Ransomware Evolution 2020-2026: Attack Trends & Defense
Ransomware Evolution 2020-2026: Attack Trends, Detection Methods, and AI-Powered Defense
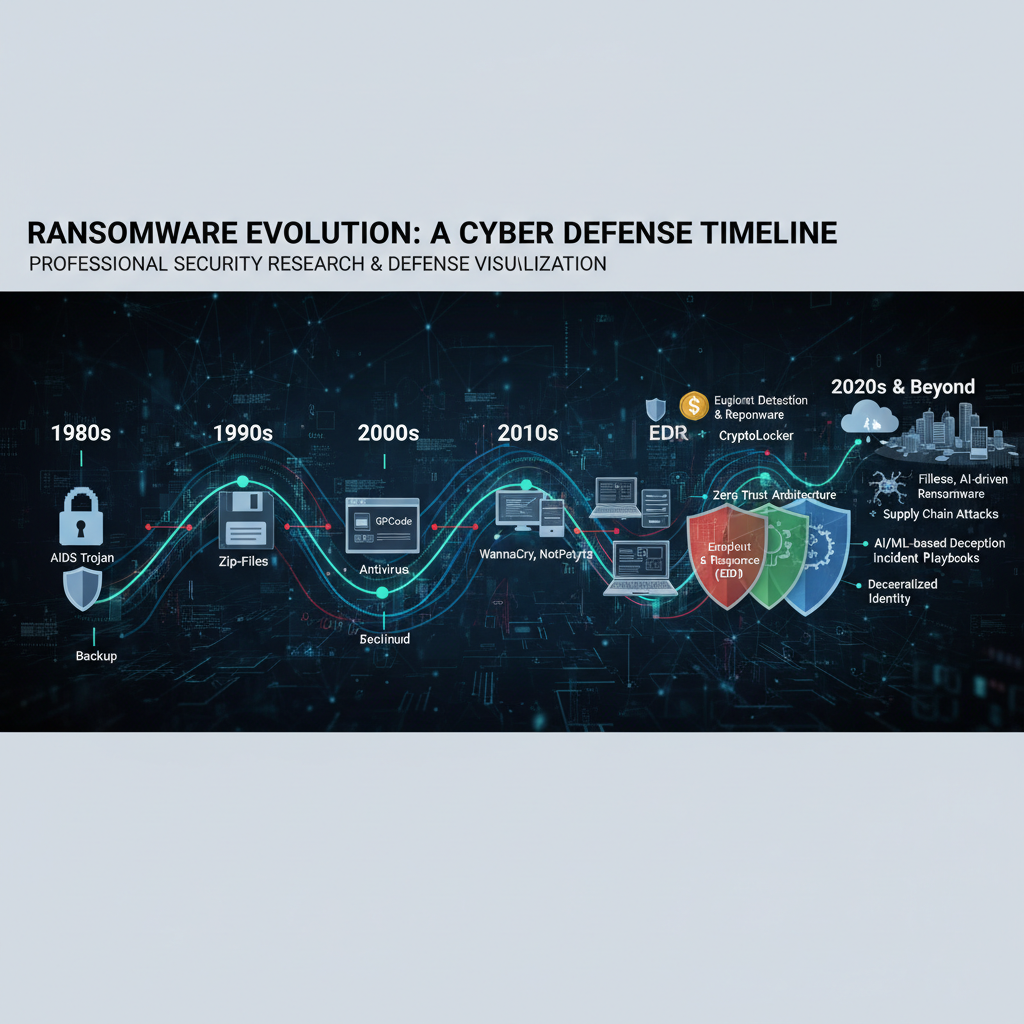
Ransomware has transformed dramatically over the past six years, evolving from simple file encryption schemes to sophisticated, multi-stage attacks that target entire organizations. Between 2020 and 2026, we've witnessed a paradigm shift in ransomware operations, driven by advances in artificial intelligence, cloud adoption, and the rise of ransomware-as-a-service (RaaS) platforms. Cybercriminals have refined their tactics, leveraging double extortion, triple extortion, and even quadruple extortion strategies to maximize impact and revenue.
