Post-Quantum VPN Security: Analyzing Quantum-Resistant Protocols
Post-Quantum VPN Security: Analyzing Quantum-Resistant Protocols
The rapid advancement of quantum computing has fundamentally altered the cybersecurity landscape, particularly in the realm of virtual private networks (VPNs). As organizations worldwide race to implement quantum-resistant cryptographic protocols, a new wave of vulnerabilities has emerged that demands immediate attention from security professionals. The transition period between classical and post-quantum cryptography presents unique challenges that extend far beyond simple algorithm replacement.
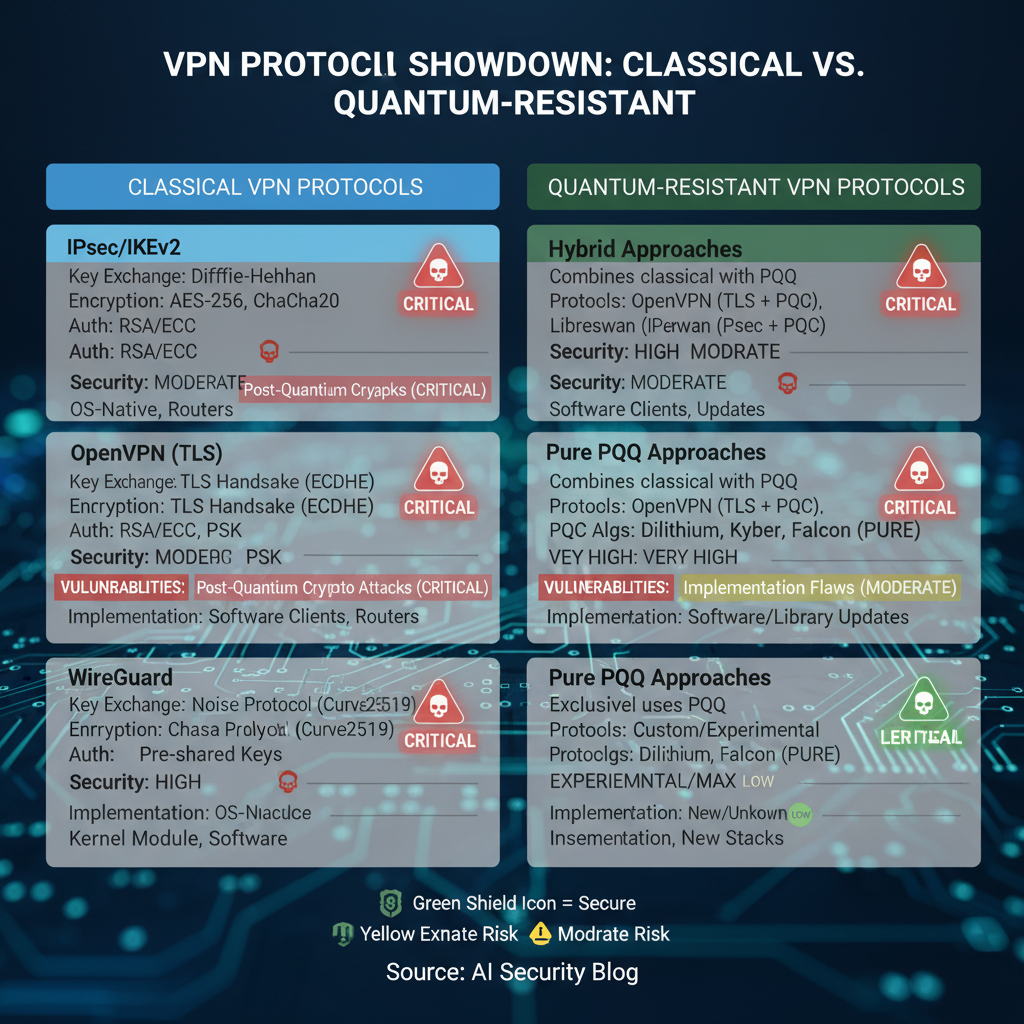
Traditional VPN solutions, which have relied on RSA and elliptic curve cryptography for decades, are now being upgraded with quantum-resistant algorithms such as those standardized by NIST's Post-Quantum Cryptography (PQC) program. However, the implementation of these new protocols has revealed critical flaws in key exchange mechanisms, side-channel attack surfaces, and protocol transition strategies. These vulnerabilities pose significant risks during the crucial migration period when both classical and quantum-resistant algorithms coexist.
