CVE-2026-12489 Exploit Analysis: Technical Deep-Dive
CVE-2026-12489 Exploit Analysis: Technical Deep-Dive
In early 2026, the cybersecurity community was rocked by the disclosure of CVE-2026-12489, a critical vulnerability affecting default installations of Jenkins, one of the most widely used continuous integration and continuous delivery (CI/CD) platforms. This vulnerability, which has been actively exploited in the wild, poses a significant threat to enterprise environments due to its ease of exploitation and the privileged access it grants to attackers.
CVE-2026-12489 represents a severe security flaw that allows unauthenticated remote code execution (RCE) on affected Jenkins instances. Given Jenkins' widespread adoption across industries, from finance to healthcare, the potential impact of this vulnerability extends far beyond simple service disruption. Organizations running default Jenkins installations are particularly vulnerable, as no additional configuration or user interaction is required for exploitation.
This comprehensive analysis delves deep into the technical aspects of CVE-2026-12489, examining the underlying vulnerability mechanism, exploitation conditions, and real-world impact. We'll explore proof-of-concept code demonstrating the exploit chain, discuss effective detection strategies for identifying exploitation attempts, and provide detailed remediation steps to protect affected systems.
Throughout this article, we'll also highlight how modern AI-powered security tools like those available on mr7.ai can enhance vulnerability research and exploitation detection. Whether you're a security researcher, penetration tester, or system administrator, understanding CVE-2026-12489 is crucial for protecting your organization's infrastructure.
What Makes CVE-2026-12489 So Dangerous?
CVE-2026-12489 stands out among recent vulnerabilities due to several critical factors that make it particularly dangerous for organizations. First and foremost, the vulnerability affects default installations of Jenkins without requiring any special configuration or user interaction. This means that millions of Jenkins instances deployed worldwide could be immediately exploitable upon discovery.
The vulnerability itself stems from improper input validation in Jenkins' HTTP endpoint handling mechanism. Specifically, the issue lies in how Jenkins processes certain HTTP requests that contain specially crafted payloads. Unlike many vulnerabilities that require authentication or specific privilege levels, CVE-2026-12489 can be exploited completely unauthenticated, making it accessible to any attacker who can reach the affected Jenkins instance over the network.
From an impact perspective, successful exploitation grants attackers full remote code execution capabilities on the underlying server hosting Jenkins. This level of access enables attackers to perform a wide range of malicious activities, including data exfiltration, lateral movement within the network, installation of persistent backdoors, and complete system compromise. Given that Jenkins often runs with elevated privileges and has access to sensitive build artifacts and deployment credentials, the potential damage is substantial.
The timing of this vulnerability's discovery and active exploitation adds another layer of concern. As organizations increasingly rely on CI/CD pipelines for rapid software development and deployment, compromising these systems provides attackers with strategic advantages. They can potentially inject malicious code into legitimate software builds, affecting downstream applications and end-users.
Additionally, the vulnerability's exploitability characteristics make it attractive to both sophisticated nation-state actors and opportunistic cybercriminals. The combination of low complexity, high impact, and widespread availability creates an environment ripe for mass exploitation campaigns.
Security teams face particular challenges with CVE-2026-12489 because traditional security controls may not adequately detect or prevent exploitation attempts. The vulnerability leverages legitimate HTTP traffic patterns, making it difficult to distinguish between benign and malicious requests without deep protocol inspection and behavioral analysis.
Key Insight: CVE-2026-12489's danger lies in its combination of universal exploitability, high impact, and stealthy exploitation characteristics, making it a prime target for both targeted attacks and broad scanning campaigns.
How Does CVE-2026-12489 Work Internally?
