Automating Reconnaissance for Bug Bounty Success: A Comprehensive Guide
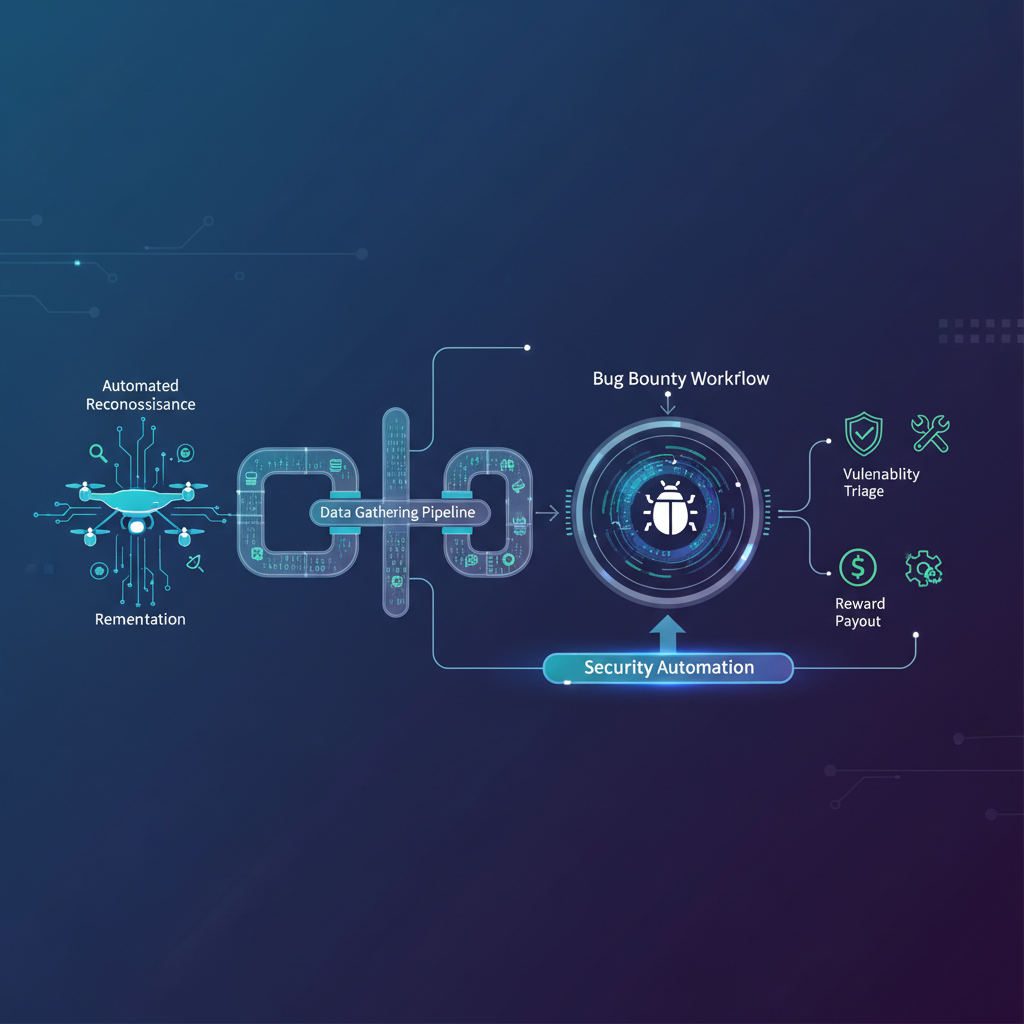
Automating Reconnaissance for Bug Bounty Success: A Comprehensive Guide Automating reconnaissance is crucial for efficient bug bounty hunting. By leveraging advanced tools and techniques, you can significantly reduce the time spent on manual tasks and focus on high-value targets. This guide will walk you through the key components of automated reconnaissance, including subdomain enumeration, port scanning, content discovery, and JavaScript analysis. We'll also explore how AI can help build efficient recon pipelines. ## Subdomain Enumeration: Uncovering Hidden Targets Subdomain enumeration is the foundation of any effective reconnaissance strategy. It involves discovering all the subdomains associated with a target domain, which can reveal hidden services, misconfigurations, and potential entry points. ### Tools and Techniques - Passive Enumeration: Gather subdomains from public sources without interacting with the target. Tools like Amass and Subfinder are excellent for this purpose. - Active Enumeration: Use DNS queries to discover subdomains. Tools like dnsrecon and dnsenum can be used for this. - Brute-Force Enumeration: Use wordlists to guess potential subdomains. Gobuster and SubBrute are popular choices. ### Example Command-Line Usage bash # Using Amass for passive enumeration amass enum -d example.com # Using Subfinder for passive enumeration subfinder -d example.com # Using Gobuster for brute-force enumeration gobuster dns -d example.com -w /path/to/wordlist.txt ### Best Practices - Combine multiple tools to maximize coverage. - Use public and private wordlists to increase the chances of discovering hidden subdomains. - Validate discovered subdomains to filter out false positives. ## Port Scanning: Identifying Open Doors Once you have a list of subdomains, the next step is to identify open ports and services. Port scanning helps you understand what services are running and can reveal potential vulnerabilities. ### Tools and Techniques - Nmap: The go-to tool for port scanning, offering a wide range of options and scripts. - Masscan: Fast and scalable port scanner ideal for large-scale scans. - Naabu: A fast port scanner written in Go, known for its speed and efficiency. ### Example Command-Line Usage bash # Using Nmap for a basic scan nmap -sS -p- example.com # Using Masscan for a fast scan masscan -p1-65535 example.com # Using Naabu for a quick scan naabu -host example.com -p 1-65535 ### Best Practices - Start with a broad scan to identify all open ports. - Follow up with more targeted scans using Nmap scripts to gather detailed information. - Use stealth techniques to avoid detection, such as TCP SYN scans. ## Content Discovery: Mapping the Attack Surface Content discovery involves identifying all the files, directories, and resources available on a target web application. This step is crucial for finding hidden endpoints, sensitive files, and potential entry points. ### Tools and Techniques - Gobuster: A versatile directory and file brute-forcer. - Dirb: Another popular directory brute-forcer with a large wordlist. - FFUF: A fast web fuzzer for discovering hidden content. ### Example Command-Line Usage bash # Using Gobuster for directory brute-forcing gobuster dir -u http://example.com -w /path/to/wordlist.txt # Using Dirb for directory brute-forcing dirb http://example.com /path/to/wordlist.txt # Using FFUF for web fuzzing ffuf -u http://example.com/FUZZ -w /path/to/wordlist.txt ### Best Practices - Use large and diverse wordlists to cover a wide range of potential targets. - Customize your wordlists based on the technology stack of the target application. - Validate discovered content to ensure it's accessible and relevant. Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. ## JavaScript Analysis: Uncovering Client-Side Vulnerabilities JavaScript analysis is often overlooked but can reveal critical client-side vulnerabilities. By analyzing the JavaScript code, you can identify security flaws, sensitive data leaks, and potential entry points for attacks. ### Tools and Techniques - JSBeautifier: Format and beautify JavaScript code for easier analysis. - JSLint: Lint JavaScript code to identify potential issues. - LinkFinder: Extract endpoints and secrets from JavaScript files. ### Example Command-Line Usage bash # Using JSBeautifier to format JavaScript code js-beautify example.js # Using JSLint to lint JavaScript code jslint example.js # Using LinkFinder to extract endpoints linkfinder example.js ### Best Practices - Download and analyze all JavaScript files from the target application. - Look for sensitive data, such as API keys, tokens, and endpoints. - Use static analysis tools to identify common vulnerabilities and coding errors. ## Building Efficient Recon Pipelines with AI Automating reconnaissance can be further enhanced by integrating AI tools. AI can help analyze large datasets, identify patterns, and prioritize targets, making your recon process more efficient and effective. ### AI-Powered Tools and Techniques - KaliGPT: An AI-powered assistant for Kali Linux, helping you automate and optimize your reconnaissance tasks. - 0Day Coder: Assists in identifying and exploiting zero-day vulnerabilities by analyzing code and behavior patterns. - DarkGPT: Specializes in dark web intelligence, helping you discover hidden services and potential threats. - OnionGPT: Focuses on Tor network analysis, aiding in the discovery of onion services and anonymous communication channels. ### Example Use Cases - Subdomain Clustering: Use AI to cluster subdomains based on similarity, helping you identify related services and potential misconfigurations. - Port Anomaly Detection: AI can help detect anomalous port behavior, indicating potential vulnerabilities or hidden services. - Content Prioritization: Analyze discovered content to prioritize high-value targets based on potential impact and exploitability. ### Comparison Table: AI Tools for Recon | Tool Name | Primary Function | Benefits | |-----------|-----------------|----------| | KaliGPT | Automates Kali tasks | Efficient task management, optimized workflows | | 0Day Coder | Zero-day vulnerability identification | Early detection of exploits, code analysis | | DarkGPT | Dark web intelligence | Discovery of hidden services, threat analysis | | OnionGPT | Tor network analysis | Identification of onion services, anonymous communication | ### Best Practices - Integrate AI tools into your existing recon pipeline to enhance efficiency. - Use AI for data analysis and pattern recognition to uncover hidden insights. - Continuously update and train your AI models to adapt to new threats and techniques. ## Ready to Level Up Your Security Research? Get 10,000 free tokens and start using KaliGPT, 0Day Coder, DarkGPT, and OnionGPT today. No credit card required! Start Free →
