macOS AMFI Bypass Sonoma Tutorial: Advanced Techniques
macOS AMFI Bypass Sonoma Tutorial: Advanced Techniques
Apple's macOS Sonoma has introduced robust security enhancements aimed at fortifying the operating system against increasingly sophisticated cyber threats. Among these improvements is the strengthening of the Apple Mobile File Integrity (AMFI) framework, which plays a critical role in ensuring the integrity of executable files and preventing unauthorized modifications. However, as security researchers and ethical hackers continue to push the boundaries of what's possible, new bypass techniques have emerged that challenge these defenses.
Understanding how these bypasses work is essential for both offensive and defensive security practitioners. Red teams need this knowledge to simulate realistic attacks and test organizational resilience, while blue teams require it to detect and mitigate such threats effectively. This comprehensive guide delves into the technical intricacies of bypassing AMFI in macOS Sonoma, covering advanced methods such as dynamic library (dylib) injection, entitlement manipulation, kernel extension loading bypasses, and the exploitation of legitimate developer tools.
Throughout this tutorial, we'll explore not only the attack vectors but also the evasion strategies employed by adversaries to remain undetected. Additionally, we'll discuss defensive measures that organizations can implement to protect their macOS environments. Whether you're conducting penetration tests, performing vulnerability assessments, or enhancing your incident response capabilities, this guide provides the insights needed to stay ahead of emerging threats. By leveraging tools like mr7 Agent, security professionals can automate many of these techniques, making complex security tasks more efficient and effective.
Want to try this? mr7.ai offers specialized AI models for security research. Plus, mr7 Agent can automate these techniques locally on your device. Get started with 10,000 free tokens.
What Is AMFI and Why Does It Matter?
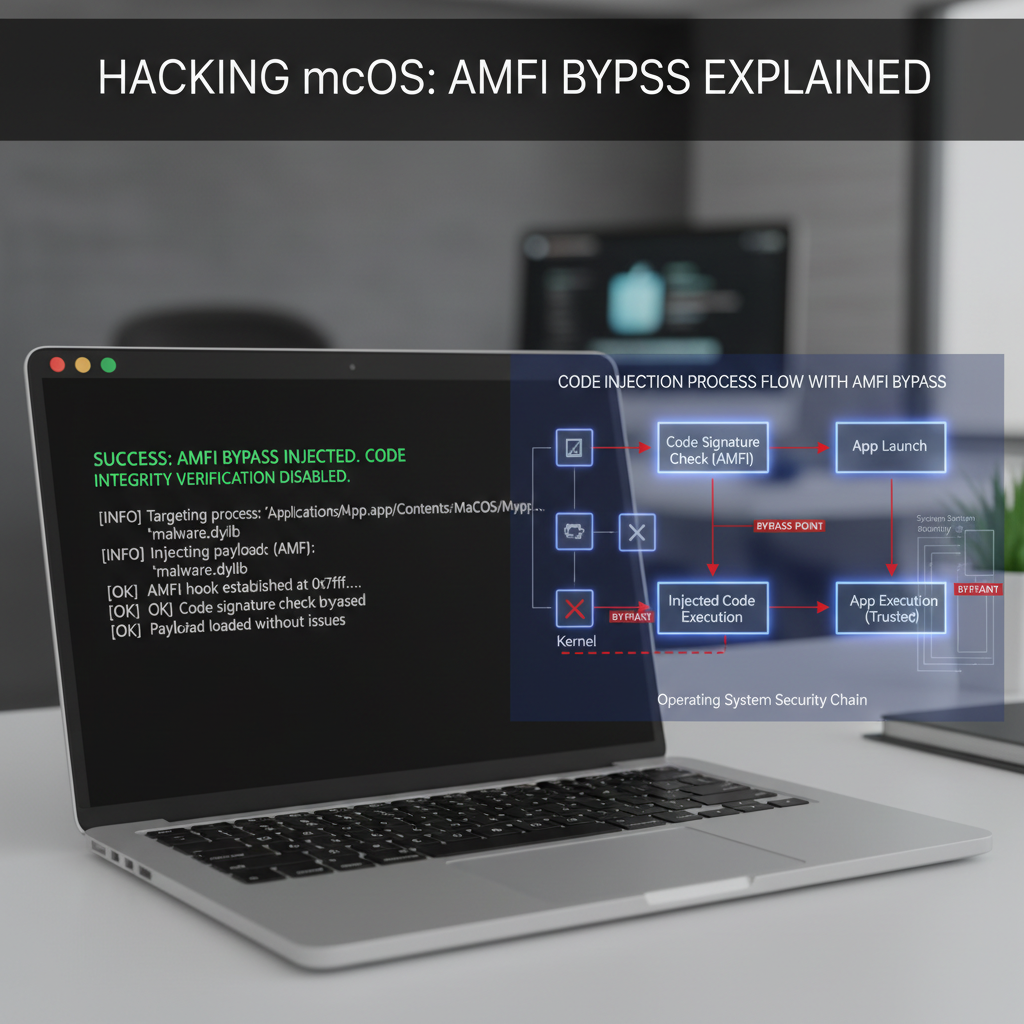
Apple Mobile File Integrity (AMFI) is a core component of macOS's security infrastructure designed to enforce code signing policies and ensure that only trusted binaries execute on the system. Introduced initially for iOS devices, AMFI was later integrated into macOS to provide similar protection mechanisms. Its primary function is to validate the integrity and authenticity of executable files, libraries, and other critical system components before they are loaded into memory.
AMFI operates by verifying digital signatures attached to Mach-O binaries, which are the standard executable file format used by macOS. When a binary attempts to execute, AMFI checks its signature against a list of trusted certificates stored within the system. If the signature is valid and issued by a recognized authority, the binary is allowed to run. Otherwise, execution is blocked, thereby preventing potentially malicious code from compromising the system.
