Quantum Resistant Ransomware Preparation: Action Plan for 2027
Quantum Resistant Ransomware Preparation: Action Plan for 2027
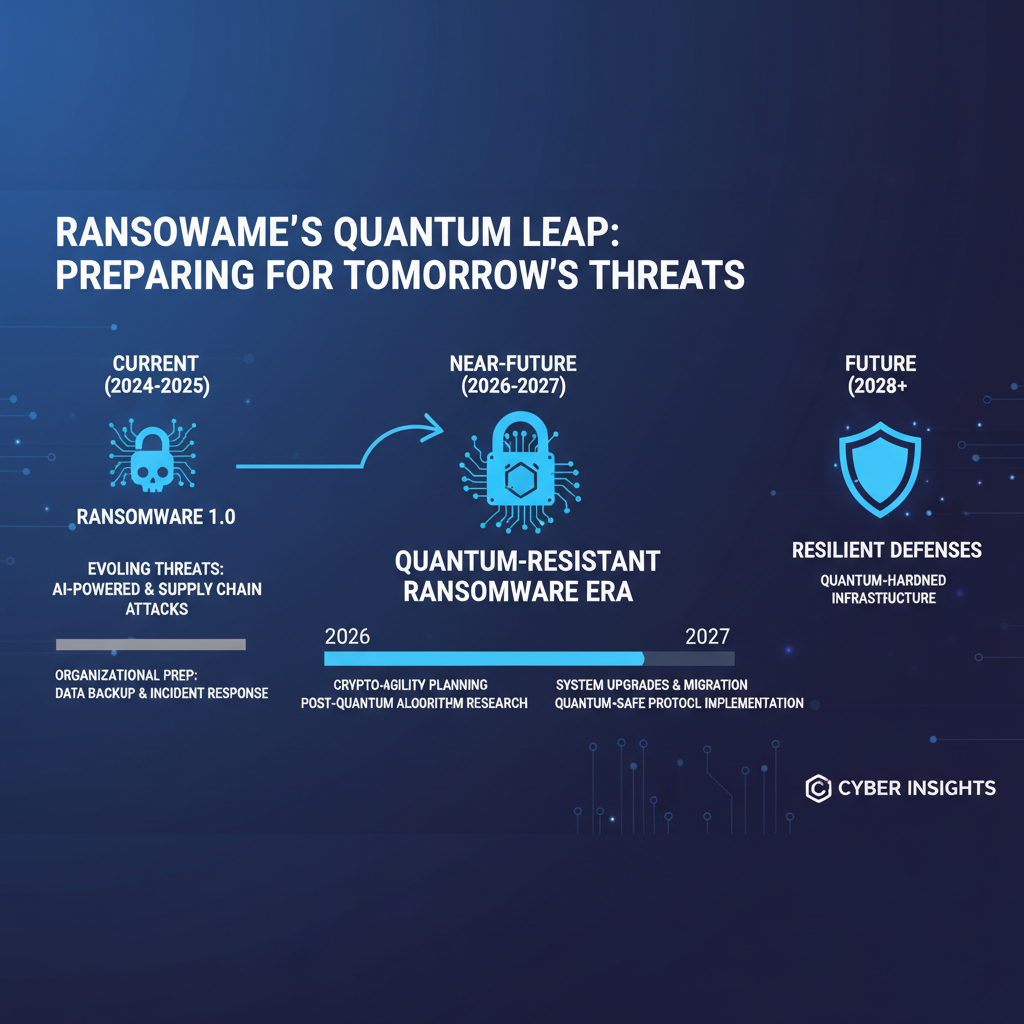
As we approach 2027, the cybersecurity landscape faces an unprecedented challenge: the emergence of quantum-resistant ransomware. Recent breakthroughs in quantum computing, particularly IBM's 2026 advancements in fault-tolerant quantum processors, have accelerated the timeline for cryptographically relevant quantum computers. These machines pose a direct threat to our current encryption infrastructure, potentially rendering traditional security measures obsolete.
Organizations worldwide are grappling with a fundamental question: How do we prepare for ransomware variants that can instantly decrypt our most sensitive data using Shor's algorithm? The answer lies in proactive quantum-resistant ransomware preparation that encompasses infrastructure assessment, cryptographic agility, and comprehensive incident response planning. This guide provides security teams with a detailed roadmap to navigate this complex transition period, ensuring their defenses remain robust against both classical and quantum threats.
