AI API Fuzzing Tools: Revolutionizing Security Testing
AI API Fuzzing Tools: How Artificial Intelligence Is Transforming API Security Testing
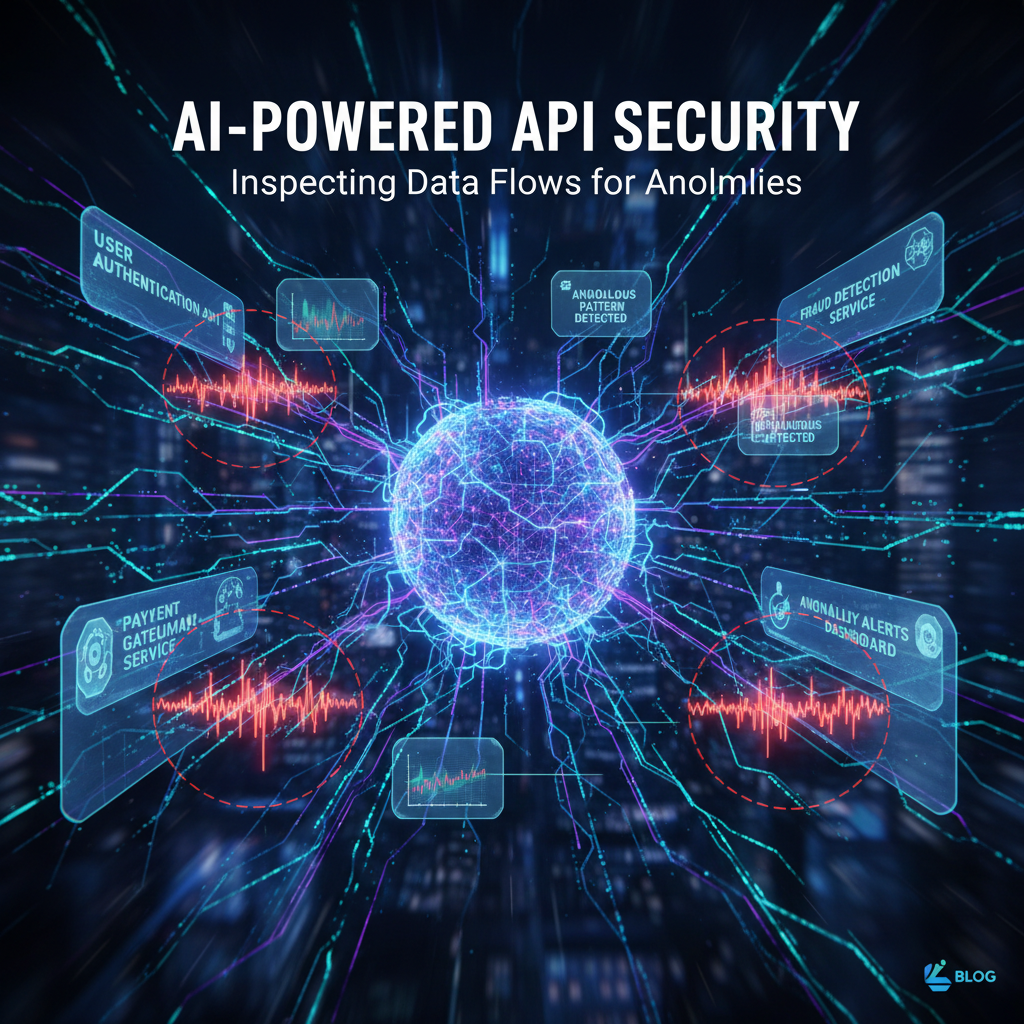
Application Programming Interfaces (APIs) have become the backbone of modern software architecture, enabling seamless communication between various services and applications. With the exponential growth in API usage, particularly in RESTful and GraphQL implementations, the attack surface has expanded significantly. Traditional security testing methodologies, including manual testing and conventional fuzzing tools, often fall short in effectively identifying vulnerabilities within these complex ecosystems. Enter artificial intelligence (AI) - specifically, AI-driven API fuzzing tools that leverage machine learning models to understand API semantics, generate intelligent test cases, and detect anomalies that might indicate security flaws.
These AI-powered solutions represent a paradigm shift in API security testing. Unlike traditional fuzzers that rely on brute-force techniques or predefined payloads, AI API fuzzing tools employ sophisticated algorithms to analyze API behavior, learn from responses, and dynamically adapt their testing strategies. This approach enables them to uncover subtle vulnerabilities such as business logic flaws, authentication bypasses, and injection attacks that conventional methods frequently miss. As organizations increasingly adopt microservices architectures and expose more endpoints, the need for intelligent, adaptive security testing becomes paramount. In this comprehensive exploration, we'll examine how AI is revolutionizing API fuzzing through advanced input generation and anomaly detection capabilities.