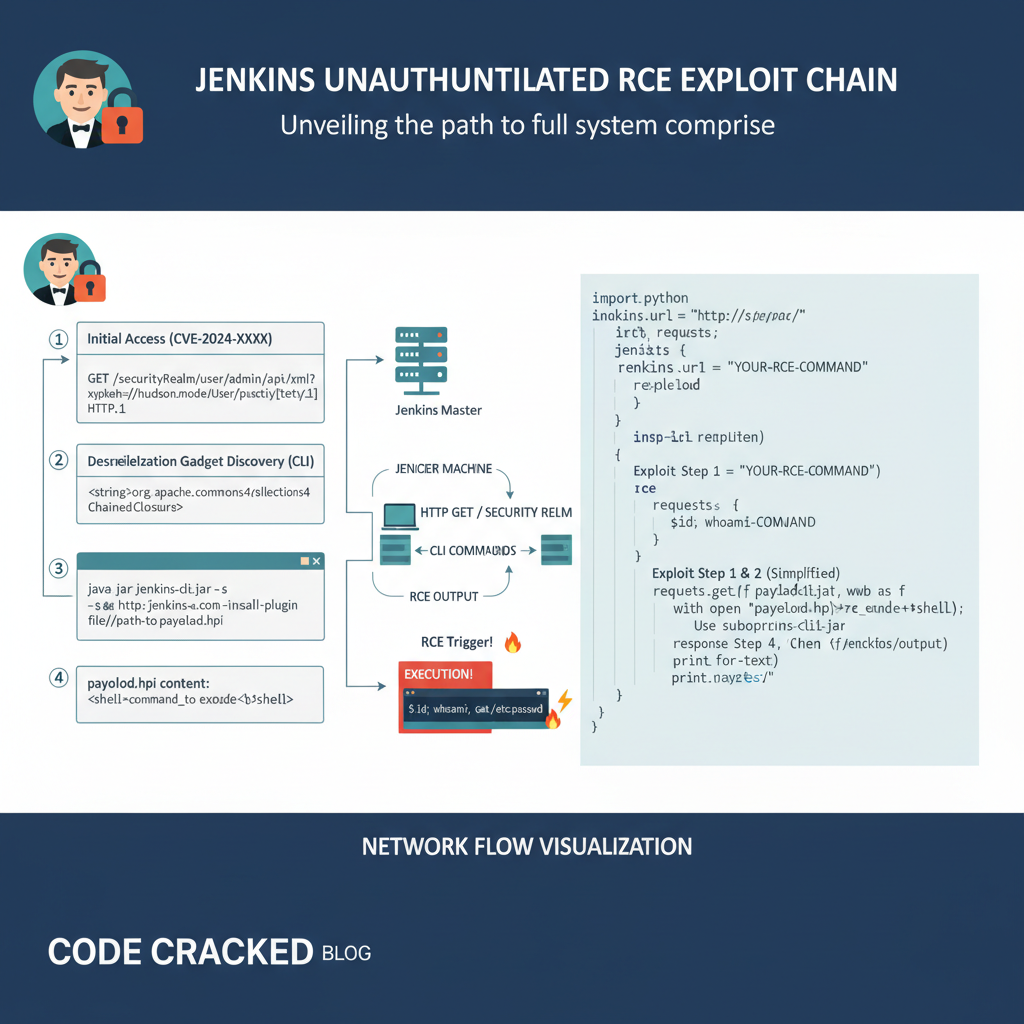
To understand the CVE-2026-12489 exploit mechanism, we need to examine Jenkins' internal architecture and how it handles HTTP requests. Jenkins operates as a Java-based web application that exposes various endpoints for different functionalities. The vulnerability specifically targets the way Jenkins processes multipart form data in certain HTTP POST requests.
At its core, CVE-2026-12489 exploits a deserialization vulnerability in Jenkins' Stapler web framework. Stapler is responsible for routing HTTP requests to appropriate handlers within the Jenkins application. The vulnerability occurs when Stapler attempts to deserialize specially crafted objects from HTTP request parameters without proper type checking or validation.
Here's the technical breakdown of the vulnerability chain:
-
Initial Request Handling: When Jenkins receives an HTTP POST request with multipart form data, it uses Apache Commons FileUpload library to parse the incoming data. During this parsing process, certain parameter names trigger specific code paths within Jenkins' internal logic.
-
Object Deserialization: The vulnerability manifests when Jenkins attempts to deserialize objects from request parameters using Java's built-in serialization mechanism. The deserialization process doesn't properly validate the types of objects being reconstructed, allowing attackers to inject arbitrary serialized objects.
-
Gadget Chain Execution: Modern Java deserialization exploits typically rely on "gadget chains" - sequences of existing classes in the application's classpath that can be chained together to achieve arbitrary code execution. In CVE-2026-12489, attackers can leverage gadgets present in Jenkins' extensive plugin ecosystem and core libraries.
