Cloud Shadow Admin Detection: Advanced Behavioral Analysis
Cloud Shadow Admin Detection: Advanced Behavioral Analysis Techniques
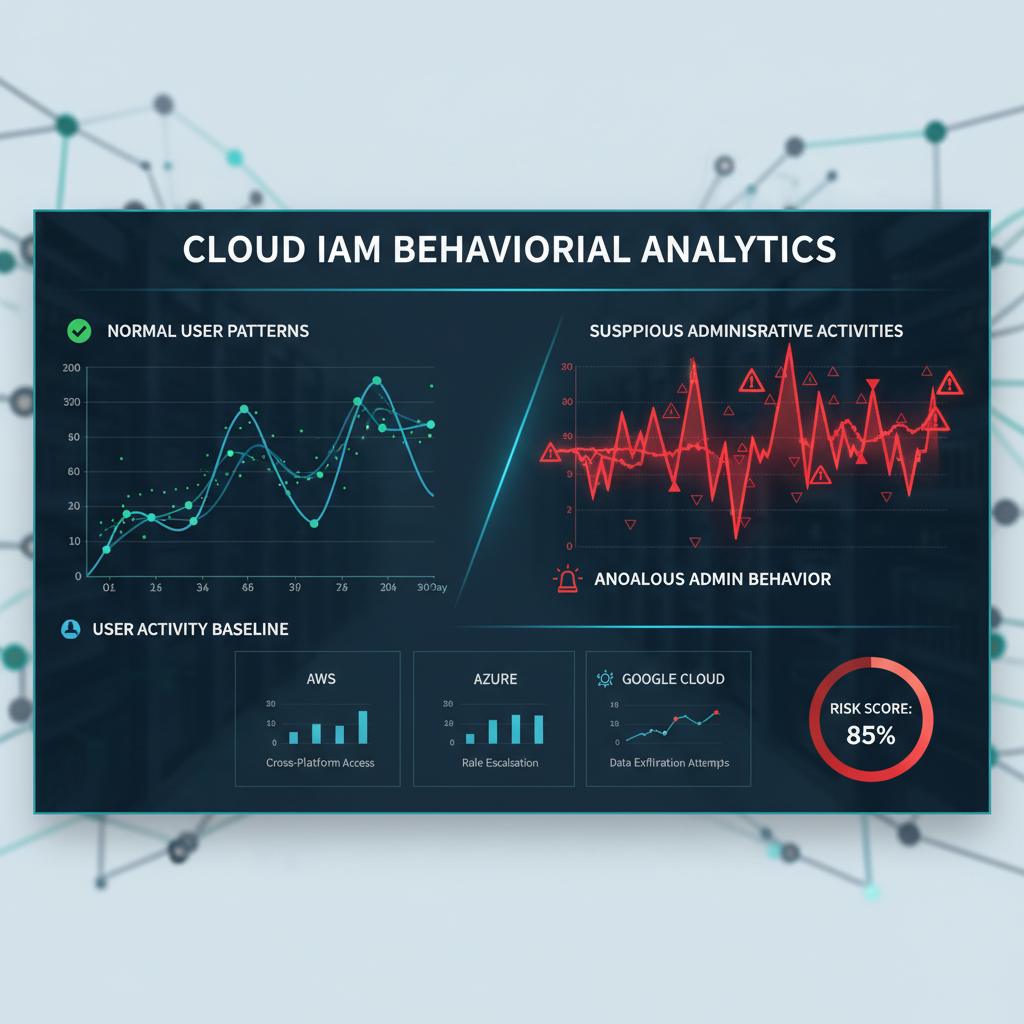
In today's complex cloud landscape, traditional IAM scanning methods fall short when identifying shadow administrators—accounts that gain unauthorized administrative privileges through misconfigurations, privilege escalation paths, or temporary role assignments. These stealthy actors pose significant security risks because they operate under the radar of conventional permission-based detection systems. Modern penetration testers and security teams have increasingly turned to behavioral analytics to uncover these hidden threats, leveraging detailed activity logs and machine learning techniques to spot anomalies that indicate unauthorized administrative access.
