provides an isolated and controlled environment, preventing the malicious software from infecting the analyst's host system or network. It allows for safe observation of the malware's full execution flow, including its attempts to persist, communicate, or spread, without risking actual damage. This isolation is critical for safely gathering behavioral intelligence.
Q: What are some common artifacts or indicators an analyst looks for during static analysis?
During static analysis, an analyst typically looks for suspicious strings (e.g., URLs, API calls, error messages), imported functions (especially those related to system modification or networking), packed or obfuscated code, and metadata like compilation timestamps or author information. These elements can reveal clues about the malware's purpose and capabilities without executing it.
Q: How can AI tools help with malware analysis, especially for beginners?
AI tools like mr7.ai, KaliGPT, and mr7 Agent can significantly assist beginners by automating repetitive tasks, identifying patterns in large datasets, and providing contextual information. They can help in quickly triaging samples, suggesting relevant analysis techniques, and even interpreting complex code or behavioral logs, thereby accelerating the learning curve and improving efficiency.
Q: What's the best way for a beginner to start practicing malware analysis techniques?
A great way for beginners to start is by setting up a safe virtual lab environment with appropriate analysis tools, like a Windows VM and a Linux distribution with pre-installed tools. Begin with simple, well-documented malware samples, practicing both static techniques (like string analysis and PE file examination) and dynamic techniques within a sandbox. To get hands-on experience and explore advanced capabilities, try out mr7.ai's free tokens for access to powerful cybersecurity tools and educational resources.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.