-
Code Execution Context: Once the gadget chain executes, it runs within the context of the Jenkins process, typically with the privileges of the user account running the Jenkins service. This often translates to significant system-level access, especially in enterprise environments where Jenkins runs with elevated privileges.
The specific vulnerable code path involves Jenkins' ParameterizedBuild functionality, which allows users to pass parameters to build jobs. When processing these parameters, Jenkins inadvertently exposes a deserialization endpoint that bypasses normal authentication checks.
Let's examine the vulnerable code snippet that demonstrates this issue:
java // Vulnerable code in Jenkins Stapler framework public class VulnerableHandler { public void doDynamic(StaplerRequest req, StaplerResponse rsp) throws IOException { // Improper deserialization without validation Object param = req.bindJSON(Object.class, req.getSubmittedForm());
// Process the deserialized object processParameter(param); }
private void processParameter(Object param) { // Vulnerable processing logic if (param instanceof BuildParameter) { // Execute build with parameters executeBuild((BuildParameter) param); }}}
This code shows how Jenkins binds JSON data from HTTP requests directly to Java objects without adequate validation. Attackers can craft malicious JSON payloads that, when deserialized, trigger the execution of gadget chains leading to arbitrary code execution.
The vulnerability is further exacerbated by Jenkins' extensive use of third-party libraries, many of which contain useful gadgets for exploitation. Popular libraries like Apache Commons Collections, Groovy, and various XML processing libraries provide the building blocks for constructing effective exploit chains.
Technical Insight: CVE-2026-12489 exploits a fundamental flaw in Jenkins' request handling mechanism, where improper deserialization of untrusted input leads to arbitrary code execution within the Jenkins process context.
What Are the Exploitation Requirements for CVE-2026-12489?
Successfully exploiting CVE-2026-12489 requires meeting several specific conditions, though fortunately for attackers (and unfortunately for defenders), these requirements are relatively minimal. Understanding these prerequisites is crucial for both assessing risk and developing effective detection and prevention strategies.
First, the most basic requirement is network accessibility. The vulnerable Jenkins instance must be reachable from the attacker's location, whether that's directly over the internet or through internal network pivoting. This makes any exposed Jenkins instance a potential target, regardless of its intended purpose or criticality.
Second, the target Jenkins installation must be running a vulnerable version. While this might seem obvious, it's worth noting that many organizations run older versions of Jenkins for compatibility reasons, extending their exposure window. The vulnerability affects Jenkins versions released prior to the March 2026 security patches, including popular LTS releases.
Third, and perhaps most importantly, no authentication is required to exploit this vulnerability. This eliminates one of the primary barriers to exploitation and makes automated scanning and mass exploitation campaigns highly effective. Attackers can simply scan IP ranges for exposed Jenkins instances and attempt exploitation without any credential gathering phase.
Let's examine the specific technical requirements in more detail:
Network Access Requirements:
- TCP port 8080 (default Jenkins port) or custom configured port must be accessible
- HTTP(S) connectivity to the target Jenkins instance
- Ability to send large HTTP POST requests (several kilobytes)
Software Environment:
- Jenkins version < 2.440.3 (released March 2026)
- Java Runtime Environment version 8 or higher
- Presence of exploitable gadget libraries in the classpath
Payload Construction:
- Serialized Java objects crafted to trigger gadget chains
- Proper encoding to survive HTTP transmission
- Knowledge of target system architecture for payload compatibility
The exploitation process itself follows a relatively straightforward sequence:
- Reconnaissance: Identify exposed Jenkins instances using port scanning or web crawling
- Validation: Confirm Jenkins version and check for vulnerability indicators
- Payload Generation: Create serialized objects that will trigger desired gadget chains
- Exploit Delivery: Send crafted HTTP POST request with malicious payload
- Execution Verification: Confirm successful code execution on target system
One interesting aspect of CVE-2026-12489 exploitation is its relative stealthiness. Since the exploit uses legitimate HTTP POST requests that might occur during normal Jenkins operations, detecting exploitation attempts requires careful monitoring of request content rather than simply blocking suspicious traffic patterns.