This comprehensive guide delves into advanced behavioral analysis techniques for detecting shadow administrators across AWS, Azure, and Google Cloud Platform (GCP). We'll explore how to establish baseline behavioral profiles, detect anomalous administrative actions, correlate cross-account activities, identify service account misuse, and implement continuous monitoring using native cloud logging services. Through practical examples, specific Sigma rules, and real-world detection logic, you'll learn to build robust detection capabilities that go beyond simple permission checks. Whether you're conducting penetration tests, red team exercises, or strengthening your organization's defensive posture, mastering these behavioral analysis techniques is essential for modern cloud security practitioners in 2026.
How Can Behavioral Analytics Reveal Hidden Cloud Administrators?
Traditional cloud security approaches primarily rely on static permission assessments to identify administrative accounts. While this method works for obvious cases, it completely misses shadow administrators who gain privileges through dynamic means such as temporary role assumption, misconfigured resource policies, or exploitation of overly permissive trust relationships. Behavioral analytics addresses these blind spots by analyzing actual user and service account activities over time, creating detailed profiles of normal behavior patterns and flagging deviations that suggest unauthorized administrative access.
The foundation of behavioral analysis lies in understanding that legitimate administrative activities follow predictable patterns. For instance, infrastructure provisioning typically occurs during business hours, involves specific API calls in logical sequences, and originates from known IP ranges or geographic locations. Shadow administrators, however, often exhibit behaviors that deviate from these established norms—accessing resources outside normal working hours, executing unusual combinations of administrative APIs, or operating from unexpected network locations.
Consider an example scenario in AWS where a developer account temporarily assumes an EC2 administration role to troubleshoot production issues. If this account begins performing unrelated administrative tasks such as modifying IAM policies or accessing S3 buckets across different departments without proper authorization, behavioral analytics would flag these activities as suspicious. Similarly, in Azure environments, a service principal designed for backup operations suddenly accessing Key Vault secrets or creating new administrative users would trigger alerts based on deviation from its established behavioral baseline.
Implementing effective behavioral analysis requires collecting comprehensive activity logs from all cloud platforms. AWS CloudTrail provides detailed records of API calls and user activities, while Azure Activity Logs capture management plane operations and resource changes. Google Cloud's audit logs offer similar visibility into administrative actions across various services. By centralizing these logs and applying advanced analytical techniques, security teams can create sophisticated detection mechanisms that identify shadow administrators with high accuracy.
To illustrate the power of behavioral analytics, let's examine a practical detection scenario. An organization notices unusual IAM policy modifications occurring at odd hours from an account that typically only manages application deployments. Upon investigation, they discover this account had been granted temporary elevated privileges for a specific task but continued using those permissions beyond their intended scope. Traditional permission scans wouldn't have caught this since the account legitimately possessed the required permissions at some point. However, behavioral analysis revealed the temporal and contextual anomalies that indicated ongoing unauthorized administrative access.
Building on this foundation, organizations can develop multi-layered detection strategies that combine statistical anomaly detection with rule-based alerting. Statistical methods help identify subtle behavioral shifts that might escape manual review, while rule-based approaches catch clear violations of established security policies. Together, these techniques create a robust framework for detecting shadow administrators that operates independently of static permission assessments.
Key Insight: Behavioral analytics transforms cloud security by shifting focus from what permissions accounts possess to how they actually behave, enabling detection of shadow administrators that evade traditional scanning methods.
What Are the Core Principles of Baseline Behavior Profiling?
Establishing accurate baseline behavior profiles forms the cornerstone of effective shadow administrator detection. Without understanding normal operational patterns, distinguishing between legitimate administrative activities and unauthorized access becomes nearly impossible. Successful profiling requires collecting extensive historical data, defining relevant behavioral metrics, and implementing adaptive models that evolve with changing organizational practices.
