Critical Infrastructure Ransomware: Attack Patterns & Defense
Critical Infrastructure Ransomware: Attack Patterns & Defense
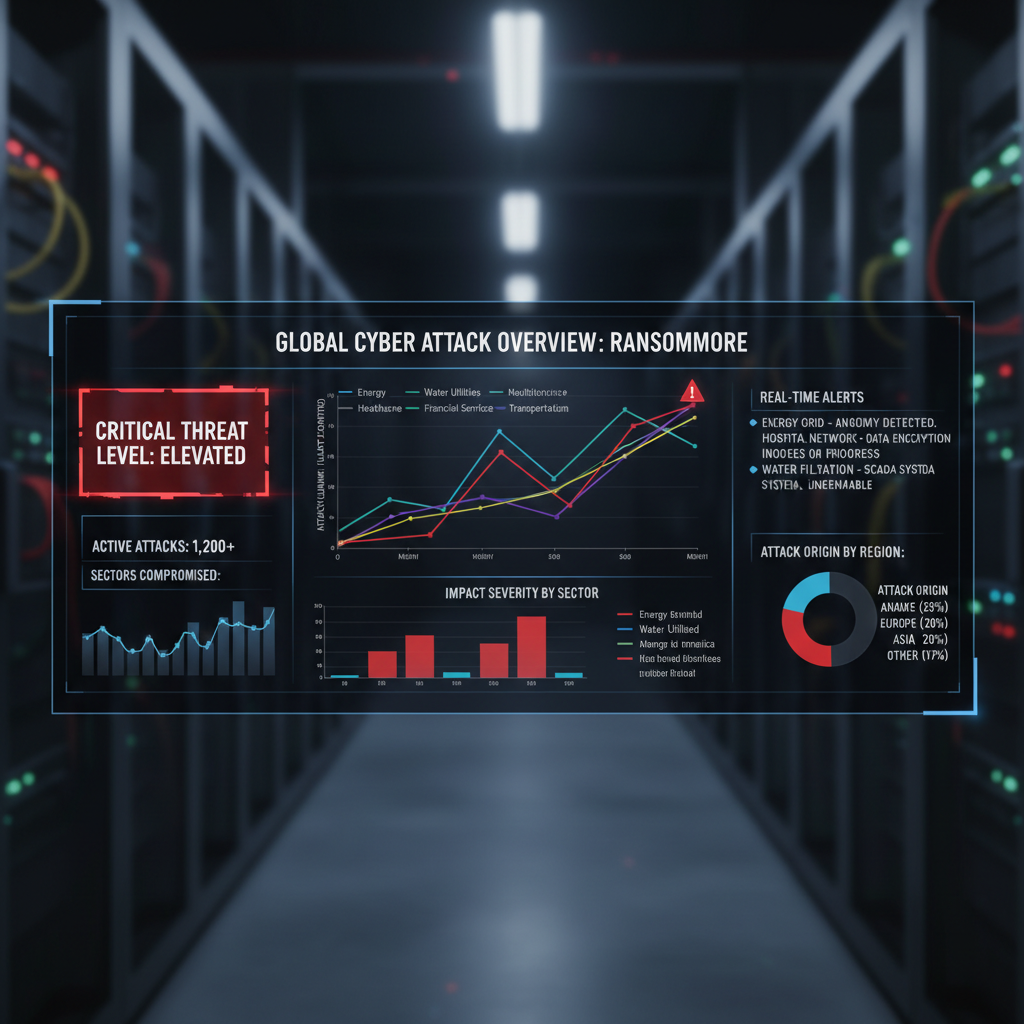
Ransomware attacks against critical infrastructure reached unprecedented levels in Q1 2026, with a staggering 156% increase compared to the previous quarter. This surge coincided with escalating geopolitical tensions and the emergence of several state-sponsored threat actors who have refined their tactics specifically for high-value targets. These adversaries are no longer satisfied with opportunistic strikes; instead, they meticulously plan campaigns designed to cripple essential services such as power grids, water treatment facilities, transportation networks, and healthcare systems.