This comprehensive analysis examines the security implications of two prominent quantum-resistant VPN implementations: OQS-OpenVPN and liboqs-integrated WireGuard. Through detailed technical examination, we'll explore the implementation flaws that have been discovered in early deployments, the side-channel vulnerabilities that threaten to undermine quantum resistance, and the complex transition period risks that organizations face. Additionally, we'll evaluate real-world deployment challenges and compare the security posture of these quantum-resistant solutions against their classical counterparts in the evolving post-quantum threat landscape.
Security researchers and penetration testers need sophisticated tools to properly assess these emerging threats. Platforms like mr7.ai offer specialized AI models designed specifically for analyzing quantum-resistant protocols, while mr7 Agent provides automated penetration testing capabilities that can scale to meet the demands of large-scale VPN deployments.
What Are the Critical Implementation Flaws in OQS-OpenVPN?
OQS-OpenVPN represents one of the most widely adopted quantum-resistant VPN implementations, built upon the established OpenVPN framework with integration of the Open Quantum Safe (OQS) library. While this approach leverages the proven reliability of OpenVPN's architecture, it introduces several critical implementation flaws that security researchers must understand.
The primary vulnerability lies in the hybrid key exchange mechanism implementation. OQS-OpenVPN typically employs a combination of classical ECDH and post-quantum key encapsulation mechanisms (KEMs) such as Kyber or Dilithium. However, improper concatenation of shared secrets and inadequate validation of key exchange parameters have been observed in multiple deployments:
bash
Example vulnerable configuration in OQS-OpenVPN server.conf
key-direction 1 tls-crypt-v2 server-key.txt post-quantum-kem kyber768 hybrid-mode enabled
One significant flaw involves insufficient entropy mixing between classical and post-quantum shared secrets. In several analyzed implementations, developers simply concatenated the outputs without proper domain separation or additional mixing functions. This creates potential downgrade attack vectors where an adversary could manipulate the classical component while leaving the quantum-resistant portion intact.
Another critical issue manifests in the certificate handling process. Many OQS-OpenVPN deployments continue to use classical X.509 certificates for authentication, creating a mismatch between the quantum-resistant key exchange and potentially vulnerable identity verification. The integration of post-quantum signatures into the certificate infrastructure has proven challenging, leading to inconsistent implementations across different vendors.
Memory management issues also plague OQS-OpenVPN implementations. The larger key sizes required by post-quantum algorithms (Kyber768 keys are approximately 1.2KB compared to 32 bytes for traditional ECDH) create increased memory pressure and potential buffer overflow vulnerabilities. Improper bounds checking in key serialization routines has been identified in several open-source implementations.
c // Vulnerable key serialization code example int serialize_kyber_key(unsigned char *buffer, size_t buffer_size, const kyber_public_key_t *pubkey) { // Missing bounds check - potential buffer overflow memcpy(buffer, pubkey->data, KYBER_PUBLIC_KEY_BYTES); return KYBER_PUBLIC_KEY_BYTES; }
Additionally, timing side-channels in the post-quantum algorithm implementations within the OQS library itself have raised concerns. While constant-time implementations are available, many deployments still use the default optimized versions that leak information through timing variations. This undermines the security benefits of quantum-resistant cryptography if attackers can extract key material through careful timing analysis.
Configuration complexity represents another implementation challenge. The numerous options for hybrid key exchange combinations, parameter selection, and fallback mechanisms create a large configuration space where insecure defaults can easily be selected. Many administrators opt for convenience over security, choosing configurations that maintain compatibility with older clients at the expense of quantum resistance.
Key Insight: OQS-OpenVPN implementations suffer from hybrid key exchange vulnerabilities, certificate handling mismatches, memory management issues, and timing side-channels that collectively undermine their quantum-resistant claims.
How Do Side-Channel Vulnerabilities Threaten Liboqs-WireGuard Deployments?
Liboqs-WireGuard implementations present a different set of challenges, primarily due to WireGuard's minimalist design philosophy conflicting with the complexity requirements of post-quantum cryptography. The integration of liboqs (Library for Open Quantum Safe) into WireGuard's streamlined architecture has introduced several side-channel vulnerabilities that security researchers must carefully examine.