The first step in baseline creation involves identifying key behavioral dimensions that distinguish administrative activities from regular user operations. These dimensions typically include temporal patterns (when activities occur), spatial characteristics (geographic locations and network origins), functional scope (which services and resources are accessed), frequency distributions (how often specific actions happen), and sequential dependencies (logical order of operations). Each dimension contributes unique insights that collectively paint a comprehensive picture of expected behavior.
For AWS environments, baseline profiling focuses heavily on API call patterns and resource access sequences. Normal administrative workflows often involve predictable combinations of services—for example, launching EC2 instances requires coordinated calls to EC2, VPC, and possibly IAM services. Deviations from these established patterns, such as simultaneously accessing unrelated services like DynamoDB and Redshift, may indicate unauthorized administrative activities. Additionally, examining the timing and frequency of these calls helps differentiate between legitimate bulk operations and potentially malicious reconnaissance or data exfiltration attempts.
Azure environments present unique challenges due to their extensive service catalog and complex identity management capabilities. Baseline profiles must account for various authentication methods including interactive logins, service principals, managed identities, and certificate-based authentication. Each method exhibits distinct behavioral signatures that require separate modeling. For instance, interactive administrative sessions typically show longer durations with varied API interactions, while automated service principal activities demonstrate consistent, repetitive patterns optimized for specific tasks.
Google Cloud Platform introduces additional complexity through its granular IAM model and extensive integration capabilities. Effective baseline creation here requires understanding project hierarchies, organization-level policies, and cross-project resource sharing mechanisms. Administrative activities often span multiple projects and folders, creating intricate dependency chains that must be accurately captured in behavioral models. Failure to account for these interdependencies can result in excessive false positives or missed detections.
Advanced profiling techniques leverage machine learning algorithms to automatically discover behavioral patterns from raw log data. Unsupervised clustering methods group similar activities together, revealing natural behavioral categories that human analysts might overlook. Time series analysis identifies cyclical patterns and seasonal trends, helping distinguish between routine maintenance activities and anomalous behavior. Feature engineering transforms raw log attributes into meaningful behavioral indicators that enhance detection accuracy.
Continuous refinement represents another crucial aspect of successful baseline management. As organizations evolve, so do their operational practices and security requirements. Static behavioral models quickly become outdated, leading to increased false positive rates and reduced detection effectiveness. Adaptive profiling systems automatically update baseline parameters based on recent activity trends, ensuring models remain relevant and accurate. Regular validation against known good and bad examples helps maintain optimal performance levels.
Actionable Takeaway: Implement adaptive behavioral profiling that continuously learns from cloud activity patterns to maintain accurate baselines for shadow admin detection.
How Do You Detect Anomalous Administrative Actions Across Cloud Platforms?
Detecting anomalous administrative actions requires sophisticated analytical approaches that can process massive volumes of cloud activity data while maintaining low false positive rates. Modern detection systems combine statistical anomaly detection, rule-based alerting, and machine learning techniques to identify suspicious behaviors that indicate potential shadow administrator activities. Each cloud platform presents unique challenges and opportunities for anomaly detection, requiring tailored approaches that leverage platform-specific features and logging capabilities.
AWS CloudTrail analysis forms the foundation of anomaly detection in Amazon Web Services environments. CloudTrail captures detailed records of API calls, including caller identity, timestamp, source IP address, user agent, and response elements. Effective detection strategies analyze these attributes to identify unusual patterns such as administrative actions originating from unfamiliar IP addresses, occurring outside normal business hours, or involving unusual combinations of services. For example, a user account that typically manages S3 buckets suddenly calling IAM modification APIs would trigger immediate investigation.