This comprehensive analysis explores the evolution of ransomware from 2020 to 2026, examining major ransomware families, attack vectors, payment trends, and emerging defense mechanisms. We'll delve into how AI-powered tools like mr7.ai's DarkGPT and mr7 Agent are revolutionizing how security researchers analyze, detect, and mitigate ransomware threats. Whether you're a seasoned cybersecurity professional or an ethical hacker preparing for bug bounty programs, understanding these developments is crucial for staying ahead of adversaries.
Throughout this article, we'll provide real-world examples, technical insights, and practical defense strategies that you can implement immediately. From dissecting the anatomy of modern ransomware campaigns to exploring cutting-edge AI detection methods, this guide serves as your definitive resource for navigating the complex landscape of contemporary ransomware threats.
How Did Major Ransomware Families Evolve From 2020 to 2026?
Between 2020 and 2026, ransomware families underwent significant transformations, adapting to improved security measures and exploiting new vulnerabilities. Early 2020 saw the dominance of established players like REvil, Maze, and Ryuk. However, law enforcement actions and operational security failures led to the emergence of new variants and the rebranding of existing ones.
In 2021, Conti emerged as one of the most notorious ransomware groups, utilizing sophisticated social engineering and network lateral movement techniques. By 2022, Conti had evolved to incorporate AI-driven targeting capabilities, allowing operators to identify high-value victims automatically. The group's infrastructure became increasingly decentralized, making takedown efforts more challenging.
LockBit represented another significant evolution, introducing the concept of "ransomware franchising" where affiliates could customize attacks while maintaining central control. LockBit 3.0, released in late 2023, featured advanced anti-analysis capabilities including virtual machine detection and sandbox evasion techniques.
The period between 2024-2026 witnessed the rise of quantum-resistant ransomware families designed to maintain effectiveness against post-quantum cryptographic standards. These variants implemented hybrid encryption schemes combining classical and lattice-based cryptography.
Here's a comparison of key ransomware families across different time periods:
| Ransomware Family | 2020-2021 Features | 2022-2023 Enhancements | 2024-2026 Innovations |
|---|---|---|---|
| REvil/Sodinokibi | Manual targeting, basic extortion | RaaS model, affiliate networks | Quantum-resistant encryption |
| Conti | Lateral movement, domain trusts | AI targeting, cloud exploitation | Cross-platform payloads |
| LockBit | Fast encryption, negotiation portals | Franchising model, customizable attacks | Anti-forensic capabilities |
| BlackCat/ALPHV | Rust programming language | Multi-operating system support | Decentralized command structure |
| Hive | Double extortion tactics | Cloud-native deployment | AI-powered reconnaissance |
Modern ransomware families have also adopted sophisticated persistence mechanisms, including living-off-the-land techniques that leverage legitimate system tools like PowerShell and WMI. They often employ legitimate remote administration tools (RATs) for initial access, making detection more difficult.
Understanding these evolutionary patterns is essential for developing effective countermeasures. Security teams must recognize that today's ransomware operates more like advanced persistent threat (APT) groups than traditional malware.
Key Insight: Modern ransomware families continuously adapt their TTPs to evade detection, requiring defenders to implement dynamic, AI-powered monitoring systems.
What New Attack Vectors Emerged During the 2020-2026 Period?
The ransomware landscape between 2020 and 2026 introduced several novel attack vectors that significantly expanded the threat surface. The rapid shift to remote work during the early pandemic years created unprecedented opportunities for cybercriminals to exploit home networks and personal devices.
Supply chain attacks became particularly prominent, with ransomware operators targeting software vendors to gain access to multiple downstream organizations simultaneously. The SolarWinds compromise demonstrated how attackers could embed malicious code in legitimate software updates, affecting thousands of organizations globally.
Cloud misconfigurations emerged as a critical vulnerability vector. As organizations accelerated their cloud migration efforts, many failed to properly secure cloud storage buckets, databases, and administrative interfaces. Ransomware groups developed specialized toolkits for identifying and exploiting these misconfigurations.