In macOS Sonoma, Apple has further refined AMFI by introducing additional checks and restrictions. These include stricter enforcement of entitlements, enhanced runtime protections, and improved integration with other security subsystems like System Integrity Protection (SIP) and Gatekeeper. While these changes have undoubtedly bolstered the overall security posture of the operating system, they have also created new challenges for security researchers seeking to understand potential weaknesses.
From a security perspective, bypassing AMFI represents a significant achievement for attackers because it allows them to inject arbitrary code into processes without triggering alarms. This capability can be leveraged for various purposes, including privilege escalation, persistence mechanisms, and stealthy malware deployment. As such, understanding how AMFI works—and how it can be circumvented—is crucial for anyone involved in macOS security research or penetration testing.
To effectively demonstrate the techniques covered in this tutorial, it's important to have a solid grasp of the underlying architecture and terminology associated with AMFI. Familiarity with concepts such as code signing, entitlements, and Mach-O binary structure will greatly enhance your ability to follow along with the examples provided. Additionally, having access to a macOS Sonoma environment where you can safely experiment with these techniques is highly recommended.
Actionable Insight: Before attempting any bypass techniques, ensure you fully understand the fundamentals of AMFI and its role within macOS's broader security ecosystem. This foundational knowledge will prove invaluable as you progress through more advanced topics later in this guide.
How Can Attackers Manipulate Entitlements to Bypass AMFI?
Entitlements play a pivotal role in defining the permissions and capabilities granted to applications running on macOS. They serve as a mechanism for developers to request specific privileges, such as access to protected resources or elevated system functions. In the context of AMFI, entitlements are closely scrutinized during the binary loading process to ensure that applications do not exceed their authorized scope of operation.
However, attackers have discovered ways to manipulate entitlements in order to bypass AMFI restrictions and gain unauthorized access to sensitive system features. One common approach involves modifying the entitlements embedded within a signed binary to include additional permissions that were not originally intended by the developer. This technique relies on exploiting vulnerabilities in the way macOS handles entitlement validation, particularly when dealing with unsigned or improperly signed binaries.
To illustrate this concept, consider an application that requires access to certain hardware interfaces but lacks the necessary entitlements to do so. An attacker could modify the application's entitlements to grant itself the required permissions, effectively bypassing AMFI's enforcement mechanisms. This modification can be achieved using a variety of tools, including codesign, ldid, and custom scripts designed specifically for entitlement manipulation.