Sigma rules provide standardized detection logic that can be applied consistently across different SIEM platforms and log sources. A sample Sigma rule for detecting unusual AWS administrative activities might look like this:
yaml title: Suspicious AWS Administrative Activity id: aws-suspicious-admin-behavior status: experimental description: Detects unusual administrative activities that deviate from normal patterns date: 2026/03/30 author: Cloud Security Team logsource: product: aws service: cloudtrail detection: selection_admin_actions: eventSource: 'iam.amazonaws.com' eventName: - 'CreateUser' - 'AttachUserPolicy' - 'CreateRole' - 'PutRolePolicy' exclusion_legitimate_admins: userIdentity.arn|contains: - 'arn:aws:sts::123456789012:assumed-role/LegitimateAdminRole/' - 'arn:aws:iam::123456789012:user/ApprovedAdminUser' timeframe: last_24h condition: selection_admin_actions and not exclusion_legitimate_admins fields: - userIdentity.arn - eventName - eventTime - sourceIPAddress falsepositives: - Legitimate administrative activities not covered by exclusions level: high
Azure Activity Logs present different detection opportunities due to their structured approach to capturing management plane operations. Unlike AWS's API-centric logging, Azure focuses on resource-level changes and management events. This difference affects detection strategies, emphasizing resource modification patterns over individual API call analysis. Effective Azure detection looks for unusual combinations of resource types being modified, unexpected geographic locations, and abnormal timing patterns.
GCP audit logs introduce additional complexity through their three-tier structure: Admin Activity, Data Access, and Policy Denied logs. Each tier serves different purposes and contains varying levels of detail. Admin Activity logs capture administrative actions affecting configuration or metadata, making them ideal for detecting shadow administrator activities. Data Access logs reveal actual data operations, useful for identifying potential data exfiltration attempts by unauthorized administrators.
Machine learning approaches significantly enhance anomaly detection capabilities by automatically discovering complex behavioral patterns that rule-based systems might miss. Isolation forests excel at identifying outliers in high-dimensional feature spaces, making them particularly effective for detecting unusual combinations of behavioral attributes. Autoencoders learn normal behavior representations and flag inputs that cannot be reconstructed accurately, indicating potential anomalies. Ensemble methods combining multiple algorithms often provide superior performance compared to individual techniques.
Real-time processing becomes critical for effective anomaly detection, especially in large-scale cloud environments generating millions of log entries daily. Stream processing frameworks like Apache Kafka and Apache Flink enable continuous analysis of incoming log data, allowing immediate response to detected threats. Alert prioritization mechanisms ensure security teams focus on the most critical findings while managing alert fatigue from less severe anomalies.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
Practical Tip: Combine statistical anomaly detection with targeted Sigma rules to achieve comprehensive coverage while minimizing false positives in shadow admin detection.
How Can You Correlate Cross-Account Activities to Identify Shadow Admins?
Cross-account activities represent one of the most challenging aspects of cloud security monitoring, particularly when trying to identify shadow administrators who operate across multiple accounts or subscriptions. These activities often involve complex trust relationships, federated identities, and temporary credential mechanisms that can obscure the true nature of administrative actions. Effective correlation requires sophisticated analytical approaches that can trace user activities across account boundaries and reconstruct complete behavioral timelines.
In AWS environments, cross-account correlation centers around role assumption mechanisms and resource-based policies that enable access delegation. When a user in Account A assumes a role in Account B, CloudTrail logs capture both the AssumeRole action in Account A and subsequent activities in Account B. However, connecting these disparate log entries requires careful attention to correlation identifiers such as role session names, external IDs, and transitive tag keys. Advanced correlation systems automatically link related activities using these identifiers to create unified behavioral profiles spanning multiple accounts.
Consider a practical example where an attacker compromises a developer account in a non-production environment and uses it to assume administrative roles in production accounts. Traditional single-account analysis might miss this threat since each account's logs appear normal in isolation. Cross-account correlation reveals the complete attack chain by tracing the initial compromise through role assumption events to final malicious activities. This holistic view enables security teams to understand the full scope of incidents and implement appropriate remediation measures.
Azure's multi-tenant architecture introduces additional complexity for cross-account correlation due to its extensive identity federation capabilities. Users can authenticate through various identity providers including Azure AD, Microsoft accounts, social providers, and enterprise directories. Service principals and managed identities add further layers of indirection that must be carefully tracked across subscriptions and tenants. Effective correlation systems maintain identity mappings across these diverse authentication mechanisms to ensure comprehensive activity tracking.
