Master Bug Bounty Hunting: Tips & AI Tools for Success

Master Bug Bounty Hunting: Tips & AI Tools for Success
Bug bounty hunting is an exciting way to contribute to cybersecurity while earning rewards. Whether you're a seasoned hunter or just starting out, these practical tips and insights into AI-powered tools can help you elevate your game.
Finding Bug Bounty Programs
To start your bug bounty journey, you need to know where to look for programs. Here are some effective methods:
- Bug Bounty Platforms: Websites like HackerOne, Bugcrowd, and Intigriti host a wide range of programs.
- Company Websites: Some companies host their own bug bounty programs. Check the security or legal sections of websites for tech giants and startups.
- Social Media and Forums: Follow cybersecurity communities on Twitter, Reddit, and specialized forums to stay updated on new programs and opportunities.
Common Vulnerability Types
Knowing what to look for is half the battle. Here are some common vulnerabilities to focus on:
- Cross-Site Scripting (XSS): Inject malicious scripts into web pages viewed by other users.
- SQL Injection: Manipulate SQL queries to access or manipulate data in the database.
- Cross-Site Request Forgery (CSRF): Trick authenticated users into performing actions they didn't intend to.
- Broken Authentication: Exploit weaknesses in authentication mechanisms to gain unauthorized access.
- Security Misconfigurations: Identify and exploit misconfigurations in servers, databases, or applications.
Report Writing Tips
A well-written report is crucial for getting your findings acknowledged and rewarded. Here are some tips:
- Clear and Concise: Start with a summary of the vulnerability, its impact, and your proposed fix.
- Reproducible Steps: Provide clear, step-by-step instructions for replicating the issue. Include screenshots or video demonstrations if possible.
- Impact Assessment: Explain the potential consequences of the vulnerability, including data breaches, unauthorized access, or financial loss.
- Proposed Fix: Offer a solution or workaround to help the program owner understand how to mitigate the risk.
- Proof of Concept (PoC): Include a PoC to demonstrate the vulnerability in action.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
How AI Tools Can Accelerate Your Hunting Process
AI-powered tools from mr7.ai can significantly enhance your bug hunting efficiency. Here's how:
- KaliGPT: Integrate AI with Kali Linux for automated scanning and vulnerability detection. KaliGPT can help you identify potential security issues faster and more accurately.
- 0Day Coder: Use this tool to discover zero-day vulnerabilities by analyzing code and identifying patterns that human eyes might miss.
- DarkGPT: Leverage DarkGPT for deep web and dark web reconnaissance. It can help you find hidden vulnerabilities and sensitive data that are often overlooked.
- OnionGPT: Specialized for Tor networks, OnionGPT can help you navigate the complexities of anonymity networks to uncover unique vulnerabilities.
Getting Started with mr7.ai
Ready to take your bug bounty hunting to the next level? mr7.ai offers a suite of AI-powered security tools designed to help you find and exploit vulnerabilities more efficiently.
Learn more about our AI tools →
💡 Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to advanced AI models designed for ethical hacking and penetration testing.
Key Takeaways
- Utilize dedicated bug bounty platforms like HackerOne and Bugcrowd as primary sources for finding programs.
- Actively monitor social media and security blogs for announcements of new or private bug bounty programs.
- Leverage AI-powered tools to streamline reconnaissance, vulnerability identification, and report generation in bug bounty hunting.
- Continuously learn and adapt to new technologies and attack vectors to remain effective in the evolving bug bounty landscape.
- Focus on clear, concise, and well-documented vulnerability reports to increase the likelihood of acceptance and higher rewards.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: What are the most effective ways to discover new bug bounty programs?
The most effective methods include regularly checking major bug bounty platforms like HackerOne and Bugcrowd, following security researchers and companies on social media, and subscribing to cybersecurity blogs and newsletters that announce new programs. Networking with other hunters can also provide insights into private or upcoming opportunities.
Q: How can AI tools specifically assist in the reconnaissance phase of bug bounty hunting?
