CVE-2026-41287: Kubernetes RBAC Bypass Exploit Analysis
CVE-2026-41287: Comprehensive Analysis of the Critical Kubernetes RBAC Bypass Vulnerability
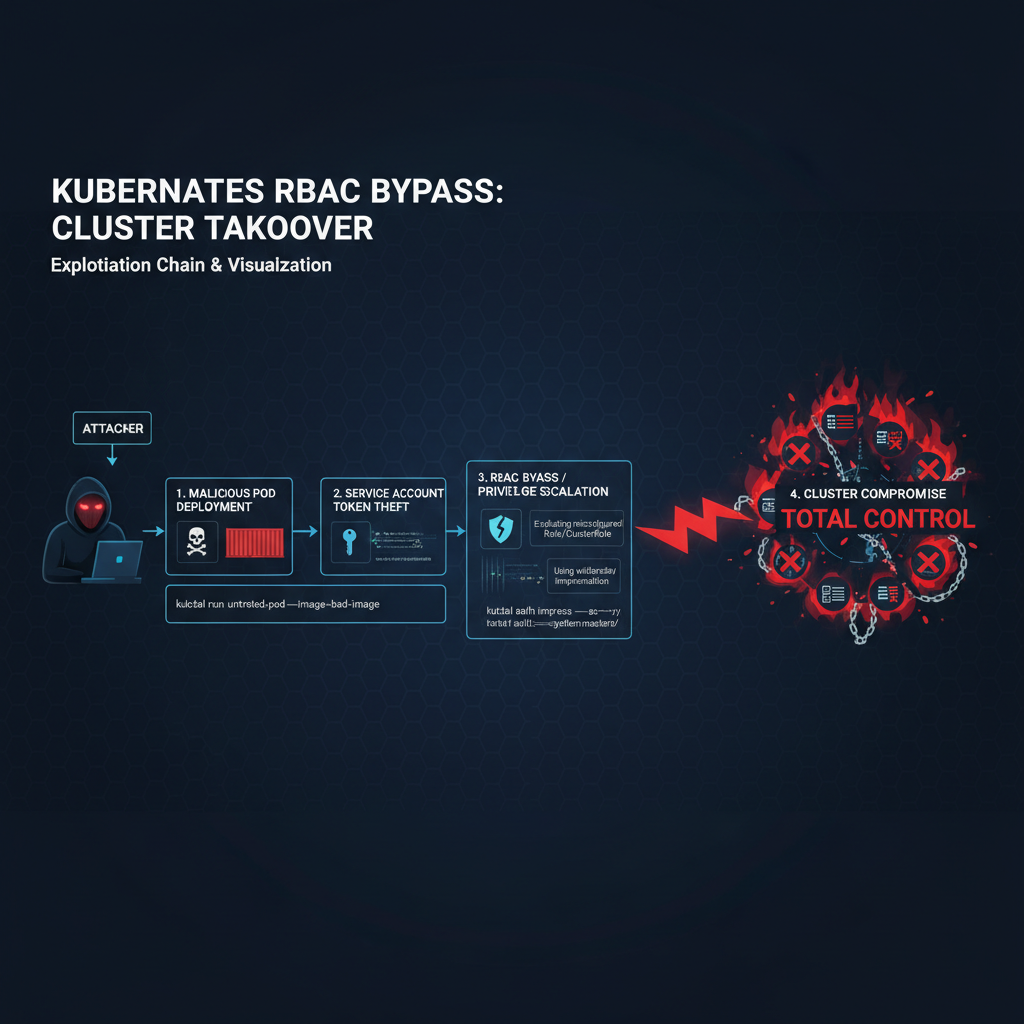
In early 2026, the Kubernetes security community was shaken by the disclosure of CVE-2026-41287, a critical vulnerability affecting Kubernetes clusters running versions v1.29 through v1.31. This high-severity flaw represents a significant threat to container orchestration security, allowing authenticated attackers to bypass Role-Based Access Control (RBAC) mechanisms and escalate privileges within cluster environments. With active exploitation reports emerging from multiple cloud providers and enterprise deployments, understanding this vulnerability's mechanics, impact, and mitigation strategies has become paramount for security professionals.