Google Cloud Platform's hierarchical organization structure creates unique correlation challenges and opportunities. Organizations, folders, projects, and resources form nested containment relationships that affect permission inheritance and access control evaluation. Cross-project activities require understanding these relationships to determine whether observed behaviors represent legitimate administrative workflows or unauthorized access attempts. Resource hierarchy-aware correlation systems can distinguish between authorized cross-project operations and suspicious lateral movement patterns.
Technical implementation of cross-account correlation involves several key components working together to create unified behavioral views. Identity resolution systems map various authentication identifiers to consistent user representations across different accounts and platforms. Event sequencing mechanisms order activities chronologically regardless of their source account or logging system. Context enrichment processes add relevant metadata such as business unit classifications, sensitivity labels, and risk scores to correlated events.
Modern correlation approaches leverage graph databases and relationship modeling to represent complex cross-account relationships effectively. Nodes represent users, roles, resources, and accounts, while edges capture various types of relationships including access grants, usage patterns, and temporal dependencies. Graph traversal algorithms can efficiently identify suspicious patterns such as rapid account hopping, unusual access chains, or violation of segregation of duties principles.
Visualization tools play a crucial role in making cross-account correlations understandable to security analysts. Interactive dashboards display correlated activities in timeline views, showing how users move between accounts and what actions they perform in each location. Network diagrams illustrate access relationships and highlight potential privilege escalation paths. Heat maps reveal temporal patterns and geographic distributions of cross-account activities.
Key Insight: Cross-account correlation transforms isolated security events into comprehensive behavioral narratives, enabling detection of shadow admins who exploit multi-account architectures for unauthorized access.
What Techniques Identify Service Account Misuse Indicating Shadow Admins?
Service account misuse represents a particularly insidious form of shadow administration since these accounts are designed for automated operations and often possess broad permissions necessary for their intended functions. Detecting unauthorized use of service accounts requires understanding their legitimate operational patterns and identifying deviations that suggest malicious activity. Unlike human user accounts, service accounts exhibit highly predictable behavior patterns that make anomaly detection both easier and more challenging—their consistency makes normal behavior obvious, but also means that subtle unauthorized activities can easily blend in with legitimate operations.
AWS service accounts primarily take the form of IAM roles assumed by applications, Lambda functions, EC2 instances, and other AWS services. These roles typically have narrowly defined permissions aligned with specific operational requirements. Misuse occurs when attackers either compromise existing service roles or create new ones with excessive permissions. Detection focuses on identifying unusual API call patterns, unexpected geographic locations, irregular timing, and access to resources outside the service's normal operational scope.
A common misuse pattern involves attackers modifying service role trust policies to allow assumption from unauthorized principals. For example, an EC2 instance profile designed for S3 access might have its trust policy altered to permit assumption from any authenticated user. Behavioral analysis detects this by monitoring AssumeRole events and comparing requesting principals against expected patterns. Sigma rules can specifically target suspicious trust policy modifications:
yaml title: Suspicious IAM Role Trust Policy Modification id: iam-trust-policy-modification status: experimental description: Detects modification of IAM role trust policies that could enable unauthorized access date: 2026/03/30 author: Cloud Security Team logsource: product: aws service: cloudtrail detection: selection_modify_trust: eventSource: 'iam.amazonaws.com' eventName: 'UpdateAssumeRolePolicy' selection_suspicious_principals: requestParameters.policyDocument|contains: - '"Principal":""' - '"Principal":{"AWS":""}' - '"Principal":{"Federated":""}' timeframe: last_1h condition: selection_modify_trust and selection_suspicious_principals fields: - userIdentity.arn - requestParameters.roleName - requestParameters.policyDocument - eventTime falsepositives: - Legitimate broadening of role trust policies for business reasons level: critical
Azure service principal misuse often involves attackers creating new applications with excessive permissions or compromising existing service principals through credential theft. Managed identities present additional challenges since they're automatically rotated and don't expose traditional credentials. Detection strategies monitor application registration activities, permission grant operations, and unusual API consumption patterns. For instance, a service principal suddenly accessing Azure Key Vault or Microsoft Graph APIs might indicate compromise.