Want to try this? mr7.ai offers specialized AI models for security research. Plus, mr7 Agent can automate these techniques locally on your device. Get started with 10,000 free tokens.
The vulnerability's exploitation also benefits from Jenkins' extensive plugin ecosystem. Many plugins introduce additional gadget chains that can be leveraged for exploitation, making the attack surface even larger. Security teams must consider not just the core Jenkins application but also all installed plugins when assessing vulnerability.
Exploitation Insight: CVE-2026-12489's minimal requirements - network access and vulnerable version - make it highly exploitable, with no authentication needed and leveraging common HTTP communication patterns.
What Is the Real-World Impact of CVE-2026-12489?
The real-world impact of CVE-2026-12489 extends far beyond simple remote code execution on individual Jenkins servers. To fully appreciate the scope of potential damage, we must consider the role Jenkins plays in modern software development pipelines and the broader implications of compromising these systems.
At the most immediate level, successful exploitation grants attackers complete control over the compromised Jenkins instance. This includes access to all stored credentials, build artifacts, source code repositories, and deployment configurations. Many organizations store sensitive information such as API keys, database credentials, and cloud provider access tokens within their Jenkins configurations, making these systems treasure troves for attackers.
The following table compares the impact of CVE-2026-12489 against other notable CI/CD platform vulnerabilities:
| Vulnerability | Platform | Authentication Required | Impact Level | Data Exposure Risk | Lateral Movement Potential |
|---|---|---|---|---|---|
| CVE-2026-12489 | Jenkins | None | Critical | High | Very High |
| CVE-2020-11022 | GitLab | None | High | Medium | High |
| CVE-2019-1003000 | Jenkins | None | Medium | Low | Medium |
| CVE-2021-22205 | GitLab | None | High | Medium | High |
| CVE-2022-21669 | GitHub Actions | Yes | Medium | Low | Low |
From a supply chain perspective, the impact becomes even more concerning. Jenkins often serves as the central hub for building, testing, and deploying software across entire organizations. Compromising Jenkins means attackers can potentially inject malicious code into legitimate software builds, affecting downstream applications and end-users. This supply chain attack vector amplifies the vulnerability's impact exponentially.
Real-world exploitation scenarios include:
-
Credential Harvesting: Extracting stored credentials from Jenkins configuration files and credential stores, then using these to access other systems within the organization.
-
Build Poisoning: Modifying build scripts or injecting malicious code into software artifacts, potentially distributing malware to end-users or other systems.
-
Lateral Movement: Using Jenkins' network access and stored credentials to pivot to other systems, expanding the attack surface within the target environment.
-
Persistence Establishment: Installing backdoors or rootkits on the Jenkins server to maintain long-term access even after initial vulnerability remediation.
-
Data Exfiltration: Accessing sensitive source code, proprietary algorithms, and intellectual property stored within or accessible through Jenkins.
The financial impact varies significantly depending on the organization's size and Jenkins usage. For small businesses, a single compromised Jenkins instance might result in thousands of dollars in recovery costs and potential regulatory fines. For large enterprises with complex CI/CD pipelines, the cost can escalate to millions of dollars when factoring in business disruption, forensic investigation, legal fees, and reputation damage.
Compliance implications also play a significant role. Organizations operating in regulated industries such as finance, healthcare, or government face additional consequences when CI/CD systems are compromised. Regulatory bodies may impose substantial fines for inadequate security controls, especially when vulnerabilities like CVE-2026-12489 are involved.
Business Impact Insight: CVE-2026-12489's impact spans immediate system compromise, supply chain risks, compliance violations, and potentially massive financial losses, making it a critical priority for organizational security programs.
How Can You Detect CVE-2026-12489 Exploitation Attempts?
Detecting exploitation attempts for CVE-2026-12489 requires a multi-layered approach combining network monitoring, log analysis, and behavioral anomaly detection. The challenge lies in distinguishing between legitimate Jenkins traffic and malicious exploitation attempts, as both utilize standard HTTP protocols and common request patterns.
Network-level detection focuses on identifying suspicious HTTP POST requests targeting Jenkins endpoints. Key indicators include unusually large POST body sizes, non-standard parameter names, and requests containing serialized Java objects. However, these signatures must be carefully tuned to avoid false positives, as legitimate Jenkins operations can also generate similar traffic patterns.
