Boost Your Bug Bounty Hunting: Top Tips & AI Tools

Boost Your Bug Bounty Hunting: Top Tips & AI Tools
Bug bounty hunting is an exciting and rewarding field for cybersecurity enthusiasts. Whether you're just starting out or looking to refine your skills, this guide will provide you with practical tips to enhance your bug bounty journey.
Finding Bug Bounty Programs
One of the first steps in bug bounty hunting is identifying programs that align with your skills and interests. Here are some tips to help you find the right programs:
- Platforms: Start by exploring popular bug bounty platforms like Intigriti, HackerOne, and Bugcrowd. These platforms host a wide range of programs from various industries.
- Research: Use search engines and social media to find companies that offer bug bounty programs. Sometimes, companies announce their programs on their blogs or social media channels.
- Networking: Connect with other bug bounty hunters through forums, social media groups, and local meetups. Networking can provide insights into lesser-known programs and opportunities.
Common Vulnerability Types
Understanding common vulnerability types is crucial for effective bug bounty hunting. Here are some of the most frequently encountered vulnerabilities:
- SQL Injection: Occurs when user input is not properly sanitized, allowing attackers to manipulate SQL queries.
- Cross-Site Scripting (XSS): Allows attackers to inject malicious scripts into web pages viewed by other users.
- Cross-Site Request Forgery (CSRF): Tricks a user into performing actions on a web application where they are authenticated.
- Insecure Direct Object References (IDOR): Happens when an application exposes a reference to an internal implementation object, such as a file, database record, or key, as a URL or form parameter.
- Authentication and Authorization Flaws: Issues with how users are authenticated and authorized can lead to unauthorized access.
Report Writing Tips
A well-written report is essential for getting your findings acknowledged and rewarded. Here are some tips for effective report writing:
- Clear and Concise: Start with a clear title and a brief summary of the vulnerability. Use bullet points to list steps to reproduce the issue.
- Detailed Steps: Provide detailed, step-by-step instructions on how to reproduce the vulnerability. Include any necessary screenshots or code snippets.
- Impact Assessment: Explain the potential impact of the vulnerability, including the risk to the application and its users.
- Remediation: Suggest possible fixes or mitigation strategies. This shows that you understand the issue and are committed to helping resolve it.
- Professional Tone: Maintain a professional and respectful tone throughout the report.
Try it yourself: Use mr7.ai's AI models to automate this process, or download mr7 Agent for local automated pentesting. Start free with 10,000 tokens.
Accelerating the Hunting Process with AI
AI tools can significantly enhance your bug bounty hunting efforts by automating repetitive tasks and providing insights. Here’s how mr7.ai's AI tools can help:
- KaliGPT: This tool can assist in automating penetration testing tasks, helping you identify vulnerabilities more efficiently.
- 0Day Coder: Use this AI to generate exploit code quickly, saving you time and effort in developing custom exploits.
- DarkGPT: Leverage this tool for advanced threat intelligence and dark web monitoring, keeping you ahead of emerging threats.
- OnionGPT: Enhance your anonymity and security while hunting by using this tool for secure communication and data analysis.
By integrating these AI tools into your workflow, you can focus more on strategic thinking and less on manual, time-consuming tasks.
💡 Try AI-Powered Security Tools
Join thousands of security researchers using mr7.ai. Get instant access to advanced AI models designed for ethical hacking and penetration testing.
Key Takeaways
- Start your bug bounty journey by carefully selecting programs that match your skills and interests to maximize your success rate.