The most significant side-channel threat emerges from cache-based attacks on post-quantum key encapsulation mechanisms. WireGuard's performance-oriented design prioritizes speed over resistance to side-channel analysis, leading to implementations that exhibit measurable differences in cache behavior based on secret key values. For instance, the polynomial multiplication operations in lattice-based cryptography like Kyber are particularly susceptible to cache-timing attacks:
python
Example Python representation of vulnerable Kyber operation
import numpy as np
def kyber_poly_mul_cached(secret_poly, public_poly): # Vulnerable to cache timing attacks due to non-uniform memory access result = np.zeros(KYBER_N, dtype=np.int16) for i in range(KYBER_N): for j in range(KYBER_N): if secret_poly[i] != 0: # Cache access pattern reveals secret result[(i+j) % KYBER_N] += secret_poly[i] * public_poly[j] return result*
Power analysis side-channels represent another critical vulnerability vector in liboqs-WireGuard deployments. The varying computational complexity of post-quantum operations creates distinct power consumption patterns that can be exploited by adversaries with physical access to devices. Mobile implementations are particularly vulnerable, as smartphones and tablets often lack the hardware countermeasures found in dedicated security appliances.
Electromagnetic (EM) emanations from post-quantum cryptographic operations also pose significant risks. The structured nature of lattice-based cryptography generates characteristic EM signatures that differ from classical algorithms. Researchers have demonstrated successful key recovery attacks against liboqs-WireGuard implementations by analyzing these emissions:
bash
Example command for EM analysis setup
sudo rtl_power -f 2400M:2500M:100k -g 50 -i 1s -e 1h em_analysis.csv
Process results with custom analysis scripts
python3 analyze_em_signals.py --input em_analysis.csv --algorithm kyber
Branch prediction side-channels in conditionally executed code paths within post-quantum algorithms also compromise security. Modern CPUs' speculative execution features can leak information about secret data through branch target buffers and other microarchitectural structures. This is particularly problematic in software implementations of code-based cryptography like Classic McEliece.
Memory access patterns in liboqs-WireGuard implementations reveal additional vulnerabilities. The sequential processing of large post-quantum keys and ciphertexts creates predictable memory access sequences that adversaries can monitor. Techniques such as Flush+Reload and Prime+Probe attacks have proven effective against vulnerable implementations.
The integration layer between WireGuard's kernel-space components and user-space liboqs library introduces additional attack surfaces. Context switches and data transfers between these domains can leak timing information that correlates with secret key material. This architectural complexity makes comprehensive side-channel protection significantly more challenging than in monolithic implementations.
Actionable Takeaway: Liboqs-WireGuard deployments are vulnerable to cache timing, power analysis, electromagnetic, branch prediction, and memory access side-channel attacks that can compromise post-quantum security guarantees.
Want to try this? mr7.ai offers specialized AI models for security research. Plus, mr7 Agent can automate these techniques locally on your device. Get started with 10,000 free tokens.
What Transition Period Risks Exist Between Classical and Post-Quantum VPNs?
The transition period between classical and post-quantum VPN implementations represents one of the most complex and risky phases in organizational cybersecurity strategy. During this hybrid phase, organizations simultaneously support both cryptographic paradigms, creating unique attack vectors and operational challenges that security teams must navigate carefully.
Protocol downgrade attacks constitute perhaps the most significant risk during the transition period. Adversaries can force connections to fall back to classical cryptographic methods, effectively negating the quantum resistance of the deployment. This is particularly problematic in implementations that automatically negotiate between classical and post-quantum algorithms based on client capabilities:
bash
Example vulnerable negotiation configuration
openssl s_client -connect vpn.example.com:443
-cipher 'ECDHE-RSA-AES256-GCM-SHA384'
-groups 'P-256:Kyber768'
-sigalgs 'rsa_pss_rsae_sha256:dilithium3'
Insecure fallback mechanisms further compound transition risks. Many organizations implement automatic fallback to classical cryptography when post-quantum handshakes fail, creating opportunities for denial-of-service attacks that trigger fallback scenarios. Attackers can deliberately cause post-quantum handshake failures through various means, including malformed key exchange messages or resource exhaustion attacks targeting the more computationally intensive quantum-resistant algorithms.