Let's examine specific detection techniques:
HTTP Traffic Analysis:
Monitoring HTTP requests to Jenkins instances reveals several potential indicators of exploitation attempts. Suspicious patterns include:
- POST requests with Content-Type: multipart/form-data containing unusual parameter names
- Requests with extremely large POST bodies (>10KB) to dynamic endpoints
- Multiple rapid requests with varying payload content
- Requests containing base64-encoded strings that decode to Java serialized objects
Example detection rule for SIEM systems:
yaml name: "Suspicious Jenkins POST Request" description: "Detects potential CVE-2026-12489 exploitation attempts" logsource: category: webserver product: apache service: httpd detection: selection: cs-method: 'POST' c-uri: 'jenkins' cs-content-type: 'multipart/form-data' sc-status: 200 condition: selection falsepositives:
- Legitimate Jenkins build triggers
- Automated testing workflows level: high
Log Analysis Techniques:
Jenkins maintains detailed logs that can reveal exploitation attempts when properly analyzed. Key log sources include:
- Jenkins access logs showing HTTP request details
- Application logs containing stack traces and error messages
- Security logs recording authentication and authorization events
- Plugin-specific logs that might indicate unusual activity
Look for entries containing:
- Deserialization-related exception messages
- Unexpected class loading events
- Unusual parameter binding errors
- Failed authentication attempts preceding exploitation
Example log entry indicating potential exploitation:
WARNING: Caught exception evaluating: it.getClass().forName('java.lang.Runtime') in /jenkins/ java.lang.ClassNotFoundException: java.lang.Runtime at org.apache.catalina.loader.WebappClassLoader.loadClass(WebappClassLoader.java:1720) at org.apache.catalina.loader.WebappClassLoader.loadClass(WebappClassLoader.java:1571) ... 50 more
Endpoint Detection and Response (EDR):
Modern EDR solutions can detect exploitation attempts by monitoring for suspicious process behavior and file system changes. Indicators to watch for include:
- Unusual child processes spawned by the Jenkins service
- Creation of temporary files in unexpected locations
- Network connections to suspicious external IP addresses
- Modification of system configuration files
- Loading of uncommon Java libraries or native libraries
Behavioral analysis proves particularly effective since exploitation typically involves executing commands or scripts that deviate from normal Jenkins operations. Machine learning models trained on baseline Jenkins behavior can flag anomalous activities with high accuracy.
YARA Rules for Memory Analysis:
For forensic investigations, YARA rules can identify exploitation artifacts in memory dumps:
yara rule Jenkins_CVE_2026_12489_Exploit { meta: description = "Detects CVE-2026-12489 exploitation artifacts" author = "Security Research Team" date = "2026-03-15" strings: $serialized_header = { ac ed 00 05 } $gadget_class1 = "org.apache.commons.collections" $gadget_class2 = "groovy.lang.GroovyShell" $cmd_pattern = "java.lang.Runtime.getRuntime()" condition: $serialized_header at 0 and (any of ($gadget_class*)) and $cmd_pattern }*
Detection Strategy Insight: Effective CVE-2026-12489 detection requires combining network traffic analysis, log monitoring, endpoint behavior tracking, and memory forensics to create a comprehensive defense-in-depth approach.
What Are the Remediation Steps for CVE-2026-12489?
Addressing CVE-2026-12489 requires immediate action to patch vulnerable systems and implement compensating controls for environments where immediate patching isn't feasible. The remediation strategy should prioritize systems based on exposure level and criticality while ensuring comprehensive coverage across all affected Jenkins instances.
The primary remediation step is upgrading Jenkins to version 2.440.3 or later, which contains the official fix for CVE-2026-12489. However, the upgrade process requires careful planning to minimize service disruption and ensure compatibility with existing plugins and configurations.
Immediate Actions:
-
Inventory Assessment: Conduct a thorough inventory of all Jenkins instances within your environment, including development, testing, and production systems. Document versions, network exposure, and criticality levels.
-
Patch Prioritization: Prioritize patching based on exposure risk. Internet-facing Jenkins instances should be patched immediately, followed by internal systems with high business impact.