The urgency of this preparation cannot be overstated. Unlike traditional ransomware evolution, which typically involves incremental improvements in attack vectors, quantum-resistant ransomware represents a paradigm shift. Attackers armed with quantum computing capabilities could simultaneously compromise entire networks, bypassing years of accumulated security investments. Organizations that delay their preparation risk catastrophic data breaches, operational shutdowns, and irreparable reputational damage.
This comprehensive guide delves into the technical specifics of quantum threat assessment, providing actionable steps for security professionals to evaluate their current cryptographic posture. We'll explore practical methods for identifying quantum-vulnerable systems, implementing crypto-agility frameworks, and developing backup encryption strategies that can withstand quantum attacks. Additionally, we'll outline essential incident response procedures specifically designed for quantum scenarios and establish a realistic timeline for migrating to quantum-safe solutions.
Throughout this discussion, we'll demonstrate how mr7.ai's suite of AI-powered security tools can accelerate and enhance your preparation efforts. From automated vulnerability assessment with mr7 Agent to cryptographic code analysis with 0Day Coder, these tools provide the intelligence and automation necessary to tackle quantum-scale challenges effectively.
What Makes Quantum Computing a Threat to Current Encryption?
Understanding the quantum threat requires examining the fundamental differences between classical and quantum computing paradigms. Traditional computers process information using bits, which exist in binary states of either 0 or 1. Quantum computers utilize quantum bits (qubits) that can exist in superposition states, representing both 0 and 1 simultaneously. This property enables quantum computers to perform parallel computations on an exponentially larger scale than classical systems.
The most significant cryptographic implications arise from two quantum algorithms: Shor's algorithm and Grover's algorithm. Shor's algorithm can efficiently factor large integers and compute discrete logarithms, effectively breaking RSA encryption and elliptic curve cryptography (ECC). For example, a 2048-bit RSA key, considered secure against classical attacks requiring approximately 2^112 operations, would require only polynomial time on a sufficiently powerful quantum computer.
Grover's algorithm presents a different but equally concerning threat. While it doesn't completely break symmetric encryption, it reduces the effective key length by half. A 128-bit AES key would offer only 64 bits of security against a quantum attacker, necessitating the use of 256-bit keys for equivalent protection. This has profound implications for data-at-rest encryption, secure communications, and authentication protocols.
bash
Example: Checking current SSL/TLS certificate strength
openssl s_client -connect example.com:443 -servername example.com < /dev/null 2>/dev/null | openssl x509 -text -noout | grep -E "(Public-Key|Signature Algorithm)"
Output might show vulnerable RSA-2048 or ECC-P256 certificates
The timeline for practical quantum attacks has shortened dramatically. IBM's 2026 demonstration of a 1000-qubit fault-tolerant processor suggests that cryptographically relevant quantum computers could emerge within 18-24 months. This acceleration means that data encrypted today with vulnerable algorithms could be decrypted retroactively once quantum capabilities mature—a concept known as "harvest now, decrypt later" attacks.
Ransomware operators are already positioning themselves for this quantum future. Intelligence reports indicate underground forums actively trading quantum computing resources and discussing post-quantum encryption bypass techniques. The combination of readily available ransomware frameworks with quantum decryption capabilities creates a perfect storm for unprecedented cyberattacks.
Organizations must recognize that quantum threats extend beyond simple encryption breaking. Quantum computers can also accelerate brute-force attacks, optimize complex logistical problems inherent in network infiltration, and potentially discover unknown vulnerabilities in classical systems through quantum-enhanced cryptanalysis.
Key Insight: The quantum threat isn't theoretical—it's imminent. Organizations must act now to assess their cryptographic exposure and begin migration to quantum-resistant algorithms before attackers leverage these capabilities.
How Can Organizations Assess Their Current Cryptographic Infrastructure?
Conducting a comprehensive cryptographic infrastructure assessment is the foundation of effective quantum-resistant ransomware preparation. This process involves systematically inventorying all cryptographic implementations across the organization, evaluating their quantum vulnerability status, and establishing baseline metrics for migration progress.