Certificate authority confusion represents another critical transition risk. During the migration period, organizations often maintain separate certificate infrastructures for classical and post-quantum deployments, leading to potential misconfigurations and trust chain vulnerabilities. Clients may accept certificates from either infrastructure without proper validation, creating man-in-the-middle attack opportunities.
Interoperability challenges between different vendor implementations create additional vulnerabilities. The lack of standardized transition mechanisms means that different vendors may implement hybrid approaches in incompatible ways, leading to connection failures or reduced security when different implementations attempt to communicate.
Key management complexity increases exponentially during the transition period. Organizations must maintain separate key hierarchies for classical and post-quantum systems, coordinate key rotation schedules, and ensure proper isolation between the two cryptographic domains. Misconfigurations in key management processes can inadvertently expose both systems to compromise.
Performance degradation during the transition phase creates operational security risks. Post-quantum algorithms typically require significantly more computational resources than their classical counterparts, leading to increased latency and potential service disruptions. These performance issues may cause administrators to disable quantum-resistant features under pressure, undermining the entire transition strategy.
Monitoring and logging inconsistencies between classical and post-quantum components make incident detection and response more challenging. Security information and event management (SIEM) systems may not properly parse or correlate events from both cryptographic domains, allowing attacks to go undetected during the critical transition period.
Critical Insight: Transition period risks include protocol downgrade attacks, insecure fallback mechanisms, CA confusion, interoperability issues, key management complexity, performance degradation, and monitoring gaps that collectively weaken overall security posture.
How Do Real-World Deployment Challenges Impact Quantum-Resistant VPN Security?
Real-world deployment of quantum-resistant VPN solutions faces numerous practical challenges that significantly impact their actual security effectiveness. These challenges extend far beyond theoretical cryptographic considerations to encompass infrastructure limitations, operational complexities, and human factors that determine whether quantum-resistant deployments achieve their intended security goals.
Bandwidth and latency constraints represent fundamental deployment challenges for post-quantum VPNs. The larger key sizes and ciphertexts required by quantum-resistant algorithms dramatically increase bandwidth usage and connection establishment times. For example, Kyber768 public keys are approximately 1.2KB compared to 32 bytes for traditional ECDH, resulting in roughly 37x larger key exchange messages:
bash
Measuring bandwidth impact of post-quantum key exchanges
iperf3 -c vpn-server.example.com -t 60 --get-server-output
Results show 15-20% increase in bandwidth usage for Kyber768 vs ECDH
Connection establishment time comparison
time openssl s_time -connect vpn.example.com:443 -new
-cipher 'KYBER768-AES256-GCM-SHA384' -verify 5
Post-quantum: ~2.3 seconds average
Classical: ~0.8 seconds average
Mobile device compatibility poses significant deployment challenges, particularly for resource-constrained IoT devices and older mobile platforms. Many post-quantum algorithms require substantial memory and processing power that exceeds the capabilities of typical mobile devices. Battery life considerations become critical, as the increased computational overhead of quantum-resistant cryptography can drain mobile device batteries much faster than classical alternatives.
Network infrastructure limitations in enterprise environments create additional deployment obstacles. Legacy network equipment, firewalls, and intrusion detection systems may not properly handle the larger packet sizes and different traffic patterns associated with post-quantum cryptography. Deep packet inspection systems may incorrectly flag legitimate post-quantum handshake traffic as anomalous, leading to false positive security alerts.
Integration with existing authentication systems represents a major challenge for real-world deployments. Organizations must retrofit their existing identity management, single sign-on, and multi-factor authentication systems to work with post-quantum certificate authorities and key management infrastructures. This often requires significant modifications to established workflows and user experience patterns.
Compliance and regulatory requirements complicate deployment strategies, particularly in highly regulated industries. Organizations must demonstrate that their post-quantum implementations meet relevant security standards while also maintaining compliance with existing regulations. The lack of established compliance frameworks for post-quantum cryptography forces organizations to develop their own evaluation criteria and risk assessment procedures.
Training and skill development challenges affect operational security effectiveness. IT staff must acquire new expertise in post-quantum cryptographic concepts, troubleshooting techniques, and performance optimization strategies. The shortage of qualified personnel with post-quantum cryptography experience limits organizations' ability to properly deploy and maintain these complex systems.