The vulnerability stems from a design oversight in the Kubernetes API server's authorization logic, specifically in how it handles complex role binding scenarios involving aggregated roles and cross-namespace references. Attackers who possess valid authentication credentials can exploit this weakness to gain unauthorized access to sensitive cluster resources, potentially leading to full cluster compromise. What makes CVE-2026-41287 particularly dangerous is its stealthy nature – exploitation attempts often leave minimal traces in standard audit logs, making detection challenging without specialized monitoring approaches.
This comprehensive analysis delves deep into the technical aspects of CVE-2026-41287, examining the underlying vulnerability mechanism, exploitation requirements, and real-world implications for container orchestration security. We'll explore how organizations can detect attempted exploitation through advanced log analysis and monitoring techniques, and provide actionable mitigation strategies that go beyond simple patching. Additionally, we'll demonstrate how modern AI-powered security tools like mr7 Agent can automate vulnerability detection and security assessments, helping teams stay ahead of threats like this.
How Does CVE-2026-41287 Allow Kubernetes RBAC Bypass?
CVE-2026-41287 exploits a fundamental flaw in Kubernetes' authorization engine when processing aggregated ClusterRoles with cross-namespace subject bindings. The vulnerability occurs during the evaluation of RoleBinding and ClusterRoleBinding objects that reference subjects across different namespaces, creating a race condition that allows unauthorized privilege escalation.
To understand the root cause, let's examine the normal RBAC evaluation process in Kubernetes. When a user makes an API request, the authorization module checks whether the user possesses the required permissions by evaluating all applicable RoleBindings and ClusterRoleBindings. However, CVE-2026-41287 introduces a timing window where concurrent modifications to RBAC objects can cause the authorization engine to incorrectly evaluate permissions.
yaml
Example of vulnerable ClusterRole configuration
apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRole metadata: name: aggregated-role-example aggregationRule: clusterRoleSelectors:
- matchLabels: rbac.example.com/aggregate-to-custom: "true"
The vulnerability manifests when an attacker creates multiple RoleBinding objects simultaneously across different namespaces, referencing the same aggregated ClusterRole. Due to improper locking mechanisms in the authorization cache, the system fails to maintain consistency during concurrent updates, leading to temporary permission elevation.
Technical analysis reveals that the issue lies in the pkg/registry/rbac/rest/storage.go component, specifically in the syncClusterRole function. This function is responsible for synchronizing aggregated roles but contains a race condition that can be triggered under specific conditions:
go // Vulnerable code pattern (simplified) func (r *REST) syncClusterRole(clusterRole *rbacv1.ClusterRole) error { // Race condition occurs here due to lack of proper locking aggregatedRules := r.aggregateRules(clusterRole)
// Cache update happens without atomic operation r.cache.Set(clusterRole.Name, aggregatedRules) return nil
}
The attack vector becomes exploitable when an attacker leverages this race condition to create a window where their user account temporarily gains elevated permissions. This can be achieved by rapidly creating and deleting RoleBinding objects while simultaneously making API requests that require higher privileges.
Impact analysis shows that successful exploitation can grant attackers permissions equivalent to the aggregated ClusterRole being targeted, which often includes cluster-admin level access. This makes CVE-2026-41287 a critical vulnerability requiring immediate attention from security teams managing Kubernetes environments.
Key Insight: The vulnerability's core lies in Kubernetes' authorization caching mechanism, where concurrent operations can lead to inconsistent permission evaluations, creating temporary privilege escalation opportunities.
What Are the Technical Requirements for Exploiting This Vulnerability?
Successful exploitation of CVE-2026-41287 requires several technical prerequisites that attackers must satisfy. Understanding these requirements is crucial for both defenders seeking to prevent exploitation and red teams conducting authorized security assessments.
First and foremost, attackers need valid authentication credentials for the target Kubernetes cluster. While this might seem like a significant barrier, many organizations inadvertently expose service account tokens or misconfigure authentication systems, making credential acquisition more feasible than expected. The credentials don't necessarily need to be highly privileged initially – the vulnerability's purpose is precisely to escalate from lower-privileged accounts to higher ones.
The second requirement involves network access to the Kubernetes API server endpoint. This typically means either direct internet exposure or access through compromised infrastructure within the organization's network perimeter. Modern cloud-native architectures often expose API servers publicly, increasing the attack surface significantly.