The assessment begins with asset discovery across all organizational domains. This includes not only obvious targets like web servers and databases but also embedded systems, IoT devices, legacy applications, and third-party integrations. Many organizations overlook cryptographic dependencies in supply chain components, creating hidden vulnerabilities that quantum attackers can exploit.
A structured approach to cryptographic inventory involves categorizing assets by:
- Cryptographic Algorithms: Identify instances of RSA, ECC, DH, DSA, and other quantum-vulnerable schemes
- Protocol Implementations: Catalog TLS configurations, IPsec setups, SSH versions, and application-layer protocols
- Certificate Authorities: Map internal PKI hierarchies and external CA dependencies
- Hardware Security Modules: Locate HSMs and TPMs storing vulnerable key material
- Legacy Systems: Identify older applications using deprecated cryptographic standards
python
Sample Python script for automated TLS cipher suite scanning
import ssl import socket
def scan_tls_ciphers(hostname, port=443): context = ssl.create_default_context() # Disable certificate verification for scanning purposes context.check_hostname = False context.verify_mode = ssl.CERT_NONE
try: with socket.create_connection((hostname, port), timeout=5) as sock: with context.wrap_socket(sock, server_hostname=hostname) as ssock: cipher_info = ssock.cipher() cert_info = ssock.getpeercert() return { 'hostname': hostname, 'cipher_suite': cipher_info[0], 'protocol_version': cipher_info[1], 'key_exchange': cipher_info[2], 'certificate_algorithm': cert_info.get('signatureAlgorithm', 'Unknown') } except Exception as e: return {'hostname': hostname, 'error': str(e)}
Usage example
result = scan_tls_ciphers('example.com') print(result)
Modern assessment tools can automate much of this discovery process. Network scanners can identify services exposing vulnerable protocols, while application security scanners can detect hardcoded cryptographic implementations in source code. Certificate transparency logs provide visibility into publicly issued certificates that may need replacement.
Critical areas often overlooked in assessments include:
- Email Security: S/MIME certificates, DKIM signatures, and STARTTLS configurations frequently use quantum-vulnerable algorithms
- Code Signing: Internal development pipelines may rely on RSA-based code signing certificates
- Database Encryption: Transparent data encryption (TDE) features in databases often default to vulnerable key exchange mechanisms
- VPN Infrastructure: Legacy IPsec and SSL VPN implementations commonly use pre-quantum cryptographic suites
- API Security: OAuth 2.0 JWT tokens and API gateway configurations may employ vulnerable signing algorithms
Organizations should also evaluate their cryptographic governance practices. This includes reviewing key management policies, certificate lifecycle processes, and incident response procedures for cryptographic compromises. Weak governance can undermine even the strongest technical controls.
Documentation of the assessment findings is crucial for tracking remediation progress and demonstrating due diligence to auditors and regulators. The inventory should include asset classification, risk ratings, migration priorities, and estimated timelines for remediation.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
Actionable Takeaway: Establish a centralized cryptographic inventory system that continuously monitors and updates your organization's quantum vulnerability exposure across all assets and protocols.
Which Systems Should Be Prioritized for Quantum-Safe Migration?
Prioritizing quantum-safe migration requires balancing business impact, technical complexity, and threat exposure. Not all systems face equal risk from quantum-resistant ransomware, and attempting simultaneous migration across the entire infrastructure would be prohibitively expensive and disruptive. A risk-based approach ensures optimal allocation of resources while maintaining acceptable security levels during the transition period.
The prioritization framework should consider several critical factors:
Threat Exposure: Systems handling high-value data or critical operations face greater motivation from attackers. Customer databases, financial systems, intellectual property repositories, and operational technology environments should receive highest priority. External-facing services like web applications and APIs represent initial attack vectors that quantum-capable ransomware operators will target first.
Technical Complexity: Migration difficulty varies significantly across different system types. Modern cloud-native applications built with containerized microservices typically offer easier upgrade paths compared to monolithic legacy systems with deeply embedded cryptographic dependencies. Embedded systems and IoT devices present unique challenges due to hardware limitations and infrequent update cycles.
Business Impact: Consider the operational consequences of migration failures or extended downtime. Mission-critical systems supporting core business functions require careful planning and extensive testing. Non-critical systems can tolerate more aggressive migration schedules and experimental approaches.