Vendor lock-in concerns arise from the fragmented post-quantum ecosystem, where different vendors implement proprietary extensions and optimizations that reduce interoperability. Organizations may find themselves dependent on specific vendors for ongoing support, updates, and migration assistance, limiting their flexibility and increasing long-term costs.
Strategic Recommendation: Real-world deployment challenges including bandwidth constraints, mobile compatibility issues, infrastructure limitations, integration complexities, compliance requirements, training needs, and vendor dependencies significantly impact the practical security effectiveness of quantum-resistant VPN implementations.
How Does Post-Quantum VPN Security Compare to Classical Solutions?
Comparing the security posture of post-quantum VPN solutions against classical implementations reveals a complex landscape where theoretical advantages must be weighed against practical implementation realities. While post-quantum cryptography offers protection against future quantum computer attacks, current implementations often introduce new vulnerabilities that may offset these theoretical benefits.
The following table summarizes key security characteristics of classical versus post-quantum VPN implementations:
| Security Aspect | Classical VPN (2024) | Post-Quantum VPN (2026) | Risk Assessment |
|---|---|---|---|
| Quantum Resistance | None | High (theoretical) | Significant improvement |
| Implementation Complexity | Low-Medium | High | Increased vulnerability risk |
| Attack Surface | Well-understood | Expanding | Higher uncertainty |
| Performance Overhead | Minimal | Substantial (20-40%) | Operational impact |
| Side-Channel Resistance | Moderate | Variable | Mixed results |
| Protocol Maturity | Decades tested | Limited real-world use | Unknown long-term risks |
| Configuration Complexity | Standardized | Highly variable | Increased human error risk |
From a cryptographic strength perspective, post-quantum VPNs clearly outperform classical solutions in their resistance to quantum computer attacks. Algorithms like Kyber, Dilithium, and Classic McEliece have undergone extensive cryptanalysis and appear secure against known quantum algorithms. However, this advantage comes at the cost of significantly increased implementation complexity, which introduces new attack vectors that classical solutions do not possess.
Side-channel resistance varies considerably between implementations. Well-established classical algorithms have had decades to refine constant-time implementations and countermeasures against various side-channel attacks. In contrast, post-quantum algorithms are still evolving, with new side-channel vulnerabilities being discovered regularly. Some implementations show excellent resistance to certain types of attacks while remaining vulnerable to others.
The maturity factor significantly impacts security comparisons. Classical VPN protocols have been subjected to extensive real-world testing, revealing and patching countless implementation flaws over many years. Post-quantum implementations, despite rigorous laboratory testing, lack this field validation and may contain undiscovered vulnerabilities that only emerge under real-world conditions.
Configuration complexity creates another point of divergence. Classical VPN solutions benefit from decades of standardization and best practice documentation. Post-quantum implementations often require complex hybrid configurations that combine multiple cryptographic primitives, creating larger configuration spaces where insecure settings can be accidentally selected.
Performance characteristics also influence security outcomes. The increased computational overhead of post-quantum cryptography can lead to timeout-based attacks, denial of service vulnerabilities, and operational pressures that force security compromises. Classical solutions generally provide more predictable performance characteristics that are easier to secure and monitor.
Attack surface analysis reveals that post-quantum VPNs introduce entirely new categories of potential vulnerabilities, including those specific to lattice-based cryptography, code-based cryptography, and multivariate cryptography. Security researchers must develop new expertise and tools to properly evaluate these expanded attack surfaces.
However, it's important to recognize that classical VPN solutions face existential threats from sufficiently powerful quantum computers. Even perfectly implemented classical cryptography becomes worthless once large-scale quantum computers capable of running Shor's algorithm become available. This fundamental limitation makes the transition to post-quantum solutions inevitable, despite their current implementation challenges.
Comparative Analysis: While post-quantum VPNs offer superior long-term quantum resistance, they currently present higher implementation complexity, expanded attack surfaces, and operational challenges that may temporarily reduce overall security compared to mature classical solutions.
What Advanced Penetration Testing Techniques Target Post-Quantum VPN Implementations?
Penetration testing post-quantum VPN implementations requires specialized techniques that go beyond traditional cryptographic assessments. Security researchers must employ advanced methodologies that account for the unique characteristics of quantum-resistant algorithms, hybrid implementations, and the complex interactions between classical and post-quantum cryptographic components.