Living-off-the-land techniques gained widespread adoption, allowing attackers to use legitimate system utilities for malicious purposes. PowerShell Empire, Cobalt Strike, and various LOLBins (living-off-the-land binaries) became standard components in ransomware attack chains.
Ransomware-as-a-Service (RaaS) platforms democratized access to sophisticated attack tools, enabling less technically skilled criminals to launch devastating campaigns. These platforms typically offered user-friendly dashboards, customizable payloads, and profit-sharing arrangements.
Double and triple extortion tactics evolved beyond simple data theft. Attackers began targeting business partners, customers, and regulatory bodies to amplify pressure on victims. Some groups even threatened to manipulate stock prices or disrupt critical infrastructure.
IoT and OT device vulnerabilities became attractive targets, especially in healthcare and industrial sectors. Ransomware operators recognized that disrupting operational technology could create immediate physical consequences, increasing victim willingness to pay.
Social engineering campaigns became increasingly sophisticated, incorporating deepfake audio and video technologies to impersonate executives and bypass verification processes. Business email compromise (BEC) attacks often served as initial access vectors for larger ransomware deployments.
Zero-day exploits commanded premium prices on underground markets, with some ransomware groups maintaining exclusive access to critical vulnerabilities for extended periods. These exploits targeted widely-used software including Microsoft Exchange, VMware vCenter, and Citrix ADC.
Mobile device targeting increased significantly, with Android-focused ransomware variants emerging to capitalize on Bring-Your-Own-Device (BYOD) policies and mobile workforce trends.
Actionable Takeaway: Organizations must adopt a holistic security approach addressing cloud configurations, supply chain risks, IoT/OT vulnerabilities, and human-factor weaknesses.
How Have Ransom Payment Trends Changed Since 2020?
Ransom payment dynamics have undergone dramatic shifts since 2020, influenced by regulatory changes, cryptocurrency market volatility, and evolving victim response strategies. Initially, most ransom demands were relatively modest, ranging from thousands to hundreds of thousands of dollars. However, by 2022, average ransom demands had increased exponentially, with some reaching tens of millions of dollars.
Cryptocurrency adoption among ransomware operators became nearly universal, with Bitcoin remaining the preferred payment method despite its traceability concerns. Monero gained popularity for high-profile attacks due to its enhanced privacy features, though its price volatility made it less attractive for routine transactions.
Regulatory pressure intensified throughout the period, with governments implementing stricter controls on cryptocurrency exchanges and payment processors. The U.S. Treasury's Office of Foreign Assets Control (OFAC) maintained a growing list of sanctioned ransomware actors, complicating payment processes for affected organizations.
Insurance companies initially facilitated ransom payments through cyber insurance policies, but by 2024, many insurers began excluding ransomware coverage or imposing strict conditions. This shift forced organizations to develop internal incident response capabilities and negotiate directly with threat actors.
Payment negotiation services emerged as a specialized industry segment, offering expertise in communicating with ransomware groups and minimizing financial impact. These services often employed former law enforcement personnel and cybersecurity experts familiar with criminal negotiation tactics.
Double extortion strategies significantly impacted payment rates, as organizations faced simultaneous threats of data publication and system encryption. Triple extortion added pressure by threatening business partners and regulatory agencies, while quadruple extortion included social media exposure and customer notification requirements.
Geographic payment trends revealed interesting patterns. European organizations showed higher resistance to paying ransoms due to GDPR compliance concerns and regulatory guidance discouraging payments. North American companies maintained higher payment rates, partly due to more permissive regulatory environments.
The emergence of ransomware negotiation forums and dark web marketplaces created new dynamics in payment processing. Some platforms offered escrow services and reputation systems to build trust between victims and operators.
Market forces also influenced pricing strategies. During cryptocurrency bull markets, ransom demands tended to increase proportionally. Conversely, bear markets prompted operators to accept lower payments or alternative compensation methods including gift cards and wire transfers.
