Advanced Tips for Bug Bounty Hunters: Find & Exploit Vulnerabilities

Advanced Tips for Bug Bounty Hunters: Find & Exploit Vulnerabilities
Bug bounty hunting is an exciting and rewarding field where security researchers can earn significant rewards by identifying and reporting vulnerabilities in software and systems. Whether you're just starting out or looking to refine your skills, these practical tips will help you navigate the world of bug bounty programs and maximize your success.
Finding Bug Bounty Programs
Before you can start hunting, you need to find programs that align with your skills and interests. Here are some tips to get you started:
-
Platforms: Utilize popular bug bounty platforms like HackerOne, Bugcrowd, and Intigriti. These platforms host a wide range of programs from various organizations.
-
Social Media: Follow security researchers and companies on Twitter and LinkedIn. They often announce new programs and updates.
-
Community Forums: Engage with communities on platforms like Reddit (r/bugbounty, r/netsec) and specialized forums where hunters share tips and program recommendations.
-
Company Websites: Directly check the websites of companies you're interested in. Many have dedicated security pages listing their bug bounty programs.
Common Vulnerability Types
Understanding the types of vulnerabilities you're likely to encounter is crucial. Here are some of the most common:
-
Cross-Site Scripting (XSS): Injecting malicious scripts into web pages viewed by other users.
-
SQL Injection: Exploiting vulnerabilities in SQL queries to manipulate databases.
-
Cross-Site Request Forgery (CSRF): Tricking users into performing actions on a web application where they're authenticated.
-
Broken Authentication: Weaknesses in authentication mechanisms that allow unauthorized access.
-
Security Misconfigurations: Improperly configured servers or applications that expose sensitive data.
Writing Effective Reports
A well-written report can significantly impact the likelihood of your findings being accepted and rewarded. Here are some tips:
-
Clear and Concise: Start with a summary of the vulnerability, its impact, and the steps to reproduce it.
-
Detailed Steps: Provide a step-by-step guide on how to exploit the vulnerability, including any necessary prerequisites.
-
Screenshots and Code: Include relevant screenshots and code snippets to support your findings.
-
Impact Assessment: Explain the potential impact of the vulnerability, including real-world scenarios and affected users.
-
Remediation Suggestions: Offer recommendations on how to fix the issue, demonstrating your understanding of the problem.
Automate this: mr7 Agent can run these security assessments automatically on your local machine. Combine it with KaliGPT for AI-powered analysis. Get 10,000 free tokens at mr7.ai.
Accelerating the Hunting Process with AI Tools
AI-powered tools can significantly enhance your bug bounty hunting efficiency. Here's how mr7.ai's tools can help:
-
KaliGPT: This tool integrates with Kali Linux, providing AI-assisted penetration testing. It can help automate routine tasks, freeing up your time to focus on more complex vulnerabilities.
-
0Day Coder: Use this tool to generate exploit code for known vulnerabilities, saving you time and effort in writing custom exploits.
-
DarkGPT: Leverage DarkGPT for deep web and dark web investigations. It can help you uncover hidden vulnerabilities and sensitive data.
-
OnionGPT: This tool is designed for anonymous and secure communications, ensuring your hunting activities remain private and protected.
By incorporating these AI tools into your workflow, you can streamline your processes, identify vulnerabilities faster, and increase your overall effectiveness as a bug bounty hunter.
Conclusion
Bug bounty hunting is a dynamic and ever-evolving field. By staying informed about new programs, understanding common vulnerabilities, writing effective reports, and leveraging AI tools, you can enhance your skills and increase your chances of success. Remember, continuous learning and adaptation are key to thriving in this exciting domain.
⚡ Supercharge Your Workflow
Professional security researchers trust mr7.ai for code analysis, vulnerability research, and automated security testing.