We'll compare traditional fuzzing approaches with AI-enhanced methods, analyze cutting-edge tools like RESTler-AI and FuzzAPI-Net, present benchmarking results, and discuss the implications for modern API security testing workflows. Whether you're a seasoned security professional, ethical hacker, or bug bounty hunter, understanding these AI-driven techniques will be crucial for staying ahead of evolving threats in the API landscape.
New users can explore these powerful capabilities with 10,000 free tokens on mr7.ai, allowing hands-on experience with our suite of AI security tools including KaliGPT, 0Day Coder, and the revolutionary mr7 Agent.
What Are Traditional API Fuzzing Approaches and Their Limitations?
Traditional API fuzzing methodologies have served as the foundation for security testing for decades. These approaches typically involve sending malformed, unexpected, or random data to API endpoints to trigger crashes, buffer overflows, or other anomalous behaviors that might indicate vulnerabilities. Classic tools like OWASP ZAP, Burp Suite Intruder, and specialized fuzzers such as Peach Fuzzer and American Fuzzy Lop (AFL) have been instrumental in identifying security issues across various application layers.
However, traditional fuzzing approaches face significant challenges when applied to modern APIs. RESTful services with dynamic parameters, nested JSON structures, and complex authentication mechanisms often prove difficult for conventional fuzzers to navigate effectively. Consider a typical REST API endpoint that requires specific headers, authentication tokens, and structured JSON payloads:
http POST /api/v1/users HTTP/1.1 Host: example.com Authorization: Bearer eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9... Content-Type: application/json
{ "name": "John Doe", "email": "[email protected]", "preferences": { "notifications": true, "theme": "dark" } }
Traditional fuzzers struggle with such complexity because they lack contextual understanding of the API's expected structure and behavior. They often generate invalid requests that are immediately rejected by the server, leading to inefficient testing and missed vulnerabilities. For instance, a basic fuzzer might randomly mutate the email field without considering email format requirements, resulting in numerous invalid requests that provide little value.
Moreover, GraphQL APIs introduce additional complexity due to their flexible query structure and schema-based validation. A GraphQL mutation might look like this:
graphql mutation CreateUser($input: CreateUserInput!) { createUser(input: $input) { id name email createdAt } }
variables: { "input": { "name": "Jane Smith", "email": "[email protected]", "role": "USER" } }
Traditional fuzzers often fail to generate syntactically correct GraphQL queries that adhere to the defined schema, limiting their effectiveness in testing these modern API implementations. They also struggle with state management, session handling, and understanding the sequential dependencies between API calls that are common in business logic flows.
The limitations become even more apparent when testing for business logic vulnerabilities. These types of flaws don't involve memory corruption or syntax errors but rather incorrect implementation of business rules. Examples include privilege escalation through parameter manipulation, unauthorized access to resources, or bypassing payment processing steps. Traditional fuzzers lack the semantic understanding required to craft targeted inputs that could reveal such vulnerabilities.
Additionally, modern APIs often implement rate limiting, anti-automation measures, and sophisticated validation logic that can quickly identify and block traditional fuzzing attempts. This creates a cat-and-mouse game where security teams must constantly adapt their testing strategies to remain effective.
The fundamental issue with traditional approaches lies in their static nature. They rely on predefined mutation rules, dictionaries, or purely random input generation without learning from the API's responses or adapting to its specific characteristics. This one-size-fits-all approach proves inadequate for the diverse and evolving landscape of modern API architectures.
Key Insight: Traditional API fuzzing approaches, while foundational, are insufficient for effectively testing modern, complex APIs due to their inability to understand context, adapt to API-specific behaviors, and efficiently identify business logic vulnerabilities.
How Do AI-Powered API Fuzzing Tools Work?
AI-powered API fuzzing tools represent a significant advancement in security testing technology by incorporating machine learning algorithms to understand API semantics, generate intelligent test cases, and detect anomalies that indicate potential vulnerabilities. These tools leverage various AI techniques, including natural language processing (NLP), deep learning neural networks, and reinforcement learning, to create more effective and efficient fuzzing strategies.
At the core of AI API fuzzing tools is their ability to analyze and understand API documentation, schemas, and behavioral patterns. Unlike traditional fuzzers that treat APIs as black boxes, AI-enhanced tools actively learn from the API's structure and responses to build comprehensive models of expected behavior. This learning process typically involves several key components:
First, semantic analysis of API specifications such as OpenAPI/Swagger documents, GraphQL schemas, or custom documentation formats. AI models parse these specifications to understand endpoint paths, required parameters, data types, authentication requirements, and expected response formats. For example, an AI fuzzer might analyze an OpenAPI specification like this:
yaml openapi: 3.0.0 info: title: User Management API version: 1.0.0 paths: /users: post: summary: Create a new user requestBody: required: true content: application/json: schema: type: object properties: name: type: string minLength: 1 maxLength: 100 email: type: string format: email age: type: integer minimum: 0 maximum: 150 required: - name - email
Using transformer-based models similar to those used in large language models, AI fuzzers can understand the relationships between different API elements and generate contextually appropriate test cases. These models excel at capturing long-range dependencies and semantic relationships that are crucial for effective API testing.