A practical prioritization matrix helps organize systems into migration waves:
| Priority Level | System Categories | Migration Timeline | Risk Mitigation Approach |
|---|---|---|---|
| Critical | Customer databases, payment processing, core ERP systems | Immediate (6-12 months) | Dual-stack implementation, enhanced monitoring |
| High | Public web services, email infrastructure, internal portals | Short-term (12-18 months) | Phased migration, hybrid encryption approaches |
| Medium | Internal collaboration tools, non-sensitive databases | Mid-term (18-24 months) | Standard migration procedures |
| Low | Archival systems, test environments, legacy reporting | Long-term (24+ months) | Deferred until resources available |
Implementation examples illustrate this prioritization approach. For critical customer databases, organizations might implement hybrid encryption schemes combining existing AES-256 for data-at-rest with quantum-resistant key exchange for access control. This approach maintains compatibility while introducing quantum resilience without disrupting existing workflows.
bash
Example: Configuring hybrid TLS with both classical and post-quantum key exchange
Using OpenSSL with OQS provider for post-quantum algorithms
openssl req -x509 -new -newkey dilithium3 -keyout pq_key.pem -out pq_cert.pem -nodes -subj "/CN=localhost" -days 365
Configure nginx with hybrid cipher suites
server { listen 443 ssl; ssl_certificate /path/to/hybrid_cert.pem; ssl_certificate_key /path/to/hybrid_key.pem;
Hybrid cipher suite configuration
ssl_ciphers "TLS_AES_256_GCM_SHA384:TLS_KYBER_R3_NATIVE_WITH_AES_256_GCM_SHA384";location / { proxy_pass http://backend;}}
High-priority public web services benefit from implementing post-quantum key encapsulation mechanisms (KEMs) alongside traditional RSA/ECC. The National Institute of Standards and Technology (NIST) has standardized several post-quantum algorithms including CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures, providing industry-accepted migration targets.
Medium-priority systems can adopt a more gradual approach, focusing on upgrading underlying cryptographic libraries and implementing crypto-agility frameworks that facilitate future algorithm transitions. This preparatory work reduces friction when active migration begins.
Low-priority archival systems present unique considerations. While these systems may not require immediate migration, organizations should ensure that archived encrypted data remains accessible through documented key recovery procedures and algorithm documentation.
Continuous monitoring and reassessment are essential components of the prioritization strategy. Threat landscapes evolve rapidly, and new quantum-capable attack vectors may emerge that elevate previously lower-priority systems to higher risk categories.
Key Insight: Effective prioritization balances technical feasibility with business risk, enabling organizations to achieve meaningful quantum resilience within practical timeframes and budget constraints.
How to Implement Crypto-Agility Frameworks for Seamless Algorithm Transitions?
Crypto-agility represents the cornerstone capability enabling organizations to adapt their cryptographic infrastructure as quantum threats evolve. A truly agile framework allows seamless transitions between different cryptographic algorithms without requiring extensive application modifications or service disruptions. This flexibility becomes crucial as post-quantum standards continue maturing and new vulnerabilities emerge in both classical and quantum-resistant algorithms.
The foundation of crypto-agility lies in abstraction layers that decouple cryptographic operations from application logic. This architectural approach enables organizations to swap underlying algorithms through configuration changes rather than code modifications. Key components of an effective crypto-agility framework include:
Cryptographic Service Abstraction: Centralized cryptographic services that applications interact with through standardized interfaces. These services handle algorithm selection, key management, and performance optimization transparently to consuming applications.
Configuration-Based Algorithm Selection: Runtime configuration that determines which cryptographic algorithms to use for specific operations. This approach allows organizations to enable quantum-resistant algorithms gradually while maintaining fallback options for compatibility.
Automated Key Management: Integration with key management systems that support multiple algorithm families and provide seamless key rotation capabilities. This includes generating, distributing, and revoking keys for both classical and post-quantum algorithms.