Start with 10,000 Free Tokens →
Key Takeaways
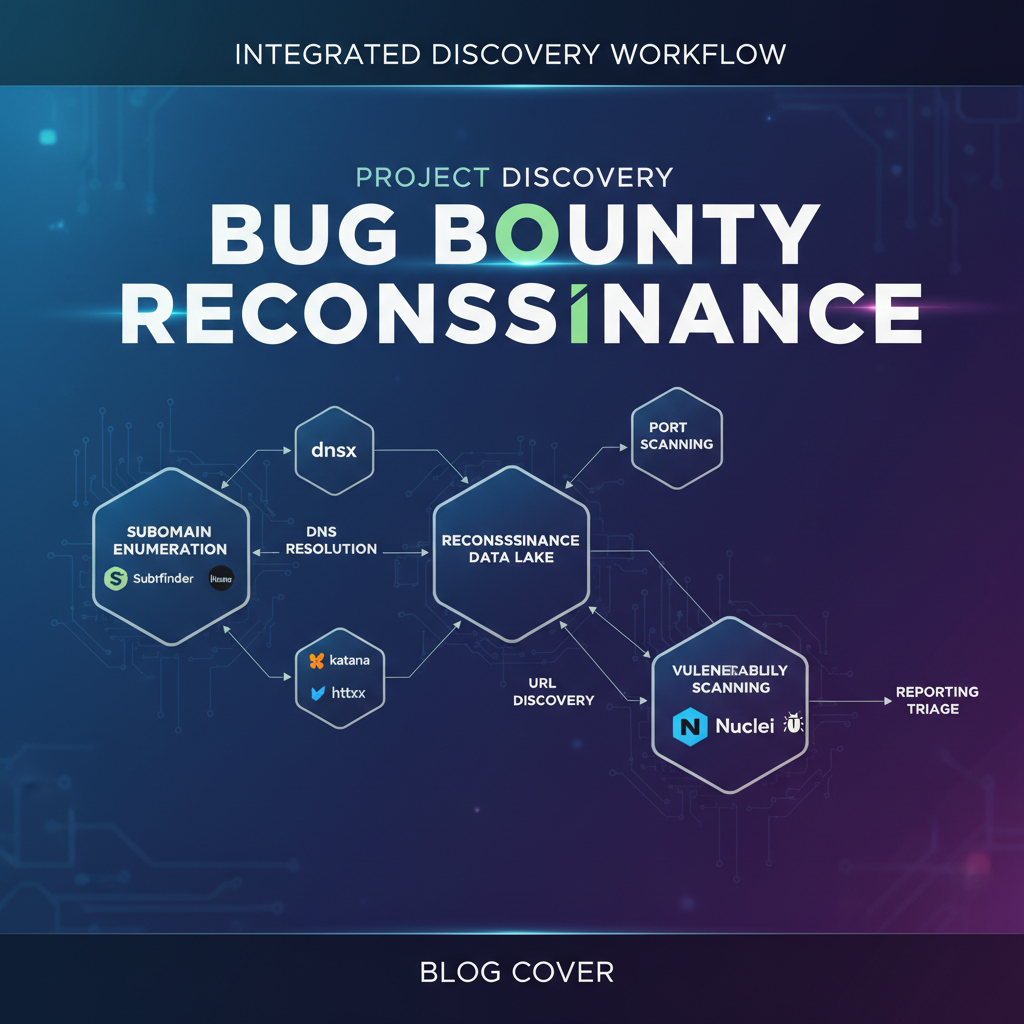
- Thoroughly understand the target's attack surface by mapping all subdomains, APIs, and third-party integrations.
- Focus on less obvious vulnerability classes such as business logic flaws, race conditions, and deserialization issues, which often yield higher rewards.
- Develop custom tooling and scripts to automate repetitive tasks and identify unique vulnerability patterns.
- Practice responsible disclosure and meticulous reporting, providing clear reproduction steps, impact analysis, and potential remediations.
- Continuously learn and adapt to new technologies and attack techniques by staying updated with industry trends and research.
- Tools like mr7 Agent and KaliGPT can help automate and enhance the techniques discussed in this article
Frequently Asked Questions
Q: What are some advanced techniques for discovering hidden attack surfaces beyond standard subdomain enumeration?
Advanced techniques include monitoring certificate transparency logs for new subdomains, analyzing JavaScript files for hidden API endpoints, and using passive reconnaissance tools to uncover forgotten assets. Additionally, examining historical DNS records and web archives can reveal previously active but now unlisted infrastructure.
Q: How can bug bounty hunters identify and exploit complex business logic vulnerabilities?
Identifying business logic vulnerabilities requires understanding the application's intended functionality and then looking for ways to manipulate it through unexpected user flows, parameter tampering, or bypassing authorization checks. This often involves chaining multiple seemingly minor flaws to achieve a significant impact, like unauthorized privilege escalation or financial fraud.
Q: What role does custom tooling play in advanced bug bounty hunting?
Custom tooling allows hunters to automate specific reconnaissance tasks, perform targeted fuzzing based on unique application characteristics, and parse large datasets for unusual patterns that off-the-shelf tools might miss. Developing custom scripts for common vulnerability classes can significantly reduce detection time and increase efficiency.
Q: How can AI tools help with this topic?
AI tools like mr7.ai, particularly KaliGPT, can assist bug bounty hunters by generating exploit suggestions based on vulnerability types, helping to write custom proof-of-concept code, and analyzing large amounts of data to identify potential attack vectors. The mr7 Agent can automate reconnaissance tasks and help prioritize potential vulnerabilities for further investigation.
Q: What's a good approach for someone looking to move from basic vulnerability finding to more advanced exploitation?
To move to advanced exploitation, focus on mastering one or two complex vulnerability classes, such as deserialization or server-side request forgery (SSRF), by studying past write-ups and practicing in labs. Experiment with chaining multiple vulnerabilities for greater impact and consider trying mr7.ai's free tokens to explore how AI can augment your learning and hunting process.
Built for Bug Bounty Hunters & Pentesters
Whether you're hunting bugs on HackerOne, running a pentest engagement, or solving CTF challenges, mr7.ai and mr7 Agent have you covered. Start with 10,000 free tokens.