Attackers also need knowledge of existing aggregated ClusterRole names within the target cluster. This information can be gathered through reconnaissance activities such as querying the /apis/rbac.authorization.k8s.io/v1/clusterroles endpoint or analyzing publicly available documentation. Organizations that follow naming conventions make this step considerably easier for potential attackers.
bash
Reconnaissance command to identify aggregated ClusterRoles
kubectl get clusterroles --selector=rbac.authorization.k8s.io/aggregate-to-admin
Alternative using direct API calls
curl -k -H "Authorization: Bearer $TOKEN"
https://kubernetes-api-server/apis/rbac.authorization.k8s.io/v1/clusterroles?labelSelector=aggregate-to-view
Additionally, successful exploitation requires precise timing and coordination between multiple API requests. The race condition window is narrow, typically lasting only milliseconds, necessitating automated tooling to reliably trigger the vulnerability. Manual exploitation would be extremely difficult and unreliable.
The following table compares exploitation requirements across different Kubernetes deployment models:
| Deployment Model | Authentication Complexity | Network Accessibility | Detection Difficulty |
|---|---|---|---|
| Public Cloud (EKS/AKS/GKE) | Medium (IAM integration) | High (public endpoints) | Medium (cloud logging) |
| On-Premises Bare Metal | High (custom auth) | Low (internal networks) | High (limited monitoring) |
| Private Cloud/OpenShift | Medium (OAuth/OIDC) | Medium (VPN/VPC) | Medium (enhanced logging) |
| Managed Service Provider | Variable | Variable | Low (MSP monitoring) |
Understanding these requirements helps security teams prioritize their defensive efforts. Organizations with public API endpoints and weak authentication controls are at the highest risk and should implement immediate mitigations regardless of their patch status.
Actionable Takeaway: Implement strict network segmentation around Kubernetes API servers and enforce strong authentication policies to raise the bar for potential attackers targeting this vulnerability.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
What Is the Real Impact Assessment of CVE-2026-41287?
The impact of CVE-2026-41287 extends far beyond simple privilege escalation within Kubernetes clusters. Successful exploitation can lead to complete cluster compromise, data exfiltration, persistent backdoor installation, and lateral movement throughout connected infrastructure. Understanding the full scope of potential consequences is essential for organizations to properly assess their risk exposure and implement appropriate countermeasures.
At the most basic level, attackers who successfully exploit this vulnerability gain unauthorized access to cluster resources that should be protected by RBAC policies. This includes the ability to read, modify, or delete any object within the cluster, depending on the permissions associated with the targeted aggregated ClusterRole. In many cases, this translates to cluster-admin level access, providing attackers with nearly unlimited control over the entire orchestration environment.
The confidentiality impact is severe, as attackers can access sensitive data stored within cluster secrets, configmaps, and persistent volumes. This includes application credentials, TLS certificates, database connection strings, and other confidential information that could facilitate further attacks against backend services and databases.
bash
Example of sensitive data exposure post-exploitation
kubectl get secrets -A -o jsonpath='{range .items[]}{.metadata.name} {.data}{"\n"}{end}'
Extracting specific secret values
kubectl get secret database-credentials -n production -o jsonpath='{.data.password}' | base64 -d
Integrity violations represent another significant concern, as attackers can modify deployment configurations, inject malicious containers, or alter network policies to redirect traffic. These changes can remain undetected for extended periods, especially in environments with inadequate change management processes or insufficient monitoring capabilities.
Availability impacts can manifest through various attack vectors, including resource exhaustion attacks, denial-of-service conditions, or deliberate destruction of critical workloads. Attackers might delete essential services, corrupt storage volumes, or consume excessive compute resources to disrupt business operations.
The following table illustrates the cascading effects of CVE-2026-41287 exploitation across different organizational assets:
| Asset Category | Direct Impact | Secondary Effects | Business Consequences |
|---|---|---|---|
| Container Workloads | Unauthorized access/modification | Data breaches, service disruption | Revenue loss, compliance violations |
| Infrastructure Components | Configuration manipulation | Lateral movement, persistence | Extended remediation time |
| Connected Services | Credential theft, API abuse | Backend system compromise | Supply chain attacks |
| Monitoring Systems | Log tampering, alert suppression | Stealthy operations | Prolonged incident response |
Beyond immediate technical impacts, successful exploitation can trigger regulatory compliance violations, particularly in industries governed by GDPR, HIPAA, or PCI-DSS standards. The breach notification requirements and potential fines associated with these regulations can result in substantial financial penalties and reputational damage.
Organizations should also consider the operational impact of responding to and recovering from such incidents. Incident response teams may need to rebuild entire clusters from scratch, restore data from backups, and conduct extensive forensic investigations to ensure complete remediation.
