Vulnerability Scoring Systems: CVSS v4.0, EPSS, SSVC, and AI-Driven Prioritization
Vulnerability Scoring Systems: CVSS v4.0, EPSS, SSVC, and AI-Driven Prioritization
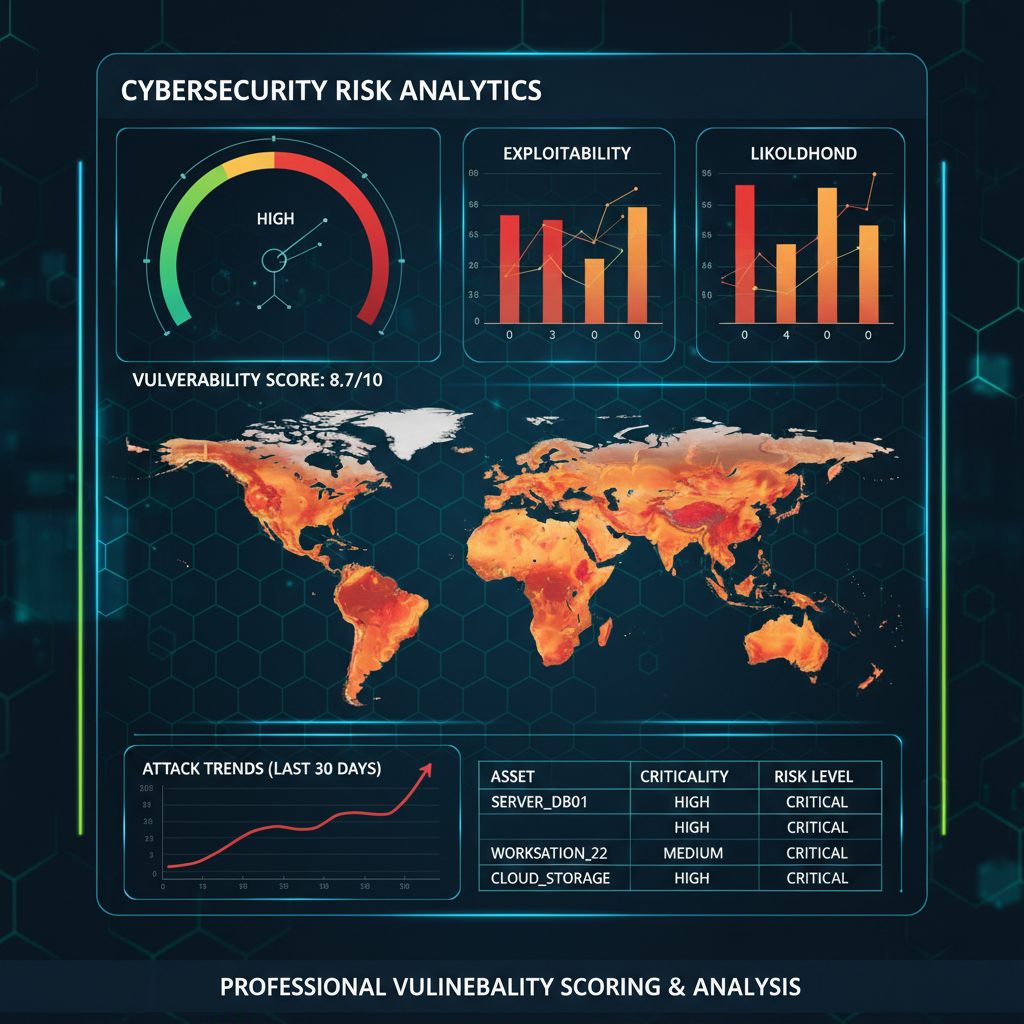
Vulnerability scoring systems are crucial for security professionals to assess and prioritize risks effectively. With the evolution of these systems, it's essential to understand the latest developments and how AI can enhance vulnerability management. This article delves into CVSS v4.0, EPSS, SSVC, risk-based vulnerability management, and the role of AI in prioritizing vulnerabilities based on actual exploitability and business impact.
Understanding CVSS v4.0
The Common Vulnerability Scoring System (CVSS) is a widely adopted framework for evaluating the severity of security vulnerabilities. CVSS v4.0, the latest iteration, introduces several enhancements to improve accuracy and relevance.