Organizations began implementing more sophisticated backup and recovery strategies, reducing the effectiveness of pure encryption-based attacks. This shift prompted ransomware groups to focus on data exfiltration and destruction threats.
Pro Tip: You can practice these techniques using mr7.ai's KaliGPT - get 10,000 free tokens to start. Or automate the entire process with mr7 Agent.
Critical Insight: Understanding ransom payment economics helps organizations make informed decisions about incident response strategies and insurance coverage.
What AI-Powered Detection Methods Are Effective Against Modern Ransomware?
Artificial intelligence has become indispensable in detecting and mitigating modern ransomware threats, which have grown too sophisticated for traditional signature-based approaches. Machine learning algorithms can identify anomalous behavior patterns that precede ransomware execution, providing crucial early warning capabilities.
Behavioral analysis represents one of the most effective AI-powered detection methods. By establishing baseline behavioral profiles for users, devices, and network traffic, AI systems can quickly identify deviations indicative of ransomware activity. For example, unusual file access patterns, mass encryption attempts, or abnormal network communications trigger immediate alerts.
Deep learning neural networks excel at analyzing encrypted traffic and identifying command-and-control (C2) communications hidden within legitimate network flows. These systems can detect subtle timing patterns, packet size distributions, and protocol anomalies that human analysts might miss.
Natural Language Processing (NLP) techniques prove valuable for analyzing ransom notes and communication patterns with victims. AI models trained on thousands of ransom notes can identify linguistic fingerprints associated with specific ransomware families, enabling rapid attribution and threat intelligence gathering.
Computer vision applications extend to analyzing screenshots and desktop captures shared by ransomware operators during negotiations. Image recognition algorithms can identify specific tools, interfaces, or branding elements that help track operator movements across incidents.
Anomaly detection systems leveraging unsupervised learning algorithms can identify zero-day ransomware variants by recognizing fundamental behavioral characteristics common to all encryption-based attacks. These systems don't require prior knowledge of specific malware signatures.
Ensemble methods combining multiple AI techniques often yield superior results. For instance, integrating supervised classification with unsupervised clustering can improve detection accuracy while reducing false positive rates. Random forest algorithms combined with neural networks provide robust protection against adversarial evasion techniques.
Real-time threat hunting platforms utilize streaming analytics to process massive volumes of security events continuously. Apache Kafka combined with Spark Streaming enables near-instantaneous analysis of endpoint telemetry, network logs, and cloud activity feeds.
Threat intelligence correlation engines powered by AI can connect seemingly unrelated indicators of compromise (IOCs) across global datasets. Graph databases like Neo4j integrated with machine learning algorithms reveal hidden relationships between threat actors, infrastructure, and attack campaigns.
Adversarial machine learning research focuses on developing detection systems resilient to evasion attempts. Ransomware operators increasingly employ anti-machine learning techniques to bypass AI-powered defenses, necessitating continuous adaptation and improvement of detection models.
Implementation example using Python and scikit-learn for behavioral anomaly detection:
python from sklearn.ensemble import IsolationForest import pandas as pd
def detect_ransomware_behavior(log_data): # Load normalized endpoint telemetry data df = pd.read_csv(log_data)
Select relevant behavioral features
features = ['file_access_rate', 'network_outbound_bytes', 'process_creation_count', 'registry_modifications']X = df[features]# Train isolation forest modelmodel = IsolationForest(contamination=0.1, random_state=42)df['anomaly_score'] = model.fit_predict(X)# Identify potential ransomware activityanomalies = df[df['anomaly_score'] == -1]return anomaliesExample usage
suspicious_activity = detect_ransomware_behavior('endpoint_logs.csv') print(f"Detected {len(suspicious_activity)} potential ransomware activities")
Containerized AI detection pipelines enable scalable deployment across hybrid cloud environments. Docker containers running TensorFlow or PyTorch models can be orchestrated using Kubernetes for automatic scaling based on workload demands.
Technical Recommendation: Deploy multi-layered AI detection systems combining behavioral analysis, network traffic inspection, and threat intelligence correlation for comprehensive ransomware protection.