Critical Insight: The true impact of CVE-2026-41287 extends beyond the cluster itself, potentially compromising connected infrastructure and triggering cascading security failures throughout the organization's technology ecosystem.
How Can Organizations Detect CVE-2026-41287 Exploitation Attempts?
Detecting exploitation attempts of CVE-2026-41287 requires sophisticated monitoring approaches that go beyond traditional security controls. The vulnerability's stealthy nature and the fact that it leverages legitimate API endpoints make detection particularly challenging without specialized techniques and tools.
The most effective detection strategy involves analyzing Kubernetes audit logs for unusual patterns of RoleBinding and ClusterRoleBinding creation/deletion activities. Since exploitation requires rapid, coordinated operations on these objects, monitoring for bursts of RBAC-related API calls can reveal suspicious behavior. Security teams should look for sequences of CREATE, DELETE, and LIST operations on rbac.authorization.k8s.io resources occurring within short time intervals.
bash
Sample audit log query to detect suspicious RBAC activity
Using jq to parse audit logs and identify patterns
jq '. | select(.verb == "create" and (.objectRef.resource == "rolebindings" or .objectRef.resource == "clusterrolebindings")) |
{timestamp: .requestReceivedTimestamp, user: .user.username, resource: .objectRef.resource}'
audit-log.json | sort -k1
Identifying rapid sequence of operations
awk '/(rolebinding|clusterrolebinding)/ && /CREATE|DELETE/' audit-log.txt |
awk '{print $1, $NF}' | uniq -c | awk '$1 > 5'
Advanced detection also involves monitoring for anomalous API request patterns that deviate from normal user behavior. Machine learning-based anomaly detection systems can establish baselines for typical RBAC usage and flag outliers that might indicate exploitation attempts. Key indicators include:
- Simultaneous API requests from the same user across multiple namespaces
- Unusual combinations of GET and POST requests targeting RBAC endpoints
- Requests originating from unexpected IP addresses or user agents
- Access patterns that don't align with documented workflows
Network-level detection focuses on identifying traffic patterns consistent with automated exploitation tools. This includes monitoring for HTTP request rates that exceed normal operational thresholds and analyzing payload characteristics that suggest scripted attacks rather than manual interactions.
Security Information and Event Management (SIEM) systems play a crucial role in aggregating and correlating signals from multiple sources. Organizations should configure alerts that trigger when specific combinations of events occur, such as:
- Multiple failed authentication attempts followed by successful RBAC modification
- Rapid succession of CREATE/DELETE operations on RBAC objects
- Access to sensitive resources immediately after RBAC changes
- Unusual geographic locations accessing RBAC endpoints
yaml
Example SIEM correlation rule for detecting CVE-2026-41287 exploitation
name: "Potential CVE-2026-41287 Exploitation" type: correlation conditions:
- event.category: "kubernetes.api"
event.action: "create"
kubernetes.object.type: ["RoleBinding", "ClusterRoleBinding"]
timeframe: 30s
threshold: 5
- event.category: "kubernetes.api" event.action: "delete" kubernetes.object.type: ["RoleBinding", "ClusterRoleBinding"] timeframe: 30s threshold: 5 actions:
- alert: "High"
- notify: security-team
- block: source-ip
Endpoint detection and response (EDR) solutions can also contribute to detection efforts by monitoring for suspicious processes or file modifications that might indicate successful exploitation. However, since CVE-2026-41287 operates entirely through the Kubernetes API, EDR coverage is limited compared to network and log-based detection methods.
Continuous monitoring and regular review of detection rules are essential as attackers evolve their techniques. Security teams should regularly test their detection capabilities using controlled exploitation scenarios and adjust their monitoring configurations based on lessons learned.
Detection Best Practice: Implement multi-layered monitoring combining audit log analysis, behavioral analytics, and network traffic inspection to maximize detection probability while minimizing false positives.
What Are the Most Effective Mitigation Strategies Beyond Patching?
While applying official patches remains the primary defense against CVE-2026-41287, organizations often face challenges that prevent immediate remediation. Legacy systems, complex deployment pipelines, and dependency conflicts can delay patch deployment for weeks or months. Fortunately, several effective mitigation strategies can significantly reduce exploitation risk without requiring immediate version upgrades.