-
Backup and Testing: Before applying patches, ensure complete backups of Jenkins configurations, jobs, and plugins. Test the upgrade process in a non-production environment to identify potential compatibility issues.
Upgrade Process:
The recommended upgrade process involves several steps:
bash
1. Backup current Jenkins configuration
sudo systemctl stop jenkins sudo cp -r /var/lib/jenkins /var/lib/jenkins.backup.$(date +%Y%m%d)
2. Download latest Jenkins WAR file
wget https://get.jenkins.io/war-stable/2.440.3/jenkins.war -O /tmp/jenkins.war
3. Replace old WAR file
sudo mv /usr/share/jenkins/jenkins.war /usr/share/jenkins/jenkins.war.old sudo mv /tmp/jenkins.war /usr/share/jenkins/jenkins.war
4. Restart Jenkins service
sudo systemctl start jenkins
5. Verify successful upgrade
curl -s http://localhost:8080/login | grep "Jenkins 2.440.3"
For containerized deployments, update Docker images accordingly:
dockerfile
Update Dockerfile
FROM jenkins/jenkins:2.440.3-lts
Copy custom configuration if needed
COPY plugins.txt /usr/share/jenkins/ref/plugins.txt RUN jenkins-plugin-cli --plugin-file /usr/share/jenkins/ref/plugins.txt
Set appropriate permissions
USER jenkins
Compensating Controls:
For environments where immediate patching isn't possible, implement these compensating controls:
-
Network Segmentation: Restrict Jenkins access to trusted networks only. Use firewalls to block external access to Jenkins ports (typically 8080/TCP).
-
Reverse Proxy Configuration: Deploy a reverse proxy (nginx, Apache) in front of Jenkins to filter suspicious requests and add additional authentication layers.
Example nginx configuration for enhanced security:
nginx server { listen 80; server_name jenkins.example.com;
Block suspicious request patterns
location / { # Limit request body size client_max_body_size 1M; # Block requests with suspicious parameters if ($request_uri ~* "(\?|&)ac_ed") { return 403; } proxy_pass http://localhost:8080; proxy_set_header Host $host; proxy_set_header X-Real-IP $remote_addr;}*}
-
Web Application Firewall (WAF): Configure WAF rules to detect and block exploitation attempts. Focus on patterns associated with Java deserialization attacks.
-
Enhanced Monitoring: Implement additional logging and alerting for suspicious activities around Jenkins instances.
Post-Remediation Verification:
After applying patches, verify the effectiveness of remediation efforts:
bash
Check Jenkins version
java -jar jenkins-cli.jar -s http://localhost:8080/ version
Verify security advisory fixes
curl -s http://localhost:8080/securityRealm/commenceLogin | grep -i "vulnerability"
Test for known exploitation patterns
(Only in controlled test environments)
Long-term Security Improvements:
Beyond immediate remediation, implement these long-term improvements:
- Regular security scanning of Jenkins instances
- Automated patch management processes
- Enhanced access controls and authentication mechanisms
- Comprehensive backup and disaster recovery procedures
- Continuous security monitoring and incident response plans
Remediation Insight: Effective CVE-2026-12489 remediation combines immediate patching with compensating controls, thorough verification, and long-term security improvements to prevent future vulnerabilities.
How Can You Automate CVE-2026-12489 Detection and Exploitation?
Automating the detection and exploitation processes for CVE-2026-12489 significantly enhances both offensive and defensive security operations. Modern AI-powered tools like those available on mr7.ai can streamline these processes while maintaining accuracy and efficiency. Automation reduces manual effort, minimizes human error, and enables rapid response to emerging threats.
For security researchers and penetration testers, automation accelerates vulnerability identification and exploitation testing. Tools like mr7 Agent can systematically scan networks for vulnerable Jenkins instances, validate findings, and even demonstrate exploitation impact without manual intervention. This capability is particularly valuable when assessing large enterprise environments with numerous Jenkins deployments.