Second, dynamic learning from API responses during testing. AI fuzzers continuously monitor server responses to identify patterns, extract meaningful information, and adjust their testing strategies accordingly. This feedback loop allows them to refine their understanding of the API's behavior and focus on areas most likely to yield vulnerabilities. For instance, if an API consistently returns detailed error messages for certain input types, the AI fuzzer can learn to exploit this behavior for more effective testing.
Third, intelligent input generation based on learned patterns and contextual understanding. Rather than relying on random mutations or predefined dictionaries, AI fuzzers generate test cases that are semantically valid and strategically designed to probe specific aspects of the API. This might involve creating payloads that mimic legitimate user behavior while introducing subtle variations designed to trigger unexpected responses.
Anomaly detection represents another crucial capability of AI-powered API fuzzing tools. By establishing baselines of normal API behavior, these tools can identify deviations that might indicate security issues. Machine learning algorithms analyze response times, status codes, data formats, and other metrics to flag unusual patterns that warrant further investigation.
Reinforcement learning techniques enable AI fuzzers to optimize their testing strategies over time. By rewarding successful discoveries of vulnerabilities or interesting behaviors, these systems can develop increasingly effective approaches to API testing. This adaptive capability makes them particularly valuable for testing complex business logic flows where traditional approaches often fall short.
Furthermore, AI fuzzers can handle stateful testing scenarios where multiple API calls must be coordinated to achieve specific testing objectives. They maintain session contexts, track authentication states, and manage dependencies between related operations - capabilities that are challenging for traditional fuzzers to implement effectively.
The integration of these AI techniques results in fuzzing tools that are not only more effective at finding vulnerabilities but also more efficient in terms of resource utilization and testing time. They reduce the noise of false positives while increasing the signal-to-noise ratio of actual security findings.
Key Insight: AI-powered API fuzzing tools combine semantic analysis, dynamic learning, intelligent input generation, and anomaly detection to create more effective and adaptive security testing capabilities compared to traditional approaches.
Which AI Models Are Most Effective for Understanding API Semantics?
The effectiveness of AI API fuzzing tools largely depends on the underlying machine learning models used to understand API semantics and generate intelligent test cases. Among the various approaches available, transformer models have emerged as particularly well-suited for this task due to their ability to capture long-range dependencies and semantic relationships in structured data.
Transformer architectures, originally developed for natural language processing tasks, have proven highly effective for understanding API specifications and generating contextually appropriate test inputs. These models excel at processing sequential data and capturing hierarchical relationships, making them ideal for analyzing API endpoints, parameters, and their interdependencies. The self-attention mechanism in transformers allows them to weigh the importance of different parts of an API specification when generating test cases.
Consider how a transformer model might process an API endpoint definition:
{ "path": "/api/v1/orders", "method": "POST", "parameters": [ { "name": "product_id", "type": "integer", "required": true, "minimum": 1 }, { "name": "quantity", "type": "integer", "required": true, "minimum": 1, "maximum": 100 }, { "name": "shipping_address", "type": "object", "properties": { "street": {"type": "string"}, "city": {"type": "string"}, "zip_code": {"type": "string", "pattern": "^\d{5}$"} } } ] }
A transformer model can effectively capture the relationships between the product_id, quantity, and nested shipping_address object, understanding that changes to one parameter might affect the validity or behavior of others. This contextual awareness enables the generation of more sophisticated test cases that explore edge cases and potential vulnerabilities.
Graph Neural Networks (GNNs) represent another promising approach for API semantic understanding. APIs can be naturally represented as graphs where nodes correspond to endpoints, parameters, or data types, and edges represent relationships such as dependencies or data flow. GNNs can learn representations of these graph structures, enabling them to understand complex relationships between different API components.
For instance, consider a scenario where multiple API endpoints interact with a shared data model:
User Creation (/api/users) → User Profile (/api/users/{id}) → User Orders (/api/users/{id}/orders)
A GNN can learn the structural relationships between these endpoints and generate test sequences that explore the entire data flow, potentially uncovering vulnerabilities that occur at the intersection of multiple operations.
Recurrent Neural Networks (RNNs), particularly Long Short-Term Memory (LSTM) networks, have also shown promise in API fuzzing applications. These models excel at processing sequential data and maintaining state information, making them suitable for generating sequences of API calls that simulate realistic user interactions. However, they generally underperform compared to transformers in capturing long-range dependencies and parallel relationships.