Network-level restrictions represent one of the most impactful mitigation approaches. Organizations should implement strict ingress controls on Kubernetes API server endpoints, limiting access to trusted IP ranges and implementing rate limiting to prevent bursty exploitation attempts. This can be accomplished through cloud provider firewalls, network security groups, or dedicated API gateway solutions.
bash
Example iptables rules to limit API server access
iptables -A INPUT -p tcp --dport 6443 -s 10.0.0.0/8 -j ACCEPT iptables -A INPUT -p tcp --dport 6443 -m limit --limit 10/min -j LOG --log-prefix "API_RATE_LIMIT: " iptables -A INPUT -p tcp --dport 6443 -j DROP
Kubernetes NetworkPolicy example to restrict namespace access
apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: api-server-restriction spec: podSelector: matchLabels: component: kube-apiserver policyTypes:
- Ingress
ingress:
- from:
- ipBlock: cidr: 172.16.0.0/12 ports:
- protocol: TCP port: 6443
- from:
RBAC hardening provides another layer of protection by implementing the principle of least privilege more rigorously. Organizations should audit existing RoleBinding and ClusterRoleBinding configurations to identify and remove unnecessary cross-namespace permissions. Where aggregated ClusterRoles are used, consider breaking them into smaller, more focused roles that limit the potential impact of exploitation.
Authentication strengthening measures include implementing multi-factor authentication for administrative accounts, rotating service account tokens regularly, and enforcing certificate-based authentication where possible. These measures increase the difficulty for attackers to obtain initial access credentials required for exploitation.
Monitoring and alerting enhancements should focus on detecting the specific patterns associated with CVE-2026-41287 exploitation. This includes configuring real-time alerts for rapid RBAC object modifications, implementing canary accounts that trigger alerts when accessed, and establishing baseline behavioral profiles for normal RBAC usage.
Application-level defenses involve modifying workload configurations to reduce the value of successful exploitation. This includes encrypting sensitive data at rest, implementing zero-trust networking principles, and ensuring that applications don't store excessive privileges within cluster secrets.
yaml
Example PodSecurityPolicy to restrict privilege escalation
apiVersion: policy/v1beta1 kind: PodSecurityPolicy metadata: name: restricted-psp spec: privileged: false allowPrivilegeEscalation: false requiredDropCapabilities:
- ALL
volumes:
- 'configMap'
- 'emptyDir'
- 'projected'
- 'secret'
- 'downwardAPI'
- 'persistentVolumeClaim'
hostNetwork: false
hostIPC: false
hostPID: false
runAsUser:
rule: 'MustRunAsNonRoot'
seLinux:
rule: 'RunAsAny'
supplementalGroups:
rule: 'MustRunAs'
ranges:
- min: 1 max: 65535 fsGroup: rule: 'MustRunAs' ranges:
- min: 1 max: 65535 readOnlyRootFilesystem: true
Regular security assessments using tools like mr7 Agent can help identify configuration weaknesses and validate the effectiveness of implemented mitigations. Automated scanning can detect vulnerable patterns before they can be exploited and provide continuous assurance that security controls remain effective.
Mitigation Priority: Focus on network access controls and RBAC hardening as immediate priorities, followed by enhanced monitoring and authentication improvements for comprehensive protection.
How Should Security Teams Prioritize Their Response Efforts?
Effective response to CVE-2026-41287 requires strategic prioritization based on risk assessment, resource availability, and business impact considerations. Not all Kubernetes clusters present equal risk, and security teams must allocate their limited resources to protect the most critical assets first while maintaining adequate coverage across their entire infrastructure estate.
Risk-based prioritization begins with asset inventory and classification exercises. Clusters hosting production workloads, handling sensitive data, or providing external services should receive top priority for immediate remediation. Development and testing environments, while still important, can be addressed later unless they contain sensitive information or serve as stepping stones to higher-value targets.
Vulnerability assessment frameworks should incorporate factors such as:
- Exposure level (public vs. internal access)
- Authentication strength (anonymous access vs. MFA-required)
- Data sensitivity (PII, financial records, intellectual property)
- Business criticality (revenue-generating vs. support functions)
- Compliance requirements (regulatory mandates, industry standards)
Clusters with public API endpoints and weak authentication controls represent the highest risk category and should be patched or mitigated within 24-48 hours of vulnerability disclosure. Internal clusters with strong access controls and limited data exposure can be addressed within standard patch cycles, typically 30-60 days.