Key Features of CVSS v4.0
-
Expanded Metrics: CVSS v4.0 includes additional metrics to capture more nuanced aspects of a vulnerability, such as the impact on confidentiality, integrity, and availability.
-
Dynamic Scoring: The new version supports dynamic scoring, allowing for real-time adjustments based on evolving threat landscapes.
-
Enhanced Temporal Metrics: CVS v4.0 refines temporal metrics to better reflect the urgency and relevance of a vulnerability over time.
Example Calculation
Here's an example of how to calculate a CVSS score using the command line with a hypothetical vulnerability:
bash cvss-calculator --base-score --attack-vector=NETWORK --attack-complexity=LOW --privileges-required=NONE --user-interaction=NONE --scope=UNCHANGED --confidentiality-impact=HIGH --integrity-impact=HIGH --availability-impact=HIGH
This command would output a base score reflecting the severity of the vulnerability based on the provided parameters.
Exploring EPSS: Exploit Prediction Scoring System
The Exploit Prediction Scoring System (EPSS) is designed to predict the likelihood of a vulnerability being exploited. It provides a probabilistic score that helps security teams focus on the most critical vulnerabilities.
How EPSS Works
EPSS uses historical data and machine learning algorithms to predict the exploitability of a vulnerability. It considers factors such as:
-
CVE Details: Information about the vulnerability itself.
-
Historical Exploits: Patterns of past exploits.
-
Threat Actor Behavior: Insights into how threat actors typically operate.
Example EPSS Score
Suppose you have a CVE with an EPSS score of 0.85. This high score indicates a high likelihood of exploitation, prompting immediate attention.
SSVC: Standardized Severity Vulnerability Classification
The Standardized Severity Vulnerability Classification (SSVC) offers a more granular approach to vulnerability severity. It categorizes vulnerabilities into standardized severity levels, making it easier to prioritize remediation efforts.
SSVC Categories
SSVC typically categorizes vulnerabilities into the following levels:
-
Critical: Immediate action required.
-
High: Urgent attention needed.
-
Medium: Important but not immediate.
-
Low: Lower priority but still significant.
Comparison Table: CVSS, EPSS, and SSVC
| Feature | CVSS v4.0 | EPSS | SSVC |
|---|---|---|---|
| Primary Focus | Severity Assessment | Exploit Prediction | Severity Classification |
| Scoring Method | Base, Temporal, Environmental | Probabilistic | Categorical |
| Data Sources | Vulnerability Characteristics | Historical Data, ML Algorithms | Standardized Levels |
| Output | Numerical Score (0-10) | Probability Score (0-1) | Severity Categories |
Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
Risk-Based Vulnerability Management
Risk-based vulnerability management involves assessing vulnerabilities based on their potential impact on the organization. This approach goes beyond traditional scoring systems by considering business context and operational risk.
Steps in Risk-Based Management
-
Identify Assets: Catalog all critical assets and systems.
-
Assess Vulnerabilities: Use CVSS, EPSS, and SSVC to evaluate each vulnerability.
-
Contextualize Risk: Consider the business impact, regulatory requirements, and operational criticality.
-
Prioritize Remediation: Focus on vulnerabilities that pose the highest risk to the organization.
Example Risk Assessment
Suppose a financial institution identifies a high-severity vulnerability in its payment processing system. Despite a CVSS score of 8.5, the institution might prioritize it lower if the system is segregated and has limited external exposure. Conversely, a lower-severity vulnerability in a publicly accessible web application might be prioritized higher due to potential data breaches.
Want to try this? mr7.ai offers specialized AI models for security research. Get started with 10,000 free tokens.
Leveraging AI for Vulnerability Prioritization
AI can significantly enhance vulnerability management by providing more accurate and context-aware prioritization. Tools like mr7.ai's KaliGPT, 0Day Coder, DarkGPT, and OnionGPT offer advanced capabilities for security researchers.
AI-Driven Prioritization
-
KaliGPT: This model can analyze vast amounts of vulnerability data to identify patterns and predict which vulnerabilities are most likely to be exploited.