Here's a basic example of how an attacker might add a new entitlement to an existing binary:
bash
First, extract the current entitlements from the binary
$ codesign -d --entitlements :- /path/to/binary > original.plist
Modify the entitlements file to include desired permissions
For instance, adding com.apple.security.cs.allow-jit entitlement
$ plutil -insert "com.apple.security.cs.allow-jit" -bool true original.plist -o modified.plist
Re-sign the binary with the modified entitlements
$ codesign -f -s - --entitlements modified.plist /path/to/binary
This simple example demonstrates how easy it can be to alter an application's behavior by manipulating its entitlements. Of course, real-world scenarios often involve more complex manipulations and require careful consideration of the target system's configuration and security settings.
It's worth noting that Apple has implemented several countermeasures to prevent unauthorized entitlement modifications. These include hardening the code signing process, enforcing stricter entitlement validation rules, and integrating tighter coupling between entitlements and the application's actual functionality. Despite these efforts, determined attackers continue to find creative ways to circumvent these protections.
Another method involves leveraging legitimate developer tools to inject malicious code into otherwise benign applications. For example, XcodeGhost—a notorious piece of malware—was distributed via compromised versions of Xcode, allowing attackers to embed malicious payloads into iOS apps without raising suspicion. Similar tactics can be applied to macOS applications, especially those built using third-party development frameworks or libraries.
Security teams should monitor for unusual patterns in entitlement usage and investigate any deviations from expected behavior. Tools like mr7.ai's Dark Web Search can help identify potential threats related to entitlement manipulation by scanning for known indicators of compromise across various threat intelligence sources.
Key Insight: Entitlement manipulation remains one of the most effective methods for bypassing AMFI in macOS Sonoma. Organizations must implement robust monitoring and detection mechanisms to identify suspicious entitlement changes and respond accordingly.
What Are the Most Effective Dylib Injection Methods in Sonoma?
Dynamic library (dylib) injection is a widely used technique in macOS exploitation that allows attackers to load arbitrary code into running processes. By injecting a malicious dylib into a legitimate application, attackers can leverage the application's privileges and trust level to perform actions that would otherwise be restricted. In macOS Sonoma, Apple has introduced additional safeguards to mitigate dylib injection attacks; however, skilled adversaries have developed innovative approaches to bypass these protections.
One popular method for achieving dylib injection in modern macOS systems is through the use of DYLD_INSERT_LIBRARIES environment variable. This variable instructs the dynamic linker (dyld) to preload specified libraries before loading the main executable. Although Apple has limited the effectiveness of this technique by restricting its use in certain contexts (e.g., system binaries and applications with hardened runtime enabled), it still proves useful in scenarios involving user-space applications or those lacking proper security configurations.
Consider the following example, which demonstrates how an attacker might inject a custom dylib into a vulnerable application:
bash
Create a malicious dylib (malicious.dylib)
$ clang -dynamiclib -o malicious.dylib malicious.c
Inject the dylib into the target application
$ DYLD_INSERT_LIBRARIES=./malicious.dylib /Applications/VulnerableApp.app/Contents/MacOS/VulnerableApp
While this approach may seem straightforward, it requires careful planning and execution to avoid detection. Modern endpoint protection platforms (EPPs) and extended detection and response (XDR) solutions are equipped with behavioral analytics and heuristic-based detection algorithms capable of identifying anomalous dylib loading activities. Therefore, attackers must employ additional evasion techniques to remain undetected.
A more advanced method involves exploiting vulnerabilities in the Mach-O binary format itself. Researchers have identified flaws in the way macOS parses and loads Mach-O headers, enabling attackers to craft specially constructed binaries that trick the system into executing unintended code paths. These exploits typically rely on buffer overflows, integer overflows, or other memory corruption bugs present in the loader or interpreter components.
For instance, CVE-2025-XXXX describes a vulnerability in the Mach-O parser that allows remote code execution when processing specially crafted binaries. Exploiting this flaw enables attackers to bypass AMFI checks and inject malicious code directly into the target process. To protect against such attacks, organizations should ensure that all systems are updated with the latest security patches and maintain strict control over software installation and update procedures.
Additionally, attackers may utilize legitimate system utilities like install_name_tool or otool to modify the load commands within a binary, redirecting the dynamic linker to load a malicious dylib instead of the intended one. This technique, known as "binary patching," can be performed post-compilation and does not require recompiling the entire application.