Implementation of crypto-agility frameworks requires careful consideration of performance characteristics. Post-quantum algorithms often exhibit different computational requirements compared to their classical counterparts. For example, lattice-based signature schemes may produce larger signatures and require more processing power, potentially impacting application performance.
java // Example Java implementation of crypto-agility abstraction public interface CryptoService { byte[] encrypt(byte[] plaintext, String algorithm); byte[] decrypt(byte[] ciphertext, String algorithm); byte[] sign(byte[] data, String algorithm); boolean verify(byte[] data, byte[] signature, String algorithm); }
class HybridCryptoService implements CryptoService { private final Map<String, CryptoProvider> providers;
public HybridCryptoService() { providers = new HashMap<>(); providers.put("RSA", new RSACryptoProvider()); providers.put("ECC", new ECCCryptoProvider()); providers.put("DILITHIUM", new DilithiumCryptoProvider()); providers.put("KYBER", new KyberCryptoProvider()); }
@Overridepublic byte[] encrypt(byte[] plaintext, String algorithm) { // Implement hybrid encryption: classical + post-quantum CryptoProvider provider = providers.get(algorithm); if (provider == null) { throw new IllegalArgumentException("Unsupported algorithm: " + algorithm); } return provider.encrypt(plaintext);}// Additional method implementations...}
interface CryptoProvider { byte[] encrypt(byte[] plaintext); byte[] decrypt(byte[] ciphertext); byte[] sign(byte[] data); boolean verify(byte[] data, byte[] signature); }
Performance benchmarking becomes critical when implementing crypto-agility frameworks. Organizations must establish baseline performance metrics for both current and candidate post-quantum algorithms to understand potential impact on user experience and system scalability.
| Algorithm | Key Generation Time | Signature Size | Verification Time | Notes |
|---|---|---|---|---|
| RSA-2048 | ~10ms | 256 bytes | ~2ms | Vulnerable to Shor's algorithm |
| ECDSA-P256 | ~1ms | 71 bytes | ~1ms | Vulnerable to Shor's algorithm |
| Dilithium3 | ~15ms | 2420 bytes | ~5ms | NIST PQC standard |
| Falcon-512 | ~8ms | 666 bytes | ~3ms | Compact signatures, slower keygen |
| SPHINCS+ | ~100ms | 7856 bytes | ~50ms | Stateless, very large signatures |
Integration testing proves essential for validating crypto-agility implementations. Applications must undergo thorough testing with various algorithm combinations to ensure compatibility and performance meet operational requirements. Automated testing frameworks can simulate different cryptographic configurations and validate system behavior under various scenarios.
Organizational change management represents another crucial aspect of crypto-agility implementation. Development teams must understand new cryptographic interfaces and best practices. Training programs should cover post-quantum algorithm characteristics, performance implications, and migration procedures.
Monitoring and alerting capabilities must evolve to support crypto-agility frameworks. Security teams need visibility into which algorithms are being used across the organization, performance metrics for different implementations, and early warning systems for potential vulnerabilities in deployed algorithms.
Version control and rollback capabilities become increasingly important in agile cryptographic environments. Organizations must maintain clear records of algorithm deployments, performance baselines, and rollback procedures to quickly address issues that arise during algorithm transitions.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
Actionable Takeaway: Build crypto-agility into your architecture from the ground up, creating abstraction layers that enable seamless algorithm transitions without application-level modifications.
What Backup Encryption Strategies Protect Against Quantum Attacks?
Backup encryption strategies require special attention in quantum-resistant ransomware preparation because backups often represent the last line of defense against successful attacks. Traditional backup encryption approaches frequently rely on the same vulnerable algorithms used in primary systems, creating single points of failure that quantum-capable attackers can exploit to compromise both operational data and recovery mechanisms simultaneously.
Effective quantum-resistant backup strategies must address multiple dimensions of protection. First, the encryption algorithms themselves must resist quantum attacks. This typically involves implementing hybrid or fully post-quantum encryption schemes for backup data. Second, key management practices must prevent quantum attackers from accessing decryption keys through side-channel attacks or key storage vulnerabilities. Third, backup integrity mechanisms must remain secure against quantum-capable forgery attempts.