Key Takeaways
- Automating reconnaissance is essential for bug bounty hunters to reduce manual effort and identify high-value targets efficiently.
- Key components of automated reconnaissance include subdomain enumeration, port scanning, content discovery, and JavaScript analysis.
- Leveraging specialized tools for each reconnaissance phase can uncover hidden assets and potential vulnerabilities that manual methods might miss.
- Integrating these automated techniques into a streamlined workflow allows for continuous monitoring and faster identification of attack surfaces.
- Focusing on a systematic approach to automation, from initial asset discovery to in-depth analysis, maximizes the chances of finding critical bugs.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: What are the core components of an effective automated reconnaissance workflow for bug bounties?
An effective automated reconnaissance workflow typically involves subdomain enumeration to discover all related assets, port scanning to identify open services, content discovery to find hidden directories and files, and JavaScript analysis to uncover API endpoints and client-side vulnerabilities. Combining these steps provides a comprehensive view of the target's attack surface.
Q: Why is JavaScript analysis specifically important in automated reconnaissance?
JavaScript analysis is crucial because it can reveal sensitive API endpoints, hidden functionalities, and client-side vulnerabilities that might not be apparent from server-side checks. Automated tools can parse JavaScript files to extract valuable information like secrets, domain names, and potential XSS vectors.
Q: How does automating reconnaissance truly save time for bug bounty hunters compared to manual methods?
Automating reconnaissance saves time by performing repetitive and exhaustive tasks much faster and more consistently than a human can. For instance, a script can enumerate thousands of subdomains and scan hundreds of ports in minutes, allowing the hunter to dedicate their valuable time to analyzing findings and exploiting vulnerabilities rather than discovery.
Q: How can AI tools help with automating reconnaissance for bug bounties?
AI tools can significantly enhance automated reconnaissance by intelligently processing large datasets, identifying patterns, and even suggesting potential vulnerabilities based on discovered information. Specifically, platforms like mr7.ai, KaliGPT, and mr7 Agent can assist with tasks like intelligently parsing scan results, generating custom wordlists, and even automating exploit development for identified weaknesses.
Q: What is the best way to get started with implementing automated reconnaissance techniques if I'm new to bug bounties?
The best way to get started is to begin with widely accepted open-source tools for each core component like subdomain enumeration and port scanning, and then gradually integrate them into simple scripts. You can also leverage platforms that provide free tokens or trials to experiment with advanced AI-powered tools, such as trying mr7.ai's free tokens, to accelerate your learning and discovery process.
Ready to Level Up Your Security Research?
Get 10,000 free tokens and start using KaliGPT, 0Day Coder, DarkGPT, OnionGPT, and mr7 Agent today. No credit card required!