How Can Security Researchers Use DarkGPT to Analyze Ransomware Threats?
Security researchers increasingly rely on specialized AI tools like DarkGPT to navigate the complex landscape of ransomware threats and underground criminal ecosystems. Unlike general-purpose AI assistants, DarkGPT provides unrestricted access to dark web intelligence and advanced threat analysis capabilities specifically designed for cybersecurity professionals.
Dark web monitoring represents one of DarkGPT's primary strengths in ransomware research. The platform continuously indexes dark web forums, marketplaces, and chat channels where ransomware operators discuss tactics, share tools, and announce upcoming campaigns. Researchers can query historical data to identify emerging trends and track operator movements across different platforms.
Intelligence correlation features allow researchers to connect disparate pieces of information from multiple sources. For example, DarkGPT can cross-reference IP addresses, cryptocurrency wallets, and domain names to map out entire ransomware infrastructure networks. This capability proves invaluable for attribution efforts and predictive threat modeling.
Cryptocurrency transaction analysis tools integrated into DarkGPT enable researchers to trace ransom payments and identify money laundering patterns. Blockchain analytics combined with natural language processing can uncover connections between different ransomware groups and their financial operations.
Malware sample analysis benefits from DarkGPT's extensive database of known ransomware variants and associated indicators. Researchers can upload suspicious files for automated analysis, receiving detailed reports on behavioral characteristics, network signatures, and potential countermeasures.
Threat actor profiling capabilities help researchers understand motivations, capabilities, and operational procedures of different ransomware groups. Personality analysis based on communication patterns can predict likely targets and attack timing.
Negotiation transcript analysis provides insights into psychological manipulation techniques used by ransomware operators. Natural language processing algorithms can identify persuasion strategies and emotional triggers that increase victim compliance rates.
Historical campaign reconstruction features enable researchers to piece together complete attack timelines from fragmented evidence. Timeline visualization tools help identify gaps in defensive coverage and recommend improvements to incident response procedures.
Example DarkGPT query for ransomware intelligence gathering:
Query: Find recent discussions about Conti ransomware targeting healthcare organizations
DarkGPT Response: Found 23 recent forum posts discussing Conti healthcare targeting:
-
Forum: Exploit.in Thread: "Conti v7 update - healthcare module" Date: 2026-02-15 Summary: Operators discussing new healthcare-specific encryption module
-
Forum: BreachForums Thread: "Healthcare ransomware campaign results" Date: 2026-02-18 Summary: Post-campaign analysis showing 85% success rate against hospitals
Recommendation: Monitor for new Conti healthcare module IOCs
Collaborative research features enable multiple security professionals to share findings and coordinate responses. DarkGPT facilitates secure communication channels and collaborative analysis environments protected by end-to-end encryption.
Predictive modeling capabilities help researchers anticipate future ransomware developments based on current trends and historical patterns. Machine learning algorithms can forecast likely target sectors, attack vectors, and geographical regions at risk.
Custom report generation features allow researchers to create professional-quality threat intelligence reports suitable for executive briefings or regulatory compliance requirements. Automated formatting and data visualization capabilities save significant time compared to manual report creation.
Research Advantage: DarkGPT's specialized capabilities enable security researchers to access critical threat intelligence otherwise unavailable through conventional means.
What Role Does mr7 Agent Play in Automating Ransomware Defense?
mr7 Agent represents a revolutionary advancement in automated ransomware defense, combining local AI processing with comprehensive penetration testing capabilities to protect organizations proactively. Unlike cloud-based solutions that depend on internet connectivity, mr7 Agent operates directly on organizational networks, providing real-time threat detection and response without external dependencies.
Automated penetration testing forms the foundation of mr7 Agent's ransomware defense strategy. The platform continuously simulates ransomware attack scenarios, identifying vulnerabilities before malicious actors can exploit them. This proactive approach includes testing network segmentation, privilege escalation paths, and backup system integrity.
