Mastering Bug Bounty Hunting: Strategies & AI Tools for Success

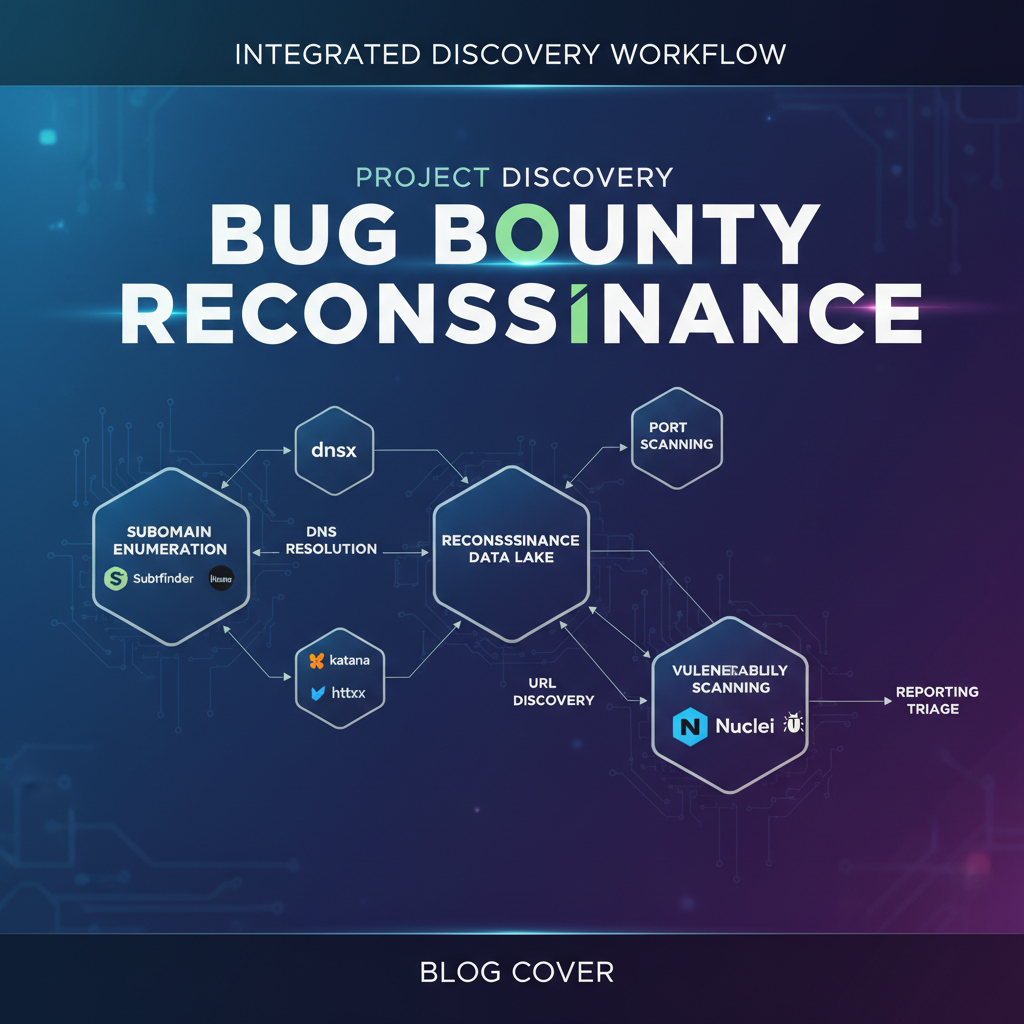
Mastering Bug Bounty Hunting: Strategies & AI Tools for Success Bug bounty hunting has evolved into a lucrative and challenging field for security professionals. This comprehensive guide will walk you through the essential strategies and techniques to maximize your success in bug bounty programs. From selecting the right programs to leveraging advanced AI tools, we'll cover everything you need to know to excel in this competitive arena. ## Selecting the Right Bug Bounty Programs Choosing the right bug bounty programs is crucial for your success. Here are some key factors to consider: ### 1. Program Reputation and Payouts - Reputation: Look for programs with a good track record and positive reviews from other hunters. Programs offered by well-known companies often have more structured and transparent processes. - Payouts: Compare the payment structures. Some programs offer higher payouts for critical vulnerabilities, while others provide bonuses for unique or creative submissions. ### 2. Scope and Assets - Scope: Ensure the program's scope aligns with your skills. For example, if you specialize in web applications, look for programs that focus on web assets. - Assets: Review the list of in-scope assets. Programs with a wide range of assets can offer more opportunities for discovery. ### 3. Program Rules and Guidelines - Rules: Understand the program's rules, including what types of vulnerabilities are eligible and any restrictions on testing methods. - Guidelines: Follow the submission guidelines closely to avoid rejection of valid findings. ### 4. Community and Support - Community: Join hunter communities and forums to get insights and updates on specific programs. - Support: Programs with responsive support teams can provide valuable assistance during your hunting process. ## Reconnaissance Workflow Effective reconnaissance is the foundation of successful bug bounty hunting. Here’s a step-by-step guide to enhance your recon process: ### 1. Information Gathering - Public Information: Start with public sources like the program's website, social media, and job listings to gather basic information. - Technical Details: Use tools like nmap and whatweb to identify technologies and services in use. bash nmap -sV -p- whatweb ### 2. Asset Discovery - Subdomain Enumeration: Use tools like subfinder and amass to discover subdomains. bash subfinder -d amass enum -d - Directory Bruteforcing: Identify hidden directories and files with tools like gobuster and dirb. bash gobuster dir -u http:// -w /path/to/wordlist.txt dirb http:// /path/to/wordlist.txt ### 3. Vulnerability Scanning - Automated Scanners: Use scanners like Nikto and OWASP ZAP for initial vulnerability assessment. bash nikto -h http:// owasp-zap -cmd -quickurl http:// - Manual Testing: Supplement automated scans with manual testing to identify complex vulnerabilities. ### 4. Exploitation and Validation - Exploitation: Use frameworks like Metasploit to exploit identified vulnerabilities. bash msfconsole use exploit/<path/to/exploit> set RHOSTS run - Validation: Ensure the vulnerability is reproducible and understand its impact. ## Common Vulnerability Types by Platform Understanding common vulnerabilities across different platforms can streamline your hunting process. ### Web Applications - Cross-Site Scripting (XSS): Inject malicious scripts into web pages viewed by other users. - SQL Injection: Exploit improper handling of user input to manipulate database queries. - Cross-Site Request Forgery (CSRF): Trick users into performing actions on a web application they are authenticated to. ### Mobile Applications - Insecure Data Storage: Sensitive data stored in insecure locations, such as plaintext files. - Weak Cryptography: Use of weak or outdated encryption algorithms. - Insecure Communication: Lack of proper encryption for data transmitted between the app and servers. ### APIs - Authentication Bypasses: Exploits that allow unauthorized access to API endpoints. - Rate Limiting Issues: Insufficient rate limiting can lead to denial of service or brute-force attacks. - Input Validation Flaws: Failure to validate input can result in various injection attacks. ## Report Writing Tips Crafting a clear and concise report is essential for a successful submission. Here are some best practices: ### 1. Executive Summary - Provide a brief overview of the vulnerability, including its type, impact, and affected assets. ### 2. Detailed Description - Explain the vulnerability in detail, including the root cause and any relevant technical details. ### 3. Reproduction Steps - Include clear, step-by-step instructions for reproducing the vulnerability. ### 4. Impact and Severity - Describe the potential impact of the vulnerability, including any data breaches or system compromises. ### 5. Remediation - Suggest specific steps for remediation, including code snippets or configuration changes if applicable. ### 6. Evidence - Attach screenshots, logs, or other evidence to support your findings. ## Accelerating the Hunting Process with AI Tools AI tools can significantly enhance your bug bounty hunting efficiency. Here’s how mr7.ai’s models can help: ### KaliGPT - Automated Recon: KaliGPT can automate the reconnaissance process, identifying potential vulnerabilities and providing actionable insights. ### 0Day Coder - Exploitation Assistance: 0Day Coder helps in crafting custom exploits for identified vulnerabilities, saving time and effort. ### DarkGPT - Threat Intelligence: DarkGPT provides real-time threat intelligence, keeping you updated on the latest vulnerabilities and attack vectors. ### OnionGPT - Anonymous Reconnaissance: OnionGPT enables anonymous reconnaissance, allowing you to gather information without revealing your identity. > Try it yourself: Use mr7.ai's AI models to automate this process. Start free with 10,000 tokens. ## Comparison of AI Tools for Bug Bounty Hunting | Feature | KaliGPT | 0Day Coder | DarkGPT | OnionGPT | |---------|----------|-----------|---------|-----------| | Automated Recon | ✓ | | | | | Exploitation Assistance | | ✓ | | | | Threat Intelligence | | | ✓ | | | Anonymous Recon | | | | ✓ | Each of these tools offers unique capabilities that can be integrated into your workflow to enhance efficiency and effectiveness. ## Actionable Takeaways - Program Selection: Choose programs that align with your skills and offer fair payouts. - Reconnaissance: Invest time in thorough reconnaissance to identify potential vulnerabilities. - Vulnerability Types: Familiarize yourself with common vulnerabilities across different platforms. - Reporting: Write clear, concise, and detailed reports to maximize your submission success. - AI Tools: Leverage AI tools like those offered by mr7.ai to automate and enhance your hunting process. ## Your AI Security Assistant Awaits From reconnaissance to exploitation to reporting - mr7.ai's AI models cover every phase of your security workflow. Try All Models Free →