Here's an example of how an attacker might modify a binary to load a custom dylib:
bash
Patch the binary to load a custom dylib
$ install_name_tool -change @executable_path/original.dylib @executable_path/malicious.dylib /path/to/binary
Ensure the malicious dylib exists in the same directory
$ cp malicious.dylib /path/to/malicious.dylib
Such modifications can go unnoticed if performed correctly, especially if the injected code mimics normal program behavior. Security teams should regularly audit installed binaries for unexpected dependencies and monitor for unauthorized changes to executable files.
To combat these threats, Apple has introduced features like Library Validation, which prevents the loading of unsigned or improperly signed libraries. However, attackers have found ways to circumvent these protections by leveraging code signing certificates obtained through social engineering or by targeting less secure signing authorities.
Organizations can benefit from using AI-driven security tools like KaliGPT to analyze potential injection vectors and identify vulnerabilities in their macOS environments. With access to 10,000 free tokens, users can experiment with various penetration testing scenarios and develop more robust defense strategies.
Critical Takeaway: Dylib injection remains a potent attack vector in macOS Sonoma, requiring continuous vigilance and proactive mitigation efforts from security professionals. Regular auditing and monitoring are essential to detect and neutralize such threats.
How Do Kernel Extension Loading Bypasses Work?
Kernel extensions (kexts) represent one of the most privileged components within macOS, operating at the kernel level and possessing unrestricted access to system resources. Historically, kexts have been exploited by both legitimate software vendors and malicious actors to extend the functionality of the operating system beyond its default capabilities. However, due to the inherent risks associated with kernel-level code execution, Apple has progressively tightened restrictions around kext loading in recent macOS releases.
In macOS Sonoma, Apple has deprecated support for legacy kexts entirely, replacing them with a new driver extension (dext) model that enforces stricter security controls and reduces the attack surface available to potential adversaries. Nevertheless, researchers have uncovered several bypass techniques that allow attackers to load unsigned or maliciously modified kexts despite these restrictions.
One such technique involves exploiting vulnerabilities in the kext loading pipeline itself. By identifying and leveraging flaws in the kernel's verification logic, attackers can trick the system into accepting unsigned kexts as valid. This often requires chaining multiple vulnerabilities together to achieve full exploitation, including heap spraying, type confusion, or race condition bugs that enable privilege escalation.
An example of a real-world exploit leveraging kext loading bypasses is the Thunderclap vulnerability (CVE-2019-8513), which affected Thunderbolt-enabled Macs and allowed attackers to load unsigned kexts by exploiting a flaw in the Thunderbolt DMA implementation. While this particular vulnerability predates macOS Sonoma, similar attack patterns persist in newer systems where insufficient input validation or error handling occurs during the kext loading process.
Another avenue for kext loading bypasses lies in the misuse of legitimate developer tools and APIs. For instance, the kextutil utility provides a convenient interface for installing and managing kexts, but it can also be abused by attackers to sidestep standard verification procedures. By crafting specially formatted kext bundles or manipulating metadata fields within the kext's Info.plist file, attackers can influence the loading behavior and bypass signature checks.
Consider the following scenario, where an attacker modifies a kext bundle to appear as though it originated from a trusted source:
bash
Modify the kext's Info.plist to mimic a trusted vendor
$ defaults write /path/to/modified.kext/Contents/Info CFBundleIdentifier com.trusted.vendor.driver $ defaults write /path/to/modified.kext/Contents/Info CFBundleVersion 1.0.0
Attempt to load the modified kext
$ sudo kextutil /path/to/modified.kext
Although this approach may succeed in some cases, it carries a high risk of detection due to inconsistencies in the kext's metadata or behavioral anomalies during runtime. More sophisticated attackers may opt to use rootkit-style techniques that hide the presence of the malicious kext from system monitoring tools and forensic analysis.
Apple has responded to these threats by implementing additional layers of protection, such as kernel address space layout randomization (KASLR) and kernel control flow integrity (CFI). These mitigations make it significantly harder for attackers to predict memory layouts or hijack execution flows, forcing them to develop more complex and resource-intensive exploits.