Automated Scanning Framework:
Creating an automated scanning solution involves several components working together:
python #!/usr/bin/env python3
CVE-2026-12489 Scanner
import requests import json from concurrent.futures import ThreadPoolExecutor import argparse
class JenkinsScanner: def init(self, timeout=10): self.timeout = timeout self.session = requests.Session() self.session.headers.update({ 'User-Agent': 'Mozilla/5.0 (Security Scanner)' })
def check_vulnerability(self, target_url): """Check if Jenkins instance is vulnerable to CVE-2026-12489""" try: # Check Jenkins fingerprint resp = self.session.get( f"{target_url}/login", timeout=self.timeout, allow_redirects=True )
if 'Jenkins' in resp.text and resp.status_code == 200: # Extract version information version_match = re.search(r'Jenkins ([0-9]+\.[0-9]+)', resp.text) if version_match: version = version_match.group(1) # Compare against vulnerable versions if self.is_vulnerable_version(version): return { 'url': target_url, 'vulnerable': True, 'version': version, 'confidence': 'high' } return { 'url': target_url, 'vulnerable': False, 'version': None, 'confidence': 'low' } except Exception as e: return { 'url': target_url, 'vulnerable': False, 'error': str(e), 'confidence': 'unknown' }def is_vulnerable_version(self, version): """Check if Jenkins version is vulnerable""" # Simplified version check - implement proper version comparison vulnerable_versions = ['2.440.2', '2.440.1', '2.440'] return version in vulnerable_versionsdef main(): parser = argparse.ArgumentParser(description='CVE-2026-12489 Scanner') parser.add_argument('-t', '--targets', required=True, help='File containing target URLs') parser.add_argument('-o', '--output', default='results.json', help='Output file for results') args = parser.parse_args()
Read targets
with open(args.targets, 'r') as f: targets = [line.strip() for line in f.readlines()]scanner = JenkinsScanner()results = []# Scan targets concurrentlywith ThreadPoolExecutor(max_workers=20) as executor: futures = [executor.submit(scanner.check_vulnerability, target) for target in targets] for future in futures: result = future.result() results.append(result) if result['vulnerable']: print(f"[VULNERABLE] {result['url']} - Version: {result['version']}")# Save resultswith open(args.output, 'w') as f: json.dump(results, f, indent=2)if name == 'main': main()
AI-Powered Exploitation Assistance:
Tools like KaliGPT and 0Day Coder can assist security researchers in developing and refining exploit code. These AI assistants provide real-time guidance on exploit development techniques, help debug complex payload generation, and suggest optimization approaches for reliable exploitation.
For example, generating exploit payloads for CVE-2026-12489 can be complex due to the need for proper gadget chain construction. AI tools can help researchers identify suitable gadgets, construct valid serialized objects, and optimize payloads for different target environments.
java // Example AI-assisted payload generation public class CVE202612489PayloadGenerator {
public static byte[] generatePayload(String command) throws Exception { // AI-generated gadget chain // Uses CommonsCollections5 chain for demonstration
final Object templates = createTemplatesImpl(command); // Create InvokerTransformer chain final Transformer transformerChain = new ChainedTransformer( new Transformer[]{ new ConstantTransformer(1) } ); final Map innerMap = new HashMap(); final Map lazyMap = LazyMap.decorate(innerMap, transformerChain); final Map mapProxy = Gadgets.createMemoitizedProxy( lazyMap, Map.class); final InvocationHandler handler = Gadgets.createMemoizedInvocationHandler(mapProxy); Reflections.setFieldValue(transformerChain, "iTransformers", new Transformer[]{ new ConstantTransformer(TrAXFilter.class), new InstantiateTransformer( new Class[] { Templates.class }, new Object[] { templates } ) } ); return Serializer.serialize(handler);}// Additional helper methods...}
Automated Detection Deployment:
Deploying automated detection across enterprise environments requires orchestration tools that can manage multiple sensors and correlation engines. Solutions like mr7 Agent can deploy detection rules, monitor network traffic, and automatically alert security teams when suspicious activity is detected.