Key Takeaways
- Effective bug bounty hunting starts with strategic program selection, focusing on scope, reward structure, and technology stack alignment with your skills.
- A deep understanding of common vulnerabilities (OWASP Top 10) and robust reconnaissance techniques are foundational for uncovering hidden flaws.
- Automating repetitive tasks and analyzing large datasets with AI tools significantly enhances efficiency and the likelihood of discovering complex bugs.
- Developing strong report writing skills, including clear vulnerability descriptions and proof-of-concept steps, is crucial for successful bug validation and payout.
- Continuous learning, staying updated with new attack vectors, and adapting to evolving security landscapes are vital for long-term success in bug bounty hunting.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: What are the key considerations when selecting a bug bounty program to maximize success?
When selecting a bug bounty program, focus on programs with clear scopes, reasonable reward structures, and technologies you are familiar with. Prioritizing programs with active communities or those that align with your specialized skills can also increase your chances of finding valid vulnerabilities.
Q: How can AI tools specifically enhance the reconnaissance phase of bug bounty hunting?
AI tools can significantly enhance reconnaissance by automating the discovery of subdomains, open ports, and potential misconfigurations across a target's infrastructure. They can process vast amounts of data to identify patterns and anomalies that human analysts might miss, thereby streamlining the initial information gathering process.
Q: What role does effective vulnerability reporting play in a bug bounty hunter's success?
Effective vulnerability reporting is paramount because a well-structured report clearly communicates the impact, reproducibility, and potential fixes for a bug. A clear and concise report, complete with a proof-of-concept, increases the likelihood of quick validation by the program's security team and ensures you receive appropriate recognition and rewards.
Q: How can AI tools help with bug bounty hunting?
AI tools like those from mr7.ai, including KaliGPT and mr7 Agent, can automate repetitive tasks such as reconnaissance, vulnerability scanning, and data analysis. KaliGPT can assist in generating exploit payloads or understanding complex vulnerability patterns, while mr7 Agent can orchestrate multi-step attacks and gather intelligence more efficiently, significantly boosting a hunter's productivity and discovery rate.
Q: What's the best way for a beginner to get started in bug bounty hunting and leverage new technologies?
Beginners should start by learning foundational cybersecurity concepts, practicing on deliberately vulnerable applications, and focusing on one or two common vulnerability types. To leverage new technologies, try experimenting with free tokens on platforms like mr7.ai to familiarize yourself with AI-powered tools that can assist in reconnaissance, vulnerability identification, and even report generation, accelerating your learning curve.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.