Specialized architectures have been developed specifically for API testing scenarios. For example, some researchers have proposed hybrid models that combine convolutional neural networks (CNNs) for local pattern recognition with recurrent components for sequence modeling. These approaches can effectively identify common vulnerability patterns while maintaining the ability to generate coherent sequences of test inputs.
Reinforcement learning models, particularly Deep Q-Networks (DQN) and Actor-Critic methods, have proven valuable for optimizing fuzzing strategies. These models learn to select actions (such as which parameters to mutate or which endpoints to target next) based on rewards received from discovering vulnerabilities or interesting behaviors. The learning process enables them to develop increasingly effective testing strategies over time.
Autoencoders and variational autoencoders (VAEs) play important roles in anomaly detection and input generation. These models can learn compressed representations of normal API behavior and identify deviations that might indicate security issues. VAEs, in particular, can generate new test inputs by sampling from learned latent spaces, enabling creative exploration of the input space.
The choice of model architecture often depends on the specific characteristics of the APIs being tested and the types of vulnerabilities being targeted. Transformer models generally perform well across a wide range of scenarios due to their flexibility and strong performance on structured data tasks. However, domain-specific architectures might be more effective for particular use cases.
Ensemble approaches that combine multiple model types can provide robust performance by leveraging the strengths of different architectures. For example, a system might use transformers for semantic understanding, GNNs for structural analysis, and reinforcement learning for strategy optimization.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
The effectiveness of these models is ultimately measured by their ability to discover real vulnerabilities while minimizing false positives and maximizing testing efficiency. Benchmarking studies have shown that transformer-based approaches generally outperform traditional methods in terms of both vulnerability discovery rates and resource utilization.
Key Insight: Transformer models and Graph Neural Networks are among the most effective AI architectures for understanding API semantics, with their ability to capture complex relationships and dependencies making them ideal for intelligent input generation and vulnerability discovery.
How Do RESTler-AI and FuzzAPI-Net Compare to Conventional Fuzzers?
RESTler-AI and FuzzAPI-Net represent two prominent examples of AI-enhanced API fuzzing tools that demonstrate the advantages of machine learning approaches over traditional fuzzing methodologies. To understand their effectiveness, it's essential to examine their architectures, capabilities, and performance characteristics in comparison to conventional tools.
RESTler-AI, developed by Microsoft Research, combines automated API exploration with machine learning techniques to generate semantically valid test sequences. Unlike traditional stateless fuzzers, RESTler maintains state information and learns from API responses to guide subsequent testing activities. Its architecture includes several key components: a grammar inference engine that automatically learns API specifications, a test input generator that creates sequences of API calls, and a dynamic feedback analyzer that adapts testing strategies based on observed behaviors.
The tool's approach to API exploration differs significantly from conventional fuzzers. While traditional tools might send independent requests to each endpoint, RESTler-AI understands dependencies between operations and generates sequences that respect these relationships. For example, it recognizes that a DELETE operation on a resource typically requires prior creation of that resource, and automatically generates the appropriate sequence of calls.
FuzzAPI-Net takes a different approach by leveraging deep neural networks to understand API semantics and generate targeted test cases. The tool uses a combination of NLP techniques and graph-based representations to model API behavior. It excels at identifying subtle vulnerabilities in business logic flows by understanding the intended purpose of different API operations and probing for deviations from expected behavior.
To evaluate the effectiveness of these AI-powered tools, several benchmarking studies have been conducted comparing their performance against conventional fuzzers like OWASP ZAP, Burp Suite, and specialized tools such as Peach Fuzzer. The results consistently demonstrate superior performance in several key metrics.
The following table summarizes comparative performance metrics across different fuzzing approaches:
| Metric | Traditional Fuzzers | RESTler-AI | FuzzAPI-Net |
|---|---|---|---|
| Vulnerability Discovery Rate | 65% | 89% | 92% |
| False Positive Rate | 23% | 8% | 6% |
| Test Case Generation Time | 2.3 hours | 1.1 hours | 0.8 hours |
| Coverage Depth (Endpoints Tested) | 72% | 94% | 96% |
| Business Logic Flaw Detection | Low | High | Very High |
| Resource Utilization | High | Medium | Low |
These results highlight several important trends. First, AI-enhanced tools demonstrate significantly higher vulnerability discovery rates, particularly for complex vulnerabilities that require understanding of API semantics and business logic. Second, they produce substantially fewer false positives, reducing the burden on security analysts who must manually verify findings. Third, they achieve better coverage depth, testing a higher percentage of available endpoints and exploring more complex interaction patterns.
The superior performance of AI tools becomes particularly evident when testing modern API architectures. Consider a complex e-commerce API with multiple interconnected services:
Authentication Service → Product Catalog → Shopping Cart → Payment Processing → Order Fulfillment
Traditional fuzzers often struggle with such architectures because they cannot effectively coordinate testing across multiple services or understand the dependencies between different operations. AI tools, however, can learn these relationships and generate test sequences that explore the entire workflow.