Google Cloud service account misuse commonly involves attackers creating new service accounts with broad permissions or modifying existing ones to expand access. Since service accounts use key files or can be impersonated through IAM policies, attackers often attempt to generate new keys or modify binding policies. Detection focuses on monitoring service account creation events, key generation activities, and unusual API access patterns that deviate from established baselines.
Behavioral analysis of service accounts requires specialized approaches since their activities differ fundamentally from human users. Machine learning models trained specifically on service account data can identify subtle anomalies that might escape general-purpose detection systems. Features such as API call frequency consistency, resource access patterns, and temporal regularity prove particularly valuable for distinguishing normal from malicious service account behavior.
Advanced detection techniques leverage peer group analysis to compare service account behavior against similar accounts within the same application category or business function. Significant deviations from peer group norms trigger investigation even when absolute behavior appears normal. This approach helps identify compromised accounts that maintain generally acceptable activity levels while performing unauthorized operations.
Continuous monitoring becomes essential for effective service account protection since attacks can occur at any time and may involve brief, targeted activities designed to avoid detection. Real-time alerting systems must balance sensitivity with specificity to prevent overwhelming security teams with false positives while ensuring critical threats receive immediate attention. Automated response mechanisms can temporarily disable suspicious service accounts pending investigation, reducing potential damage from ongoing attacks.
Actionable Takeaway: Monitor service account behavior patterns rigorously, focusing on trust policy modifications, unusual API access, and deviation from established operational baselines to detect shadow admin activities.
How Do You Implement Continuous Monitoring Using Native Cloud Logging Services?
Continuous monitoring forms the backbone of effective shadow administrator detection, requiring robust collection, processing, and analysis of cloud activity logs across all major platforms. Native cloud logging services provide comprehensive visibility into user and service activities, but implementing effective monitoring demands sophisticated architectural design and operational practices that can scale with growing cloud footprints while maintaining high detection fidelity. Successful implementations combine automated log ingestion, intelligent alerting, and adaptive analysis techniques to create responsive security monitoring systems.
AWS CloudTrail serves as the primary source for continuous monitoring in Amazon environments, capturing detailed records of API calls, user activities, and resource changes across all supported services. Effective monitoring architectures typically deploy CloudTrail to deliver logs to centralized S3 buckets with appropriate lifecycle policies for cost optimization. Additional CloudWatch Events rules can trigger near real-time processing of high-priority events such as IAM modifications or console logins from unusual locations. Integration with Amazon Athena enables ad-hoc querying of historical log data for investigative purposes.
Configuration of CloudTrail for optimal monitoring requires careful consideration of delivery frequencies, log file integrity validation, and multi-region coverage. Standard configurations deliver logs every five minutes, but high-security environments may require more frequent delivery. Log file validation using digest files ensures tamper evidence, critical for forensic investigations. Multi-region trails capture activities across all commercial regions, preventing gaps in coverage that attackers might exploit.
Azure Monitor and Activity Logs provide equivalent monitoring capabilities for Microsoft cloud environments, capturing management plane operations and resource-level changes across Azure services. Activity Logs contain information about subscription-level events such as resource creation, policy changes, and health notifications. Diagnostic settings enable forwarding of detailed service logs to Log Analytics workspaces or storage accounts for long-term retention and analysis. Event Hubs integration supports real-time stream processing for immediate threat detection.
Google Cloud's operations suite combines Cloud Audit Logs, Cloud Monitoring, and Cloud Logging to provide comprehensive visibility into GCP activities. Admin Activity logs capture administrative actions affecting configuration and metadata, while Data Access logs reveal actual data operations. Cloud Monitoring provides metrics and alerting capabilities, while Cloud Logging offers flexible query interfaces and export mechanisms. Pub/Sub integration enables real-time processing of log entries for immediate threat response.
Centralized log management architectures typically employ SIEM solutions or custom-built platforms to aggregate logs from multiple cloud providers and on-premises systems. These platforms normalize log formats, enrich events with contextual information, and apply detection rules consistently across diverse data sources. Popular choices include Splunk, Elasticsearch, and custom solutions built on open-source components. Cloud-native alternatives like AWS Security Hub, Azure Sentinel, and Google Chronicle offer integrated monitoring capabilities with minimal infrastructure overhead.