The consequences extend far beyond financial loss. Disruptions to critical infrastructure can result in widespread public safety risks, economic instability, and erosion of trust in government institutions. In Q1 2026 alone, over 400 confirmed incidents affected operations globally, with average downtime exceeding 18 days per incident. Average ransom demands skyrocketed to $8.4 million, while total recovery costs—including remediation, legal fees, and regulatory penalties—often exceeded $50 million per breach. As regulatory bodies worldwide enforce stricter reporting mandates under frameworks like NIS2 and Executive Order 14028, organizations face heightened scrutiny and potential sanctions for delayed disclosures.
This comprehensive analysis examines the evolving threat landscape targeting critical infrastructure sectors. We dissect prominent attack vectors including supply chain compromises, remote access exploitation, and insider threats. Real-world case studies illustrate how adversaries leveraged novel techniques to infiltrate secure environments, maintain persistence, and execute devastating payloads. Additionally, we explore how AI-driven platforms like mr7.ai empower defenders with intelligent automation and advanced analytics to detect, respond to, and prevent these sophisticated intrusions. With 10,000 free tokens available for new users, mr7.ai enables immediate access to cutting-edge tools including mr7 Agent for automated penetration testing and Dark Web Search capabilities.
What Are the Most Common Attack Vectors Used Against Critical Infrastructure?
In Q1 2026, adversaries targeting critical infrastructure employed increasingly sophisticated attack vectors tailored to exploit inherent vulnerabilities within complex operational technology (OT) and information technology (IT) ecosystems. Among the most prevalent methods were supply chain compromises, remote access exploitation, and insider threats—all of which capitalized on weak security postures and insufficient monitoring controls.
Supply chain attacks gained significant traction during this period, with threat actors compromising trusted third-party vendors to gain indirect access to target environments. Notable incidents included breaches of software update mechanisms, where malicious code was injected into legitimate patches distributed to downstream customers. For example, a widely-used industrial control system vendor experienced a compromise that allowed attackers to backdoor firmware updates affecting hundreds of utility companies. These types of attacks are particularly insidious because they bypass traditional perimeter defenses and often remain undetected until lateral movement has occurred deep within victim networks.
Remote access exploitation also played a pivotal role in facilitating unauthorized entry. Adversaries frequently targeted exposed Remote Desktop Protocol (RDP), Virtual Private Network (VPN), and Secure Shell (SSH) endpoints using credential stuffing, brute-force attacks, and zero-day exploits. Command-line reconnaissance revealed extensive scanning activity:
bash
Example nmap scan identifying open RDP ports
nmap -p 3389 --script rdp-vuln-ms12-020 <target_range>
Once inside, attackers leveraged stolen credentials to escalate privileges and move laterally using tools like mimikatz or custom PowerShell scripts. The proliferation of misconfigured cloud services further expanded attack surfaces, enabling adversaries to pivot between IT and OT environments through shared identity providers or network segmentation flaws.
Insider threats represented another growing concern, especially in cases involving disgruntled employees or compromised accounts with elevated permissions. Threat actors sometimes recruited insiders through social engineering campaigns or financial incentives, gaining access to sensitive systems without triggering external detection mechanisms. Behavioral analytics proved crucial in identifying anomalous activities such as unusual data transfers or irregular login times.
Each vector exploited distinct weaknesses within organizational infrastructures, underscoring the need for layered defense strategies that address both external and internal risks comprehensively.
Key Insight: Supply chain attacks, remote access exploitation, and insider threats form a deadly trio of entry points for critical infrastructure ransomware campaigns. Defenders must adopt proactive measures spanning vendor risk management, robust authentication protocols, and behavioral monitoring to counteract these evolving threats effectively.
Want to try this? mr7.ai offers specialized AI models for security research. Plus, mr7 Agent can automate these techniques locally on your device. Get started with 10,000 free tokens.
How Has Dwell Time Evolved Across Critical Infrastructure Sectors?
Dwell time—the duration between initial compromise and detection—remains one of the most critical metrics in assessing the effectiveness of defensive postures across critical infrastructure sectors. In Q1 2026, the average dwell time across all monitored sectors decreased slightly to 21 days, down from 28 days in Q4 2025. However, this improvement masks significant disparities among individual industries.