Resource allocation planning must balance immediate security needs with operational constraints. Patching Kubernetes clusters often requires careful coordination with application teams, thorough testing procedures, and rollback plans to prevent service disruptions. Security teams should work closely with DevOps and SRE teams to develop efficient patching workflows that minimize downtime while maximizing security benefits.
Communication strategies should clearly articulate the urgency and business impact of CVE-2026-41287 to executive stakeholders. This includes quantifying potential financial losses, regulatory penalties, and reputation damage that could result from successful exploitation. Clear risk communication helps justify resource allocation decisions and ensures adequate support for remediation efforts.
Incident response preparedness plays a crucial role in prioritization decisions. Organizations should ensure that their incident response playbooks include specific procedures for Kubernetes-related vulnerabilities and that response team members have the necessary skills and tools to investigate and remediate such incidents effectively.
bash
Risk assessment scoring script for Kubernetes clusters
#!/bin/bash
assess_cluster_risk() { local cluster_name=$1 local score=0
Check for public endpoint exposure
if kubectl config view -o jsonpath='{.clusters[?(@.name=="'$cluster_name'")].cluster.server}' | grep -q "https://"; then score=$((score + 30))fi# Check for anonymous authenticationif kubectl get configmap -n kube-system kube-apiserver -o yaml | grep -q "--anonymous-auth=true"; then score=$((score + 25))fi# Check for aggregated rolesif kubectl get clusterroles --selector=rbac\.authorization\.k8s\.io\/aggregate-to-admin | grep -q "aggregate-to-admin"; then score=$((score + 20))fiecho "Risk Score for $cluster_name: $score"}
Usage
for cluster in $(kubectl config get-contexts -o name); do assess_cluster_risk "$cluster" done
Continuous improvement processes should capture lessons learned from the CVE-2026-41287 response effort to enhance future vulnerability management practices. This includes updating risk assessment methodologies, improving communication protocols, and refining patch management procedures based on actual experience.
Strategic Priority: Focus immediate efforts on externally exposed clusters with weak authentication, while developing systematic approaches for comprehensive vulnerability management across all Kubernetes environments.
What Advanced Techniques Can Security Researchers Use for Testing?
Security researchers and penetration testers require sophisticated methodologies to thoroughly assess Kubernetes environments for CVE-2026-41287 vulnerabilities. These techniques go beyond basic scanning tools and involve custom exploitation frameworks, behavioral analysis, and advanced monitoring approaches that simulate real-world attack scenarios.
Controlled exploitation testing involves creating safe, isolated environments that mirror production configurations while eliminating risks to actual systems. Researchers should establish dedicated test clusters with identical Kubernetes versions, RBAC configurations, and network policies to accurately evaluate vulnerability presence and exploitation feasibility.
Custom exploitation scripts can be developed to systematically test the race condition conditions described in CVE-2026-41287. These scripts should coordinate multiple concurrent API requests to trigger the timing window where authorization inconsistencies occur. Python-based frameworks using the Kubernetes client library prove particularly effective for this type of testing.
python #!/usr/bin/env python3
CVE-2026-41287 exploitation testing framework
import threading import time import random from kubernetes import client, config from kubernetes.client.rest import ApiException
config.load_kube_config() v1 = client.RbacAuthorizationV1Api() core_v1 = client.CoreV1Api()
def create_role_binding(namespace, name): """Create a RoleBinding in specified namespace""" role_binding = client.V1RoleBinding( metadata=client.V1ObjectMeta(name=name, namespace=namespace), subjects=[client.V1Subject(kind="User", name="test-user")], role_ref=client.V1RoleRef(kind="ClusterRole", name="view", api_group="rbac.authorization.k8s.io") ) try: v1.create_namespaced_role_binding(namespace, role_binding) print(f"Created RoleBinding {name} in {namespace}") except ApiException as e: print(f"Error creating RoleBinding: {e}")
def delete_role_binding(namespace, name): """Delete a RoleBinding from specified namespace""" try: v1.delete_namespaced_role_binding(name, namespace) print(f"Deleted RoleBinding {name} from {namespace}") except ApiException as e: print(f"Error deleting RoleBinding: {e}")
def test_race_condition(): """Test for race condition by creating/deleting bindings concurrently""" threads = [] namespaces = [f"test-{i}" for i in range(10)]
Create test namespaces
for ns in namespaces: try: core_v1.create_namespace(client.V1Namespace(metadata=client.V1ObjectMeta(name=ns))) except ApiException: pass # Namespace may already exist# Launch concurrent operationsfor i in range(50): ns = random.choice(namespaces) t1 = threading.Thread(target=create_role_binding, args=(ns, f"rb-{i}")) t2 = threading.Thread(target=delete_role_binding, args=(ns, f"rb-{i}")) threads.extend([t1, t2]) for thread in threads: thread.start() time.sleep(0.01) # Small delay to increase race condition likelihood for thread in threads: thread.join()if name == "main": test_race_condition()
Behavioral analysis techniques focus on monitoring system responses to exploitation attempts, looking for telltale signs of vulnerability presence. This includes analyzing API response times, error patterns, and authorization decision inconsistencies that indicate the underlying race condition is active.