Automated alerting mechanisms must balance sensitivity with manageability to prevent alert fatigue while ensuring critical threats receive immediate attention. Tiered alerting approaches categorize findings by severity and confidence level, routing high-confidence critical alerts to immediate response teams while directing lower-severity items to routine investigation queues. Dynamic threshold adjustment based on historical trends helps maintain appropriate sensitivity levels despite changing operational conditions.
Performance optimization becomes crucial as log volumes grow exponentially with expanding cloud usage. Efficient indexing strategies, partitioning schemes, and query optimization techniques ensure responsive monitoring systems even under heavy load conditions. Data retention policies balance compliance requirements with storage costs, automatically archiving older logs to cheaper storage tiers while maintaining quick access to recent events for active investigations.
Key Insight: Continuous monitoring requires integrated architectures that collect, process, and analyze cloud logs in real-time while scaling efficiently and maintaining high detection accuracy across diverse cloud environments.
What Specific Sigma Rules Help Detect Shadow Administrator Behaviors?
Sigma rules provide standardized detection logic that enables consistent threat identification across different SIEM platforms and cloud environments. For shadow administrator detection, Sigma rules focus on identifying behavioral patterns that indicate unauthorized administrative access rather than simply checking permission assignments. Effective Sigma rules combine multiple conditions to reduce false positives while maintaining high detection coverage for various shadow admin scenarios. These rules leverage platform-specific log attributes and behavioral indicators to create precise detection criteria.
AWS-specific Sigma rules target common shadow admin behaviors such as unusual IAM modifications, suspicious console access patterns, and unauthorized role assumptions. A comprehensive rule set might include detections for bulk permission changes, creation of overly permissive policies, modification of trust relationships, and access from unexpected geographic locations. These rules often incorporate temporal conditions to identify activities outside normal business hours and contextual filters to exclude known legitimate administrative workflows.
Example Sigma rule detecting unusual IAM policy creation:
yaml title: Unusual IAM Policy Creation with Administrative Permissions id: unusual-iam-policy-creation status: experimental description: Detects creation of IAM policies containing administrative permissions from unusual contexts date: 2026/03/30 author: Cloud Security Team logsource: product: aws service: cloudtrail detection: selection_policy_create: eventSource: 'iam.amazonaws.com' eventName: 'CreatePolicy' selection_admin_permissions: requestParameters.policyDocument.Statement.Action|contains: - '' - 'iam:' - 'ec2:' - 's3:' selection_unusual_context: userIdentity.type: 'AssumedRole' userIdentity.sessionContext.sessionIssuer.type: 'Role' userIdentity.sessionContext.attributes.creationDate|time_delta_hours:> 24 timeframe: last_1h condition: selection_policy_create and selection_admin_permissions and selection_unusual_context fields: - userIdentity.arn - requestParameters.policyName - requestParameters.policyDocument - eventTime - sourceIPAddress falsepositives: - Legitimate administrative policy creation during deployment processes - Automated security tooling creating temporary administrative policies level: high
Azure Sigma rules focus on detecting suspicious application registrations, permission grants, and administrative API access patterns. Common detections include creation of applications with excessive permissions, granting of admin consent to suspicious applications, and unusual access to Azure Active Directory management APIs. These rules often incorporate tenant-specific context to reduce false positives from legitimate administrative activities.
GCP Sigma rules target behaviors such as unusual service account creation, modification of IAM bindings with broad permissions, and access to sensitive APIs from unexpected sources. Detection logic considers project hierarchies, organization policies, and cross-project access patterns to identify potentially unauthorized administrative activities. Geographic and temporal conditions help distinguish between legitimate global operations and suspicious access attempts.
Multi-platform Sigma rules enable consistent detection across different cloud environments by focusing on behavioral patterns that transcend specific platforms. These rules detect activities such as simultaneous administrative actions across multiple clouds, unusual credential usage patterns, and coordination between different cloud services that might indicate orchestrated attacks. Cross-platform correlation enhances overall detection effectiveness while reducing complexity compared to maintaining separate rule sets for each environment.