One approach gaining traction involves layered encryption strategies that combine multiple algorithms with different security properties. For example, organizations might implement three-tiered backup encryption:
- Primary Layer: Fast symmetric encryption (AES-256) for bulk data protection
- Secondary Layer: Post-quantum key encapsulation (Kyber) for key exchange
- Tertiary Layer: Classical public-key encryption (RSA-3072) for compatibility and redundancy
This approach provides quantum resistance while maintaining compatibility with existing backup infrastructure. The layered design ensures that compromising any single layer doesn't immediately expose backup contents.
bash
Example: Implementing hybrid backup encryption with GPG
Generate post-quantum compatible key pair
gpg --expert --full-generate-key
Select option for ECC and specify Curve25519 for post-quantum readiness
Encrypt backup with hybrid approach
tar -czf - /important/data | gpg --encrypt --recipient [email protected] --output backup_$(date +%Y%m%d).tar.gz.gpg_
Verify encryption details
gpg --list-packets backup_$(date +%Y%m%d).tar.gz.gpg_
Store keys securely with quantum-resistant hardware security modules
pkcs11-tool --module /usr/lib/softhsm/libsofthsm2.so --login --pin 1234 --write-object backup-key --type privkey
Key management for quantum-resistant backup encryption requires careful consideration of quantum attack vectors. Traditional approaches storing master keys in hardware security modules (HSMs) or key management services may prove insufficient if quantum attackers can extract keys through improved side-channel analysis or direct quantum attacks on key storage mechanisms.
Alternative key management strategies include:
- Split-Key Approaches: Distributing key material across multiple locations or systems, requiring quantum-resistant threshold cryptography for reconstruction
- Time-Based Key Rotation: Implementing frequent key changes that limit the window of opportunity for quantum attacks
- Physical Isolation: Storing backup keys in air-gapped systems or quantum-resistant physical media
- Multi-Factor Key Derivation: Combining passwords, biometrics, and hardware tokens with quantum-resistant key derivation functions
Backup integrity protection becomes equally important in quantum-resistant strategies. Hash-based signatures using XMSS (eXtended Merkle Signature Scheme) or LMS (Leighton-Micali Signature) provide quantum-resistant integrity verification while maintaining reasonable performance characteristics for large backup datasets.
Organizations should also consider geographic distribution of backup copies using different encryption schemes. This approach ensures that regional quantum computing advances don't simultaneously compromise all backup locations. Cloud-based backup services should be evaluated for their quantum-resistance capabilities and compliance with emerging post-quantum standards.
Testing and validation of quantum-resistant backup strategies require specialized approaches. Traditional penetration testing may not adequately simulate quantum attack scenarios. Organizations should develop quantum-aware testing frameworks that can validate backup restoration processes under simulated quantum conditions.
Recovery time objectives (RTOs) and recovery point objectives (RPOs) may need adjustment when implementing quantum-resistant backup encryption. Post-quantum algorithms often require more processing power, potentially extending backup windows and restoration times. Performance optimization becomes critical for maintaining operational continuity.
Documentation and procedural changes are essential components of quantum-resistant backup strategies. Teams must understand new encryption procedures, key management workflows, and restoration processes. Regular training and drills ensure that personnel can effectively operate quantum-resistant backup systems during crisis situations.
Key Insight: Quantum-resistant backup encryption requires a multi-layered approach that combines algorithm diversity, robust key management, and integrity protection to ensure reliable data recovery against advanced quantum threats.
How Should Incident Response Plans Address Quantum Attack Scenarios?
Traditional incident response plans inadequately prepare organizations for quantum-resistant ransomware attacks due to the fundamentally different nature of quantum threats. Quantum-capable attackers can potentially compromise entire cryptographic infrastructures instantaneously, bypassing conventional detection mechanisms and rendering standard containment procedures ineffective. Organizations must develop quantum-aware incident response capabilities that account for these unique characteristics.
The initial detection phase requires enhanced monitoring for indicators of quantum attack activity. Unlike traditional ransomware that typically exhibits gradual infiltration patterns, quantum attacks may manifest as sudden, widespread cryptographic failures across multiple systems simultaneously. Monitoring systems should watch for unusual patterns such as:
- Unexpected certificate validation failures across diverse services
- Simultaneous decryption of previously secure communications
- Rapid compromise of multiple authentication systems
- Unusual network traffic patterns indicating large-scale data exfiltration
yaml
Example SIEM rule for detecting potential quantum attack indicators
name: "Potential Quantum Decryption Activity" type: correlation conditions:
- event_type: "tls_handshake_failure"
count: "> 50"
timeframe: "5 minutes"
- event_type: "authentication_failure" count: "> 100" timeframe: "5 minutes"
- event_type: "file_decryption" count: "> 1000" timeframe: "10 minutes" actions:
- alert_severity: "critical"
- notify_security_team
- initiate_quantum_response_playbook
- isolate_affected_network_segments
Containment strategies for quantum attacks differ significantly from traditional approaches. Since quantum attackers can potentially decrypt all similarly encrypted data simultaneously, organizations must assume complete cryptographic compromise and implement network segmentation based on physical isolation rather than cryptographic boundaries. This may involve disconnecting critical systems from networks entirely or implementing air-gap procedures for sensitive operations.