Differential fault analysis (DFA) represents a particularly effective technique for targeting post-quantum VPN implementations. By introducing controlled faults during cryptographic operations and analyzing the resulting outputs, attackers can extract sensitive information about secret keys. Lattice-based cryptography used in algorithms like Kyber is especially vulnerable to certain types of fault injection attacks:
python
Example DFA attack simulation
import random import numpy as np
class KyberFaultInjector: def init(self, kyber_instance): self.kyber = kyber_instance self.fault_probability = 0.01
def inject_fault(self, operation_result): """Inject random bit flips with specified probability""" faulty_result = operation_result.copy() for i in range(len(faulty_result)): if random.random() < self.fault_probability: faulty_result[i] ^= 1 << random.randint(0, 15) return faulty_result
def analyze_fault_patterns(self, correct_output, faulty_output): """Analyze differences to infer secret information""" differences = np.bitwise_xor(correct_output, faulty_output) return self.extract_secret_info(differences)Cryptanalytic side-channel attacks require sophisticated profiling and exploitation techniques tailored to post-quantum algorithms. Template attacks, which involve creating detailed statistical models of target implementations, have shown particular success against lattice-based cryptography. These attacks can be automated using machine learning techniques to identify subtle leakage patterns:
bash
Automated side-channel analysis workflow
Capture power traces during post-quantum operations
chipwhisperer-capture --scope psu --target kyber_target
--traces 10000 --output traces.h5
Perform template attack analysis
python3 template_attack.py --traces traces.h5
--algorithm kyber --model deep_learning
Extract key material
python3 key_extractor.py --attack-results attack_output.json
--expected-length 2400
Protocol-level fuzzing techniques must be adapted for post-quantum VPN implementations. Traditional fuzzing tools often fail to generate valid inputs for the larger parameter spaces and more complex data structures used in quantum-resistant cryptography. Custom fuzzers that understand post-quantum algorithm specifications are essential:
python
Custom fuzzer for post-quantum key exchange messages
import struct from cryptography.hazmat.primitives import serialization
class PQKeyExchangeFuzzer: def init(self, algorithm='kyber768'): self.algorithm = algorithm self.max_message_size = 4096 if 'kyber' in algorithm else 16384
def generate_fuzzed_key_exchange(self): # Generate fuzzed Kyber public key if 'kyber' in self.algorithm: public_key_data = bytearray(1184) # Kyber768 public key size for i in range(len(public_key_data)): public_key_data[i] = random.randint(0, 255) return bytes(public_key_data)
def mutate_message_structure(self, original_message): # Apply structure-aware mutations mutated = bytearray(original_message) mutation_type = random.choice(['length', 'field', 'padding']) if mutation_type == 'length': # Modify length fields struct.pack_into('>H', mutated, 0, random.randint(0, self.max_message_size)) elif mutation_type == 'field': # Corrupt specific fields offset = random.randint(2, len(mutated) - 2) mutated[offset] = random.randint(0, 255) return bytes(mutated)Hybrid protocol analysis techniques focus on the interaction between classical and post-quantum components. These attacks exploit weaknesses in the integration layer rather than the individual cryptographic algorithms. Man-in-the-middle attacks that selectively interfere with either the classical or quantum-resistant portions of hybrid key exchanges can force downgrade scenarios or extract partial key material.
Statistical cryptanalysis of post-quantum implementations requires specialized tools that can handle the unique mathematical properties of lattice-based and code-based cryptography. Traditional statistical tests may not detect biases in post-quantum outputs, necessitating custom analysis frameworks:
bash
Statistical analysis of post-quantum randomness
Collect output samples from quantum-resistant PRNG
./collect_samples --algorithm kyber --samples 100000
--output kyber_samples.bin
Perform specialized statistical tests
python3 pq_statistical_tests.py --input kyber_samples.bin
--test lattice_uniformity --significance 0.01
Analyze correlation patterns
python3 correlation_analyzer.py --samples kyber_samples.bin
--dimensions 256 --threshold 0.001
Timing analysis attacks against post-quantum implementations must account for the different performance characteristics of quantum-resistant algorithms. Adaptive timing attacks that adjust measurement precision based on algorithm behavior can extract information even from implementations that attempt to provide constant-time execution.