Rule tuning and optimization become critical for maintaining effective detection coverage without overwhelming security teams with false positives. Regular review of rule performance metrics helps identify opportunities for improvement, while feedback from incident investigations informs refinements to detection logic. Automated testing frameworks validate rule effectiveness against historical data and synthetic attack scenarios to ensure continued relevance.
Integration with threat intelligence feeds enhances Sigma rule effectiveness by incorporating known malicious indicators and emerging threat patterns. Rules can dynamically adjust sensitivity based on current threat levels and incorporate reputation data for IP addresses, domains, and user agents. This integration helps prioritize alerts based on threat severity and enables proactive detection of evolving attack techniques targeting shadow administrators.
Actionable Takeaway: Deploy comprehensive Sigma rule sets that target behavioral indicators of shadow admin activities across all major cloud platforms, regularly tuning rules based on operational feedback and threat intelligence updates.
Key Takeaways
• Behavioral analytics surpasses traditional permission scanning by detecting shadow administrators through actual activity patterns rather than static access rights • Establishing accurate baseline behavior profiles requires collecting extensive historical data across temporal, spatial, and functional dimensions for each cloud platform • Cross-account correlation techniques connect disparate log entries to reveal complete attack chains that span multiple cloud environments and identity domains • Service account misuse detection focuses on identifying deviations from established operational patterns, including trust policy modifications and unusual API access sequences • Continuous monitoring architectures must integrate native cloud logging services with centralized analysis platforms to maintain real-time visibility across hybrid cloud environments • Sigma rules provide standardized detection logic that targets specific behavioral indicators of shadow administrator activities while minimizing false positive rates • Implementation of these techniques requires sophisticated tooling and expertise, which security professionals can accelerate using mr7.ai's AI-powered platforms like mr7 Agent
Frequently Asked Questions
Q: How does behavioral analysis differ from traditional IAM permission scanning for detecting shadow admins?
Traditional IAM scanning only examines assigned permissions at a point in time, missing accounts that gain temporary or conditional administrative access. Behavioral analysis monitors actual user activities and API calls over time, identifying unauthorized administrative actions regardless of formal permission assignments. This approach catches shadow admins who exploit misconfigurations, temporary role assumptions, or overly permissive policies that static scanning would overlook.
Q: What are the most effective behavioral indicators for identifying shadow administrator activities?
The most effective indicators include unusual timing patterns (admin actions outside business hours), geographic anomalies (access from unexpected locations), API call sequence irregularities (unusual combinations of administrative services), and resource access patterns that deviate from established baselines. Additionally, rapid privilege escalation, simultaneous access to unrelated systems, and bypassing normal approval workflows strongly suggest shadow admin activities.
Q: How can organizations implement cross-account correlation without overwhelming their security teams?
Organizations should start with high-risk accounts and critical business processes, gradually expanding correlation coverage based on demonstrated value. Automated correlation systems that prioritize findings based on risk scores and business impact help manage alert volume. Integration with existing ticketing systems and workflow automation tools streamlines investigation processes while maintaining appropriate oversight and documentation.
Q: What specific cloud logging configurations optimize detection of shadow administrator behaviors?
Optimal configurations include enabling detailed logging for all administrative APIs, configuring real-time log delivery to centralized analysis platforms, implementing log integrity verification to prevent tampering, and establishing appropriate retention periods for forensic investigations. Multi-region logging coverage prevents geographic evasion tactics, while diagnostic logging for key services provides additional behavioral context for analysis.
Q: How frequently should behavioral baselines be updated to maintain detection effectiveness?
Baselines should be updated continuously using adaptive learning algorithms that incorporate recent activity trends while maintaining stability for reliable anomaly detection. Major organizational changes such as new business processes, seasonal variations, or infrastructure migrations require manual baseline adjustments to prevent false positives. Regular validation against known good and bad examples ensures baselines remain accurate and effective over time.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.