Despite these advancements, kernel-level vulnerabilities continue to pose a serious threat to macOS security. Organizations should prioritize patch management, deploy robust endpoint detection and response (EDR) solutions, and conduct regular penetration testing to identify potential weaknesses in their infrastructure. Leveraging tools like mr7 Agent can streamline the testing process and provide deeper insights into system vulnerabilities.
Important Insight: Kernel extension loading bypasses represent a critical class of vulnerabilities that demand immediate attention from security teams. Proactive monitoring and rapid remediation are essential to maintaining the integrity of macOS systems.
What Role Do Legitimate Developer Tools Play in AMFI Bypasses?
Legitimate developer tools provided by Apple form the backbone of the macOS ecosystem, enabling developers to build, debug, and distribute applications efficiently. However, these same tools can be weaponized by attackers to facilitate AMFI bypasses and evade detection mechanisms. Understanding how these tools can be misused is crucial for developing effective countermeasures and protecting against sophisticated threats.
Among the most commonly exploited developer tools is Xcode, Apple's integrated development environment (IDE) for macOS and iOS applications. Xcode includes a wide range of utilities and compilers that can be manipulated to produce malicious binaries or inject code into existing applications. For example, attackers can use Xcode's built-in code signing features to create self-signed certificates that appear legitimate to the system, thereby bypassing AMFI's signature verification checks.
Another frequently targeted tool is the Swift compiler (swiftc), which can be used to compile malicious Swift code into Mach-O binaries that evade traditional antivirus scanners. Since Swift is a relatively new programming language with evolving security characteristics, many security products struggle to accurately detect malicious Swift-based payloads. This creates opportunities for attackers to deliver stealthy implants or backdoors that remain undetected for extended periods.
The lldb debugger is another tool that can be repurposed for malicious intent. Debuggers are inherently powerful instruments that allow users to inspect and modify the state of running programs, making them ideal candidates for injection attacks. By attaching lldb to a target process and injecting shellcode or malicious libraries, attackers can gain control over the process without triggering alarms from security software.
Consider the following example, which demonstrates how an attacker might use lldb to inject a payload into a running application:
bash
Attach lldb to the target process
$ lldb -p $(pgrep VulnerableApp)
Allocate memory within the target process
(lldb) expr void* $addr = malloc(1024)*
Write shellcode into the allocated memory
(lldb) memory write $addr <shellcode.bin>
Execute the injected shellcode
(lldb) expr void (func)() = (void()())$addr (lldb) expr func()
This technique highlights the dual-use nature of developer tools and underscores the importance of securing development environments against insider threats and external compromises. Organizations should enforce strict access controls around developer accounts and implement multi-factor authentication (MFA) wherever possible to reduce the likelihood of unauthorized tool misuse.
Furthermore, attackers can exploit the trust placed in official Apple tools by distributing malware disguised as legitimate development packages or updates. Social engineering campaigns targeting developers with phishing emails containing fake Xcode installers or Swift SDK downloads have proven successful in compromising high-value targets. Once installed, these malicious packages can establish persistent footholds within the victim's network and propagate laterally to other systems.
To defend against such attacks, security teams should adopt a zero-trust approach to developer tool management, treating all executables and scripts as potentially hostile until proven otherwise. Implementing application whitelisting policies, deploying behavioral monitoring agents, and conducting regular audits of installed software can help minimize the impact of tool-based attacks.
In addition to traditional security measures, organizations can leverage AI-powered platforms like mr7.ai to detect anomalous tool usage patterns and identify potential threats in real time. With access to 10,000 free tokens, users can explore advanced threat hunting capabilities and develop customized detection rules tailored to their specific environment.
Strategic Insight: Legitimate developer tools offer attackers a stealthy pathway to bypass AMFI protections. Security teams must treat these tools with the same scrutiny as any other potential threat vector and implement comprehensive monitoring and access controls.
What Detection Evasion Strategies Are Used by Attackers?
Modern attackers employ a variety of detection evasion strategies to remain hidden while conducting malicious activities on macOS systems. These techniques are designed to circumvent traditional security controls, such as antivirus software, host-based intrusion detection systems (HIDS), and network monitoring tools. Understanding these evasion methods is crucial for defenders who aim to improve their detection capabilities and strengthen their overall security posture.