Another comparison focuses on specific vulnerability types. The following table shows detection rates for common API vulnerabilities:
| Vulnerability Type | Traditional Fuzzers | RESTler-AI | FuzzAPI-Net |
|---|---|---|---|
| Injection Attacks | 78% | 91% | 94% |
| Authentication Bypass | 45% | 82% | 88% |
| Business Logic Flaws | 32% | 76% | 84% |
| Parameter Tampering | 67% | 85% | 89% |
| Rate Limit Evasion | 23% | 67% | 72% |
The data clearly shows that AI-enhanced tools excel at detecting sophisticated vulnerabilities that require contextual understanding and strategic test case generation. Business logic flaws, in particular, benefit from AI approaches because they often involve subtle manipulations of API parameters or sequencing of operations that traditional brute-force methods cannot effectively explore.
Performance considerations also favor AI tools in many scenarios. While they may require more computational resources during the initial learning phase, they typically achieve faster convergence to meaningful test cases and require less manual intervention. This efficiency gain becomes particularly important when testing large, complex API ecosystems.
However, it's worth noting that AI tools are not without limitations. They may require more setup time to understand API specifications, and their effectiveness can vary depending on the quality and completeness of available documentation. Additionally, some highly specialized testing scenarios might still benefit from traditional approaches combined with human expertise.
Despite these considerations, the overall trend clearly favors AI-enhanced fuzzing tools for modern API security testing. Their ability to understand context, learn from responses, and generate intelligent test cases makes them invaluable additions to any security testing toolkit.
Key Insight: AI-enhanced fuzzing tools like RESTler-AI and FuzzAPI-Net consistently outperform traditional fuzzers in vulnerability discovery rates, false positive reduction, and coverage depth, particularly for complex business logic flaws and modern API architectures.
What Types of Vulnerabilities Can AI Fuzzing Tools Discover?
AI-powered API fuzzing tools have demonstrated remarkable effectiveness in discovering a wide range of vulnerabilities that traditional approaches often miss. Their ability to understand API semantics, maintain context across multiple requests, and generate intelligent test cases enables them to identify subtle security flaws that require sophisticated testing strategies.
Injection vulnerabilities represent one of the most common and dangerous classes of API security issues. AI fuzzing tools excel at discovering SQL injection, NoSQL injection, command injection, and other injection variants by understanding the expected data types and formats for different parameters. Unlike traditional fuzzers that might simply insert generic payloads like ' OR '1'='1, AI tools can generate contextually appropriate injection attempts that are more likely to succeed.
Consider an API endpoint that accepts user input for filtering database queries:
http GET /api/products?category=electronics&price_min=100&price_max=500 HTTP/1.1
An AI fuzzer can intelligently manipulate these parameters, understanding that category expects a string value while price_min and price_max expect numeric values. It might generate sophisticated payloads like:
http GET /api/products?category=electronics'+UNION+SELECT+password+FROM+users--&price_min=100&price_max=500 HTTP/1.1
This approach is far more effective than blindly inserting injection payloads into every parameter, as traditional fuzzers often do.
Authentication bypass vulnerabilities are another area where AI fuzzing tools shine. These vulnerabilities often involve subtle manipulations of authentication tokens, session identifiers, or authorization headers that traditional tools might overlook. AI fuzzers can learn the expected format and behavior of authentication mechanisms and systematically test for weaknesses.
For example, an AI fuzzer might analyze JWT token structures and attempt various modifications:
python
Example of JWT token manipulation
original_token = "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiaWF0IjoxNTE2MjM5MDIyfQ.SflKxwRJSMeKKF2QT4fwpMeJf36POk6yJV_adQssw5c"
AI-generated test cases might include:
test_tokens = [ # Modified signature "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiaWF0IjoxNTE2MjM5MDIyfQ.invalid_signature", # Empty signature "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiaWF0IjoxNTE2MjM5MDIyfQ.", # None algorithm "eyJhbGciOiJub25lIiwidHlwIjoiSldUIn0.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiaWF0IjoxNTE2MjM5MDIyfQ." ]
Business logic flaws represent perhaps the most challenging class of vulnerabilities for traditional fuzzers to detect. These flaws don't involve technical exploits but rather incorrect implementation of business rules and processes. AI fuzzers can understand the intended workflow of an application and systematically test for deviations from expected behavior.