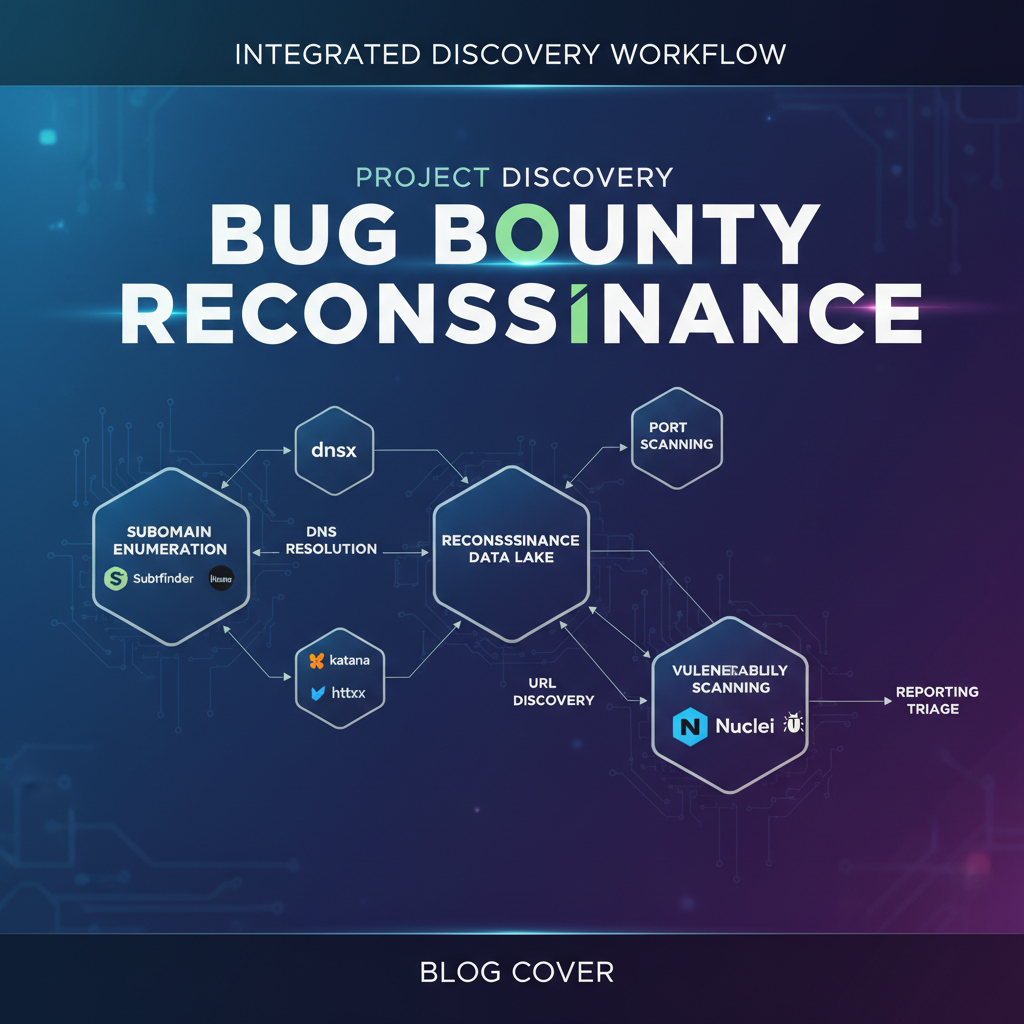
- Effective reconnaissance, including subdomain enumeration and port scanning, is crucial for uncovering potential vulnerabilities.
- Prioritize understanding the target application's business logic, as many critical bugs stem from logical flaws rather than technical ones.
- Leverage automation tools for repetitive tasks like scanning and information gathering to free up time for deeper analysis.
- Continuously learn and adapt to new techniques and exploit methodologies to stay ahead in the ever-evolving bug bounty landscape.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: How can I effectively find bug bounty programs that suit my skill set?
To find suitable bug bounty programs, begin by exploring major platforms like HackerOne and Bugcrowd, filtering by technology stack or specific vulnerability types you're familiar with. Additionally, look for private programs or direct invitations once you've built a reputation and demonstrated proficiency in public programs.
Q: What are the most critical initial steps for reconnaissance in bug bounty hunting?
Initial reconnaissance should focus on comprehensive subdomain enumeration and thorough port scanning to map the target's attack surface. Understanding the technologies in use and identifying exposed services are foundational for pinpointing potential entry points for further investigation.
Q: Why is understanding business logic important for finding critical bugs?
Understanding the business logic of an application is paramount because many high-impact vulnerabilities arise from flaws in how the application handles its core functions, rather than purely technical exploits. These logical flaws, such as improper authorization or privilege escalation, often lead to significant security breaches.
Q: How can AI tools help with bug bounty hunting?
AI tools can significantly enhance bug bounty hunting by automating repetitive tasks like reconnaissance, vulnerability scanning, and report generation. Specifically, mr7.ai offers KaliGPT for advanced query and analysis, and mr7 Agent can automate complex attack sequences, allowing hunters to focus on deeper analysis and exploit development.
Q: What's a good first step for someone new to bug bounty hunting looking to improve?
A good first step for newcomers is to start with well-defined, public bug bounty programs with clear scopes and rules, focusing on common vulnerabilities like XSS or SQLi. To quickly get hands-on experience and explore advanced techniques, consider trying mr7.ai's free tokens to experiment with AI-powered tools like KaliGPT.
Ready to Level Up Your Security Research?
Get 10,000 free tokens and start using KaliGPT, 0Day Coder, DarkGPT, OnionGPT, and mr7 Agent today. No credit card required!