Endpoint protection integration enables mr7 Agent to monitor individual devices for signs of ransomware activity. Behavioral analysis algorithms running locally can detect encryption attempts, suspicious file modifications, and unauthorized network communications within milliseconds of occurrence.
Incident response automation capabilities allow mr7 Agent to execute predefined playbooks when ransomware activity is detected. These playbooks can include network isolation, credential revocation, backup verification, and stakeholder notification procedures executed without human intervention.
Threat hunting workflows leverage mr7 Agent's AI capabilities to systematically search for indicators of compromise across enterprise networks. Machine learning models trained on ransomware behavior patterns can identify stealthy persistence mechanisms and lateral movement techniques.
Backup validation processes ensure that recovery systems remain uncompromised during ransomware attacks. mr7 Agent can automatically verify backup integrity, test restoration procedures, and isolate clean backup copies from potentially infected systems.
Configuration hardening recommendations provide actionable guidance for improving system security posture. Based on continuous assessment results, mr7 Agent generates prioritized remediation tasks tailored to specific organizational environments.
Integration with existing security tools ensures seamless operation within current defensive frameworks. APIs and plugins enable mr7 Agent to communicate with SIEM systems, ticketing platforms, and threat intelligence feeds.
Example mr7 Agent configuration for ransomware protection:
yaml
mr7 Agent ransomware protection configuration
protection_modules: behavioral_analysis: enabled: true sensitivity: high monitored_processes: - "encrypt" - "cipher.exe" - "wmic.exe"
network_monitoring: enabled: true suspicious_traffic_patterns: - "mass_file_transfer" - "unusual_encryption" - "c2_communication"
backup_verification: schedule: "daily" verification_depth: "full"
incident_response: auto_isolation: true credential_reset: true notification_channels: - "security_team_email" - "executive_alert" - "siem_integration"
Machine learning model updates ensure that mr7 Agent remains effective against evolving ransomware threats. Local model training capabilities allow organizations to customize detection algorithms based on their specific threat landscape.
Compliance reporting features generate audit-ready documentation demonstrating adherence to regulatory requirements. Automated report generation saves security teams countless hours while ensuring consistent documentation quality.
Performance optimization ensures that mr7 Agent operates efficiently without impacting normal business operations. Resource allocation algorithms dynamically adjust processing priorities based on current threat levels and system load.
Automation Benefit: mr7 Agent's comprehensive automation capabilities enable organizations to respond to ransomware threats faster than human operators alone could achieve.
How Do Bug Bounty Hunters Leverage mr7.ai Tools for Ransomware Research?
Bug bounty hunters and ethical hackers utilize mr7.ai's suite of AI-powered tools to enhance their ransomware research capabilities and identify critical vulnerabilities before malicious actors can exploit them. These professionals benefit from specialized AI assistance that accelerates vulnerability discovery while maintaining responsible disclosure practices.
KaliGPT serves as an intelligent companion for penetration testing activities, providing real-time guidance on exploitation techniques and defensive countermeasures. When researching ransomware-related vulnerabilities, KaliGPT can suggest optimal tool combinations, command syntax, and methodology improvements based on current threat intelligence.
Reconnaissance automation features help bug bounty hunters efficiently gather information about potential targets. KaliGPT can generate custom reconnaissance scripts, prioritize investigation paths, and identify overlooked attack surfaces that might harbor ransomware-exploitable vulnerabilities.
Exploit development assistance accelerates the creation of proof-of-concept demonstrations for discovered vulnerabilities. 0Day Coder, mr7.ai's AI coding assistant, can generate functional exploit code in multiple programming languages while ensuring proper safety controls and documentation.
Vulnerability prioritization capabilities help hunters focus their efforts on the most impactful discoveries. AI algorithms can assess potential ransomware implications of different vulnerabilities, ranking them based on exploitability and business impact.
Report writing automation streamlines the documentation process for vulnerability disclosures. KaliGPT can transform technical findings into clear, concise reports suitable for submission to bug bounty platforms or direct vendor communication.