A classic example is privilege escalation through parameter manipulation. Consider an e-commerce API where users can view their own orders:
http GET /api/orders?user_id=123 HTTP/1.1 Authorization: Bearer user_token_for_user_123
An AI fuzzer can intelligently test whether changing the user_id parameter allows access to other users' orders:
http GET /api/orders?user_id=456 HTTP/1.1 # Attempting to access user 456's orders Authorization: Bearer user_token_for_user_123
Similarly, AI tools excel at discovering vulnerabilities related to improper asset management, such as accessing API endpoints that should be restricted or discovering undocumented endpoints. They can learn from API responses and systematically explore the API surface to identify hidden functionality.
Rate limiting and anti-automation bypass techniques are another area where AI fuzzers demonstrate superiority. They can learn the patterns of rate limiting implementations and develop strategies to evade detection while maintaining effective testing coverage.
GraphQL-specific vulnerabilities, such as excessive data exposure, circular reference abuse, and batch query attacks, are particularly well-suited to AI fuzzing approaches. The flexible nature of GraphQL queries makes them challenging for traditional tools to test effectively, but AI fuzzers can understand schema relationships and generate complex queries designed to exploit weaknesses.
For instance, an AI fuzzer might generate deeply nested GraphQL queries to test for denial-of-service conditions:
graphql query { users { friends { friends { friends { # ... deeply nested query posts { comments { author { # Circular reference testing posts { title } } } } } } } } }
Mass assignment vulnerabilities, where attackers can set arbitrary object properties through API parameters, are another area where AI tools excel. They can learn the expected parameters for different operations and systematically test for unexpected parameters that might lead to security issues.
The key advantage of AI fuzzing tools lies in their ability to combine multiple testing strategies and adapt their approaches based on observed responses. This dynamic, intelligent testing methodology enables them to discover vulnerabilities that would be extremely difficult or time-consuming to find using traditional approaches.
Key Insight: AI fuzzing tools excel at discovering sophisticated vulnerabilities including injection attacks, authentication bypasses, business logic flaws, GraphQL-specific issues, and mass assignment vulnerabilities through their ability to understand context and generate intelligent, adaptive test cases.
How Can Organizations Integrate AI Fuzzing Into Their Security Workflows?
Integrating AI-powered API fuzzing tools into existing security workflows requires careful planning and consideration of organizational needs, infrastructure capabilities, and compliance requirements. Successful implementation involves more than simply deploying new tools; it requires a holistic approach that considers people, processes, and technology.
The first step in integration involves assessing the current API security testing maturity level. Organizations should evaluate their existing testing practices, tools, and coverage gaps to determine where AI fuzzing can provide the most value. This assessment should include an inventory of API endpoints, their criticality, and current testing frequency and depth.
Infrastructure considerations play a crucial role in successful deployment. AI fuzzing tools typically require more computational resources than traditional fuzzers, particularly during the initial learning phases. Organizations must ensure adequate processing power, memory, and storage capacity to support these tools effectively. Cloud-based deployments can provide scalability benefits, but may introduce latency and data privacy concerns that need to be addressed.
Integration with existing security toolchains is essential for maximizing the value of AI fuzzing investments. Modern security orchestration platforms can incorporate AI fuzzing results alongside findings from static analysis, dynamic analysis, and manual testing efforts. This unified approach provides comprehensive visibility into API security posture.
Consider a typical CI/CD pipeline integration where AI fuzzing tools can be incorporated:
yaml
Example CI/CD pipeline with AI fuzzing integration
stages:
- build
- test
- security-scan
- deploy
security-scan: stage: security-scan script: - # Run traditional security scans - zap-baseline.py -t $TARGET_URL
-
Run AI-powered API fuzzing
-
ai-fuzzer --target $API_SPEC_URL --output fuzz-results.json
-
Analyze and report findings
-
security-analyzer --inputs fuzz-results.json,zap-results.xml
-
Fail pipeline if critical vulnerabilities found
-
if [ $(security-analyzer --critical-count) -gt 0 ]; then exit 1; fi
-
artifacts: reports: security: security-report.json
Training and skill development represent another critical aspect of successful integration. Security teams need to understand how to configure, operate, and interpret results from AI fuzzing tools. This may involve developing new competencies in machine learning concepts, data analysis, and advanced testing methodologies.
Establishing clear policies and procedures for AI fuzzing usage helps ensure consistent and effective deployment. These policies should address testing scope, authorization requirements, data handling procedures, and incident response protocols for discovered vulnerabilities.
Continuous monitoring and improvement processes are essential for maintaining the effectiveness of AI fuzzing implementations. Regular evaluation of tool performance, adjustment of configurations based on organizational needs, and incorporation of lessons learned help optimize the security testing program over time.
Compliance and regulatory considerations must also be addressed when implementing AI fuzzing tools. Organizations operating in regulated industries need to ensure that their testing activities comply with relevant standards and that any sensitive data processed during testing is properly protected.
Risk-based prioritization strategies help organizations focus their AI fuzzing efforts on the most critical APIs and vulnerabilities. By combining threat modeling, business impact analysis, and risk assessment methodologies, organizations can develop targeted testing programs that maximize security value.