Energy sector organizations continued to experience some of the longest dwell times, averaging 32 days due to the complexity of legacy OT systems and limited visibility into network traffic flows. Many facilities still rely on air-gapped networks that lack modern endpoint detection and response (EDR) solutions, creating blind spots that adversaries exploit for extended periods. Water utilities followed closely behind with an average dwell time of 29 days, primarily attributed to outdated SCADA systems and insufficient log aggregation practices.
Transportation networks showed moderate improvements, reducing dwell time to approximately 18 days through enhanced network segmentation and deployment of next-generation firewalls. Nevertheless, the interconnected nature of rail, aviation, and maritime systems introduces additional challenges in correlating threat indicators across disparate domains. Healthcare institutions faced similar struggles, with dwell times hovering around 24 days despite investments in EHR security and medical device monitoring.
To visualize these differences, consider the following table comparing dwell times across sectors:
| Sector | Q4 2025 Avg Dwell Time | Q1 2026 Avg Dwell Time | Change (%) |
|---|---|---|---|
| Energy | 35 days | 32 days | -8.6% |
| Water | 32 days | 29 days | -9.4% |
| Transportation | 21 days | 18 days | -14.3% |
| Healthcare | 27 days | 24 days | -11.1% |
| Overall | 28 days | 21 days | -25.0% |
Despite overall reductions, many organizations still struggle to meet recommended benchmarks of detecting threats within hours rather than weeks. Rapid identification requires continuous monitoring, threat intelligence integration, and automated alerting workflows capable of distinguishing benign anomalies from malicious behavior.
Implementing AI-assisted threat hunting tools like those offered by mr7.ai can significantly reduce dwell times by analyzing vast datasets in real-time and flagging suspicious patterns that human analysts might overlook. New users receive 10,000 free tokens to experiment with these capabilities immediately.
Key Insight: While dwell times have improved marginally, critical infrastructure sectors continue to lag behind best practices for rapid threat detection. Proactive threat hunting, integrated analytics, and AI-driven monitoring are essential for minimizing exposure windows and preventing catastrophic outcomes.
What Are the Financial Impacts of Ransomware on Critical Infrastructure?
The financial toll of ransomware attacks on critical infrastructure escalated dramatically in Q1 2026, driven by higher ransom demands, prolonged outages, and mounting regulatory penalties. Organizations now face multimillion-dollar bills stemming from direct extortion payments, business interruption losses, and costly recovery efforts.
Average ransom demands surged to $8.4 million—a 42% increase from Q4 2025’s $5.9 million. High-profile victims in the energy and transportation sectors reportedly paid ransoms exceeding $50 million to regain access to encrypted systems and prevent data leaks. However, paying ransoms rarely guarantees full restoration or prevents future attacks, making them a risky proposition fraught with reputational damage and legal implications.
Recovery costs proved equally burdensome, with median expenses reaching $53.7 million per incident. These figures encompassed emergency response consulting, forensic investigations, system rebuilds, customer notifications, credit monitoring services, and regulatory fines. For instance, a regional water authority incurred $72 million in cleanup costs after suffering a ransomware infection that disrupted service delivery for nearly three weeks. Similarly, a major airline canceled thousands of flights following a cyberattack, resulting in estimated losses surpassing $100 million.
Regulatory compliance added another layer of financial strain. Under updated frameworks such as NIS2 and EO 14028, breached entities must report incidents within 72 hours and demonstrate adherence to stringent cybersecurity standards. Non-compliance can trigger fines equivalent to 2% of annual global turnover or €10 million, whichever is greater. Several organizations faced multimillion-dollar penalties for failing to implement adequate safeguards or delaying mandatory disclosures.
A breakdown of typical cost components reveals the multifaceted nature of these incidents:
| Cost Component | Typical Range |
|---|---|
| Ransom Payment | $1M – $50M+ |
| Incident Response | $2M – $10M |
| System Restoration | $3M – $15M |
| Legal & Compliance Fees | $0.5M – $5M |
| Regulatory Penalties | $1M – $20M+ |
| Business Interruption | Variable (often highest) |
These astronomical sums underscore the importance of investing in preventive measures rather than reactive responses. Leveraging AI-powered platforms like mr7.ai allows organizations to simulate attacks, identify vulnerabilities proactively, and strengthen resilience before adversaries strike. With 10,000 free tokens available, users can begin evaluating these tools instantly via mr7 Agent.