Communication protocols during quantum incidents require special consideration. Traditional encrypted communication channels may prove compromised, necessitating alternative communication methods. Organizations should maintain pre-established out-of-band communication procedures using quantum-resistant channels or physical media.
The eradication phase presents unique challenges in quantum attack scenarios. Standard malware removal techniques prove inadequate when attackers possess quantum decryption capabilities that allow continuous access to systems. Organizations must implement complete system rebuilds from trusted sources, including firmware verification and hardware attestation processes.
Recovery procedures must account for potential compromise of backup systems encrypted with vulnerable algorithms. Organizations should maintain multiple generations of backups using different encryption schemes and regularly test restoration procedures under simulated quantum attack conditions.
Post-incident analysis for quantum attacks requires specialized forensic capabilities. Traditional disk imaging and memory analysis may prove insufficient when attackers can decrypt data at rest. Organizations should develop quantum-aware forensic procedures that can preserve evidence integrity even when underlying encryption is compromised.
Coordination with external stakeholders becomes more complex in quantum attack scenarios. Regulatory bodies, law enforcement agencies, and industry partners may lack understanding of quantum threats, requiring organizations to provide specialized briefing materials and coordinate response activities through established quantum security channels.
Training and simulation exercises prove essential for effective quantum incident response. Teams must practice responding to scenarios involving instantaneous cryptographic compromise, widespread system access, and potential data exfiltration at quantum speeds. These exercises should incorporate realistic quantum attack simulations and test both technical and procedural response capabilities.
Documentation and lessons learned processes must capture quantum-specific insights that can inform future response activities. This includes cataloging effective countermeasures, identifying gaps in current capabilities, and developing improvement recommendations for ongoing quantum preparedness.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
Actionable Takeaway: Develop quantum-aware incident response playbooks that account for instantaneous cryptographic compromise and implement alternative communication and containment strategies.
What Is the Recommended Timeline for Quantum-Safe Migration?
Establishing a realistic timeline for quantum-safe migration requires balancing technical complexity with evolving threat landscapes. Given IBM's 2026 breakthroughs and projected timelines for cryptographically relevant quantum computers, organizations face an 18-24 month window for completing critical migration activities. This compressed timeframe demands strategic planning and phased implementation approaches that maximize security improvements within practical constraints.
A recommended migration timeline spans four distinct phases over 24-36 months:
Phase 1: Assessment and Planning (Months 1-6) This foundational phase focuses on comprehensive cryptographic inventory, risk assessment, and migration strategy development. Organizations should complete detailed assessments of their cryptographic infrastructure, prioritize systems based on risk exposure, and develop detailed migration roadmaps. Key deliverables include cryptographic inventories, risk classifications, resource requirements, and executive approval for migration initiatives.
Phase 2: Foundation Building (Months 7-12) During this phase, organizations implement crypto-agility frameworks, upgrade cryptographic libraries, and begin pilot migrations of low-risk systems. This period focuses on building technical capabilities and organizational readiness rather than large-scale production migrations. Training programs, testing environments, and monitoring systems should be established during this phase.
Phase 3: Critical System Migration (Months 13-24) High-priority systems undergo migration to quantum-resistant algorithms during this critical phase. Organizations should implement hybrid encryption schemes, upgrade certificate authorities, and deploy post-quantum authentication mechanisms. Continuous monitoring and incident response capabilities for quantum threats should be fully operational by the end of this phase.
Phase 4: Complete Transition (Months 25-36) Remaining systems complete migration to quantum-resistant algorithms, and organizations transition from hybrid approaches to fully post-quantum implementations. Ongoing maintenance procedures, performance optimization, and continuous improvement processes should be institutionalized during this final phase.