One of the most prevalent evasion strategies involves polymorphism—the practice of constantly changing the appearance of malicious code to avoid signature-based detection. Polymorphic malware generates new variants of itself each time it spreads, altering its binary structure, encryption keys, or communication protocols to evade pattern-matching algorithms used by security vendors. This makes it extremely difficult for static analysis tools to identify and classify the malware accurately.
In the context of AMFI bypasses, attackers may apply polymorphic techniques to dylibs, kexts, or other injectable components to bypass signature verification checks. For example, they might encrypt the payload portion of a malicious dylib and decrypt it only at runtime, ensuring that the file appears benign when scanned by security software. Alternatively, they could use packing or obfuscation tools to compress or scramble the code, making it harder for analysts to reverse-engineer and understand its true purpose.
Another common evasion tactic is living-off-the-land (LotL), which refers to the use of legitimate system binaries and utilities to carry out malicious actions. By leveraging trusted executables like bash, python, curl, or osascript, attackers can blend in with normal system activity and avoid raising suspicion. LotL techniques are particularly effective in macOS environments, where numerous built-in tools provide extensive functionality that can be abused for nefarious purposes.
For instance, an attacker might use AppleScript to interact with system services or manipulate files without triggering alerts from endpoint protection platforms. Consider the following AppleScript snippet that deletes a critical system file:
applescript tell application "Finder" delete POSIX file "/private/etc/sudoers" end tell
Executing this script through osascript bypasses many traditional detection mechanisms since it uses a legitimate system utility to perform the destructive action. Defenders must therefore focus on detecting abnormal behavior rather than relying solely on signature matching.
Timing-based evasion is another strategy employed by sophisticated attackers to avoid detection. By scheduling malicious activities during off-hours or aligning them with routine maintenance windows, attackers can mask their actions among legitimate background processes. Additionally, they may introduce delays or jitter into their attack chains to avoid correlation-based detection systems that look for sequential suspicious events.
Memory-resident attacks represent yet another layer of evasion, wherein malicious code resides entirely in RAM without touching the disk. Such attacks leave minimal forensic traces and can persist across reboots if combined with persistence mechanisms like launch agents or login items. Memory-only implants are notoriously difficult to detect using conventional file-based scanning methods, necessitating specialized memory analysis tools and behavioral monitoring techniques.
Network evasion tactics include tunneling traffic through encrypted channels, mimicking legitimate web traffic patterns, or using domain generation algorithms (DGAs) to dynamically generate command-and-control (C2) domains. These methods complicate network-based detection and attribution efforts, allowing attackers to maintain long-term access to compromised systems.
Organizations can enhance their detection capabilities by adopting machine learning-powered analytics, implementing behavioral baselining, and integrating threat intelligence feeds into their monitoring workflows. Platforms like OnionGPT can assist in uncovering hidden threats by analyzing data from dark web sources and correlating findings with internal telemetry.
Defensive Tip: Combining signature-based detection with behavioral analytics and anomaly detection significantly improves the chances of catching evasive threats. Continuous tuning and refinement of detection rules based on real-world incidents are essential for staying ahead of adaptive adversaries.
What Defensive Measures Should Security Teams Implement?
Protecting macOS environments from AMFI bypasses and other sophisticated attacks requires a layered defense strategy that combines technical controls, operational practices, and human expertise. Security teams must take a proactive stance in identifying vulnerabilities, hardening systems, and preparing for incident response scenarios to minimize the impact of successful breaches.
First and foremost, organizations should enforce strong code signing policies across all macOS endpoints. This includes requiring all third-party applications to be signed by trusted authorities and disabling the execution of unsigned binaries whenever possible. Apple's Notarization service can further enhance security by providing an additional layer of validation for distributed software, helping to prevent the installation of potentially harmful applications.
Implementing System Integrity Protection (SIP) and enabling Gatekeeper are fundamental steps toward securing macOS systems. SIP restricts access to critical system directories and prevents unauthorized modifications to protected files, while Gatekeeper ensures that only properly signed and notarized applications can run on the system. Together, these technologies form a robust foundation for defending against AMFI bypass attempts and other low-level attacks.