Key Insight: The financial devastation wrought by ransomware extends far beyond ransom payments themselves. Organizations must factor in cascading costs related to downtime, recovery, litigation, and regulatory enforcement when calculating true exposure and planning mitigation budgets accordingly.
Which Sectors Experienced the Highest Impact From Ransomware in Q1 2026?
While no single industry remained immune to ransomware threats in Q1 2026, certain sectors bore disproportionate brunt due to their strategic importance and operational dependencies on digital systems. Energy, water, transportation, and healthcare emerged as prime targets, each grappling with unique vulnerabilities and consequences.
Energy Sector
The energy sector topped the list in terms of both frequency and severity of attacks. Nation-state actors and financially motivated groups alike recognized the potential for maximum disruption by targeting electrical grids, oil refineries, and natural gas pipelines. A notable campaign dubbed "Blackout Storm" involved coordinated intrusions across multiple utility providers, leading to temporary blackouts affecting millions of residents. Attackers deployed destructive malware alongside encryption routines, rendering backup systems unusable and forcing manual recovery processes that took weeks to complete.
Command-and-control communications were observed using DNS tunneling and steganography to evade detection:
python
Sample Python script extracting hidden data from DNS queries
import dns.resolver
def extract_data(domain): try: answers = dns.resolver.resolve(domain, 'TXT') for rdata in answers: print(rdata.to_text()) except Exception as e: print(f"Error resolving {domain}: {e}")
extract_data("malicious-c2.example.com")
Such stealthy communication channels enabled attackers to exfiltrate sensitive configuration files and deploy custom implants tailored to specific plant architectures.
Water Utilities
Water treatment plants became increasingly attractive targets amid concerns over public health and safety. Several municipalities reported disruptions to chlorination processes and pump controls following successful breaches. One attack involved manipulation of programmable logic controllers (PLCs) to alter chemical dosing levels, posing serious contamination risks. Emergency responders relied heavily on physical inspections and manual overrides to restore normal operations, highlighting gaps in automated fail-safe mechanisms.
Transportation Networks
Airports, seaports, and railway systems faced persistent threats aimed at disrupting logistics chains and passenger travel. Malware infections targeting baggage handling systems, cargo tracking databases, and ticketing platforms caused widespread delays and cancellations. An international airport suffered a complete shutdown lasting five days after attackers encrypted core reservation servers, forcing staff to revert to paper-based check-in procedures. The ripple effects impacted connecting flights and hotel bookings worldwide, amplifying economic losses exponentially.
Healthcare Institutions
Hospitals and clinics encountered relentless pressure from ransomware operators seeking quick payouts under duress. Patient records, diagnostic imaging archives, and life-support equipment interfaces were common targets. During one harrowing episode, a children’s hospital temporarily suspended surgeries after its radiology department fell victim to an encryption attack. Critical care units had to rely on offline backups and handwritten notes, straining already overwhelmed personnel.
Collectively, these sectors demonstrated varying degrees of preparedness yet shared common shortcomings in asset inventory management, patch prioritization, and cross-domain coordination. Addressing systemic weaknesses requires holistic approaches incorporating threat modeling, red team exercises, and AI-enhanced monitoring solutions like those provided by mr7.ai. Try them today with 10,000 complimentary tokens.
Key Insight: Critical infrastructure ransomware disproportionately affects energy, water, transportation, and healthcare sectors due to their reliance on interconnected technologies and societal significance. Tailored defense strategies must account for sector-specific risks and operational constraints to mitigate cascading failures effectively.
How Have New Regulatory Requirements Affected Incident Reporting and Response Procedures?
The introduction of stricter regulatory frameworks in early 2026 fundamentally altered how organizations approach ransomware incident reporting and response procedures. Mandates such as the EU’s NIS2 Directive, the US Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA), and enhanced provisions under Executive Order 14028 imposed unprecedented obligations on covered entities regarding transparency, timeliness, and remediation accountability.