Milestone tracking becomes essential for managing migration progress effectively. Organizations should establish quarterly review cycles that assess migration completion rates, identify blockers, and adjust timelines based on actual progress versus projections. Key performance indicators might include:
- Percentage of systems migrated to quantum-resistant algorithms
- Number of remaining vulnerable certificates in production
- Performance benchmarks for post-quantum implementations
- Staff training completion rates
- Budget utilization versus projections
Resource allocation planning must account for the specialized skills required for quantum-safe migration. Organizations may need to hire cryptographic specialists, train existing staff, or engage consulting partners with post-quantum expertise. Budget planning should include provisions for hardware upgrades, software licensing, training costs, and potential delays in migration schedules.
Risk management throughout the migration process requires continuous threat assessment and adaptation. As quantum computing capabilities evolve and new attack vectors emerge, organizations must remain flexible in their migration approaches and prepared to accelerate critical activities when necessary.
Compliance and regulatory considerations add additional complexity to migration timelines. Organizations operating in regulated industries must ensure that quantum-safe implementations meet applicable standards and obtain necessary approvals for new cryptographic approaches. Early engagement with regulatory bodies can help streamline approval processes and avoid delays.
Testing and validation activities should occur throughout the migration timeline rather than as discrete phases. Organizations should implement continuous testing frameworks that validate quantum-resistant implementations under realistic conditions and provide early warning of potential issues.
Contingency planning proves essential given the uncertainty surrounding quantum computing development timelines. Organizations should maintain rollback capabilities for critical systems and develop alternative approaches for scenarios where migration activities fall behind schedule or encounter unexpected technical challenges.
Communication with stakeholders throughout the migration process helps maintain support and alignment with business objectives. Regular updates to executive leadership, board members, and key business partners ensure continued investment in migration activities and help manage expectations regarding potential impacts on operations.
Key Insight: Successful quantum-safe migration requires a structured, phased approach spanning 24-36 months with regular milestone reviews and adaptive planning to accommodate evolving threat landscapes and technical developments.
Key Takeaways
• Quantum computing breakthroughs have accelerated threat timelines, making quantum-resistant ransomware preparation urgent for all organizations • Comprehensive cryptographic infrastructure assessment forms the foundation for effective migration planning and risk prioritization • Implementing crypto-agility frameworks enables seamless algorithm transitions without application-level modifications or service disruptions • Backup encryption strategies must incorporate quantum-resistant algorithms and robust key management to ensure reliable data recovery • Quantum-aware incident response plans require specialized detection, containment, and communication procedures that account for instantaneous cryptographic compromise • A structured 24-36 month migration timeline with phased implementation maximizes security improvements while maintaining operational continuity • mr7.ai's AI-powered tools including mr7 Agent, 0Day Coder, and KaliGPT can accelerate assessment, migration, and testing activities
Frequently Asked Questions
Q: How soon do quantum computers pose a real threat to current encryption?
Based on recent breakthroughs like IBM's 2026 fault-tolerant quantum processors, cryptographically relevant quantum computers capable of breaking RSA-2048 and ECC-256 encryption could emerge within 18-24 months. Organizations should prepare for quantum-resistant ransomware threats by late 2027.
Q: What are the most vulnerable cryptographic algorithms to quantum attacks?
RSA encryption, elliptic curve cryptography (ECC), Diffie-Hellman key exchange, and DSA signatures are highly vulnerable to Shor's algorithm. Symmetric encryption like AES-128 becomes effectively 64-bit secure against Grover's algorithm, requiring AES-256 for quantum resistance.
Q: Can existing systems be upgraded to quantum-resistant cryptography?
Most modern systems can be upgraded through crypto-agility frameworks that abstract cryptographic operations. Legacy systems may require more extensive modifications or replacement. The key is implementing flexible architectures that support algorithm transitions.
Q: What post-quantum algorithms should organizations implement?
NIST has standardized CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures. Additional candidates like Falcon and SPHINCS+ offer different performance trade-offs. Organizations should implement hybrid approaches combining classical and post-quantum algorithms during transition periods.
Q: How can small organizations afford quantum-resistant security upgrades?
Many quantum-resistant implementations are available as open-source libraries and cloud services. Organizations can start with critical systems and gradually expand coverage. mr7.ai offers affordable AI-powered tools that can automate much of the assessment and migration process, reducing manual effort costs.
Stop Manual Testing. Start Using AI.
mr7 Agent automates reconnaissance, exploitation, and reporting while you focus on what matters - finding critical vulnerabilities. Plus, use KaliGPT and 0Day Coder for real-time AI assistance.