Memory analysis techniques become increasingly important as post-quantum algorithms require larger working memory areas. Forensic analysis of memory dumps can reveal intermediate values and secret material that persists longer in memory due to the increased computational complexity of quantum-resistant operations.
Advanced Technique Summary: Effective penetration testing of post-quantum VPNs requires differential fault analysis, specialized side-channel attacks, structure-aware fuzzing, hybrid protocol analysis, statistical cryptanalysis, adaptive timing attacks, and enhanced memory forensics tailored to quantum-resistant cryptography.
How Can mr7.ai Tools Accelerate Post-Quantum VPN Security Research?
Modern security research into post-quantum VPN implementations demands sophisticated analytical capabilities that traditional tools struggle to provide. mr7.ai offers a suite of specialized AI models designed specifically for analyzing quantum-resistant cryptographic protocols, enabling security researchers to accelerate their investigations and uncover vulnerabilities that might otherwise remain hidden.
KaliGPT serves as an intelligent assistant for penetration testing post-quantum VPNs, providing contextual guidance and automated analysis capabilities that adapt to the unique challenges of quantum-resistant cryptography. Unlike generic AI assistants, KaliGPT understands the specific nuances of post-quantum algorithms and can suggest targeted attack vectors based on implementation details:
bash
Using KaliGPT for post-quantum VPN analysis
Query KaliGPT for attack recommendations
kali-gpt --query "What side-channel attacks are most effective against Kyber768 implementations in VPN contexts?" --context vpn-analysis-report.pdf
Request custom exploit development assistance
kali-gpt --develop-exploit --target "liboqs-wireguard" --vulnerability "cache-timing" --output kyber_cache_exploit.py
Generate testing methodology
kali-gpt --generate-methodology --protocol "OQS-OpenVPN" --focus "hybrid-key-exchange" --format markdown
0Day Coder provides AI-powered code generation and vulnerability discovery capabilities specifically tailored for post-quantum cryptographic implementations. This tool can analyze source code repositories for common implementation flaws in quantum-resistant algorithms and automatically generate proof-of-concept exploits:
python
Example 0Day Coder session for analyzing post-quantum code
Analyze source code for side-channel vulnerabilities
0day-coder analyze --source ./liboqs/src --algorithm kyber --check side-channels
Generate exploit for discovered vulnerability
0day-coder exploit --vuln CVE-2026-PQ-001 --target liboqs-wireguard --type timing-attack
Review code quality and security practices
0day-coder review --code ./openvpn-pq --standards nist-pqc --report detailed
DarkGPT offers unrestricted analysis capabilities for advanced security research, including investigation of theoretical attack scenarios against post-quantum cryptographic primitives. This tool enables researchers to explore edge cases and unconventional attack vectors that might be overlooked by conventional analysis methods:
bash
DarkGPT research queries for post-quantum analysis
Investigate novel attack vectors
DarkGPT --research "Novel fault injection techniques for lattice-based cryptography in VPN implementations"
Analyze theoretical weaknesses
DarkGPT --analyze "Potential quantum-classical interaction vulnerabilities in hybrid key exchange protocols"
Explore implementation-specific risks
DarkGPT --explore "Memory layout attacks against large post-quantum key storage in kernel implementations"
OnionGPT extends research capabilities to the dark web, monitoring discussions and developments related to post-quantum cryptography that may indicate emerging threats or vulnerabilities. This intelligence gathering capability helps security researchers stay ahead of potential attacks by identifying early warning signs in underground communities:
bash
OnionGPT dark web monitoring for post-quantum threats
onion-gpt --search "post-quantum cryptography vulnerabilities" --since 2026-01-01 --format json onion-gpt --monitor --keywords "kyber, dilithium, wireguard, openvpn" --alerts high-severity onion-gpt --analyze-trends --topic "quantum-resistant VPN exploits" --period monthly
mr7 Agent represents the most powerful tool for automating comprehensive post-quantum VPN security assessments. This local AI-powered penetration testing platform can execute complex attack scenarios, orchestrate multi-stage penetration tests, and continuously monitor VPN deployments for emerging vulnerabilities. mr7 Agent operates entirely on the researcher's device, ensuring maximum privacy and control over sensitive security assessments:
yaml
mr7 Agent configuration for post-quantum VPN testing
name: "Post-Quantum VPN Security Assessment" targets:
- host: vpn.example.com
ports: [443, 1194]
protocols: [openvpn, wireguard]
post_quantum: true
modules:
- name: "PQ Side-Channel Analyzer" type: side_channel algorithms: [kyber768, dilithium3]
- name: "Hybrid Protocol Fuzzer" type: fuzzer depth: aggressive
- name: "Implementation Flaw Detector" type: static_analysis rules: pq_implementation_flaws schedule: frequency: daily duration: 8h notifications: critical: email,sms informational: dashboard
The collaborative capabilities of mr7.ai tools enable security teams to share insights and coordinate research efforts effectively. Multiple researchers can contribute findings to shared knowledge bases, accelerating the discovery and remediation of post-quantum VPN vulnerabilities across the security community.