Under NIS2, operators of essential services must notify national competent authorities within 24 hours of becoming aware of a significant incident. This represents a substantial reduction from previous thresholds and necessitates robust internal escalation pathways. Entities are also required to conduct root cause analyses and submit detailed post-incident reports within 30 days, outlining corrective actions taken and lessons learned. Failure to comply carries severe penalties, including suspension of operating licenses and monetary sanctions proportional to annual revenues.
Similarly, CIRCIA mandates that critical infrastructure owners report qualifying cybersecurity incidents to the Cybersecurity and Infrastructure Security Agency (CISA) within 72 hours. Covered sectors include energy, water, transportation, communications, and healthcare. Reports must include information about the nature of the incident, affected systems, mitigation steps underway, and contact details for designated representatives. CISA retains authority to issue binding directives requiring immediate remediation if deemed necessary to protect broader national interests.
These regulatory shifts prompted widespread changes in organizational policies and technological investments. Security teams scrambled to establish formalized incident response playbooks aligned with statutory timelines, integrate automated alerting mechanisms, and enhance collaboration with law enforcement agencies. Tools supporting real-time log aggregation, forensic evidence preservation, and stakeholder communication became indispensable assets in maintaining compliance.
For example, many enterprises adopted SIEM platforms capable of generating standardized incident reports compatible with regulatory templates. Scripts automating evidence collection streamlined the documentation process:
powershell
PowerShell script collecting relevant logs for incident reporting
$LogsPath = "C:\Windows\System32\winevt\Logs" $OutputDir = "C:\IncidentReports"
Copy-Item "$LogsPath\Security.evtx" -Destination "$OutputDir\Security_$((Get-Date).ToString('yyyyMMdd_HHmmss')).evtx" wevtutil epl Application "$OutputDir\Application_$((Get-Date).ToString('yyyyMMdd_HHmmss')).evtx"
Write-Host "Log collection completed successfully."
Moreover, board-level oversight intensified as executives assumed personal liability for inadequate cybersecurity governance. Regular tabletop exercises simulating ransomware scenarios helped validate readiness plans and refine decision-making protocols under stress conditions. Investment in AI-powered threat intelligence feeds and predictive analytics further bolstered situational awareness capabilities.
Organizations leveraging mr7.ai benefited from built-in compliance modules that automatically generate audit trails and assist with regulatory submissions. The platform’s mr7 Agent facilitates rapid vulnerability assessments and penetration testing to preemptively address gaps identified during mock drills. All features are accessible with 10,000 free tokens upon registration.
Key Insight: Stricter regulatory regimes compel critical infrastructure entities to adopt more rigorous incident reporting and response practices. Automation, structured workflows, and proactive testing are vital for meeting compliance deadlines while minimizing operational disruption during crisis situations.
What Were Some Notable Ransomware Incidents in Q1 2026 and Their Operational Consequences?
Several high-profile ransomware incidents in Q1 2026 captured global attention due to their scale, sophistication, and profound operational impacts. These events served as stark reminders of the evolving threat landscape and highlighted critical vulnerabilities within supposedly secure environments.
One of the most disruptive attacks targeted a multinational energy conglomerate, impacting operations across North America and Europe. Dubbed “Operation Gridlock,” the assault began with a spear-phishing email compromising a junior engineer’s workstation. From there, attackers moved laterally using Mimikatz to harvest domain credentials and eventually accessed supervisory control and data acquisition (SCADA) systems managing pipeline flow rates and compressor stations. Encryption routines disabled monitoring dashboards, forcing operators to manually inspect field devices and temporarily halt production. The company reported revenue losses exceeding $200 million and spent over $80 million restoring systems and upgrading security infrastructure.
Another noteworthy incident involved a regional transit authority responsible for urban rail services. Adversaries exploited a known vulnerability in an unpatched web application used for employee scheduling to gain initial access. Once inside, they deployed Cobalt Strike beacon implants and spent nearly two weeks mapping the network before launching synchronized encryption attacks against fare collection terminals, maintenance databases, and dispatch consoles. Service disruptions lasted eight days, affecting daily commutes for over half a million passengers and prompting city officials to declare a state of emergency. Legal proceedings resulted in class-action lawsuits and federal investigations into procurement practices.