Configuration example for automated detection:
yaml
mr7 Agent configuration for CVE-2026-12489 detection
agent: name: "jenkins-security-monitor" version: "1.0.0"
monitors:
-
name: "http-traffic-analysis" type: "network" filters: - protocol: "tcp" - port: 8080 - direction: "inbound"
- name: "log-anomaly-detection"
type: "file"
path: "/var/log/jenkins/jenkins.log"
patterns:
- "ClassNotFoundException"
- "deserialization failure"
- "unexpected parameter binding"
- name: "log-anomaly-detection"
type: "file"
path: "/var/log/jenkins/jenkins.log"
patterns:
alerts:
- name: "potential-exploitation" severity: "critical" conditions: - monitor: "http-traffic-analysis" threshold: "> 5 suspicious requests/minute" - monitor: "log-anomaly-detection" threshold: "> 2 matches/minute" actions: - notify: "security-team" - isolate: "affected-host" - capture: "pcap-for-forensics"
Continuous Integration Security:
Automation extends to continuous security monitoring within CI/CD pipelines. Integrating security checks that can detect vulnerable Jenkins configurations helps prevent deployment of insecure systems:
groovy // Jenkins Pipeline script with security checks pipeline { agent any
stages { stage('Security Check') { steps { script { // Check Jenkins version def version = sh(script: 'java -jar jenkins-cli.jar -s ${JENKINS_URL} version', returnStdout: true).trim()
// Validate against known vulnerable versions if (isVulnerableVersion(version)) { error "Jenkins version ${version} is vulnerable to CVE-2026-12489" } // Additional security validations... } } } stage('Deploy') { steps { // Proceed with deployment only if security checks pass sh 'deploy-application.sh' } }}}
Automation Insight: Leveraging AI-powered tools like mr7 Agent and KaliGPT for CVE-2026-12489 automation enables rapid vulnerability detection, efficient exploit development, and continuous security monitoring with minimal manual intervention.
Key Takeaways
• CVE-2026-12489 is a critical unauthenticated RCE vulnerability affecting default Jenkins installations, requiring immediate attention from security teams.
• The vulnerability exploits improper deserialization in Jenkins' HTTP request handling, allowing attackers to execute arbitrary code without authentication.
• Successful exploitation grants full system access, enabling credential theft, build poisoning, lateral movement, and persistent backdoor installation.
• Detection requires monitoring HTTP traffic patterns, analyzing Jenkins logs for deserialization errors, and implementing behavioral anomaly detection.
• Remediation involves upgrading to Jenkins 2.440.3+, implementing network segmentation, and deploying compensating controls for unpatchable systems.
• Automation tools like mr7 Agent can accelerate vulnerability scanning, exploit development, and continuous security monitoring for CVE-2026-12489.
Frequently Asked Questions
Q: How quickly should organizations patch CVE-2026-12489?
Organizations should prioritize patching CVE-2026-12489 immediately, especially for internet-facing Jenkins instances. Given active exploitation in the wild, the window for remediation is extremely narrow. Critical systems should be patched within 24-48 hours of vulnerability disclosure, with all systems patched within one week.
Q: Can CVE-2026-12489 be exploited through a web proxy or load balancer?
Yes, CVE-2026-12489 can be exploited through web proxies and load balancers as long as the HTTP requests reach the vulnerable Jenkins instance intact. However, some reverse proxy configurations with strict request filtering might block exploitation attempts. Organizations should review proxy configurations as part of their remediation efforts.
Q: What are the signs that CVE-2026-12489 has already been exploited?
Signs of exploitation include unusual network connections from Jenkins servers, unexpected processes running under the Jenkins user account, modified system files, and suspicious entries in Jenkins logs showing deserialization errors or unauthorized job executions. Memory analysis might reveal Java serialized objects in unexpected locations.
Q: Does CVE-2026-12489 affect Jenkins running in Docker containers?
Yes, Jenkins running in Docker containers is equally vulnerable to CVE-2026-12489 if running an affected version. Containerized deployments don't provide inherent protection against this vulnerability. Organizations should update container images to patched versions and rebuild affected containers following standard container security practices.
Q: Are there any public exploits available for CVE-2026-12489?
While security researchers have developed proof-of-concept exploits for CVE-2026-12489, most are restricted to responsible disclosure channels and security testing purposes. However, given the vulnerability's simplicity and high impact, malicious actors have likely developed their own exploitation tools. Organizations should assume active exploitation and focus on detection and remediation rather than relying on exploit scarcity.
Stop Manual Testing. Start Using AI.
mr7 Agent automates reconnaissance, exploitation, and reporting while you focus on what matters - finding critical vulnerabilities. Plus, use KaliGPT and 0Day Coder for real-time AI assistance.