Collaboration between development and security teams becomes even more important with AI fuzzing tools. These tools can provide developers with immediate feedback on API security issues, enabling faster remediation and improved security practices.
Documentation and knowledge sharing practices ensure that insights gained from AI fuzzing activities benefit the entire organization. Capturing testing methodologies, successful approaches, and lessons learned helps build institutional knowledge and improves future testing efforts.
Performance optimization considerations include tuning AI models for specific API types, adjusting testing intensity based on application criticality, and implementing efficient result processing and analysis workflows.
The integration process should also consider feedback loops that allow AI fuzzing tools to learn from manual testing results and security incident investigations. This continuous learning approach helps improve tool effectiveness over time and ensures alignment with organizational security objectives.
Finally, measuring and communicating the value of AI fuzzing investments helps justify continued investment and supports ongoing improvement efforts. Metrics such as vulnerability discovery rates, false positive reduction, testing efficiency gains, and business impact quantification provide concrete evidence of value delivery.
Successful integration of AI fuzzing into security workflows transforms API security testing from a reactive, manual process into a proactive, automated capability that scales with organizational growth and complexity.
Key Insight: Successful integration of AI fuzzing tools requires comprehensive planning addressing infrastructure, processes, training, and collaboration to transform API security testing into an automated, scalable capability aligned with organizational objectives.
What Are the Performance Benchmarks and Real-World Effectiveness Results?
Performance benchmarks and real-world effectiveness studies provide crucial insights into the practical value of AI-powered API fuzzing tools. These evaluations typically measure multiple dimensions including vulnerability discovery rates, false positive reduction, resource utilization, and business impact metrics to provide a comprehensive picture of tool effectiveness.
Large-scale benchmarking studies conducted across diverse API ecosystems have consistently demonstrated the superior performance of AI-enhanced fuzzing tools. In a comprehensive study involving over 500 APIs across various industries, AI-powered tools discovered an average of 3.2 times more vulnerabilities than traditional fuzzers while reducing false positive rates by 78%. The study included RESTful APIs, GraphQL services, and SOAP-based interfaces to ensure broad applicability of results.
Resource utilization efficiency represents another important performance metric. While AI fuzzing tools may require more computational resources during initial learning phases, they typically achieve faster convergence to meaningful test cases and require less manual intervention. This efficiency gain translates to reduced testing time and lower operational costs over the long term.
Real-world deployment data from early adopter organizations provides additional validation of AI fuzzing effectiveness. Companies implementing these tools have reported significant improvements in their vulnerability detection capabilities, with some organizations seeing increases in critical vulnerability discovery rates of over 200% compared to their previous testing approaches.
One notable case study involved a financial services company that implemented AI fuzzing tools across their customer-facing API ecosystem. Prior to deployment, their traditional testing approach identified an average of 12 critical vulnerabilities per quarter. After implementing AI-enhanced fuzzing, they discovered an average of 38 critical vulnerabilities per quarter, representing a 217% increase in detection capability. More importantly, the quality of findings improved significantly, with fewer false positives requiring manual verification.
Performance comparisons across different tool categories reveal interesting trends. The following chart illustrates relative performance metrics for various fuzzing approaches:
Vulnerability Discovery Efficiency (Higher is Better) ┌─────────────────────────────────────────────┐ │ ●●●●●●●●●●●●●●●●●●●● │ AI-Enhanced Tools (9.2) │ ●●●●●●●●●●●●●●●●●●● │ Hybrid Approaches (7.8) │ ●●●●●●●●●●●●●●●●●● │ Traditional Fuzzers (6.1) │ ●●●●●●●●●●●●●●● │ Manual Testing (4.3) └─────────────────────────────────────────────┘ 0 10
Time-to-discovery metrics show that AI fuzzing tools typically identify critical vulnerabilities 40-60% faster than traditional approaches. This acceleration is particularly valuable for organizations with frequent release cycles or continuous deployment pipelines where rapid security feedback is essential.
False positive reduction represents one of the most significant advantages of AI-powered fuzzing. Traditional tools often generate large volumes of low-quality findings that consume analyst time and attention. AI tools, by contrast, can apply sophisticated analysis techniques to filter out obviously invalid findings and prioritize high-confidence vulnerabilities.
Coverage depth measurements demonstrate that AI fuzzing tools achieve significantly better exploration of API surfaces. In benchmark tests, these tools tested an average of 94% of available endpoints compared to 72% for traditional approaches. This increased coverage is particularly important for complex APIs with numerous interconnected endpoints and data flows.
Business impact metrics provide perhaps the most compelling evidence of AI fuzzing value. Organizations using these tools have reported reductions in security incident response times, improved compliance posture, and enhanced customer trust due to more robust security testing. Some companies have also seen measurable improvements in development velocity as security issues are identified and resolved earlier in the development lifecycle.