In the healthcare domain, a pediatric specialty hospital endured a particularly harrowing ordeal when ransomware infected its electronic health record (EHR) system. Patient appointments were canceled en masse, laboratory results delayed, and medication orders suspended pending manual verification. Physicians reverted to paper charts and dictated notes, severely hampering clinical efficiency and patient care quality. Although no lives were lost directly, several families filed complaints alleging negligence and emotional distress. The institution ultimately paid a $12 million ransom but only recovered partial data integrity, necessitating extensive revalidation procedures.
A fourth case involved a municipal water treatment facility experiencing dual-stage compromise involving both ransomware and wiper malware. Initial infiltration occurred via a compromised contractor account, allowing intruders to modify PLC logic controlling filtration cycles. Simultaneously, they initiated file encryption across administrative workstations and database servers. Public alerts warned residents to boil tap water for five consecutive days while technicians worked around the clock to recalibrate chemical dosing parameters. Estimated damages approached $35 million, including infrastructure upgrades mandated by environmental regulators.
These incidents underscore the necessity of adopting resilient architectures, conducting regular penetration tests, and deploying intelligent threat detection systems. Platforms like mr7.ai offer specialized models trained on adversarial TTPs and enable practitioners to emulate realistic attack scenarios using mr7 Agent. Sign up now to explore these capabilities with 10,000 free tokens.
Key Insight: Notable ransomware incidents in Q1 2026 exposed systemic vulnerabilities across diverse critical infrastructure sectors. Comprehensive incident analysis reveals recurring themes of poor credential hygiene, inadequate network segmentation, and delayed threat recognition—all remediable through disciplined cybersecurity hygiene and advanced analytical tools.
How Can AI-Powered Tools Like mr7.ai Help Defend Against Critical Infrastructure Ransomware?
Artificial intelligence has become instrumental in defending against the increasingly complex and adaptive nature of ransomware targeting critical infrastructure. Traditional signature-based detection methods prove insufficient against polymorphic malware variants and living-off-the-land techniques favored by modern adversaries. AI-powered platforms like mr7.ai bridge this gap by providing intelligent automation, contextual threat intelligence, and scalable vulnerability assessment capabilities uniquely suited for high-stakes environments.
mr7.ai delivers a suite of specialized models designed for various aspects of cybersecurity research and defense. KaliGPT assists ethical hackers in crafting effective penetration testing methodologies, guiding users through reconnaissance phases, privilege escalation paths, and post-exploitation strategies based on real-time environmental feedback. Meanwhile, 0Day Coder accelerates exploit development and PoC creation, helping red teams validate assumptions quickly and securely. DarkGPT supports advanced research tasks requiring unrestricted knowledge access, while OnionGPT facilitates safe exploration of dark web forums where threat actors coordinate and share tactics.
Central to mr7.ai's offerings is the mr7 Agent—a powerful local automation engine that executes complex workflows directly on user devices. Unlike cloud-based alternatives, mr7 Agent operates independently of internet connectivity, ensuring confidentiality and eliminating latency concerns during time-sensitive engagements. It supports full-stack testing ranging from network enumeration (nmap, masscan) to application fuzzing (boofuzz, afl++) and binary reverse engineering (Ghidra, Radare2). Integration with popular frameworks like Metasploit and Empire streamlines payload generation and command execution orchestration.
Consider how mr7 Agent could automate a multi-phase ransomware simulation exercise:
yaml
Sample mr7 Agent workflow definition
name: "Ransomware Simulation" tasks:
- name: "Network Discovery"
module: "network.discover"
args:
target: "192.168.1.0/24"
- name: "Vulnerability Scan" module: "vuln.scan" depends_on: ["Network Discovery"] args: policy: "cis_benchmark"
- name: "Credential Harvesting" module: "auth.harvest" depends_on: ["Vulnerability Scan"] args: method: "kerberoasting"
- name: "Lateral Movement" module: "lateral.move" depends_on: ["Credential Harvesting"] args: technique: "pass_the_hash"
- name: "Payload Deployment" module: "payload.deploy" depends_on: ["Lateral Movement"] args: type: "ransomware_simulator" encrypt_files: false
By executing predefined sequences autonomously, mr7 Agent reduces manual overhead while increasing consistency and repeatability. Users retain granular control over every stage, enabling fine-tuning based on specific objectives or environmental constraints.