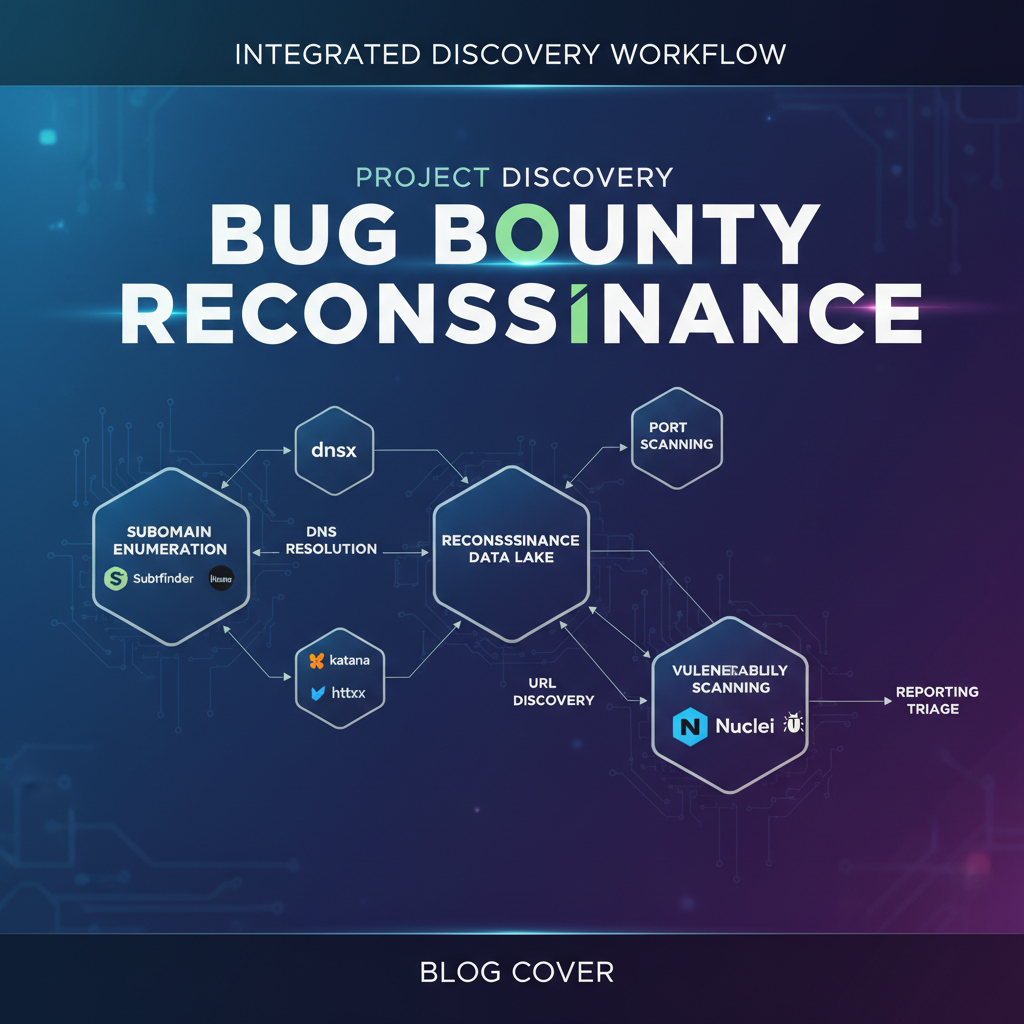
AI tools can significantly enhance reconnaissance by automating tasks such as subdomain enumeration, port scanning, and identifying publicly exposed assets. They can process large amounts of data quickly, highlighting potential entry points or misconfigurations that a human might miss.
Q: What role do bug bounty platforms play in a successful bug bounty hunting career?
Bug bounty platforms are crucial as they centralize program listings, provide structured submission processes, and handle reward distribution. They also offer a reputation system that helps hunters build credibility and gain access to more exclusive programs as their skills improve.
Q: How can AI tools help with this topic?
AI tools like mr7.ai, specifically KaliGPT for intelligent command generation and mr7 Agent for automated vulnerability scanning, can significantly streamline the bug bounty hunting process. They assist in reconnaissance, vulnerability identification, and even report generation, allowing hunters to focus on critical analysis and exploitation.
Q: What is a good starting point for someone new to bug bounty hunting, especially considering AI tools?
A good starting point involves familiarizing yourself with basic web application security concepts and common vulnerabilities (OWASP Top 10). Then, explore bug bounty platforms and consider using AI tools like KaliGPT to assist with initial commands and reconnaissance tasks, which can accelerate the learning curve. Try mr7.ai's free tokens to experiment with these capabilities.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.