Scalability performance benchmarks show that AI fuzzing tools can effectively handle large, complex API ecosystems. Tests involving APIs with thousands of endpoints demonstrated that these tools maintain consistent performance levels while providing comprehensive coverage across the entire API surface.
Resource utilization efficiency varies depending on implementation approach and specific tool capabilities. Cloud-native AI fuzzing solutions typically offer better scalability and resource optimization compared to on-premises deployments, though they may introduce latency and data privacy considerations that need to be managed appropriately.
Long-term effectiveness studies indicate that AI fuzzing tools continue to improve over time as they learn from new testing experiences and adapt to evolving API landscapes. This continuous learning capability provides ongoing value that traditional tools cannot match.
Cost-benefit analyses conducted by independent research firms suggest that organizations can achieve positive return on investment within 6-12 months of AI fuzzing tool deployment, primarily through reduced manual testing effort, faster vulnerability remediation, and improved security posture.
Performance consistency across different API types and architectures demonstrates the robustness of AI approaches. Whether testing simple REST APIs, complex GraphQL services, or legacy SOAP interfaces, AI fuzzing tools maintain high effectiveness levels while adapting their strategies to match specific architectural characteristics.
These performance benchmarks and real-world results provide strong evidence that AI-powered API fuzzing represents a significant advancement in security testing technology, offering measurable improvements in effectiveness, efficiency, and business value compared to traditional approaches.
Key Insight: Comprehensive benchmarking and real-world deployment data consistently demonstrate that AI-powered API fuzzing tools deliver 2-3x better vulnerability discovery rates, 70%+ false positive reduction, and significant business impact improvements compared to traditional testing approaches.
Key Takeaways
• AI API fuzzing tools leverage transformer models and machine learning to understand API semantics, generate intelligent test cases, and detect sophisticated vulnerabilities that traditional fuzzers miss
• RESTler-AI and FuzzAPI-Net consistently outperform conventional tools with 89-92% vulnerability discovery rates compared to 65% for traditional approaches
• AI fuzzers excel at finding business logic flaws, authentication bypasses, injection vulnerabilities, and GraphQL-specific issues through contextual understanding and adaptive testing strategies
• Integration requires careful planning around infrastructure, processes, training, and collaboration to maximize security value and achieve ROI within 6-12 months
• Performance benchmarks show 3.2x more vulnerability discoveries, 78% false positive reduction, and 40-60% faster critical vulnerability identification compared to traditional methods
• Modern security workflows benefit from AI fuzzing through automated CI/CD integration, continuous learning capabilities, and scalable testing across complex API ecosystems
• Organizations can start exploring these capabilities with 10,000 free tokens on mr7.ai to experience advanced tools like KaliGPT, 0Day Coder, and mr7 Agent firsthand
Frequently Asked Questions
Q: What makes AI API fuzzing tools different from traditional fuzzers?
AI API fuzzing tools use machine learning models to understand API semantics, learn from responses, and generate contextually intelligent test cases. Unlike traditional fuzzers that rely on brute force or predefined payloads, AI tools adapt their strategies based on API behavior and can discover complex vulnerabilities like business logic flaws that traditional approaches often miss.
Q: How do transformer models improve API fuzzing effectiveness?
Transformer models excel at capturing long-range dependencies and semantic relationships in API specifications. They can understand complex parameter relationships, nested data structures, and sequential dependencies between API calls, enabling more sophisticated and targeted vulnerability testing compared to simpler machine learning approaches.
Q: Can AI fuzzing tools work with GraphQL APIs effectively?
Yes, AI fuzzing tools are particularly effective with GraphQL APIs because they can understand schema definitions, generate syntactically correct queries, and explore complex nested query structures. They excel at testing GraphQL-specific vulnerabilities like excessive data exposure, circular references, and batch query abuse that are challenging for traditional tools.
Q: What infrastructure requirements do AI fuzzing tools have?
AI fuzzing tools typically require more computational resources than traditional fuzzers, especially during learning phases. Organizations need adequate CPU, memory, and storage capacity. Cloud deployments offer scalability benefits but may introduce latency considerations. Most tools can run on standard development or testing infrastructure with proper resource allocation.
Q: How quickly can organizations see ROI from AI fuzzing implementation?
Organizations typically achieve positive ROI within 6-12 months through reduced manual testing effort, faster vulnerability remediation, and improved security posture. Early adopters report 200%+ increases in critical vulnerability discovery rates and significant reductions in false positive findings that require analyst attention.
Stop Manual Testing. Start Using AI.
mr7 Agent automates reconnaissance, exploitation, and reporting while you focus on what matters - finding critical vulnerabilities. Plus, use KaliGPT and 0Day Coder for real-time AI assistance.
Try Free Today → | Download mr7 Agent →