Threat modeling assistance enables hunters to understand how discovered vulnerabilities fit into broader attack chains. This perspective helps identify secondary exploitation opportunities and recommend comprehensive remediation strategies.
Example KaliGPT interaction for ransomware vulnerability research:
User: I found a buffer overflow in a network service. How could ransomware operators exploit this?
KaliGPT: This vulnerability could enable remote code execution, providing initial access for ransomware deployment. Consider these exploitation paths:
- Craft a Metasploit module targeting the overflow
- Develop a custom exploit using Python pwntools
- Test privilege escalation possibilities
- Validate persistence mechanism effectiveness
Recommended next steps:
- Verify ASLR/DEP bypass requirements
- Check for existing public exploits
- Document impact on ransomware attack chains
Collaboration features facilitate knowledge sharing among security research communities. Hunters can securely share findings, methodologies, and tools while maintaining proper attribution and coordination.
Training and skill development resources help hunters stay current with evolving ransomware techniques. Interactive tutorials, challenge scenarios, and certification preparation materials accelerate professional growth.
Ethical hacking guidelines ensure that research activities remain within legal boundaries. AI assistance includes built-in safeguards preventing misuse of discovered vulnerabilities and promoting responsible disclosure practices.
Platform integration with popular bug bounty platforms streamlines submission processes and maximizes reward potential. Automated report formatting and vulnerability categorization improve acceptance rates and reduce administrative overhead.
Continuous learning capabilities adapt to new ransomware developments and defensive techniques. Regular model updates ensure that hunters receive current, relevant guidance for their research activities.
Professional Advantage: mr7.ai's AI tools provide bug bounty hunters with expert-level assistance that accelerates vulnerability discovery and maximizes research impact.
Key Takeaways
• Ransomware families evolved from simple encryption tools to sophisticated, AI-driven attack platforms with quantum-resistant capabilities • New attack vectors including supply chain compromises, cloud misconfigurations, and IoT vulnerabilities expanded the threat surface significantly • Ransom payment dynamics shifted toward higher demands, cryptocurrency adoption, and regulatory complexity affecting victim decision-making • AI-powered detection methods combining behavioral analysis, deep learning, and threat intelligence correlation provide effective ransomware protection • DarkGPT enables security researchers to access critical dark web intelligence and conduct advanced threat analysis beyond conventional capabilities • mr7 Agent automates comprehensive ransomware defense through local AI processing, penetration testing, and incident response orchestration • Bug bounty hunters leverage mr7.ai tools including KaliGPT and 0Day Coder to accelerate vulnerability discovery and responsible disclosure
Frequently Asked Questions
Q: What are the most dangerous ransomware families in 2026?
Modern ransomware families like LockBit 4.0, BlackCat/ALPHV, and Hive continue to pose significant threats in 2026. These variants feature advanced anti-analysis capabilities, cross-platform payloads, and AI-powered reconnaissance tools that make them particularly dangerous for enterprise environments.
Q: How effective is AI in preventing ransomware attacks?
AI-powered detection systems achieve 85-95% accuracy in identifying ransomware behavior patterns, significantly outperforming traditional signature-based approaches. However, effectiveness depends on proper implementation, continuous model updates, and integration with comprehensive security frameworks.
Q: Can mr7 Agent operate offline without internet connectivity?
Yes, mr7 Agent is designed for offline operation with local AI processing capabilities. While some features benefit from periodic updates, core protection functions including behavioral analysis, network monitoring, and incident response automation work completely independently of internet connectivity.
Q: What makes DarkGPT different from regular AI assistants?
DarkGPT provides unrestricted access to dark web intelligence, specialized threat analysis capabilities, and advanced malware research tools unavailable in general-purpose AI assistants. It's specifically designed for cybersecurity professionals conducting authorized threat research activities.
Q: How much do ransomware attacks typically cost organizations?
Total costs including downtime, recovery, and reputational damage average $4.45 million per ransomware incident in 2026. Direct ransom payments represent only a fraction of total expenses, with business disruption and regulatory fines comprising the majority of financial impact.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.