Automated security testing platforms like mr7 Agent can streamline this process by providing pre-built exploitation modules and comprehensive reporting capabilities. These tools can execute complex testing scenarios while maintaining detailed logs and evidence of vulnerability presence.
Fuzzing approaches involve sending malformed or unexpected input to Kubernetes API endpoints to identify edge cases that might trigger the vulnerability. Advanced fuzzing frameworks can generate thousands of test cases per minute, systematically exploring the input space for conditions that lead to authorization bypass.
Red team exercises should incorporate CVE-2026-41287 exploitation scenarios as part of broader attack simulations. This helps organizations understand how this vulnerability fits into realistic attack chains and validates the effectiveness of their defensive measures.
Post-exploitation analysis focuses on understanding the full scope of access gained through successful exploitation. Researchers should document all accessible resources, identify potential persistence mechanisms, and map out lateral movement possibilities within compromised clusters.
Collaborative research efforts benefit from sharing findings and testing methodologies with the broader security community while respecting responsible disclosure principles. Open-source security tools and frameworks can incorporate CVE-2026-41287 testing capabilities, making them accessible to wider audiences.
Research Recommendation: Combine automated testing tools with manual validation techniques to ensure comprehensive vulnerability assessment while maintaining safety and accuracy in testing environments.
Key Takeaways
• CVE-2026-41287 exploits a race condition in Kubernetes RBAC aggregation, allowing authenticated users to bypass authorization controls and escalate privileges • Successful exploitation requires valid credentials, network access to API server, and knowledge of aggregated ClusterRole configurations • Impact includes complete cluster compromise, data exfiltration, and potential lateral movement to connected infrastructure systems • Detection requires advanced log analysis focusing on rapid RBAC object modifications and anomalous API request patterns • Immediate mitigation strategies include network access controls, RBAC hardening, and enhanced authentication requirements • Organizations should prioritize response efforts based on risk assessment factors including exposure level and business criticality • Security researchers can leverage automated tools like mr7 Agent combined with custom exploitation frameworks for comprehensive vulnerability testing
Frequently Asked Questions
Q: How quickly should organizations patch CVE-2026-41287?
Organizations should prioritize patching within 72 hours for externally exposed clusters and within 30 days for internal systems. The critical nature of this vulnerability and active exploitation reports make rapid remediation essential. Delay patching only if immediate deployment would cause unacceptable service disruption, and implement compensating controls during the interim period.
Q: Can this vulnerability be exploited without authentication?
No, CVE-2026-41287 requires valid authentication credentials to access the Kubernetes API server. However, attackers can combine this vulnerability with other weaknesses such as exposed service account tokens or misconfigured authentication systems to achieve initial access before exploiting the RBAC bypass.
Q: Which Kubernetes versions are affected by this vulnerability?
CVE-2026-41287 affects Kubernetes clusters running versions v1.29.x through v1.31.x. Organizations running older versions (v1.28 and below) are not directly impacted by this specific vulnerability but should still maintain regular patch schedules for other security issues.
Q: What monitoring tools are best for detecting CVE-2026-41287 exploitation?
The most effective approach combines Kubernetes audit logging with SIEM correlation rules and behavioral analytics platforms. Tools like Falco, Sysdig Secure, and commercial SIEM solutions with Kubernetes integration provide the granular visibility needed to detect exploitation patterns associated with this vulnerability.
Q: How does mr7 Agent help with CVE-2026-41287 security testing?
mr7 Agent automates vulnerability detection by executing pre-built exploitation modules that test for CVE-2026-41287 conditions. It provides detailed reporting, integrates with existing security workflows, and supports both offensive security testing and defensive validation scenarios. New users can try these capabilities with 10,000 free tokens at mr7.ai.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.
Try All Tools Free → | Get mr7 Agent →