Beyond automation, mr7.ai enhances situational awareness through machine learning algorithms trained on massive datasets encompassing historical breaches, malware samples, and behavioral patterns. Predictive analytics flag anomalous network behaviors indicative of early-stage compromise, empowering defenders to intervene before encryption begins. Natural language processing capabilities parse unstructured threat feeds, extracting actionable intelligence from blog posts, forum discussions, and dark web chatter.
Furthermore, mr7’s modular architecture accommodates custom integrations with existing enterprise tools such as SIEMs, SOARs, and ticketing systems. RESTful APIs facilitate seamless data exchange and centralized dashboard visualization, simplifying complex workflows and improving cross-functional collaboration.
New users can immediately harness these benefits by registering for mr7.ai and claiming 10,000 free tokens. Whether conducting routine audits, validating incident response procedures, or preparing for certification exams, mr7 Agent provides the speed, accuracy, and flexibility needed to stay ahead of evolving threats.
Key Insight: AI-driven platforms like mr7.ai revolutionize critical infrastructure defense by combining intelligent automation, deep threat insights, and flexible deployment options. Leveraging tools such as mr7 Agent empowers security teams to anticipate, detect, and neutralize ransomware threats faster and more efficiently than ever before.
Key Takeaways
- Critical infrastructure ransomware incidents rose 156% in Q1 2026, driven by geopolitical factors and emerging threat actors.
- Supply chain compromises, remote access exploitation, and insider threats represent the dominant attack vectors.
- Average dwell time remains alarmingly high at 21 days, exposing organizations to prolonged exposure and secondary compromises.
- Financial impacts exceed $50 million per incident on average, including ransoms, recovery costs, and regulatory penalties.
- Energy, water, transportation, and healthcare sectors suffer the greatest operational disruptions due to their societal importance and system interdependencies.
- New regulations mandate swift incident reporting and impose strict penalties for non-compliance, reshaping organizational governance structures.
- AI-powered tools like mr7.ai provide scalable defense mechanisms through intelligent automation, predictive analytics, and comprehensive testing capabilities.
Frequently Asked Questions
Q: Why are critical infrastructure sectors particularly vulnerable to ransomware?
Critical infrastructure sectors often operate legacy systems with limited update cycles, possess high societal value motivating attackers, and exhibit complex interdependencies that amplify cascading failure risks. Additionally, many facilities prioritize uptime over security, creating exploitable gaps in protective measures.
Q: How do ransomware groups typically gain initial access to critical infrastructure networks?
Common initial access methods include phishing emails delivering malicious attachments, exploiting unpatched internet-facing applications, brute-forcing weak remote desktop credentials, and leveraging compromised third-party vendors through supply chain attacks. Social engineering remains a potent tool for bypassing technical defenses.
Q: What distinguishes ransomware attacks on critical infrastructure from general enterprise breaches?
Infrastructure-focused attacks tend to involve deeper reconnaissance phases, customized malware payloads targeting specific industrial control systems, and greater emphasis on destructive payloads beyond mere encryption. Motivations may include political coercion, economic sabotage, or ideological messaging rather than pure profit extraction.
Q: How effective are backups in recovering from critical infrastructure ransomware attacks?
Backups serve as a cornerstone of recovery but are not foolproof. Sophisticated adversaries often seek and destroy backup repositories prior to encryption, rendering traditional restore mechanisms ineffective. Immutable storage solutions and offline/offsite copies improve survivability but require careful implementation and frequent validation.
Q: What role does artificial intelligence play in defending against infrastructure ransomware?
AI enhances defense capabilities through anomaly detection, threat intelligence correlation, automated response orchestration, and predictive modeling of attacker behavior. Platforms like mr7.ai leverage specialized models to accelerate red teaming, streamline compliance audits, and simulate adversarial campaigns for proactive hardening purposes.
Stop Manual Testing. Start Using AI.
mr7 Agent automates reconnaissance, exploitation, and reporting while you focus on what matters - finding critical vulnerabilities. Plus, use KaliGPT and 0Day Coder for real-time AI assistance.