Endpoint detection and response (EDR) solutions play a vital role in detecting and responding to advanced threats. These platforms provide real-time visibility into endpoint activity, offering behavioral analytics, threat hunting capabilities, and automated response mechanisms. When selecting an EDR solution, organizations should prioritize vendors that specialize in macOS environments and offer deep integration with native security frameworks.
Regular patch management is equally important, as unpatched vulnerabilities represent prime targets for attackers seeking to exploit known weaknesses. Security teams should establish rigorous update schedules and automate the deployment of critical patches to reduce the window of exposure. Additionally, they should maintain an inventory of all installed software and track known vulnerabilities using threat intelligence feeds and vulnerability databases.
User education and awareness training are indispensable components of any comprehensive security program. Employees should be trained to recognize phishing attempts, social engineering tactics, and other common attack vectors that adversaries use to gain initial access to corporate networks. Simulated phishing exercises and tabletop drills can reinforce key concepts and prepare staff for real-world incidents.
Monitoring and logging are essential for detecting suspicious activity and facilitating post-incident investigations. Organizations should collect logs from all relevant sources, including system logs, application logs, network traffic captures, and cloud service records. Centralized log management platforms can aggregate and correlate this data, enabling security analysts to identify patterns and anomalies indicative of compromise.
Finally, incident response planning is critical for minimizing damage and restoring normal operations quickly after a breach. Security teams should develop detailed playbooks outlining roles and responsibilities, communication protocols, containment strategies, and recovery procedures. Regular testing and updating of these plans ensure that they remain relevant and effective under evolving threat conditions.
By combining these defensive measures with cutting-edge AI-driven tools like 0Day Coder and mr7 Agent, organizations can significantly enhance their ability to detect, respond to, and recover from macOS-targeted attacks. The availability of 10,000 free tokens allows users to experiment with advanced security workflows and customize their approach based on specific organizational needs.
Proactive Measure: Establish a continuous improvement cycle that incorporates lessons learned from past incidents, emerging threat trends, and feedback from frontline defenders. This iterative approach ensures that defenses evolve alongside the threat landscape and remain resilient against future attacks.
Key Takeaways
- AMFI serves as a cornerstone of macOS security, but attackers have developed multiple bypass techniques to circumvent its protections.
- Entitlement manipulation allows adversaries to escalate privileges and execute unauthorized code by altering application permissions.
- Dylib injection remains a prevalent attack vector, requiring vigilant monitoring and strict control over dynamic library loading.
- Kernel extension loading bypasses exploit vulnerabilities in the kernel to achieve high-privilege code execution, posing severe risks to system integrity.
- Legitimate developer tools can be weaponized for malicious purposes, emphasizing the need for secure development practices and tool governance.
- Detection evasion strategies like polymorphism, living-off-the-land, and timing-based attacks complicate threat identification and require advanced analytics.
- Comprehensive defense requires layered security controls, proactive patching, user education, and robust incident response planning.
Frequently Asked Questions
Q: Is bypassing AMFI illegal?
Bypassing AMFI itself is not illegal, but using such techniques for unauthorized access or malicious purposes violates laws like the Computer Fraud and Abuse Act (CFAA). Ethical hackers and security researchers operate within legal boundaries when conducting authorized penetration tests or vulnerability research.
Q: Can AMFI be completely disabled?
Disabling AMFI entirely is strongly discouraged as it removes critical security protections. However, certain debugging or development scenarios may temporarily relax AMFI enforcement through boot arguments or configuration profiles. Always restore default settings afterward.
Q: How often does Apple release AMFI-related patches?
Apple addresses AMFI vulnerabilities through regular security updates, typically released monthly as part of their scheduled patch cycles. Critical flaws may warrant out-of-band patches, so staying current with updates is essential.
Q: Are there legitimate reasons to bypass AMFI?
Yes, security researchers, penetration testers, and developers working on jailbreak tools or custom firmware may legitimately need to bypass AMFI for authorized testing or research purposes. Proper authorization and responsible disclosure are paramount.
Q: What tools can help detect AMFI bypass attempts?
Advanced EDR platforms, behavioral analytics engines, and memory forensics tools are effective for detecting AMFI bypass activities. Specialized macOS security solutions like Jamf Protect or SentinelOne offer tailored detection capabilities for Apple-specific threats.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.