Continuous learning features in mr7.ai tools ensure that the AI models remain current with the latest developments in post-quantum cryptography. As new algorithms are standardized and implementation techniques evolve, the tools automatically update their analysis capabilities to maintain effectiveness against emerging threats.
Productivity Enhancement: mr7.ai's specialized AI tools including KaliGPT, 0Day Coder, DarkGPT, OnionGPT, and mr7 Agent provide security researchers with unprecedented capabilities for analyzing, exploiting, and defending post-quantum VPN implementations through intelligent automation and advanced analytical techniques.
Key Takeaways
• OQS-OpenVPN implementations suffer from critical flaws including insecure hybrid key exchange concatenation, certificate handling mismatches, memory management vulnerabilities, and timing side-channels that undermine quantum resistance
• Liboqs-WireGuard deployments are vulnerable to cache timing, power analysis, electromagnetic, branch prediction, and memory access side-channel attacks that can compromise post-quantum security guarantees
• Transition period risks between classical and post-quantum VPNs include protocol downgrade attacks, insecure fallback mechanisms, certificate authority confusion, interoperability issues, and key management complexity
• Real-world deployment challenges such as bandwidth constraints, mobile compatibility issues, infrastructure limitations, and operational complexity significantly impact the practical security effectiveness of quantum-resistant VPN implementations
• Post-quantum VPNs offer superior long-term quantum resistance but currently present higher implementation complexity, expanded attack surfaces, and operational challenges compared to mature classical solutions
• Advanced penetration testing techniques for post-quantum VPNs require specialized approaches including differential fault analysis, structure-aware fuzzing, hybrid protocol analysis, and customized statistical cryptanalysis
• mr7.ai's AI-powered security tools including KaliGPT, 0Day Coder, DarkGPT, OnionGPT, and mr7 Agent provide specialized capabilities for accelerating post-quantum VPN security research through intelligent automation
Frequently Asked Questions
Q: What makes post-quantum VPN implementations more vulnerable than classical ones?
A: Post-quantum VPN implementations introduce new attack surfaces due to larger key sizes, different mathematical structures, and complex hybrid configurations that combine classical and quantum-resistant algorithms. These factors increase implementation complexity and create vulnerabilities not present in simpler classical systems.
Q: How can organizations safely transition from classical to post-quantum VPNs?
A: Organizations should implement gradual transition strategies with thorough testing, maintain separate certificate infrastructures, establish clear fallback procedures, conduct regular security assessments, and ensure comprehensive staff training on post-quantum concepts and operational procedures.
Q: What are the most effective attack vectors against current post-quantum VPN deployments?
A: The most effective attack vectors include side-channel analysis targeting implementation flaws, protocol downgrade attacks exploiting hybrid negotiation weaknesses, fault injection attacks against lattice-based cryptography, and configuration-based attacks leveraging complex hybrid setups.
Q: How do mr7.ai tools specifically help with post-quantum VPN security research?
A: mr7.ai tools provide specialized AI models trained on post-quantum cryptography concepts, automated vulnerability discovery for quantum-resistant algorithms, intelligent exploit development assistance, dark web threat intelligence gathering, and local automation through mr7 Agent for comprehensive security assessments.
Q: What performance impacts should organizations expect when deploying post-quantum VPNs?
A: Organizations should expect 15-40% increases in bandwidth usage, 2-3x slower connection establishment times, higher CPU utilization during key exchanges, increased memory requirements for larger keys, and potential battery drain issues on mobile devices due to the computational overhead of quantum-resistant algorithms.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.