-
0Day Coder: Specializes in identifying zero-day vulnerabilities and providing insights into their potential impact.
-
DarkGPT: Focuses on dark web intelligence, helping to understand how vulnerabilities are being discussed and traded among threat actors.
-
OnionGPT: Provides deep web analysis, offering a comprehensive view of vulnerability discussions and potential exploits.
Example AI Analysis
Using KaliGPT, a security team can input a list of CVEs and receive a prioritized list based on actual exploitability and business impact. For instance:
bash kali-gpt --analyze-cves --input cve_list.txt --output prioritized_cves.json
This command would output a JSON file with CVEs ranked by their likelihood of exploitation and potential business impact.
Actionable Takeaways
-
CVSS v4.0 provides a comprehensive framework for evaluating vulnerability severity, but it should be used in conjunction with other systems for a holistic view.
-
EPSS offers valuable insights into the likelihood of exploitation, helping to focus remediation efforts on the most critical vulnerabilities.
-
SSVC simplifies severity classification, making it easier to communicate risk levels within an organization.
-
Risk-based vulnerability management ensures that remediation efforts are aligned with business priorities and operational risks.
-
AI tools like those offered by mr7.ai can significantly enhance vulnerability prioritization by providing context-aware and data-driven insights.
Your AI Security Assistant Awaits
From reconnaissance to exploitation to reporting - mr7.ai's AI models cover every phase of your security workflow.
Key Takeaways
- CVSS v4.0 introduces finer granularity and improved clarity for environmental metrics, moving beyond just technical severity to incorporate real-world impact.
- EPSS provides a data-driven, predictive score for the likelihood of a vulnerability being exploited in the wild, offering a crucial complement to traditional severity scores.
- SSVC offers a decision-tree model for vulnerability response, guiding organizations through a structured process to determine appropriate actions based on operational context.
- AI-driven prioritization leverages machine learning to analyze vast datasets, identify patterns, and predict which vulnerabilities pose the highest actual risk to an organization, enhancing traditional scoring methods.
- Effective vulnerability management now requires integrating multiple scoring systems and leveraging AI to move beyond static scores towards dynamic, risk-based prioritization.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: How does CVSS v4.0 improve upon previous versions for vulnerability assessment?
CVSS v4.0 enhances previous versions by providing more precise and granular metrics, particularly within environmental factors. It aims to better reflect the real-world impact and exploitability of vulnerabilities, moving beyond a purely technical severity score to include aspects like automation and recovery.
Q: What unique value does EPSS bring to vulnerability prioritization compared to CVSS?
EPSS (Exploit Prediction Scoring System) offers a predictive, data-driven score indicating the likelihood of a vulnerability being exploited in the wild, which CVSS does not directly provide. While CVSS assesses technical severity, EPSS focuses on the probability of exploitation, allowing organizations to prioritize based on actual threat intelligence.
Q: How does SSVC help organizations make better decisions about vulnerability response?
SSVC (Stakeholder-Specific Vulnerability Categorization) provides a structured decision-tree model that guides organizations through a series of questions to determine the most appropriate response action for a vulnerability. It considers operational context, impact, and exploitability, helping to move beyond a simple "patch or ignore" approach.
Q: How can AI tools help with this topic?
AI tools like mr7.ai, KaliGPT, and mr7 Agent can significantly enhance vulnerability prioritization by analyzing complex data, identifying patterns, and predicting exploitability with greater accuracy. They automate the correlation of various scoring systems and threat intelligence, allowing security teams to focus on the most critical risks efficiently.
Q: What is a good first step for an organization looking to implement these advanced scoring systems and AI prioritization?
A good first step is to assess your current vulnerability management process and identify where existing scoring systems fall short. Then, consider piloting one of the advanced systems like EPSS alongside your current CVSS usage, and explore how AI-driven platforms, such as those offered by mr7.ai (which offers free tokens), can integrate to provide a more holistic and predictive view of your risk landscape.
Stop Manual Testing. Start Using AI.
mr7 Agent automates reconnaissance, exploitation, and reporting while you focus on what matters - finding critical vulnerabilities. Plus, use KaliGPT and 0Day Coder for real-time AI assistance.


